444:
194:
3047:
439:{\displaystyle {\begin{aligned}\operatorname {HMAC} (K,m)&=\operatorname {H} {\Bigl (}{\bigl (}K'\oplus opad{\bigr )}\parallel \operatorname {H} {\bigl (}\left(K'\oplus ipad\right)\parallel m{\bigr )}{\Bigr )}\\K'&={\begin{cases}\operatorname {H} \left(K\right)&{\text{if}}\ K{\text{ is larger than block size}}\\K&{\text{otherwise}}\end{cases}}\end{aligned}}}
40:
1057:), suffers from the problem that an attacker who can find a collision in the (unkeyed) hash function has a collision in the MAC (as two messages m1 and m2 yielding the same hash will provide the same start condition to the hash function before the appended key is hashed, hence the final hash will be the same). Using MAC =
1668:
under the sole assumption that the compression function is a PRF. This recovers a proof based guarantee since no known attacks compromise the pseudorandomness of the compression function, and it also helps explain the resistance-to-attack that HMAC has shown even when implemented with hash functions
1131:
The cryptographic strength of the HMAC depends upon the size of the secret key that is used and the security of the underlying hash function used. It has been proven that the security of an HMAC construction is directly related to security properties of the hash function used. The most common attack
125:
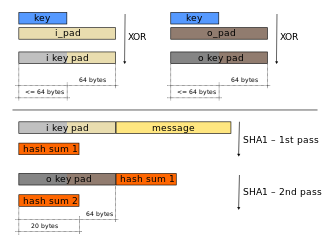
HMAC uses two passes of hash computation. Before either pass, the secret key is used to derive two keys – inner and outer. Next, the first pass of the hash algorithm produces an internal hash derived from the message and the inner key. The second pass produces the final HMAC code derived from the
1155:. This property is sometimes raised as a possible weakness of HMAC in password-hashing scenarios: it has been demonstrated that it's possible to find a long ASCII string and a random value whose hash will be also an ASCII string, and both values will produce the same HMAC output.
1242:
HMAC_MD5("key", "The quick brown fox jumps over the lazy dog") = 80070713463e7749b90c2dc24911e275 HMAC_SHA1("key", "The quick brown fox jumps over the lazy dog") = de7c9b85b8b78aa6bc8a7a36f70a90701c9db4d9 HMAC_SHA256("key", "The quick brown fox jumps over the lazy dog") =
1243:
f7bc83f430538424b13298e6aa6fb143ef4d59a14946175997479dbc2d1a3cd8 HMAC_SHA512("key", "The quick brown fox jumps over the lazy dog") = b42af09057bac1e2d41708e48a902e09b5ff7f12ab428a4fe86653c73dd248fb82f948a549f7b791a5b41915ee4d1ec3935357e4e2317250d0372afa2ebeeb3a
141:. For example, SHA-256 operates on 512-bit blocks. The size of the output of HMAC is the same as that of the underlying hash function (e.g., 256 and 512 bits in the case of SHA-256 and SHA3-512, respectively), although it can be truncated if desired.
144:
HMAC does not encrypt the message. Instead, the message (encrypted or not) must be sent alongside the HMAC hash. Parties with the secret key will hash the message again themselves, and if it is authentic, the received and computed hashes will match.
1028:
The design of the HMAC specification was motivated by the existence of attacks on more trivial mechanisms for combining a key with a hash function. For example, one might assume the same security that HMAC provides could be achieved with MAC =
1559:
Unlike SHA-1 and SHA-2, Keccak does not have the length-extension weakness, hence does not need the HMAC nested construction. Instead, MAC computation can be performed by simply prepending the message with the
1208:
presented a distinguishing attack on HMAC-MD5 without using related keys. It can distinguish an instantiation of HMAC with MD5 from an instantiation with a random function with 2 queries with probability 0.87.
1132:
against HMACs is brute force to uncover the secret key. HMACs are substantially less affected by collisions than their underlying hashing algorithms alone. In particular, Mihir
Bellare proved that HMAC is a
199:
1633:
The strongest attack known against HMAC is based on the frequency of collisions for the hash function H ("birthday attack") , and is totally impractical for minimally reasonable hash functions.
1123:
competition winner, doesn't need this nested approach and can be used to generate a MAC by simply prepending the key to the message, as it is not susceptible to length-extension attacks.
3027:
2857:
1190:
or HMAC with a random function. Differential distinguishers allow an attacker to devise a forgery attack on HMAC. Furthermore, differential and rectangle distinguishers can lead to
470:
1041:). However, this method suffers from a serious flaw: with most hash functions, it is easy to append data to the message without knowing the key and obtain another valid MAC ("
94:
by delegating the key exchange to the communicating parties, who are responsible for establishing and using a trusted channel to agree on the key prior to communication.
567:
547:; either by padding to the right with 0s up to the block size, or by hashing down to less than or equal to the block size first and then padding to the right with zeros.
1108:
from each other and so the inner and outer keys will have fewer bits in common. The security reduction of HMAC does require them to be different in at least one bit.
593:
541:
1919:
659:
628:
1136:(PRF) under the sole assumption that the compression function is a PRF. Therefore, HMAC-MD5 does not suffer from the same weaknesses that have been found in MD5.
2710:
514:
492:
1198:
with this knowledge. These attacks do not contradict the security proof of HMAC, but provide insight into HMAC based on existing cryptographic hash functions.
2630:
2018:
2047:
877:
demonstrates how HMAC may be implemented. The block size is 512 bits (64 bytes) when using one of the following hash functions: SHA-1, MD5, RIPEMD-128.
122:
of the HMAC depends upon the cryptographic strength of the underlying hash function, the size of its hash output, and the size and quality of the key.
75:
and authenticity of a message. An HMAC is a type of keyed hash function that can also be used in a key derivation scheme or a key stretching scheme.
1433:
161:
3075:
1428:
2574:
134:
2407:
2703:
1073:) is better, but various security papers have suggested vulnerabilities with this approach, even when two different keys are used.
2011:
1880:
2906:
2615:
2100:
2052:
1147:" which leads to a confusing pseudo-collision: if the key is longer than the hash block size (e.g. 64 bytes for SHA-1), then
2402:
2696:
2620:
1252:
1133:
1096:)) because the outer application of the hash function masks the intermediate result of the internal hash. The values of
138:
3022:
2977:
2790:
2389:
2031:
2027:
1978:
68:
64:
2901:
2004:
1406:
1222:"attacks on HMAC-MD5 do not seem to indicate a practical vulnerability when used as a message authentication code"
3017:
2646:
2285:
91:
3007:
2997:
2852:
2625:
2461:
2160:
2155:
173:
160:, and they also wrote RFC 2104 in 1997. The 1996 paper also defined a nested variant called NMAC (Nested MAC).
3002:
2992:
2795:
2755:
2748:
2738:
2733:
2548:
2368:
1042:
127:
87:
2743:
2656:
2042:
1665:
1505:
1456:
1288:
1195:
119:
3050:
2896:
2842:
2671:
2321:
2275:
2165:
2123:
2108:
2090:
1960:
1846:
1519:
1470:
455:
1239:
Here are some HMAC values, assuming 8-bit ASCII for the input and hexadecimal encoding for the output:
1231:
In May 2011, RFC 6234 was published detailing the abstract theory and source code for SHA-based HMACs.
1076:
No known extension attacks have been found against the current HMAC specification which is defined as
3012:
2936:
2341:
2245:
2195:
2170:
1902:
1705:
1616:
1363:
1293:
919:
block_sized_key = computeBlockSizedKey(key, hash, blockSize) o_key_pad ← block_sized_key xor
373:
2775:
2666:
2543:
2492:
2431:
2250:
2210:
2190:
1828:
1510:
1461:
1171:
1159:
1104:
are not critical to the security of the algorithm, but were defined in such a way to have a large
71:
and a secret cryptographic key. As with any MAC, it may be used to simultaneously verify both the
2881:
2865:
2812:
2600:
2584:
2533:
2118:
1573:
552:
148:
The definition and analysis of the HMAC construction was first published in 1996 in a paper by
2941:
2931:
2802:
2477:
1913:
1894:
1501:
1452:
83:
1388:
578:
3080:
2876:
2564:
2518:
2280:
1936:
1928:
1884:
1695:
1606:
1353:
1105:
2579:
2528:
2523:
2311:
1859:
1532:
1483:
1191:
1187:
1174:
showed how to distinguish HMAC with reduced versions of MD5 and SHA-1 or full versions of
635:
604:
126:
inner hash result and the outer key. Thus the algorithm provides better immunity against
1212:
In 2011 an informational RFC 6151 was published to summarize security considerations in
521:
110:, may be used in the calculation of an HMAC; the resulting MAC algorithm is termed HMAC-
2951:
2871:
2832:
2780:
2765:
2569:
2297:
499:
477:
177:
72:
1983:
1687:
Updated
Security Considerations for the MD5 Message-Digest and the HMAC-MD5 Algorithms
1586:
although it doesn't affect applications such as HMAC where collisions aren't important
3069:
3032:
2987:
2946:
2926:
2822:
2785:
2760:
2661:
2538:
2240:
1277:
1163:
668:
570:
157:
149:
79:
1314:
2982:
2827:
2817:
2807:
2770:
2719:
1497:
1448:
1202:
1167:
596:
169:
48:
1216:
and HMAC-MD5. For HMAC-MD5 the RFC summarizes that – although the security of the
1281:
2961:
2651:
2497:
2426:
2422:
2331:
1940:
1932:
1905:
1874:
1721:
1717:
1708:
1685:
1628:
1619:
1600:
1375:
1366:
1347:
153:
137:) breaks up a message into blocks of a fixed size and iterates over them with a
1759:
1226:"for a new protocol design, a ciphersuite with HMAC-MD5 should not be included"
164:
PUB 198 generalizes and standardizes the use of HMACs. HMAC is used within the
2921:
2891:
2886:
2847:
874:
33:
1898:
1734:
2911:
2326:
1973:
1807:"On the Security of HMAC and NMAC Based on HAVAL, MD4, MD5, SHA-0 and SHA-1"
1780:
1547:
2113:
661:
is the block-sized inner padding, consisting of repeated bytes valued 0x36.
630:
is the block-sized outer padding, consisting of repeated bytes valued 0x5c.
1955:
2956:
2916:
2605:
2502:
2487:
2482:
2472:
2436:
2356:
2270:
2150:
1429:"SHA-3 Standard: Permutation-Based Hash and Extendable-Output Functions"
2441:
2397:
2175:
1645:
1827:
Wang, Xiaoyun; Yu, Hongbo; Wang, Wei; Zhang, Haina; Zhan, Tao (2009).
1806:
2837:
2610:
2351:
2346:
2316:
2306:
2265:
2260:
2255:
2235:
2230:
2205:
2200:
2185:
2145:
1889:
1700:
1646:"New Proofs for NMAC and HMAC: Security without Collision-Resistance"
1611:
1358:
1112:
1805:
Jongsung, Kim; Biryukov, Alex; Preneel, Bart; Hong, Seokhie (2006).
17:
1315:"Message Authentication using Hash Functions—The HMAC Construction"
1220:
hash function itself is severely compromised – the currently known
118:
is the hash function used (e.g. HMAC-SHA256 or HMAC-SHA3-512). The
39:
2336:
2225:
2180:
2128:
2085:
2080:
2074:
1183:
1175:
1120:
839:
826:
813:
800:
787:
774:
761:
748:
735:
722:
709:
165:
107:
103:
38:
1968:
914:// The output size of the hash function (e.g. 20 bytes for SHA-1)
32:"NMAC" redirects here. For the Nissan Motor Acceptance Corp, see
2451:
2446:
2417:
2376:
1691:
1116:
959:// The block size of the hash function (e.g. 64 bytes for SHA-1)
910:// The block size of the hash function (e.g. 64 bytes for SHA-1)
689:
680:
2692:
2000:
1389:"FIPS 198-1: The Keyed-Hash Message Authentication Code (HMAC)"
2220:
2215:
2068:
1781:"RFC 2104 Errata Held for Document Update · Erdem Memisyazici"
1455:(1995). "MDx-MAC and Building Fast MACs from Hash Functions".
1217:
1213:
1179:
696:
1313:
Bellare, Mihir; Canetti, Ran; Krawczyk, Hugo (Spring 1996).
1876:
US Secure Hash
Algorithms (SHA and SHA-based HMAC and HKDF)
428:
1735:"PBKDF2+HMAC hash collisions explained · Mathias Bynens"
2858:
Cryptographically secure pseudorandom number generator
1599:
H. Krawczyk; M. Bellare; R. Canetti (February 1997).
1346:
H. Krawczyk; M. Bellare; R. Canetti (February 1997).
638:
607:
581:
555:
524:
502:
480:
458:
197:
1988:
2970:
2726:
2639:
2593:
2557:
2511:
2460:
2388:
2365:
2294:
2138:
2099:
2061:
1045:"). The alternative, appending the key using MAC =
1282:"Keying Hash Functions for Message Authentication"
653:
622:
587:
561:
543:is a block-sized key derived from the secret key,
535:
508:
486:
464:
438:
1963:The Keyed-Hash Message Authentication Code (HMAC)
1669:whose (weak) collision resistance is compromised.
1504:(1995). "On the Security of Two MAC Algorithms".
344:
238:
27:Computer communications authentication algorithm
1602:HMAC: Keyed-Hashing for Message Authentication
1349:HMAC: Keyed-Hashing for Message Authentication
133:An iterative hash function (one that uses the
2704:
2012:
337:
291:
275:
245:
8:
1829:"Cryptanalysis on HMAC/NMAC-MD5 and MD5-MAC"
932:hash(o_key_pad ∥ hash(i_key_pad ∥ message))
1918:: CS1 maint: numeric names: authors list (
1194:. HMAC with the full version of MD4 can be
2711:
2697:
2689:
2019:
2005:
1997:
1993:
1989:
1679:
1677:
1888:
1873:Eastlake 3rd, D.; Hansen, T. (May 2011).
1699:
1610:
1509:
1460:
1357:
1341:
1339:
1337:
1335:
1292:
1139:RFC 2104 requires that "keys longer than
637:
606:
580:
554:
523:
501:
479:
457:
420:
406:
395:
368:
343:
342:
336:
335:
290:
289:
274:
273:
244:
243:
237:
236:
198:
196:
102:Any cryptographic hash function, such as
1434:Federal Information Processing Standards
1393:Federal Information Processing Standards
955:// The hash function to use (e.g. SHA-1)
906:// The hash function to use (e.g. SHA-1)
664:
188:This definition is taken from RFC 2104:
78:HMAC can provide authentication using a
1280:; Canetti, Ran; Krawczyk, Hugo (1996).
1272:
1270:
1268:
1264:
90:. It trades off the need for a complex
1911:
1855:
1844:
1528:
1517:
1479:
1468:
61:hash-based message authentication code
57:keyed-hash message authentication code
7:
1760:"Aaron Toponce : Breaking HMAC"
1308:
1306:
1304:
1115:hash function, that was selected by
1956:Online HMAC Generator / Tester Tool
1548:"Keccak Team – Design and security"
923:i_key_pad ← block_sized_key xor
494:is the message to be authenticated.
989:by padding with zeros on the right
465:{\displaystyle \operatorname {H} }
459:
376:
283:
230:
25:
1684:S. Turner; L. Chen (March 2011).
1664:This paper proves that HMAC is a
1427:Dworkin, Morris (4 August 2015).
1407:"FIPS 180-2 with Change Notice 1"
1009:// Pad key with zeros to make it
472:is a cryptographic hash function.
3046:
3045:
1881:Internet Engineering Task Force
1572:Schneier, Bruce (August 2005).
408: is larger than block size
2907:Information-theoretic security
2616:NIST hash function competition
1437:– via NIST Publications.
917:// Compute the block sized key
902:// Array of bytes to be hashed
220:
208:
55:(sometimes expanded as either
1:
1143:bytes are first hashed using
996:(length(key) < blockSize)
973:(length(key) > blockSize)
966:are shortened by hashing them
861:b = H's internal block length
3076:Message authentication codes
2621:Password Hashing Competition
2032:message authentication codes
2028:Cryptographic hash functions
1627:sec. 6. Updated by RFC
1253:HMAC-based one-time password
3023:Message authentication code
2978:Cryptographic hash function
2791:Cryptographic hash function
2575:Merkle–Damgård construction
135:Merkle–Damgård construction
69:cryptographic hash function
65:message authentication code
3097:
2902:Harvest now, decrypt later
1974:Python HMAC implementation
1724:.
1378:.
562:{\displaystyle \parallel }
31:
3041:
3018:Post-quantum cryptography
2688:
2038:
1996:
1992:
1605:. Network Working Group.
1352:. Network Working Group.
851:
92:public key infrastructure
3008:Quantum key distribution
2998:Authenticated encryption
2853:Random number generation
2369:key derivation functions
1984:Rust HMAC implementation
1224:, but it also adds that
128:length extension attacks
63:) is a specific type of
3003:Public-key cryptography
2993:Symmetric-key algorithm
2796:Key derivation function
2756:Cryptographic primitive
2749:Authentication protocol
2739:Outline of cryptography
2734:History of cryptography
2647:Hash-based cryptography
2549:Length extension attack
1192:second-preimage attacks
1043:length-extension attack
588:{\displaystyle \oplus }
88:asymmetric cryptography
2744:Cryptographic protocol
2657:Message authentication
1854:Cite journal requires
1527:Cite journal requires
1478:Cite journal requires
1134:pseudo-random function
655:
624:
589:
563:
537:
510:
488:
466:
440:
120:cryptographic strength
44:
2897:End-to-end encryption
2843:Cryptojacking malware
1969:C HMAC implementation
1653:Journal of Cryptology
1502:van Oorschot, Paul C.
1453:van Oorschot, Paul C.
981:// Keys shorter than
957:blockSize: Integer
953:hash: Function
949:key: Bytes
938:computeBlockSizedKey
912:outputSize: Integer
908:blockSize: Integer
904:hash: Function
900:message: Bytes
896:key: Bytes
656:
625:
590:
564:
538:
511:
489:
467:
441:
42:
3013:Quantum cryptography
2937:Trusted timestamping
1374:Updated by RFC
1007:Pad(key, blockSize)
979:key = hash(key)
962:// Keys longer than
654:{\displaystyle ipad}
636:
623:{\displaystyle opad}
605:
579:
553:
522:
500:
478:
456:
195:
139:compression function
43:HMAC-SHA1 generation
2776:Cryptographic nonce
2544:Side-channel attack
1979:Java implementation
925:// Inner padded key
921:// Outer padded key
2882:Subliminal channel
2866:Pseudorandom noise
2813:Key (cryptography)
2601:CAESAR Competition
2585:HAIFA construction
2534:Brute-force attack
1816:. Springer-Verlag.
1785:www.rfc-editor.org
651:
620:
585:
559:
536:{\displaystyle K'}
533:
516:is the secret key.
506:
484:
462:
436:
434:
427:
176:protocols and for
84:digital signatures
67:(MAC) involving a
45:
3063:
3062:
3059:
3058:
2942:Key-based routing
2932:Trapdoor function
2803:Digital signature
2684:
2683:
2680:
2679:
2478:ChaCha20-Poly1305
2295:Password hashing/
1716:Updates RFC
1287:. pp. 1–15.
1024:Design principles
951:// Array of bytes
898:// Array of bytes
866:
865:
509:{\displaystyle K}
487:{\displaystyle m}
423:
409:
402:
398:
82:instead of using
16:(Redirected from
3088:
3049:
3048:
2877:Insecure channel
2713:
2706:
2699:
2690:
2565:Avalanche effect
2519:Collision attack
2062:Common functions
2021:
2014:
2007:
1998:
1994:
1990:
1961:FIPS PUB 198-1,
1943:
1923:
1917:
1909:
1892:
1890:10.17487/RFC6234
1870:
1864:
1863:
1857:
1852:
1850:
1842:
1840:
1838:
1833:
1824:
1818:
1817:
1811:
1802:
1796:
1795:
1793:
1791:
1777:
1771:
1770:
1768:
1766:
1756:
1750:
1749:
1747:
1745:
1739:mathiasbynens.be
1731:
1725:
1712:
1703:
1701:10.17487/RFC6151
1681:
1672:
1671:
1661:
1659:
1650:
1644:Bellare, Mihir.
1641:
1635:
1623:
1614:
1612:10.17487/RFC2104
1596:
1590:
1589:
1582:
1580:
1569:
1563:
1562:
1556:
1554:
1543:
1537:
1536:
1530:
1525:
1523:
1515:
1513:
1494:
1488:
1487:
1481:
1476:
1474:
1466:
1464:
1445:
1439:
1438:
1424:
1418:
1417:
1411:
1403:
1397:
1396:
1385:
1379:
1370:
1361:
1359:10.17487/RFC2104
1343:
1330:
1329:
1319:
1310:
1299:
1298:
1296:
1286:
1274:
1154:
1150:
1106:Hamming distance
1018:
1014:
1005:
1000:
994:
990:
977:
971:
967:
960:
956:
952:
947:
942:
936:
930:
926:
922:
918:
915:
911:
907:
903:
899:
894:
889:
883:
862:
858:
854:
687:
678:
673:
665:
660:
658:
657:
652:
629:
627:
626:
621:
595:denotes bitwise
594:
592:
591:
586:
568:
566:
565:
560:
542:
540:
539:
534:
532:
515:
513:
512:
507:
493:
491:
490:
485:
471:
469:
468:
463:
445:
443:
442:
437:
435:
431:
430:
424:
421:
410:
407:
400:
399:
396:
392:
360:
348:
347:
341:
340:
328:
324:
308:
295:
294:
279:
278:
257:
249:
248:
242:
241:
21:
3096:
3095:
3091:
3090:
3089:
3087:
3086:
3085:
3066:
3065:
3064:
3055:
3037:
2966:
2722:
2717:
2676:
2635:
2594:Standardization
2589:
2580:Sponge function
2553:
2529:Birthday attack
2524:Preimage attack
2507:
2463:
2456:
2384:
2367:
2366:General purpose
2361:
2296:
2290:
2139:Other functions
2134:
2101:SHA-3 finalists
2095:
2057:
2034:
2025:
1952:
1947:
1946:
1910:
1872:
1871:
1867:
1853:
1843:
1836:
1834:
1831:
1826:
1825:
1821:
1809:
1804:
1803:
1799:
1789:
1787:
1779:
1778:
1774:
1764:
1762:
1758:
1757:
1753:
1743:
1741:
1733:
1732:
1728:
1683:
1682:
1675:
1657:
1655:
1648:
1643:
1642:
1638:
1598:
1597:
1593:
1578:
1576:
1571:
1570:
1566:
1552:
1550:
1545:
1544:
1540:
1526:
1516:
1496:
1495:
1491:
1477:
1467:
1447:
1446:
1442:
1426:
1425:
1421:
1409:
1405:
1404:
1400:
1395:. 16 July 2008.
1387:
1386:
1382:
1345:
1344:
1333:
1317:
1312:
1311:
1302:
1294:10.1.1.134.8430
1284:
1276:
1275:
1266:
1261:
1249:
1244:
1237:
1188:random function
1152:
1151:is computed as
1148:
1129:
1026:
1021:
1016:
1008:
1003:
998:
992:
980:
975:
969:
961:
958:
954:
950:
945:
940:
934:
928:
924:
920:
916:
913:
909:
905:
901:
897:
892:
887:
881:
871:
860:
859:
857:L = length(out)
856:
855:
852:
685:
676:
671:
634:
633:
603:
602:
577:
576:
551:
550:
525:
520:
519:
498:
497:
476:
475:
454:
453:
433:
432:
426:
425:
418:
412:
411:
393:
382:
369:
361:
353:
350:
349:
301:
300:
296:
250:
223:
193:
192:
186:
178:JSON Web Tokens
100:
37:
28:
23:
22:
15:
12:
11:
5:
3094:
3092:
3084:
3083:
3078:
3068:
3067:
3061:
3060:
3057:
3056:
3054:
3053:
3042:
3039:
3038:
3036:
3035:
3030:
3028:Random numbers
3025:
3020:
3015:
3010:
3005:
3000:
2995:
2990:
2985:
2980:
2974:
2972:
2968:
2967:
2965:
2964:
2959:
2954:
2952:Garlic routing
2949:
2944:
2939:
2934:
2929:
2924:
2919:
2914:
2909:
2904:
2899:
2894:
2889:
2884:
2879:
2874:
2872:Secure channel
2869:
2863:
2862:
2861:
2850:
2845:
2840:
2835:
2833:Key stretching
2830:
2825:
2820:
2815:
2810:
2805:
2800:
2799:
2798:
2793:
2783:
2781:Cryptovirology
2778:
2773:
2768:
2766:Cryptocurrency
2763:
2758:
2753:
2752:
2751:
2741:
2736:
2730:
2728:
2724:
2723:
2718:
2716:
2715:
2708:
2701:
2693:
2686:
2685:
2682:
2681:
2678:
2677:
2675:
2674:
2669:
2664:
2659:
2654:
2649:
2643:
2641:
2637:
2636:
2634:
2633:
2628:
2623:
2618:
2613:
2608:
2603:
2597:
2595:
2591:
2590:
2588:
2587:
2582:
2577:
2572:
2570:Hash collision
2567:
2561:
2559:
2555:
2554:
2552:
2551:
2546:
2541:
2536:
2531:
2526:
2521:
2515:
2513:
2509:
2508:
2506:
2505:
2500:
2495:
2490:
2485:
2480:
2475:
2469:
2467:
2458:
2457:
2455:
2454:
2449:
2444:
2439:
2434:
2429:
2420:
2415:
2410:
2405:
2400:
2394:
2392:
2386:
2385:
2383:
2382:
2379:
2373:
2371:
2363:
2362:
2360:
2359:
2354:
2349:
2344:
2339:
2334:
2329:
2324:
2319:
2314:
2309:
2303:
2301:
2298:key stretching
2292:
2291:
2289:
2288:
2283:
2278:
2273:
2268:
2263:
2258:
2253:
2248:
2243:
2238:
2233:
2228:
2223:
2218:
2213:
2208:
2203:
2198:
2193:
2188:
2183:
2178:
2173:
2168:
2163:
2158:
2153:
2148:
2142:
2140:
2136:
2135:
2133:
2132:
2126:
2121:
2116:
2111:
2105:
2103:
2097:
2096:
2094:
2093:
2088:
2083:
2078:
2072:
2065:
2063:
2059:
2058:
2056:
2055:
2050:
2045:
2039:
2036:
2035:
2026:
2024:
2023:
2016:
2009:
2001:
1987:
1986:
1981:
1976:
1971:
1966:
1958:
1951:
1950:External links
1948:
1945:
1944:
1925:Informational.
1865:
1856:|journal=
1819:
1797:
1772:
1751:
1726:
1714:Informational.
1673:
1636:
1625:Informational.
1591:
1574:"SHA-1 Broken"
1564:
1538:
1529:|journal=
1511:10.1.1.42.8908
1489:
1480:|journal=
1462:10.1.1.34.3855
1440:
1419:
1398:
1380:
1372:Informational.
1331:
1300:
1278:Bellare, Mihir
1263:
1262:
1260:
1257:
1256:
1255:
1248:
1245:
1241:
1236:
1233:
1128:
1125:
1025:
1022:
985:are padded to
879:
873:The following
870:
869:Implementation
867:
864:
863:
849:
848:
845:
842:
836:
835:
832:
829:
823:
822:
819:
816:
810:
809:
806:
803:
797:
796:
793:
790:
784:
783:
780:
777:
771:
770:
767:
764:
758:
757:
754:
751:
745:
744:
741:
738:
732:
731:
728:
725:
719:
718:
715:
712:
706:
705:
702:
699:
693:
692:
683:
674:
663:
662:
650:
647:
644:
641:
631:
619:
616:
613:
610:
600:
584:
574:
558:
548:
531:
528:
517:
505:
495:
483:
473:
461:
447:
446:
429:
419:
417:
414:
413:
405:
394:
391:
388:
385:
381:
378:
375:
374:
372:
367:
364:
362:
359:
356:
352:
351:
346:
339:
334:
331:
327:
323:
320:
317:
314:
311:
307:
304:
299:
293:
288:
285:
282:
277:
272:
269:
266:
263:
260:
256:
253:
247:
240:
235:
232:
229:
226:
224:
222:
219:
216:
213:
210:
207:
204:
201:
200:
185:
182:
99:
96:
73:data integrity
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
3093:
3082:
3079:
3077:
3074:
3073:
3071:
3052:
3044:
3043:
3040:
3034:
3033:Steganography
3031:
3029:
3026:
3024:
3021:
3019:
3016:
3014:
3011:
3009:
3006:
3004:
3001:
2999:
2996:
2994:
2991:
2989:
2988:Stream cipher
2986:
2984:
2981:
2979:
2976:
2975:
2973:
2969:
2963:
2960:
2958:
2955:
2953:
2950:
2948:
2947:Onion routing
2945:
2943:
2940:
2938:
2935:
2933:
2930:
2928:
2927:Shared secret
2925:
2923:
2920:
2918:
2915:
2913:
2910:
2908:
2905:
2903:
2900:
2898:
2895:
2893:
2890:
2888:
2885:
2883:
2880:
2878:
2875:
2873:
2870:
2867:
2864:
2859:
2856:
2855:
2854:
2851:
2849:
2846:
2844:
2841:
2839:
2836:
2834:
2831:
2829:
2826:
2824:
2823:Key generator
2821:
2819:
2816:
2814:
2811:
2809:
2806:
2804:
2801:
2797:
2794:
2792:
2789:
2788:
2787:
2786:Hash function
2784:
2782:
2779:
2777:
2774:
2772:
2769:
2767:
2764:
2762:
2761:Cryptanalysis
2759:
2757:
2754:
2750:
2747:
2746:
2745:
2742:
2740:
2737:
2735:
2732:
2731:
2729:
2725:
2721:
2714:
2709:
2707:
2702:
2700:
2695:
2694:
2691:
2687:
2673:
2670:
2668:
2665:
2663:
2662:Proof of work
2660:
2658:
2655:
2653:
2650:
2648:
2645:
2644:
2642:
2638:
2632:
2629:
2627:
2624:
2622:
2619:
2617:
2614:
2612:
2609:
2607:
2604:
2602:
2599:
2598:
2596:
2592:
2586:
2583:
2581:
2578:
2576:
2573:
2571:
2568:
2566:
2563:
2562:
2560:
2556:
2550:
2547:
2545:
2542:
2540:
2539:Rainbow table
2537:
2535:
2532:
2530:
2527:
2525:
2522:
2520:
2517:
2516:
2514:
2510:
2504:
2501:
2499:
2496:
2494:
2491:
2489:
2486:
2484:
2481:
2479:
2476:
2474:
2471:
2470:
2468:
2465:
2462:Authenticated
2459:
2453:
2450:
2448:
2445:
2443:
2440:
2438:
2435:
2433:
2430:
2428:
2424:
2421:
2419:
2416:
2414:
2411:
2409:
2406:
2404:
2401:
2399:
2396:
2395:
2393:
2391:
2390:MAC functions
2387:
2380:
2378:
2375:
2374:
2372:
2370:
2364:
2358:
2355:
2353:
2350:
2348:
2345:
2343:
2340:
2338:
2335:
2333:
2330:
2328:
2325:
2323:
2320:
2318:
2315:
2313:
2310:
2308:
2305:
2304:
2302:
2299:
2293:
2287:
2284:
2282:
2279:
2277:
2274:
2272:
2269:
2267:
2264:
2262:
2259:
2257:
2254:
2252:
2249:
2247:
2244:
2242:
2239:
2237:
2234:
2232:
2229:
2227:
2224:
2222:
2219:
2217:
2214:
2212:
2209:
2207:
2204:
2202:
2199:
2197:
2194:
2192:
2189:
2187:
2184:
2182:
2179:
2177:
2174:
2172:
2169:
2167:
2164:
2162:
2159:
2157:
2154:
2152:
2149:
2147:
2144:
2143:
2141:
2137:
2130:
2127:
2125:
2122:
2120:
2117:
2115:
2112:
2110:
2107:
2106:
2104:
2102:
2098:
2092:
2089:
2087:
2084:
2082:
2079:
2077:(compromised)
2076:
2073:
2071:(compromised)
2070:
2067:
2066:
2064:
2060:
2054:
2053:Known attacks
2051:
2049:
2046:
2044:
2041:
2040:
2037:
2033:
2029:
2022:
2017:
2015:
2010:
2008:
2003:
2002:
1999:
1995:
1991:
1985:
1982:
1980:
1977:
1975:
1972:
1970:
1967:
1965:
1964:
1959:
1957:
1954:
1953:
1949:
1942:
1938:
1934:
1930:
1926:
1921:
1915:
1907:
1904:
1900:
1896:
1891:
1886:
1882:
1878:
1877:
1869:
1866:
1861:
1848:
1830:
1823:
1820:
1815:
1808:
1801:
1798:
1786:
1782:
1776:
1773:
1761:
1755:
1752:
1740:
1736:
1730:
1727:
1723:
1719:
1715:
1710:
1707:
1702:
1697:
1693:
1689:
1688:
1680:
1678:
1674:
1670:
1667:
1654:
1647:
1640:
1637:
1634:
1630:
1626:
1621:
1618:
1613:
1608:
1604:
1603:
1595:
1592:
1588:
1587:
1575:
1568:
1565:
1561:
1549:
1546:Keccak team.
1542:
1539:
1534:
1521:
1512:
1507:
1503:
1499:
1498:Preneel, Bart
1493:
1490:
1485:
1472:
1463:
1458:
1454:
1450:
1449:Preneel, Bart
1444:
1441:
1436:
1435:
1430:
1423:
1420:
1415:
1414:csrc.nist.gov
1408:
1402:
1399:
1394:
1390:
1384:
1381:
1377:
1373:
1368:
1365:
1360:
1355:
1351:
1350:
1342:
1340:
1338:
1336:
1332:
1327:
1323:
1316:
1309:
1307:
1305:
1301:
1295:
1290:
1283:
1279:
1273:
1271:
1269:
1265:
1258:
1254:
1251:
1250:
1246:
1240:
1234:
1232:
1229:
1227:
1223:
1219:
1215:
1210:
1207:
1204:
1199:
1197:
1193:
1189:
1185:
1181:
1177:
1173:
1169:
1165:
1164:Alex Biryukov
1161:
1156:
1153:HMAC(H(k), m)
1146:
1142:
1137:
1135:
1126:
1124:
1122:
1118:
1114:
1109:
1107:
1103:
1099:
1095:
1091:
1087:
1083:
1079:
1074:
1072:
1068:
1064:
1060:
1056:
1052:
1048:
1044:
1040:
1036:
1032:
1023:
1019:
1012:
1006:
1001:
995:
988:
984:
978:
972:
965:
948:
943:
937:
931:
895:
890:
884:
878:
876:
868:
850:
846:
843:
841:
838:
837:
833:
830:
828:
825:
824:
820:
817:
815:
812:
811:
807:
804:
802:
799:
798:
794:
791:
789:
786:
785:
781:
778:
776:
773:
772:
768:
765:
763:
760:
759:
755:
752:
750:
747:
746:
742:
739:
737:
734:
733:
729:
726:
724:
721:
720:
716:
713:
711:
708:
707:
703:
700:
698:
695:
694:
691:
684:
682:
675:
670:
669:Hash function
667:
666:
648:
645:
642:
639:
632:
617:
614:
611:
608:
601:
598:
582:
575:
572:
571:concatenation
556:
549:
546:
529:
526:
518:
503:
496:
481:
474:
452:
451:
450:
415:
403:
389:
386:
383:
379:
370:
365:
363:
357:
354:
332:
329:
325:
321:
318:
315:
312:
309:
305:
302:
297:
286:
280:
270:
267:
264:
261:
258:
254:
251:
233:
227:
225:
217:
214:
211:
205:
202:
191:
190:
189:
183:
181:
179:
175:
171:
167:
163:
159:
158:Hugo Krawczyk
155:
151:
150:Mihir Bellare
146:
142:
140:
136:
131:
129:
123:
121:
117:
113:
109:
105:
97:
95:
93:
89:
85:
81:
80:shared secret
76:
74:
70:
66:
62:
58:
54:
50:
41:
35:
30:
19:
2983:Block cipher
2828:Key schedule
2818:Key exchange
2808:Kleptography
2771:Cryptosystem
2720:Cryptography
2412:
1962:
1924:
1875:
1868:
1847:cite journal
1835:. Retrieved
1822:
1813:
1800:
1790:23 September
1788:. Retrieved
1784:
1775:
1763:. Retrieved
1754:
1742:. Retrieved
1738:
1729:
1713:
1686:
1663:
1656:. Retrieved
1652:
1639:
1632:
1624:
1601:
1594:
1585:
1584:
1577:. Retrieved
1567:
1558:
1551:. Retrieved
1541:
1520:cite journal
1492:
1471:cite journal
1443:
1432:
1422:
1413:
1401:
1392:
1383:
1371:
1348:
1325:
1321:
1238:
1230:
1225:
1221:
1211:
1205:
1203:Xiaoyun Wang
1200:
1172:Seokhie Hong
1168:Bart Preneel
1160:Jongsung Kim
1157:
1144:
1140:
1138:
1130:
1110:
1101:
1097:
1093:
1089:
1085:
1081:
1077:
1075:
1070:
1066:
1062:
1058:
1054:
1050:
1046:
1038:
1034:
1030:
1027:
1015:
1010:
1002:
997:
991:
986:
982:
974:
968:
963:
944:
939:
933:
927:
891:
886:
880:
872:
597:exclusive or
544:
448:
187:
147:
143:
132:
124:
115:
111:
101:
77:
60:
56:
52:
49:cryptography
46:
29:
2971:Mathematics
2962:Mix network
2652:Merkle tree
2640:Utilization
2626:NSA Suite B
1658:15 December
1322:CryptoBytes
853:out = H(in)
762:SHA-512/256
749:SHA-512/224
154:Ran Canetti
3070:Categories
2922:Ciphertext
2892:Decryption
2887:Encryption
2848:Ransomware
2464:encryption
2241:RadioGatún
2048:Comparison
1935:. Updates
1927:Obsoletes
1553:31 October
1259:References
1149:HMAC(k, m)
1013:bytes long
875:pseudocode
184:Definition
34:Nissan USA
2912:Plaintext
2381:KDF1/KDF2
2300:functions
2286:Whirlpool
1899:2070-1721
1579:9 January
1506:CiteSeerX
1457:CiteSeerX
1289:CiteSeerX
1201:In 2009,
1158:In 2006,
1011:blockSize
987:blockSize
983:blockSize
964:blockSize
583:⊕
557:∥
422:otherwise
380:
330:∥
310:⊕
287:
281:∥
259:⊕
234:
206:
3051:Category
2957:Kademlia
2917:Codetext
2860:(CSPRNG)
2606:CRYPTREC
2437:Poly1305
2357:yescrypt
2271:Streebog
2151:CubeHash
2131:(winner)
1914:citation
1814:SCN 2006
1765:7 August
1744:7 August
1247:See also
1235:Examples
1127:Security
935:function
882:function
840:SHA3-512
827:SHA3-384
814:SHA3-256
801:SHA3-224
569:denotes
530:′
358:′
306:′
255:′
114:, where
3081:Hashing
2727:General
2512:Attacks
2442:SipHash
2398:CBC-MAC
2332:LM hash
2312:Balloon
2176:HAS-160
1837:15 June
1186:from a
1119:as the
1094:message
1067:message
1051:message
1039:message
788:SHA-512
775:SHA-384
736:SHA-256
723:SHA-224
98:Details
2838:Keygen
2672:Pepper
2611:NESSIE
2558:Design
2352:scrypt
2347:PBKDF2
2322:Catena
2317:bcrypt
2307:Argon2
2266:Snefru
2261:Shabal
2256:SWIFFT
2236:RIPEMD
2231:N-hash
2206:MASH-2
2201:MASH-1
2186:Kupyna
2146:BLAKE3
2129:Keccak
2114:Grøstl
2091:BLAKE2
1939:
1931:
1897:
1508:
1459:
1291:
1206:et al.
1196:forged
1182:, and
1170:, and
1113:Keccak
1017:return
1004:return
946:input:
929:return
893:input:
599:(XOR).
449:where
401:
156:, and
2868:(PRN)
2466:modes
2342:Makwa
2337:Lyra2
2327:crypt
2276:Tiger
2226:MDC-2
2181:HAVAL
2166:Fugue
2124:Skein
2109:BLAKE
2086:SHA-3
2081:SHA-2
2075:SHA-1
1832:(PDF)
1810:(PDF)
1649:(PDF)
1410:(PDF)
1318:(PDF)
1285:(PDF)
1184:SHA-0
1176:HAVAL
1121:SHA-3
885:hmac
710:SHA-1
690:bytes
681:bytes
166:IPsec
108:SHA-3
104:SHA-2
86:with
51:, an
2667:Salt
2631:CNSA
2498:IAPM
2452:VMAC
2447:UMAC
2432:PMAC
2427:CMAC
2423:OMAC
2418:NMAC
2413:HMAC
2408:GMAC
2377:HKDF
2246:SIMD
2196:Lane
2171:GOST
2156:ECOH
2043:List
2030:and
1941:3174
1933:4634
1920:link
1906:6234
1895:ISSN
1860:help
1839:2015
1792:2016
1767:2019
1746:2019
1722:1321
1720:and
1718:2104
1709:6151
1692:IETF
1660:2021
1629:6151
1620:2104
1581:2009
1560:key.
1555:2019
1533:help
1484:help
1376:6151
1367:2104
1328:(1).
1117:NIST
1111:The
1102:opad
1100:and
1098:ipad
1020:key
999:then
976:then
203:HMAC
172:and
162:FIPS
53:HMAC
18:NMAC
2503:OCB
2493:GCM
2488:EAX
2483:CWC
2473:CCM
2403:DAA
2281:VSH
2251:SM3
2221:MD6
2216:MD4
2211:MD2
2191:LSH
2161:FSB
2069:MD5
1937:RFC
1929:RFC
1903:RFC
1885:doi
1706:RFC
1696:doi
1666:PRF
1617:RFC
1607:doi
1364:RFC
1354:doi
1218:MD5
1214:MD5
1180:MD4
1090:key
1082:key
1071:key
1063:key
1055:key
1035:key
847:64
834:48
831:104
821:32
818:136
808:28
805:144
795:64
792:128
782:48
779:128
769:32
766:128
756:28
753:128
743:32
730:28
717:20
704:16
697:MD5
174:TLS
170:SSH
106:or
59:or
47:In
3072::
2119:JH
1916:}}
1912:{{
1901:.
1893:.
1883:.
1879:.
1851::
1849:}}
1845:{{
1812:.
1783:.
1737:.
1704:.
1694:.
1690:.
1676:^
1662:.
1651:.
1631:.
1615:.
1583:.
1557:.
1524::
1522:}}
1518:{{
1500:;
1475::
1473:}}
1469:{{
1451:;
1431:.
1412:.
1391:.
1362:.
1334:^
1324:.
1320:.
1303:^
1267:^
1228:.
1178:,
1166:,
1162:,
1092:∥
1084:∥
1069:∥
1065:∥
1053:∥
1037:∥
993:if
970:if
941:is
888:is
844:72
740:64
727:64
714:64
701:64
688:,
679:,
397:if
180:.
168:,
152:,
130:.
2712:e
2705:t
2698:v
2425:/
2020:e
2013:t
2006:v
1922:)
1908:.
1887::
1862:)
1858:(
1841:.
1794:.
1769:.
1748:.
1711:.
1698::
1622:.
1609::
1535:)
1531:(
1514:.
1486:)
1482:(
1465:.
1416:.
1369:.
1356::
1326:2
1297:.
1145:H
1141:B
1088:(
1086:H
1080:(
1078:H
1061:(
1059:H
1049:(
1047:H
1033:(
1031:H
686:L
677:b
672:H
649:d
646:a
643:p
640:i
618:d
615:a
612:p
609:o
573:.
545:K
527:K
504:K
482:m
460:H
416:K
404:K
390:)
387:K
384:(
377:H
371:{
366:=
355:K
345:)
338:)
333:m
326:)
322:d
319:a
316:p
313:i
303:K
298:(
292:(
284:H
276:)
271:d
268:a
265:p
262:o
252:K
246:(
239:(
231:H
228:=
221:)
218:m
215:,
212:K
209:(
116:x
112:x
36:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.