676:'s RAPT implementation is PAT or NAT overloading and maps multiple private IP addresses to a single public IP address. Multiple addresses can be mapped to a single address because each private address is tracked by a port number. PAT uses unique source port numbers on the inside global IP address to distinguish between translations. PAT attempts to preserve the original source port. If this source port is already used, PAT assigns the first available port number starting from the beginning of the appropriate port group 0–511, 512–1023, or 1024–65535. When there are no more ports available and there is more than one external IP address configured, PAT moves to the next IP address to try to allocate the original source port again. This process continues until it runs out of available ports and external IP addresses.
617:
inserting this port number in the source port field. The packet is then forwarded to the external network. The NAT device then makes an entry in a translation table containing the internal IP address, original source port, and the translated source port. Subsequent packets from the same internal source IP address and port number are translated to the same external source IP address and port number. The computer receiving a packet that has undergone NAT establishes a connection to the port and IP address specified in the altered packet, oblivious to the fact that the supplied address is being translated.
136:
383:
558:
354:
981:
33:
408:
318:
1228:(ALG) software or hardware may correct these problems. An ALG software module running on a NAT firewall device updates any payload data made invalid by address translation. ALGs need to understand the higher-layer protocol that they need to fix, and so each protocol with this problem requires a separate ALG. For example, on many Linux systems, there are kernel modules called
1328:, it is highly desirable not to translate UDP source port numbers of outgoing DNS requests from a DNS server behind a firewall that implements NAT. The recommended workaround for the DNS vulnerability is to make all caching DNS servers use randomized UDP source ports. If the NAT function de-randomizes the UDP source ports, the DNS server becomes vulnerable.
1199:(SIP), send explicit network addresses within their application data. File Transfer Protocol in active mode, for example, uses separate connections for control traffic (commands) and for data traffic (file contents). When requesting a file transfer, the host making the request identifies the corresponding data connection by its
824:
IP packets have a checksum in each packet header, which provides error detection only for the header. IP datagrams may become fragmented and it is necessary for a NAT to reassemble these fragments to allow correct recalculation of higher-level checksums and correct tracking of which packets belong to
620:
Upon receiving a packet from the external network, the NAT device searches the translation table based on the destination port in the packet header. If a match is found, the destination IP address and port number is replaced with the values found in the table and the packet is forwarded to the inside
590:
Private IP addresses as described in RFC 1918 are usable only on private networks not directly connected to the internet. Ports are endpoints of communication unique to that host, so a connection through the NAT device is maintained by the combined mapping of port and IP address. A private address on
832:
that contains the source and destination IP addresses of the packet carrying the TCP or UDP header. For an originating NAT to pass TCP or UDP successfully, it must recompute the TCP or UDP header checksum based on the translated IP addresses, not the original ones, and put that checksum into the TCP
418:
Many NAT implementations combine these types, so it is better to refer to specific individual NAT behavior instead of using the Cone/Symmetric terminology. RFC 4787 attempts to alleviate confusion by introducing standardized terminology for observed behaviors. For the first bullet in each row of the
251:
Network address and port translation may be implemented in several ways. Some applications that use IP address information may need to determine the external address of a network address translator. This is the address that its communication peers in the external network detect. Furthermore, it may
1547:
As the NAT router allocates an individual port for each outgoing connection, a huge number of outgoing connections may saturate the range of available ports. As ports typically get freed when the connection doesn't produce any more traffic for a certain time, the maximum number of active connection
1286:
are located behind a NAT. Phones that encrypt their signaling with IPsec encapsulate the port information within an encrypted packet, meaning that NAT devices cannot access and translate the port. In these cases, the NAT devices revert to simple NAT operations. This means that all traffic returning
616:
When a computer on the private (internal) network sends an IP packet to the external network, the NAT device replaces the internal source IP address in the packet header with the external IP address of the NAT device. PAT may then assign the connection a port number from a pool of available ports,
473:
Section 4.1 of the RFC covers NAT mapping and specifies how an external IP address and port number should be translated into an internal IP address and port number. It defines
Endpoint-Independent Mapping, Address-Dependent Mapping and Address and Port-Dependent Mapping, explains that these three
1178:
The large addressing space of IPv6 can still be defeated depending on the actual prefix length given by the carrier. It is not uncommon to be handed a /64 prefix – the smallest recommended subnet – for an entire home network, requiring a variety of techniques to be used to manually subdivide the
82:
As network address translation modifies the IP address information in packets, NAT implementations may vary in their specific behavior in various addressing cases and their effect on network traffic. The specifics of NAT behavior are not commonly documented by vendors of equipment containing NAT
633:
Network address translation can be used to mitigate IP address overlap. Address overlap occurs when hosts in different networks with the same IP address space try to reach the same destination host. This is most often a misconfiguration and may result from the merger of two networks or subnets,
599:
A NAT device is similar to a phone system at an office that has one public telephone number and multiple extensions. Outbound phone calls made from the office all appear to come from the same telephone number. However, an incoming call that does not specify an extension cannot be automatically
517:
design for TCP. For a given outgoing TCP communication, the same port numbers are used on both sides of the NAT. NAT port preservation for outgoing TCP connections is crucial for TCP NAT traversal because, under TCP, one port can only be used for one communication at a time. Programs that bind
174:
All IP packets have a source IP address and a destination IP address. Typically, packets passing from the private network to the public network will have their source address modified, while packets passing from the public network back to the private network will have their destination address
776:
request for a web page with many embedded objects. This problem can be mitigated by tracking the destination IP address in addition to the port thus sharing a single local port with many remote hosts. This additional tracking increases implementation complexity and computing resources at the
477:
Section 5 of the RFC covers NAT filtering and describes what criteria are used by the NAT to filter packets originating from specific external endpoints. The options are
Endpoint-Independent Filtering, Address-Dependent Filtering and Address and Port-Dependent Filtering. Endpoint-Independent
397:
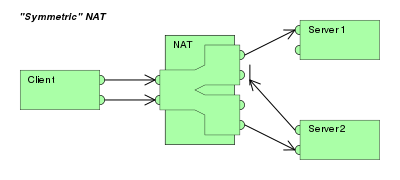
The combination of one internal IP address plus a destination IP address and port is mapped to a single unique external source IP address and port; if the same internal host sends a packet even with the same source address and port but to a different destination, a different mapping is
1106:
is the address of its WAN interface, and treats the packet as if coming from that interface. It determines the destination for that packet, based on DNAT (port forwarding) rules for the destination. If the data were sent to port 80 and a DNAT rule exists for port 80 directed to
1274:
Most client–server protocols (FTP being the main exception), however, do not send layer 3 contact information and do not require any special treatment by NATs. In fact, avoiding NAT complications is practically a requirement when designing new higher-layer protocols today.
1557:
The port numbers are 16-bit integers. The total number of internal addresses that can be translated to one external address could theoretically be as high as 65,536 per IP address. Realistically, the number of ports that can be assigned a single IP address is around
165:
As traffic passes from the network to the
Internet, the router translates the source address in each packet from a private address to the router's own public address. The router tracks basic data about each active connection (particularly the destination address and
279:, and proposed a methodology for testing a device accordingly. However, these procedures have since been deprecated from standards status, as the methods are inadequate to correctly assess many devices. RFC 5389 standardized new methods in 2008 and the acronym
638:
addressing. The destination host experiences traffic apparently arriving from the same network, and intermediate routers have no way to determine where reply traffic should be sent to. The solution is either renumbering to eliminate overlap or network address
235:
within the private network would be able to browse websites that are outside the network, whereas web browsers outside the network would be unable to browse a website hosted within. Protocols not based on TCP and UDP require other translation techniques.
536:
However, if two internal hosts attempt to communicate with the same external host using the same port number, the NAT may attempt to use a different external IP address for the second connection or may need to forgo port preservation and remap the port.
1537:
The more common arrangement is having computers that require end-to-end connectivity supplied with a routable IP address, while having others that do not provide services to outside users behind NAT with only a few IP addresses used to enable
Internet
532:
Furthermore, port preservation in NAT for TCP allows P2P protocols to offer less complexity and less latency because there is no need to use a third party (like STUN) to discover the NAT port since the application itself already knows the NAT port.
1255:
is simpler, more widely understood, and more compatible with legacy NATs. In either case, the high-level protocol must be designed with NAT traversal in mind, and it does not work reliably across symmetric NATs or other poorly behaved legacy NATs.
591:
the inside of the NAT is mapped to an external public address. Port address translation (PAT) resolves conflicts that arise when multiple hosts happen to use the same source port number to establish different external connections at the same time.
1016:
is able to access another machine on the LAN via the external IP address of the LAN/router (with port forwarding set up on the router to direct requests to the appropriate machine on the LAN). This notion is officially described in 2008,
612:
IP address and port information of the NAT device instead of internal host IP addresses or port numbers. NAT only translates IP addresses and ports of its internal hosts, hiding the true endpoint of an internal host on a private network.
734:, can be disrupted. Unless the NAT router makes a specific effort to support such protocols, incoming packets cannot reach their destination. Some protocols can accommodate one instance of NAT between participating hosts ("passive mode"
988:
Dynamic NAT, just like static NAT, is not common in smaller networks but is found within larger corporations with complex networks. Where static NAT provides a one-to-one internal to public static IP address mapping, dynamic NAT uses a
230:
This method allows communication through the router only when the conversation originates in the private network, since the initial originating transmission is what establishes the required information in the translation tables. Thus a
1166:
because one of the design goals of IPv6 is to restore end-to-end network connectivity. The large addressing space of IPv6 obviates the need to conserve addresses and every device can be given a unique globally routable address. Use of
587:. The IP address of a public server is also important, similar in global uniqueness to a postal address or telephone number. Both IP address and port number must be correctly known by all hosts wishing to successfully communicate.
655:
forward client requests to a set of server computers to manage the workload of each server. Network address translation may be used to map a representative IP address of the server cluster to specific hosts that service the
481:
Some NAT devices are not yet compliant with RFC 4787 as they treat NAT mapping and filtering in the same way so that their configuration option for changing the NAT filtering method also changes the NAT mapping method (e.g.
157:
The network has a router having both a private and a public address. The private address is used by the router for communicating with other devices in the private local network. The public address (typically assigned by an
1515:
Most NAT devices today allow the network administrator to configure static translation table entries for connections from the external network to the internal masqueraded network. This feature is often referred to as
529:) can occur on the same source port, and applications usually reuse the same UDP socket to send packets to distinct hosts. This makes port prediction straightforward, as it is the same source port for each packet.
780:
Because the internal addresses are all disguised behind one publicly accessible address, it is impossible for external hosts to directly initiate a connection to a particular internal host. Applications such as
170:). When the router receives inbound traffic from the Internet, it uses the connection tracking data it stored during the outbound phase to determine to which private address (if any) it should forward the reply.
1207:
addresses. If the host making the request lies behind a simple NAT firewall, the translation of the IP address or TCP port number makes the information received by the server invalid. SIP commonly controls
252:
be necessary to examine and categorize the type of mapping in use, for example when it is desired to set up a direct communication path between two clients both of which are behind separate NAT gateways.
447:. Other classifications of NAT behavior mentioned in the RFC include whether they preserve ports, when and how mappings are refreshed, whether external mappings can be used by internal hosts (i.e., its
1179:
range for all devices to remain reachable. Even actual IPv6-to-IPv6 NAT, NAT66, can turn out useful at times: the APNIC blog outlines a case where the author was only provided a single address (/128).
621:
network. Otherwise, if the destination port number of the incoming packet is not found in the translation table, the packet is dropped or rejected because the PAT device doesn't know where to send it.
600:
transferred to an individual inside the office. In this scenario, the office is a private LAN, the main phone number is the public IP address, and the individual extensions are unique port numbers.
1528:
which passes all traffic received on the external interface (on any port number) to an internal IP address while preserving the destination port. Both types may be available in the same NAT device.
769:, but that NAT does have a valid role in careful design. There is considerably more concern with the use of IPv6 NAT, and many IPv6 architects believe IPv6 was intended to remove the need for NAT.
99:
describes NAT as a "short-term solution" to the two most compelling problems facing the IP Internet at that time: IP address depletion and scaling in routing. By 2004, NAT had become widespread.
474:
possible choices do not relate to the security of the NAT as security is determined by the filtering behavior and then specifies "A NAT MUST have an 'Endpoint-Independent
Mapping' behavior."
844:(DF) bit in the appropriate packet header field. This is only a one-way solution, because the responding host can send packets of any size, which may be fragmented before reaching the NAT.
2154:
2082:
478:
Filtering is recommended where maximum application transparency is required while
Address-Dependent Filtering is recommended where more stringent filtering behavior is most important.
1154:. When the server replies, the process is identical to an external sender. Thus, two-way communication is possible between hosts inside the LAN network via the public IP address.
714:
and statefulness problems of carrier-grade NAT, and also provides a transition mechanism for the deployment of native IPv6 at the same time with very little added complexity.
1122:
reply may be sent. If any DNAT rules were present, address translation is still in effect; the router still rewrites the source IP address in the packet. The local computer (
2136:
2064:
1287:
to the NAT is mapped onto one client, causing service to more than one client behind the NAT to fail. There are a couple of solutions to this problem: one is to use
2475:
1923:
127:, and any higher-level checksums that include the IP address are changed. Basic NAT can be used to interconnect two IP networks that have incompatible addressing.
1856:
1308:
67:
was replaced, but could not route the network's address space. It has become a popular and essential tool in conserving global address space in the face of
2416:
1811:
91:
IPv4 uses 32-bit addresses, capable of uniquely addressing about 4.3 billion devices. By 1992 it became evident that that would not be enough. The 1994
945:
175:
modified. To avoid ambiguity in how replies are translated, further modifications to the packets are required. The vast bulk of
Internet traffic uses
1220:. IP addresses and port numbers are encoded in the payload data and must be known before the traversal of NATs. Without special techniques, such as
576:
For publicly accessible services such as web and mail servers the port number is important. For example, port 443 connects through a socket to the
565:
Every TCP and UDP packet contains a source port number and a destination port number. Each of those packets is encapsulated in an IP packet, whose
2165:
2093:
1172:
369:
Once an internal address (iAddr:iPort) is mapped to an external address (eAddr:ePort), any packets from iAddr:iPort are sent through eAddr:ePort.
332:
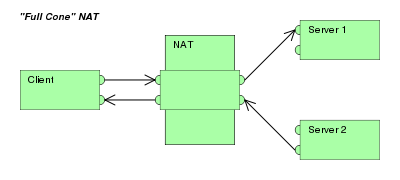
Once an internal address (iAddr:iPort) is mapped to an external address (eAddr:ePort), any packets from iAddr:iPort are sent through eAddr:ePort.
305:
Once an internal address (iAddr:iPort) is mapped to an external address (eAddr:ePort), any packets from iAddr:iPort are sent through eAddr:ePort.
772:
An implementation that only tracks ports can be quickly depleted by internal applications that use multiple simultaneous connections such as an
1314:
1244:
868:
DNAT is commonly used to publish a service located in a private network on a publicly accessible IP address. This use of DNAT is also called
1964:
63:. The technique was originally used to bypass the need to assign a new address to every host when a network was moved, or when the upstream
2501:
2328:
2303:
2485:
1615:
1405:
957:
802:
569:
contains a source IP address and a destination IP address. The IP address/protocol/port number triple defines an association with a
376:) can send packets to iAddr:iPort by sending packets to eAddr:ePort only if iAddr:iPort has previously sent a packet to hAddr:hPort.
2451:
1456:
1268:
801:
Pure NAT, operating on IP alone, may or may not correctly parse protocols with payloads containing information about IP, such as
2461:
339:) can send packets to iAddr:iPort by sending packets to eAddr:ePort only if iAddr:iPort has previously sent a packet to hAddr:
195:) on the returned packet can be unambiguously mapped to the corresponding private network destination. RFC 2663 uses the term
1842:
462:, where incoming packets addressed to the external address and port are redirected to a specific internal address and port.
814:
727:
525:
On the other hand, for UDP, NATs do not need port preservation. Indeed, multiple UDP communications (each with a distinct
176:
2155:"Use NAT for Public Accessto Servers with Private IP Addresses on the Private Network (WatchGuard configuration example)"
2083:"Use NAT for Public Accessto Servers with Private IP Addresses on the Private Network (WatchGuard configuration example)"
1450:
1217:
1213:
1119:
1337:
1196:
762:
707:
679:
2249:
451:
behavior), and the level of determinism NATs exhibit when applying all these rules. Specifically, most NATs combine
1778:
1581:
1524:
which forwards traffic from a specific external port to an internal host on a specified port, and designation of a
652:
584:
167:
2229:
1468:
1264:
1248:
1225:
739:
159:
64:
2426:
1415:
1288:
949:
419:
above table, the RFC would characterize Full-Cone, Restricted-Cone, and Port-Restricted Cone NATs as having an
506:. Another way is to use various NAT traversal techniques. The most popular technique for TCP NAT traversal is
1818:
427:. For the second bullet in each row of the above table, RFC 4787 would also label Full-Cone NAT as having an
723:
502:
problem arises when peers behind different NATs try to communicate. One way to solve this problem is to use
240:
192:
188:
143:
The majority of network address translators map multiple private hosts to one publicly exposed IP address.
68:
1937:
Singh, R.; Tay, Y.C.; Teo, W.T.; Yeow, S.W. (1999). "RAT: A quick (and dirty?) push for mobility support".
828:
TCP and UDP, have a checksum that covers all the data they carry, as well as the TCP or UDP header, plus a
1942:
1693:
1296:
1192:
818:
731:
526:
180:
857:
Destination network address translation (DNAT) is a technique for transparently changing the destination
1474:
1260:
135:
952:. It provides connection tracking and filtering for the additional network connections needed for the
746:), but fail when both systems are separated from the internet by NAT. The use of NAT also complicates
2398:
2047:
2009:
1675:
1438:
1168:
766:
1325:
1947:
1895:
761:
End-to-end connectivity has been a core principle of the
Internet, supported, for example, by the
1970:
1746:
881:
877:
862:
837:
747:
691:
60:
648:
1960:
1738:
1611:
1444:
1252:
1188:
1041:
911:). This is used to describe one-to-many NAT; NAT for outgoing connections to public services.
786:
695:
683:
507:
243:
by allowing entire networks to be connected to the
Internet using a single public IP address.
754:
because NAT modifies values in the headers which interfere with the integrity checks done by
2388:
2037:
1999:
1952:
1875:
1795:
1730:
1665:
1495:
1018:
840:
to determine the packet size that can be transmitted without fragmentation and then set the
108:
92:
726:
and cannot participate in some internet protocols. Services that require the initiation of
2455:
1521:
1480:
1232:
that serve to implement ALGs. However, ALG cannot work if the protocol data is encrypted.
1204:
1095:
873:
869:
730:
connections from the outside network, or that use stateless protocols such as those using
635:
519:
503:
401:
Only an external host that receives a packet from an internal host can send a packet back.
382:
76:
52:
17:
2353:
706:/port translation function (and the maintenance of NAT state) entirely into the existing
483:
1764:
561:
In bidirectional NAT the session can be established both from inside and outside realms.
2458: (archived 2006-01-11) – Paper discussing the different types of NAT
1939:
Proceedings WMCSA'99. Second IEEE Workshop on Mobile
Computing Systems and Applications
1409:
1393:
672:
changes from time to time to remain reachable as a server via a fixed home IP address.
570:
107:
The simplest type of NAT provides a one-to-one translation of IP addresses (RFC 1631).
2467:
2462:
Anatomy: A Look Inside Network Address Translators – Volume 7, Issue 3, September 2004
2495:
2479:
2421:
2281:
1399:
1304:
1236:
1209:
1200:
918:
790:
499:
48:
1750:
1465: – Intermediary box on the data path between a source host and destination host
557:
1974:
1321:
969:
703:
541:
458:
353:
765:. Current Internet architectural documents observe that NAT is a violation of the
1909:
1605:
880:, which becomes exposed to the WAN, becoming analogous to an undefended military
2401:
2378:
2270:
2050:
2027:
2012:
1989:
1799:
1678:
1655:
1351:
1022:
933:
448:
366:
Like an address restricted cone NAT, but the restriction includes port numbers.
232:
184:
112:
96:
1718:
686:
translation with tunneling of the IPv4 packets over an ISP provider's internal
2329:"subnet - IPv6 subnetting a /64 - what will break, and how to work around it?"
1765:"Characterization and Measurement of TCP Traversal through NATs and Firewalls"
1486:
1419:
1369:
1295:
and does not mask the port number; another is to encapsulate the IPsec within
937:
865:
situated between two endpoints can perform this transformation of the packet.
858:
669:
577:
223:. This is the most common type of NAT and has become synonymous with the term
72:
1956:
1742:
1441:(AYIYA) – IPv6 over IPv4 UDP, thus working IPv6 tunneling over most NATs
2275:
1462:
1375:
1363:
1283:
1216:
may use multiple ports to set up a connection and transmit voice stream via
980:
861:
of a routed packet and performing the inverse function for any replies. Any
668:
Reverse Address and Port Translation (RAPT or RAT) allows a host whose real
566:
56:
32:
2182:
2110:
821:
cannot function properly unless NAT takes action beyond the network layer.
407:
317:
2482: (archived 2013-01-03) (Part of the documentation for the IBM iSeries)
2377:
D. Wing, Ed; Cheshire, S.; Boucadair, M.; Penno, R.; Selkirk, P. (2013).
1657:
Network Address Translation (NAT) Behavioral Requirements for Unicast UDP
1525:
1383:
1379:
1347:
1251:. NAT traversal is possible in both TCP- and UDP-based applications, but
1118:
If no applicable DNAT rule is available, the router drops the packet. An
608:
With NAT, all communications sent to external hosts actually contain the
522:
for each TCP communication, make NAT port prediction impossible for TCP.
124:
2026:
Velde, G. Van de; Hain, T.; Droms, R.; Carpenter, B.; Klein, E. (2007).
1782:
1734:
162:) is used by the router for communicating with the rest of the Internet.
1568:
1425:
1355:
1341:
1292:
699:
490:
available to enable RFC 4787 support but this has not yet been merged.
2208:
1880:
1324:
on July 8, 2008, is indirectly affected by NAT port mapping. To avoid
805:. This depends on whether the payload is interpreted by a host on the
36:
Network address translation between a private network and the Internet
2393:
2042:
2004:
1779:"Illuminating the shadows: Opportunistic network and web measurement"
1670:
1359:
1300:
711:
487:
833:
or UDP header of the first packet of the fragmented set of packets.
470:
RFC 4787 makes a distinction between NAT mapping and NAT filtering.
1719:"Network Address Translation: Extending the Internet Address Space"
1387:
1282:
encryption is applied and in cases where multiple devices such as
1279:
979:
961:
755:
751:
673:
556:
311:
can send packets to iAddr:iPort by sending packets to eAddr:ePort.
134:
31:
1098:(the router) A router with the NAT loopback feature detects that
968:
protocols as well as the ability to configure a transparent HTTP
944:
Secure network address translation (SNAT) is part of Microsoft's
2384:
2033:
1995:
1661:
1317:
is a NAT traversal technique that does not rely on ALG support.
1240:
1221:
1163:
965:
782:
773:
687:
665:
581:
494:
Type of NAT and NAT traversal, role of port preservation for TCP
260:
1012:, is a feature in many consumer routers where a machine on the
1013:
953:
735:
239:
An additional benefit of one-to-many NAT is that it mitigates
187:
are changed so that the combination of IP address (within the
1271:
but these require the NAT device to implement that protocol.
1224:, NAT behavior is unpredictable and communications may fail.
1212:
calls, and suffer the same problem. SIP and its accompanying
423:, whereas it would characterize a Symmetric NAT as having an
406:
381:
352:
316:
2304:"After staunch resistance, NAT may come to IPv6 after all"
27:
Technique for making connections between IP address spaces
1610:(2 ed.). Javvin Technologies Inc. 2005. p. 27.
1309:
use a session border controller to help traverse the NAT
123:. In this type of NAT, only the IP addresses, IP header
1491:
Pages displaying short descriptions of redirect targets
255:
For this purpose, RFC 3489 specified a protocol called
2250:"What is NAT Reflection/NAT Loopback/NAT Hairpinning?"
59:
of packets while they are in transit across a traffic
1991:
Some Internet Architectural Guidelines and Philosophy
1115:, then the host at that address receives the packet.
1694:"Anatomy: A Look Inside Network Address Translators"
1235:
Another possible solution to this problem is to use
1162:
Network address translation is not commonly used in
738:, for example), sometimes with the assistance of an
1924:"Configure Server Load Balancing Using Dynamic NAT"
1340:(ICS): NAT & DHCP implementation included with
283:now represents the new title of the specification:
1567:Unless an explicit route is set in the computer's
2137:"Enhanced IP Resiliency Using Cisco Stateful NAT"
2065:"Enhanced IP Resiliency Using Cisco Stateful NAT"
1872:Load Sharing using IP Network Address Translation
948:and is an extension to the NAT driver built into
743:
513:TCP hole punching requires the NAT to follow the
1857:"VPNs with Overlapping Subnets Problem Scenario"
1654:François Audet; Cullen Jennings (January 2007).
1428:: third-party routing implementation for Windows
903:is a common expansion and is the counterpart of
836:Alternatively, the originating host may perform
263:) in 2003. It classified NAT implementations as
1303:to achieve secure NAT traversal, or a NAT with
789:, and other peer-to-peer applications must use
1453: – Connection between two network systems
1870:Srisuresh, Pyda; Gan, Der-Hwa (August 1998).
1408:(RRAS): routing implementation included with
1094:, the packet would normally be routed to the
722:Hosts behind NAT-enabled routers do not have
8:
1489: – Logical subdivision of an IP network
1320:The DNS protocol vulnerability announced by
1028:The following describes an example network:
203:) for this type of NAT. Other names include
2417:"Major DNS flaw could disrupt the Internet"
150:A local network uses one of the designated
75:of a NAT gateway can be used for an entire
1422:packet forwarding implementation for Linux
1299:– the latter being the solution chosen by
540:As of 2006, roughly 70% of the clients in
2392:
2041:
2003:
1946:
1879:
1669:
1649:
1647:
1645:
1643:
1641:
1639:
1637:
1635:
1633:
946:Internet Security and Acceleration Server
580:software and port 465 to a mail server's
1812:"The Audio over IP Instant Expert Guide"
439:, and Symmetric NAT as having either an
435:, Port-Restricted Cone NAT as having an
289:
1817:. Tieline. January 2010. Archived from
1597:
1508:
813:of the translation. Basic protocols as
2452:Characterization of different TCP NATs
1520:. It may be implemented in two types:
1315:Interactive Connectivity Establishment
1247:(ICE), or proprietary approaches in a
1245:Interactive Connectivity Establishment
710:NAT implementation. Thus avoiding the
690:network. In effect, it is an (almost)
2486:Network Address Translation (NAT) FAQ
2470:How Network Address Translation Works
347:means the port number doesn't matter.
7:
2354:"NAT66: The good, the bad, the ugly"
1712:
1710:
1372:(ipfw): FreeBSD-native packet filter
1175:can achieve results similar to NAT.
544:networks employed some form of NAT.
445:Address and Port-Dependent Filtering
437:Address and Port-Dependent Filtering
197:network address and port translation
2302:Iljitsch van Beijnum (2008-07-23).
1843:"Using NAT in Overlapping Networks"
1580:This issue can be avoided by using
1278:NATs can also cause problems where
1239:techniques using protocols such as
976:Dynamic network address translation
936:and by Microsoft (in regard to the
744:§ Applications affected by NAT
431:, Restricted-Cone NAT as having an
425:Address- and Port-Dependent Mapping
291:NAT implementation classifications
285:Session Traversal Utilities for NAT
2183:"K7820: Overview of SNAT features"
2111:"K7820: Overview of SNAT features"
1447: – NAT behind NAT within ISP.
1130:) sends the packet as coming from
682:is a Cisco proposal that combines
595:Telephone number extension analogy
553:Establishing two-way communication
25:
2029:Local Network Protection for IPv6
1896:"What Is Layer 4 Load Balancing?"
1406:Routing and Remote Access Service
257:Simple Traversal of UDP over NATs
146:Here is a typical configuration:
2271:"NAT Loopback Routers – OpenSim"
1548:is limited to approximately 64K.
1498: – NAT traversal using IPv6
1457:Internet Gateway Device Protocol
1269:Internet Gateway Device Protocol
183:(UDP). For these protocols, the
2327:Dupont, Kasper (Aug 18, 2015).
1781:. December 2006. Archived from
1692:Geoff Huston (September 2004).
1483: – NAT traversal mechanism
1459:(UPnP IGD) NAT-traversal method
758:and other tunneling protocols.
634:especially when using RFC 1918
47:) is a method of mapping an IP
1471:(NAT-PMP) NAT-traversal method
1402:: OpenBSD-native packet filter
455:for outgoing connections with
429:Endpoint-Independent Filtering
191:) and port number (within the
154:IP address subnets (RFC 1918).
115:refers to this type of NAT as
1:
2415:Messmer, Ellen (2008-07-08).
2352:Cilloni, Marco (2018-02-01).
1701:The Internet Protocol Journal
1396:: NetBSD-native packet filter
1146:) receives it as coming from
1067:Address of a local computer:
1040:. This is the address of the
328:(Address)-restricted-cone NAT
269:(address) restricted-cone NAT
177:Transmission Control Protocol
2252:. NYC Networkers. 2014-11-09
1988:Bush, R.; Meyer, D. (2002).
1451:Gateway (telecommunications)
1218:Real-time Transport Protocol
1214:Session Description Protocol
1183:Applications affected by NAT
1120:ICMP Destination Unreachable
1047:Internal address of router:
466:NAT mapping vs NAT filtering
421:Endpoint-Independent Mapping
2502:Network address translation
2380:Port Control Protocol (PCP)
1362:, available for many other
1338:Internet Connection Sharing
1197:Session Initiation Protocol
797:Fragmentation and checksums
763:Internet Architecture Board
708:customer premises equipment
680:Mapping of Address and Port
441:Address-Dependent Filtering
433:Address-Dependent Filtering
41:Network address translation
2518:
1607:Network Protocols Handbook
1477:(PCP) NAT-traversal method
1173:network prefix translation
51:into another by modifying
18:Network address translator
1910:"What is load balancing?"
1469:NAT Port Mapping Protocol
1344:desktop operating systems
1265:NAT Port Mapping Protocol
1249:session border controller
1226:Application Layer Gateway
740:application-level gateway
486:). The PF firewall has a
160:Internet service provider
65:Internet service provider
1957:10.1109/MCSA.1999.749275
1717:Wing, Dan (2010-07-01).
1332:Examples of NAT software
1259:Other possibilities are
1044:interface on the router.
993:of public IP addresses.
950:Microsoft Windows Server
892:The meaning of the term
793:techniques to function.
518:distinct TCP sockets to
364:Port-restricted cone NAT
273:port-restricted cone NAT
205:port address translation
71:. One Internet-routable
1723:IEEE Internet Computing
1307:support; another is to
1253:the UDP-based technique
1078:If a packet is sent to
1057:Address of the server:
876:when used on an entire
724:end-to-end connectivity
241:IPv4 address exhaustion
139:Network address mapping
69:IPv4 address exhaustion
1193:File Transfer Protocol
1169:unique local addresses
985:
984:How dynamic NAT works.
718:Issues and limitations
562:
411:
386:
357:
321:
247:Methods of translation
193:Transport Layer header
181:User Datagram Protocol
140:
119:; it is also called a
37:
1475:Port Control Protocol
1261:Port Control Protocol
983:
926:is used by WatchGuard
560:
410:
385:
356:
320:
138:
35:
1439:Anything In Anything
1291:, which operates at
1171:in combination with
777:translation device.
767:end-to-end principle
1735:10.1109/MIC.2010.96
1326:DNS cache poisoning
1230:connection trackers
1191:protocols, such as
748:tunneling protocols
604:Translation process
292:
55:information in the
2162:www.watchguard.com
2090:www.watchguard.com
1941:. pp. 32–40.
1138:, but the server (
986:
896:varies by vendor:
882:demilitarized zone
838:path MTU Discovery
825:which connection.
661:Related techniques
563:
412:
387:
372:An external host (
358:
335:An external host (
322:
290:
141:
38:
2211:. 26 January 2016
2189:. August 28, 2007
2117:. August 28, 2007
1966:978-0-7695-0025-6
1859:. September 2017.
1445:Carrier-grade NAT
1412:operating systems
1366:operating systems
1350:: included with (
1189:application layer
1086:by a computer at
1004:, also known as
787:videoconferencing
696:carrier-grade NAT
684:Address plus Port
515:port preservation
508:TCP hole punching
416:
415:
309:Any external host
227:in common usage.
83:implementations.
16:(Redirected from
2509:
2476:Routing with NAT
2439:
2438:
2436:
2434:
2425:. Archived from
2412:
2406:
2405:
2396:
2394:10.17487/RFC6887
2374:
2368:
2367:
2365:
2364:
2349:
2343:
2342:
2340:
2339:
2324:
2318:
2317:
2315:
2314:
2299:
2293:
2292:
2290:
2289:
2279:
2267:
2261:
2260:
2258:
2257:
2246:
2240:
2239:
2237:
2236:
2226:
2220:
2219:
2217:
2216:
2205:
2199:
2198:
2196:
2194:
2179:
2173:
2172:
2170:
2164:. Archived from
2159:
2151:
2145:
2144:
2133:
2127:
2126:
2124:
2122:
2107:
2101:
2100:
2098:
2092:. Archived from
2087:
2079:
2073:
2072:
2061:
2055:
2054:
2045:
2043:10.17487/RFC4864
2023:
2017:
2016:
2007:
2005:10.17487/RFC3439
1985:
1979:
1978:
1950:
1934:
1928:
1927:
1920:
1914:
1913:
1912:. November 2018.
1906:
1900:
1899:
1892:
1886:
1885:
1883:
1867:
1861:
1860:
1853:
1847:
1846:
1839:
1833:
1832:
1830:
1829:
1823:
1816:
1808:
1802:
1793:
1787:
1786:
1775:
1769:
1768:
1767:. December 2006.
1761:
1755:
1754:
1714:
1705:
1704:
1698:
1689:
1683:
1682:
1673:
1671:10.17487/RFC4787
1651:
1628:
1627:
1625:
1624:
1602:
1585:
1578:
1572:
1565:
1559:
1555:
1549:
1545:
1539:
1535:
1529:
1513:
1496:Teredo tunneling
1492:
1305:"IPsec Passthru"
1152:
1151:
1144:
1143:
1136:
1135:
1128:
1127:
1113:
1112:
1104:
1103:
1092:
1091:
1084:
1083:
1073:
1072:
1063:
1062:
1053:
1052:
1038:
1037:
1032:Public address:
702:that pushes the
299:, also known as
293:
21:
2517:
2516:
2512:
2511:
2510:
2508:
2507:
2506:
2492:
2491:
2488:– Cisco Systems
2468:HowStuffWorks:
2456:Wayback Machine
2448:
2443:
2442:
2432:
2430:
2414:
2413:
2409:
2376:
2375:
2371:
2362:
2360:
2351:
2350:
2346:
2337:
2335:
2326:
2325:
2321:
2312:
2310:
2301:
2300:
2296:
2287:
2285:
2273:
2269:
2268:
2264:
2255:
2253:
2248:
2247:
2243:
2234:
2232:
2228:
2227:
2223:
2214:
2212:
2207:
2206:
2202:
2192:
2190:
2181:
2180:
2176:
2168:
2157:
2153:
2152:
2148:
2135:
2134:
2130:
2120:
2118:
2109:
2108:
2104:
2096:
2085:
2081:
2080:
2076:
2063:
2062:
2058:
2025:
2024:
2020:
1987:
1986:
1982:
1967:
1936:
1935:
1931:
1922:
1921:
1917:
1908:
1907:
1903:
1894:
1893:
1889:
1869:
1868:
1864:
1855:
1854:
1850:
1841:
1840:
1836:
1827:
1825:
1821:
1814:
1810:
1809:
1805:
1794:
1790:
1777:
1776:
1772:
1763:
1762:
1758:
1716:
1715:
1708:
1696:
1691:
1690:
1686:
1653:
1652:
1631:
1622:
1620:
1618:
1604:
1603:
1599:
1594:
1589:
1588:
1579:
1575:
1566:
1562:
1556:
1552:
1546:
1542:
1536:
1532:
1522:port forwarding
1514:
1510:
1505:
1490:
1481:Port triggering
1435:
1334:
1205:transport layer
1185:
1160:
1149:
1148:
1141:
1140:
1133:
1132:
1125:
1124:
1110:
1109:
1101:
1100:
1096:default gateway
1089:
1088:
1081:
1080:
1070:
1069:
1060:
1059:
1050:
1049:
1035:
1034:
1002:NAT hairpinning
999:
997:NAT hairpinning
978:
905:destination NAT
890:
870:port forwarding
855:
850:
799:
720:
694:alternative to
663:
636:private network
627:
606:
597:
555:
550:
520:ephemeral ports
504:port forwarding
496:
468:
249:
221:many-to-one NAT
213:IP masquerading
133:
131:One-to-many NAT
105:
89:
77:private network
53:network address
28:
23:
22:
15:
12:
11:
5:
2515:
2513:
2505:
2504:
2494:
2493:
2490:
2489:
2483:
2473:
2464:
2459:
2447:
2446:External links
2444:
2441:
2440:
2407:
2369:
2344:
2319:
2294:
2262:
2241:
2221:
2200:
2174:
2171:on 2013-01-17.
2146:
2128:
2102:
2099:on 2013-01-17.
2074:
2056:
2018:
1980:
1965:
1929:
1915:
1901:
1887:
1862:
1848:
1845:. August 2005.
1834:
1803:
1788:
1785:on 2010-07-24.
1770:
1756:
1706:
1684:
1629:
1616:
1596:
1595:
1593:
1590:
1587:
1586:
1584:instead of FTP
1573:
1560:
1550:
1540:
1530:
1507:
1506:
1504:
1501:
1500:
1499:
1493:
1484:
1478:
1472:
1466:
1460:
1454:
1448:
1442:
1434:
1431:
1430:
1429:
1423:
1413:
1410:Windows Server
1403:
1397:
1391:
1373:
1367:
1345:
1333:
1330:
1267:(NAT-PMP), or
1184:
1181:
1159:
1156:
1076:
1075:
1065:
1055:
1045:
1010:NAT reflection
998:
995:
977:
974:
942:
941:
927:
921:
912:
889:
886:
854:
851:
849:
846:
842:don't fragment
798:
795:
719:
716:
662:
659:
658:
657:
653:load balancers
651:applications,
645:
644:Load balancing
641:
640:
631:
626:
623:
605:
602:
596:
593:
571:network socket
554:
551:
549:
548:Implementation
546:
495:
492:
467:
464:
414:
413:
404:
403:
402:
399:
389:
388:
379:
378:
377:
370:
360:
359:
350:
349:
348:
333:
324:
323:
314:
313:
312:
306:
301:one-to-one NAT
248:
245:
172:
171:
163:
155:
132:
129:
121:one-to-one NAT
104:
101:
88:
85:
61:routing device
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
2514:
2503:
2500:
2499:
2497:
2487:
2484:
2481:
2480:archive.today
2477:
2474:
2472:
2471:
2465:
2463:
2460:
2457:
2453:
2450:
2449:
2445:
2429:on 2009-02-13
2428:
2424:
2423:
2422:Network World
2418:
2411:
2408:
2403:
2400:
2395:
2390:
2386:
2382:
2381:
2373:
2370:
2359:
2355:
2348:
2345:
2334:
2330:
2323:
2320:
2309:
2305:
2298:
2295:
2283:
2282:OpenSimulator
2277:
2272:
2266:
2263:
2251:
2245:
2242:
2231:
2230:"Dynamic NAT"
2225:
2222:
2210:
2209:"Dynamic NAT"
2204:
2201:
2188:
2184:
2178:
2175:
2167:
2163:
2156:
2150:
2147:
2142:
2138:
2132:
2129:
2116:
2112:
2106:
2103:
2095:
2091:
2084:
2078:
2075:
2070:
2066:
2060:
2057:
2052:
2049:
2044:
2039:
2035:
2031:
2030:
2022:
2019:
2014:
2011:
2006:
2001:
1997:
1993:
1992:
1984:
1981:
1976:
1972:
1968:
1962:
1958:
1954:
1949:
1948:10.1.1.40.461
1944:
1940:
1933:
1930:
1925:
1919:
1916:
1911:
1905:
1902:
1897:
1891:
1888:
1882:
1877:
1873:
1866:
1863:
1858:
1852:
1849:
1844:
1838:
1835:
1824:on 2011-10-08
1820:
1813:
1807:
1804:
1801:
1797:
1792:
1789:
1784:
1780:
1774:
1771:
1766:
1760:
1757:
1752:
1748:
1744:
1740:
1736:
1732:
1728:
1724:
1720:
1713:
1711:
1707:
1702:
1695:
1688:
1685:
1680:
1677:
1672:
1667:
1663:
1659:
1658:
1650:
1648:
1646:
1644:
1642:
1640:
1638:
1636:
1634:
1630:
1619:
1617:9780974094526
1613:
1609:
1608:
1601:
1598:
1591:
1583:
1577:
1574:
1570:
1564:
1561:
1554:
1551:
1544:
1541:
1534:
1531:
1527:
1523:
1519:
1512:
1509:
1502:
1497:
1494:
1488:
1485:
1482:
1479:
1476:
1473:
1470:
1467:
1464:
1461:
1458:
1455:
1452:
1449:
1446:
1443:
1440:
1437:
1436:
1432:
1427:
1424:
1421:
1417:
1414:
1411:
1407:
1404:
1401:
1398:
1395:
1392:
1390:packet filter
1389:
1385:
1381:
1377:
1374:
1371:
1368:
1365:
1361:
1357:
1353:
1349:
1346:
1343:
1339:
1336:
1335:
1331:
1329:
1327:
1323:
1318:
1316:
1312:
1310:
1306:
1302:
1298:
1294:
1290:
1285:
1281:
1276:
1272:
1270:
1266:
1262:
1257:
1254:
1250:
1246:
1242:
1238:
1237:NAT traversal
1233:
1231:
1227:
1223:
1219:
1215:
1211:
1210:voice over IP
1206:
1202:
1201:network layer
1198:
1194:
1190:
1182:
1180:
1176:
1174:
1170:
1165:
1157:
1155:
1153:
1145:
1137:
1134:192.168.1.100
1129:
1126:192.168.1.100
1121:
1116:
1114:
1105:
1097:
1093:
1090:192.168.1.100
1085:
1074:
1071:192.168.1.100
1066:
1064:
1056:
1054:
1046:
1043:
1039:
1031:
1030:
1029:
1026:
1024:
1020:
1015:
1011:
1007:
1003:
996:
994:
992:
982:
975:
973:
971:
967:
963:
959:
955:
951:
947:
939:
935:
931:
928:
925:
922:
920:
919:Cisco Systems
916:
913:
910:
906:
902:
899:
898:
897:
895:
887:
885:
883:
879:
875:
871:
866:
864:
860:
852:
848:Variant terms
847:
845:
843:
839:
834:
831:
830:pseudo-header
826:
822:
820:
816:
812:
808:
804:
796:
794:
792:
791:NAT traversal
788:
784:
778:
775:
770:
768:
764:
759:
757:
753:
749:
745:
741:
737:
733:
729:
725:
717:
715:
713:
709:
705:
701:
697:
693:
689:
685:
681:
677:
675:
671:
667:
660:
654:
650:
649:client–server
646:
643:
642:
637:
632:
629:
628:
624:
622:
618:
614:
611:
603:
601:
594:
592:
588:
586:
583:
579:
574:
572:
568:
559:
552:
547:
545:
543:
538:
534:
530:
528:
523:
521:
516:
511:
509:
505:
501:
500:NAT traversal
493:
491:
489:
485:
479:
475:
471:
465:
463:
461:
460:
454:
453:symmetric NAT
450:
446:
442:
438:
434:
430:
426:
422:
409:
405:
400:
396:
395:
394:
393:Symmetric NAT
391:
390:
384:
380:
375:
371:
368:
367:
365:
362:
361:
355:
351:
346:
342:
338:
334:
331:
330:
329:
326:
325:
319:
315:
310:
307:
304:
303:
302:
298:
297:Full-cone NAT
295:
294:
288:
286:
282:
278:
277:symmetric NAT
274:
270:
266:
265:full-cone NAT
262:
258:
253:
246:
244:
242:
237:
234:
228:
226:
222:
218:
214:
210:
206:
202:
198:
194:
190:
186:
182:
178:
169:
164:
161:
156:
153:
149:
148:
147:
144:
137:
130:
128:
126:
122:
118:
114:
110:
102:
100:
98:
94:
86:
84:
80:
78:
74:
70:
66:
62:
58:
54:
50:
49:address space
46:
42:
34:
30:
19:
2469:
2466:Jeff Tyson,
2431:. Retrieved
2427:the original
2420:
2410:
2379:
2372:
2361:. Retrieved
2357:
2347:
2336:. Retrieved
2333:Server Fault
2332:
2322:
2311:. Retrieved
2308:Ars Technica
2307:
2297:
2286:. Retrieved
2284:. 2013-10-21
2265:
2254:. Retrieved
2244:
2233:. Retrieved
2224:
2213:. Retrieved
2203:
2193:February 24,
2191:. Retrieved
2186:
2177:
2166:the original
2161:
2149:
2140:
2131:
2121:February 24,
2119:. Retrieved
2114:
2105:
2094:the original
2089:
2077:
2068:
2059:
2028:
2021:
1990:
1983:
1938:
1932:
1926:. June 2018.
1918:
1904:
1898:. June 2020.
1890:
1871:
1865:
1851:
1837:
1826:. Retrieved
1819:the original
1806:
1791:
1783:the original
1773:
1759:
1729:(4): 66–70.
1726:
1722:
1700:
1687:
1656:
1621:. Retrieved
1606:
1600:
1576:
1563:
1553:
1543:
1533:
1517:
1511:
1322:Dan Kaminsky
1319:
1313:
1277:
1273:
1258:
1234:
1229:
1186:
1177:
1161:
1147:
1139:
1131:
1123:
1117:
1108:
1099:
1087:
1079:
1077:
1068:
1058:
1048:
1033:
1027:
1009:
1006:NAT loopback
1005:
1001:
1000:
990:
987:
970:proxy server
943:
929:
923:
915:stateful NAT
914:
908:
904:
900:
893:
891:
867:
856:
841:
835:
829:
827:
823:
810:
806:
800:
779:
771:
760:
721:
704:IPv4 address
678:
664:
639:translation.
625:Applications
619:
615:
609:
607:
598:
589:
575:
564:
539:
535:
531:
524:
514:
512:
497:
484:Netgate TNSR
480:
476:
472:
469:
459:port mapping
456:
452:
444:
440:
436:
432:
428:
424:
420:
417:
392:
373:
363:
344:
340:
336:
327:
308:
300:
296:
284:
280:
276:
272:
268:
264:
256:
254:
250:
238:
229:
224:
220:
217:NAT overload
216:
212:
208:
204:
200:
196:
185:port numbers
173:
151:
145:
142:
120:
116:
106:
90:
81:
44:
40:
39:
29:
1352:OpenSolaris
1158:NAT in IPv6
1150:203.0.113.1
1142:192.168.1.2
1111:192.168.1.2
1102:203.0.113.1
1082:203.0.113.1
1061:192.168.1.2
1051:192.168.1.1
1036:203.0.113.1
934:F5 Networks
932:is used by
917:is used by
449:hairpinning
374:hAddr:hPort
233:web browser
2363:2023-04-20
2358:APNIC Blog
2338:2023-04-20
2313:2014-04-24
2288:2014-02-21
2256:2017-04-27
2235:2022-04-19
2215:2022-04-19
1828:2011-08-19
1623:2014-09-16
1592:References
1518:static NAT
1487:Subnetwork
1420:user space
1370:ipfirewall
1284:SIP phones
1195:(FTP) and
938:ISA Server
930:secure NAT
924:static NAT
901:source NAT
859:IP address
670:IP address
578:web server
73:IP address
2276:MediaWiki
1943:CiteSeerX
1743:1089-7801
1463:Middlebox
1376:Netfilter
1364:Unix-like
692:stateless
567:IP header
337:hAddr:any
189:IP header
179:(TCP) or
117:basic NAT
103:Basic NAT
57:IP header
2496:Category
1751:31082389
1526:DMZ host
1433:See also
1384:nftables
1380:iptables
1348:IPFilter
750:such as
656:request.
610:external
527:endpoint
125:checksum
2454:at the
2433:14 June
1975:7657883
1571:tables.
1569:routing
1538:access.
1426:WinGate
1356:FreeBSD
1342:Windows
1293:layer 4
1263:(PCP),
884:(DMZ).
811:outside
700:DS-Lite
630:Routing
457:static
152:private
87:History
1973:
1963:
1945:
1878:
1798:
1749:
1741:
1614:
1386:: the
1360:NetBSD
1301:TISPAN
1021:
964:, and
878:server
863:router
807:inside
712:NAT444
585:daemon
219:, and
111:
95:
2187:AskF5
2169:(PDF)
2158:(PDF)
2141:Cisco
2115:AskF5
2097:(PDF)
2086:(PDF)
2069:Cisco
1971:S2CID
1822:(PDF)
1815:(PDF)
1747:S2CID
1697:(PDF)
1558:4000.
1503:Notes
1388:Linux
1378:with
1280:IPsec
1187:Some
991:group
962:H.323
872:, or
756:IPsec
752:IPsec
742:(see
674:Cisco
488:patch
398:used.
2435:2021
2402:6887
2385:IETF
2195:2019
2123:2019
2051:4864
2034:IETF
2013:3439
1996:IETF
1961:ISBN
1881:2391
1800:8314
1739:ISSN
1679:4787
1662:IETF
1612:ISBN
1582:SFTP
1358:and
1241:STUN
1222:STUN
1203:and
1164:IPv6
1023:5128
966:PPTP
958:ICMP
909:DNAT
894:SNAT
888:SNAT
853:DNAT
817:and
803:ICMP
783:VOIP
774:HTTP
698:and
688:IPv6
666:IEEE
582:SMTP
498:The
281:STUN
261:STUN
201:NAPT
168:port
113:2663
97:1631
2478:at
2399:RFC
2389:doi
2048:RFC
2038:doi
2010:RFC
2000:doi
1953:doi
1876:RFC
1796:RFC
1731:doi
1676:RFC
1666:doi
1416:VPP
1394:NPF
1297:UDP
1289:TLS
1243:or
1042:WAN
1019:RFC
1014:LAN
1008:or
954:FTP
874:DMZ
819:UDP
815:TCP
809:or
736:FTP
732:UDP
728:TCP
647:In
542:P2P
443:or
345:Any
341:any
275:or
225:NAT
211:),
209:PAT
109:RFC
93:RFC
45:NAT
2498::
2419:.
2397:.
2387:.
2383:.
2356:.
2331:.
2306:.
2280:.
2185:.
2160:.
2139:.
2113:.
2088:.
2067:.
2046:.
2036:.
2032:.
2008:.
1998:.
1994:.
1969:.
1959:.
1951:.
1874:.
1745:.
1737:.
1727:14
1725:.
1721:.
1709:^
1699:.
1674:.
1664:.
1660:.
1632:^
1418::
1400:PF
1354:,
1311:.
1025:.
972:.
960:,
956:,
785:,
573:.
510:.
343:.
287:.
271:,
267:,
215:,
79:.
2437:.
2404:.
2391::
2366:.
2341:.
2316:.
2291:.
2278:)
2274:(
2259:.
2238:.
2218:.
2197:.
2143:.
2125:.
2071:.
2053:.
2040::
2015:.
2002::
1977:.
1955::
1884:.
1831:.
1753:.
1733::
1703:.
1681:.
1668::
1626:.
1382:/
940:)
907:(
259:(
207:(
199:(
43:(
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.