1417:
cyber attacks and cyber crime are going to expand as threat actors will continue to exploit weaknesses in protection and existing vulnerabilities to achieve their end goals, often being data theft or exfiltration. To combat cybercrime, the United States Secret
Service maintains an Electronic Crimes Task Force which extends beyond the United States as it helps to locate threat actors that are located globally and performing cyber related crimes within the United States. The Secret Service is also responsible for the National Computer Forensic Institute which allows law enforcement and people of the court to receive cyber training and information on how to combat cyber crime. The United States Immigration and Customs Enforcement is responsible for the Cyber Crimes Center (C3) providing cyber crime related services for federal, state, local and international agencies. Finally, the United States also has resources relating to Law Enforcement Cyber Incident Reporting to allow local and state agencies to understand how, when, and what should be reported as a cyber incident to the federal government.
1553:
protect information and the tactics criminals use to steal that information is paramount. However, despite cybercrime becoming a mounting problem, many people are not aware of the severity of this problem. This could be attributed to a lack of experience and knowledge of technological issues. There are 1.5 million cyber-attacks annually, which means that there are over 4,000 attacks a day, 170 attacks every hour, or nearly three attacks every minute, with studies showing that only 16 percent of victims had asked the people who were carrying out the attacks to stop. Comparitech's 2023 study shows that cybercrime victims have peaked to 71 million annually, which means there is a cyberattack every 39 seconds. Anybody who uses the internet for any reason can be a victim, which is why it is important to be aware of how to be protected while online.
1389:
1086:. With thousands of people dying each year due to drug overdose, investigators have made internet drug sales a priority. Many vendors do not realize the extra criminal charges that go along with selling drugs online, such as money laundering and illegal use of the mail. In 2019, a vendor was sentenced to 10 years in prison after selling cocaine and methamphetamine under the name JetSetLife. But despite the large amount of time investigators spend tracking down people, in 2018 only 65 suspects who bought and sold illegal goods on some of the biggest markets were identified. Meanwhile, thousands of transactions take place daily on these markets.
1562:
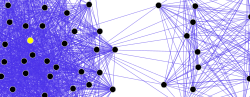
of stolen content, and so forth. A few of the leading cybersecurity companies have the skills and resources to follow the activities of these individuals and groups. A wide variety of information that can be used for defensive purposes is available from these sources, for example, technical indicators such as hashes of infected files and malicious IPs/URLs, as well as strategic information profiling the goals and techniques of the profiled groups. Much of it is freely available, but consistent, ongoing access typically requires a subscription. Some in the corporate sector see a crucial role for
1544:. A possible counter to this is for courts to ban convicted hackers from using the internet or computers, even after they have been released from prison – though as computers and the internet become more and more central to everyday life, this type of punishment becomes more and more draconian. Nuanced approaches have been developed that manage cyber offenders' behavior without resorting to total computer or internet bans. These approaches involve restricting individuals to specific devices which are subject to monitoring or searches by probation or parole officers.
1492:
Enhancement Act of 2014. Although the
Federal Information Security Modernization Act of 2014 was just an update of an older version of the act, it focused on the practices federal agencies were to abide by relating to cybersecurity. While the National Cybersecurity Protection Act of 2014 was aimed toward increasing the amount of information sharing that occurs across the federal and private sector to improve cybersecurity amongst the industries. Finally, the Cybersecurity Enhancement Act of 2014 relates to cybersecurity research and education.
51:
961:, which states that sending messages or letters electronically that the government deems "indecent or grossly offensive" and/or language intended to cause "distress and anxiety" can lead to a prison sentence of six months and a potentially large fine. Australia, while not directly addressing the issue of harassment, includes most forms of online harassment under the Criminal Code Act of 1995. Using telecommunication to send threats, harass, or cause offense is a direct violation of this act.
1078:, which re-opened in August 2021 under the control of DeSnake, one of the original administrators. Investigators pose as buyers and order products from darknet vendors in the hope that the vendors leave a trail the investigators can follow. In one case an investigator posed as a firearms seller, and for six months people purchased from them and provided home addresses. The FBI was able to make over a dozen arrests during this six-month investigation. Another crackdown targeted vendors selling
574:. Cyberextortionists demand money in return for promising to stop the attacks and provide "protection". According to the FBI, cyberextortionists are increasingly attacking corporate websites and networks, crippling their ability to operate, and demanding payments to restore their service. More than 20 cases are reported each month to the FBI, and many go unreported in order to keep the victim's name out of the public domain. Perpetrators often use a
863:
5764:
348:. These crimes involve the use of technology to commit fraud, identity theft, data breaches, computer viruses, scams, and expanded upon in other malicious acts. Cybercriminals exploit vulnerabilities in computer systems and networks to gain unauthorized access, steal sensitive information, disrupt services, and cause financial or reputational harm to individuals, organizations, and governments.
823:; click farms (companies where low-wage employees are paid to click or engage in conversations); incentivized browsing; video placement abuse (delivered in display banner slots); hidden ads (which will never be viewed by real users); domain spoofing (ads served on a fake website); and clickjacking, in which the user is forced to click on an ad.
1353:
there has been a 17.75% increase in vulnerabilities across all online devices. The internet's expansive reach causes the damage inflicted to people to be magnified since many methods of cybercrime have the opportunity to reach many people. The availability of virtual spaces has allowed cybercrime to become an everyday occurrence. In 2018, the
1488:
implemented, but there is still a gap in responding to current cyber related crime. The most recent cyber related law, according to NIST, was the NIST Small
Business Cybersecurity Act, which came out in 2018, and provides guidelines to small businesses to ensure that cybersecurity risks are being identified and addressed accurately.
1479:, laws against cybercrime are weak or sometimes nonexistent. Cybercriminals can then strike from across international borders and remain undetected. Even when identified, these criminals can typically avoid being extradited to a country such as the US that has laws that allow for prosecution. For this reason, agencies such as the
1055:. Darknet markets entice customers by making them feel comfortable. Although people can easily gain access to a Tor browser, actually gaining access to an illicit market is not as simple as typing it in on a search engine, as one would with Google. Darknet markets have special links that change frequently, ending in
1413:
to train professionals in law enforcement at the
National Computer Forensic Institute. The NCFI provides "state and local members of the law enforcement community with training in cyber incident response, investigation, and forensic examination in cyber incident response, investigation, and forensic examination."
1487:
The first cyber related law in the United States was the
Privacy Act of 1974 which was only required for federal agencies to follow to ensure privacy and protection of personally identifiable information (PII). However, since 1974, in the United States other laws and regulations have been drafted and
941:
to "persuade, induce, entice, coerce, or facilitate the travel of, the minor to engage in prohibited sexual conduct." Kramer appealed the sentence on the grounds that there was insufficient evidence to convict him under this statute because his charge included persuading through a computer device and
826:
Ad-fraud services include all online infrastructure and hosting services that might be needed to undertake identity or attribution fraud. Services can involve the creation of spam websites (fake networks of websites that provide artificial backlinks); link building services; hosting services; or fake
604:
Ransomware is a type of malware used in cyberextortion to restrict access to files, sometimes threatening permanent data erasure unless a ransom is paid. Ransomware is a global issue, with more than 300 million attacks worldwide in 2021. According to the 2022 Unit 42 Ransomware Threat Report, in 2021
394:
The World
Economic Forum’s 2023 Global Risks Report ranks cybercrime as one of the top 10 risks facing the world today and for the next 10 years. If cybercrime were viewed as a nation state, cybercrime would count as the third largest economy in the world. In numbers, cybercrime is predicted to cause
1412:
has a Cyber
Intelligence Section that works to target financial cybercrimes. They combat international cybercrime and work to protect institutions such as banks from intrusions and information breaches. Based in Alabama, the Secret Service and the Alabama Office of Prosecution Services work together
1561:
As cybercrime proliferated, a professional ecosystem evolved to support individuals and groups seeking to profit from cybercrime activities. The ecosystem has become quite specialized, and includes malware developers, botnet operators, professional cybercrime groups, groups specializing in the sale
1070:
A problem that marketplace users sometimes face is exit scamming. That is, a vendor with a high rating acts as if they are selling on the market and have users pay for products they never receive. The vendor then closes their account after receiving money from multiple buyers and never sending what
1594:
for mail is a scalable and inexpensive bulk e-mail-sending service for marketing purposes that could be easily set up for spam. Cloud computing could help cybercriminals leverage their attacks, whether brute-forcing a password, improving the reach of a botnet, or facilitating a spamming campaign.
1429:
The
Department of Homeland Security also instituted the Continuous Diagnostics and Mitigation (CDM) Program. The CDM Program monitors and secures government networks by tracking network risks and informing system personnel so that they can take action. In an attempt to catch intrusions before the
1416:
Investigating cyber crime within the United States and globally often requires partnerships. Within the United States, cyber crime may be investigated by law enforcement, the
Department of Homeland Security, among other federal agencies. However, as the world becomes more dependent on technology,
1042:
Darknet markets have had a rise in traffic in recent years for many reasons, such as the anonymous purchases and often a system of reviews by other buyers. There are many ways in which darknet markets can financially drain individuals. Vendors and customers alike go to great lengths to keep their
1569:
Interpol's Cyber Fusion Center began a collaboration with key cybersecurity players to distribute information on the latest online scams, cyber threats, and risks to internet users. Since 2017, reports on social engineering frauds, ransomware, phishing, and other attacks have been distributed to
1552:
Cybercrime is becoming more of a threat in our society. According to
Accenture's State of Cybersecurity, security attacks increased 31% from 2020 to 2021. The number of attacks per company increased from 206 to 270. Due to this rising threat, the importance of raising awareness about measures to
1352:
Due to cybercriminals using the internet for cross-border attacks and crimes, the process of prosecuting cybercriminals has been difficult. The number of vulnerabilities that a cybercriminal could use as points of opportunity to exploit has also increased over the years. From 2008 to 2014 alone,
1483:
have used deception and subterfuge to catch criminals. For example, two Russian hackers had been evading the FBI for some time. The FBI set up a fake computing company based in Seattle, Washington. They proceeded to lure the two Russian men into the United States by offering them work with this
1312:
Illicit access to camera sensors, microphone sensors, phonebook contacts, all internet-enabled apps, and metadata of mobile telephones running Android and iOS was reportedly provided by Israeli spyware that was found to be in operation in at least 46 nation-states around the world. Journalists,
972:
Cyberbullying has increased drastically with the growing popularity of online social networking. As of January 2020, 44 percent of adult internet users in the United States had "personally experienced online harassment". Online harassment of children often has negative and even life-threatening
1384:
trace; however, that does not necessarily enable detectives to solve a case. Different types of high-tech crime may also include elements of low-tech crime, and vice versa, making cybercrime investigators an indispensable part of modern law enforcement. Methods of cybercrime detective work are
1491:
During President Barack Obama's presidency three cybersecurity related bills were signed into order in December 2014. The first was the Federal Information Security Modernization Act of 2014, the second was the National Cybersecurity Protection Act of 2014, and the third was the Cybersecurity
949:
In the United States, at least 41 states have passed laws and regulations that regard extreme online harassment as a criminal act. These acts can also be prosecuted on the federal level, because of US Code 18 Section 2261A, which states that using computers to threaten or harass can lead to a
609:
climbed 144 percent to $ 2.2 million, and there was an 85 percent increase in the number of victims who had their personal information shown on dark web information dumps. A loss of nearly $ 400 million in 2021 and 2022 is just one of the statistics showing the impact of ransomware attacks on
720:
When an individual is the target of cybercrime, the computer is often the tool rather than the target. These crimes, which typically exploit human weaknesses, usually do not require much technical expertise. These are the types of crimes which have existed for centuries in the offline world.
1071:
was paid for. The vendors, all of whom are involved in illegal activities, have no reason not to engage in exit scamming when they no longer want to be a vendor. In 2019, an entire market known as Wall Street Market allegedly exit scammed, stealing $ 30 million dollars in bitcoin.
774:, or offensive for a variety of reasons. In some instances, it may be illegal. What content is unlawful varies greatly between countries, and even within nations. It is a sensitive area in which the courts can become involved in arbitrating between groups with strong beliefs.
1204:(RBN) was registered as an internet site in 2006. Initially, much of its activity was legitimate. But apparently the founders soon discovered that it was more profitable to host illegitimate activities and to offer its services to criminals. The RBN has been described by
4711:
1035:, which started operations in 2011, was the first major online marketplace for drugs. It was permanently shut down in October 2013 by the FBI and Europol. After Silk Road 2.0 went down, Silk Road 3 Reloaded emerged. However, it was just an older marketplace named
1581:
Hacking has become less complex as hacking communities disseminate their knowledge through the internet. Blogs and social networks have contributed substantially to information sharing, so that beginners can benefit from older hackers' knowledge and advice.
355:
placed cyber crimes into five categories: unauthorized access, damage to computer data or programs, sabotage to hinder the functioning of a computer system or network, unauthorized interception of data within a system or network, and computer espionage.
5060:"Insights into Iranian Cyber Espionage: APT33 Targets Aerospace and Energy Sectors and has Ties to Destructive Malware « Insights into Iranian Cyber Espionage: APT33 Targets Aerospace and Energy Sectors and has Ties to Destructive Malware"
352:
5253:
Herrero, J., Torres, A., Vivas, P., & Urueña, A. (2022). Smartphone Addiction, Social Support, and Cybercrime Victimization: A Discrete Survival and Growth Mixture Model: Psychosocial Intervention. Psychosocial Intervention, 31(1), 59–66.
1589:
era, in order to spam or scam, one needed a variety of resources, such as a dedicated server; skills in server management, network configuration, and network maintenance; and knowledge of internet service provider standards. By comparison, a
2450:
815:; falsification of user characteristics, such as location and browser type; fake social traffic (misleading users on social networks into visiting the advertised website); and fake social media accounts that make a bot appear legitimate.
2726:
1484:
company. Upon completion of the interview, the suspects were arrested. Clever tricks like that are sometimes a necessary part of catching cybercriminals when weak laws and limited international cooperation make it impossible otherwise.
632:
on webcam. Victims are abducted, threatened, or deceived and transferred to "cybersex dens". The dens can be in any location where the cybersex traffickers have a computer, tablet, or phone with an internet connection. Perpetrators use
761:
Phishing is mostly propagated via email. Phishing emails may contain links to other websites that are affected by malware. Or they may contain links to fake online banking or other websites used to steal private account information.
946:, or other high-speed data processing device performing logical, arithmetic, or storage functions, and includes any data storage facility or communications facility directly related to or operating in conjunction with such device."
2696:
4715:
386:
confirmed that organized cybercrime groups are joining forces to commit criminal activities online, while estimating the likelihood of their detection and prosecution to be less than 1 percent in the US. There are also many
1536:
can range from a fine and a short period of jail time for a Class A misdemeanor, such as unauthorized use of a computer, up to 3 to 15 years in prison for a Class C felony, such as computer tampering in the first degree.
968:
is protected by law in most democratic societies, it does not include all types of speech. Spoken or written threats can be criminalized because they harm or intimidate. This applies to online or network-related threats.
4031:
810:
Identity fraud aims to impersonate real users and inflate audience numbers. The techniques used for identity fraud include traffic from bots (coming from a hosting company, a data center, or compromised devices);
1420:
Because cybercriminals commonly use encryption and other techniques to hide their identity and location, it can be difficult to trace a perpetrator after a crime is committed, so prevention measures are crucial.
1342:
tool for the UAE. An investigation revealed that the Emirati government was attempting to track every conversation, movement, relationship, appointment, sound, and image of those who installed the app on their
818:
Attribution fraud impersonates the activities of real users, such as clicks and conversations. Many ad-fraud techniques belong to this category: the use of hijacked and malware-infected devices as part of a
942:
his cellular phone technically is not a computer. Although Kramer tried to argue this point, the U.S. Sentencing Guidelines Manual states that the term "computer" means "an electronic, magnetic, optical,
4489:
1540:
However, some former cybercriminals have been hired as information security experts by private companies due to their inside knowledge of computer crime, a phenomenon which theoretically could create
1441:
has argued that individual companies using a combination of products for security is not a scalable approach and has advocated for the use of cybersecurity technology primarily at the platform level.
1223:
On 2 March 2010, Spanish investigators arrested three men suspected of infecting over 13 million computers around the world. The botnet of infected computers included PCs inside more than half of the
1495:
In April 2015, then-President Barack Obama released an executive order that allows the US to freeze the assets of convicted cybercriminals and block their economic activity within the United States.
4801:
2816:
554:(IT) security specialists have documented a significant increase in network problems and server scams since early 2001. In the United States there is an increasing concern from agencies such as the
5131:
1208:
as "the baddest of the bad". It provides web hosting services and internet access to all kinds of criminal and objectionable activities that earn up to $ 150 million in one year. It specializes in
429:
Computer fraud is the act of using a computer to take or alter electronic data, or to gain unlawful use of a computer or system. Computer fraud that involves the use of the internet is also called
2442:
2756:
3770:
2718:
2636:
1313:
royalty, and government officials were among the targets. Earlier accusations that Israeli weapons companies were meddling in international telephony and smartphones have been eclipsed by the
4612:
3975:
2688:
653:
to hide their identities. Millions of reports of cybersex incidents are sent to authorities annually. New legislation and police procedures are needed to combat this type of cybercrime.
1936:
3269:
2543:
2370:
1509:
It is not only the US and the European Union that have been introducing measures against cybercrime. On 31 May 2017, China announced that its new cybersecurity law was taking effect.
1238:
of child pornography (roughly equivalent to 16,000 DVDs). To date this is the single largest US prosecution of an international child pornography ring; 52 arrests were made worldwide.
3332:
3903:
5067:
7188:
656:
There are an estimated 6.3 million victims of cybersex trafficking, according to a recent report by the International Labour Organization. This number includes about 1.7 million
1286:
On 23 April 2013, the Twitter account of the Associated Press was hacked. The hacker posted a hoax tweet about fictitious attacks on the White House that they claimed left then-
2666:
1267:
website experienced a denial-of-service attack that potentially compromised 70 million customers and 8.5 million active viewers. Other banks thought to be compromised included
953:
Several countries besides the US have also created laws to combat online harassment. In China, a country with over 20 percent of the world's internet users, in response to the
2849:
7939:
7019:
6606:
2595:
4027:
2311:
1408:(DHS) are government agencies that combat cybercrime. The FBI has trained agents and analysts in cybercrime placed in their field offices and headquarters. In the DHS, the
4062:
2960:
3832:
2073:
4005:
4548:
3639:
1431:
3933:
3533:
2905:
1095:
One of the highest-profile banking computer crimes occurred over a course of three years beginning in 1970. The chief teller at the Park Avenue branch of New York's
7029:
6410:
2513:
728:
Fraud and identity theft (although this increasingly uses malware, hacking or phishing, making it an example of "computer as target" as well as "computer as tool")
6248:
5658:
4862:
3767:"DHS: Secretary Napolitano and Attorney General Holder Announce Largest U.S. Prosecution of International Criminal Network Organized to Sexually Exploit Children"
873:
5627:
3209:
1437:
Cybersecurity professionals have been skeptical of prevention-focused strategies. The mode of use of cybersecurity products has also been called into question.
1405:
1245:
experienced a security breach compromising the credit card numbers, personal information, and billing and shipping addresses of as many as 24 million customers.
367:, and other cross-border crimes. Cybercrimes crossing international borders and involving the actions of at least one nation-state are sometimes referred to as
4232:
2573:
5531:
3801:
4481:
694:. Fearing that such attacks may become a normal part of future warfare among nation-states, military commanders see a need to develop cyberspace operations.
2808:
1388:
5139:
4092:
973:
effects. According to a 2021 survey, 41 percent of children develop social anxiety, 37 percent develop depression, and 26 percent have suicidal thoughts.
803:
Ad-frauds are particularly popular among cybercriminals, as such frauds are lucrative and unlikely to be prosecuted. Jean-Loup Richet, a professor at the
5603:
5333:
Csonka P. (2000) Internet Crime; the Draft council of Europe convention on cyber-crime: A response to the challenge of crime in the age of the internet?
4313:
3093:
807:, classified the large variety of ad-frauds committed by cybercriminals into three categories: identity fraud, attribution fraud, and ad-fraud services.
4793:
2786:
2748:
2336:
1966:
5108:
3442:
3119:
570:
Cyberextortion occurs when a website, e-mail server, or computer system is subjected to or threatened with attacks by malicious hackers, often through
7181:
6717:
6202:
5169:
4651:
2628:
3419:
686:, cyberspace has emerged as an arena for national-security threats through several recent events of geostrategic importance, including the attack on
7952:
7153:
6499:
166:
5525:
4604:
3979:
3766:
3389:
433:. The legal definition of computer fraud varies by jurisdiction, but typically involves accessing a computer without permission or authorization.
1110:, and other telephone companies as well as several big credit agencies and two major universities. The damage caused was extensive; one company,
957:
bullying incident, the Legislative Affairs Office of the State Council passed a strict law against cyberbullying. The United Kingdom passed the
6761:
6573:
2400:
1369:). Even when a computer is not directly used for criminal purposes, it may contain records of value to criminal investigators in the form of a
4281:
3508:
3179:
1928:
6729:
6651:
6543:
6179:
5465:
5403:
5364:
5320:
5303:
4910:
4884:
4776:
4694:
3261:
3149:
1648:
1475:
Because of weak laws, cybercriminals operating from developing countries can often evade detection and prosecution. In countries such as the
721:
Criminals have simply been given a tool that increases their pool of potential victims and makes them all the harder to trace and apprehend.
324:
5221:
3824:
3239:
2535:
2362:
2036:
7174:
7014:
6636:
6601:
3324:
3011:
1999:
1321:
575:
4388:
3895:
1067:
domain extensions. To add to privacy, the most prevalent currency on these markets is Bitcoin, which allows transactions to be anonymous.
5617:
4139:
2215:
7828:
6631:
6210:
5607:
5598:
5059:
4943:
4824:
3301:
1766:
1209:
683:
156:
3955:
6241:
5651:
5388:
4825:"Analysis of Directive 2013/40/EU on attacks against information systems in the context of approximation of law at the European level"
4552:
1654:
1620:
929:
755:
293:
2658:
8000:
6456:
6420:
6364:
6142:
4953:
4204:
3718:
2838:
2191:
1892:
1609:
958:
934:
903:
6870:
5034:
3581:
3033:
2882:
2603:
1121:
5004:
4259:
8005:
6989:
6402:
5938:
2483:
2262:
587:
4054:
3468:
2318:
7957:
7893:
7818:
6707:
6192:
2938:
1666:
1480:
1354:
993:
690:'s infrastructure in 2007, allegedly by Russian hackers. In August 2008, Russia again allegedly conducted cyberattacks against
555:
187:
116:
3606:
2952:
2065:
7397:
7054:
6855:
6355:
5311:
4001:
1614:
1143:
infected a document on a victim's computer, then automatically emailed that document and a copy of the virus to other people.
5612:
3748:
3631:
1906:
5524:
Robertson, J. (2 March 2010). Authorities bust 3 in infection of 13m computers. Retrieved 26 March 2010, from Boston News:
4574:
3063:
1004:
was one of the many high-profile female journalists and activists who were targeted. She filed a lawsuit against UAE ruler
7838:
7633:
7247:
6786:
6712:
6234:
6005:
5644:
4429:
3525:
2912:
1125:
288:
283:
5206:
Richet, Jean-Loup (2012). "How to Become a Black Hat Hacker? An Exploratory Study of Barriers to Entry Into Cybercrime".
4459:
4366:
3925:
7522:
7337:
6791:
6391:
5278:
2505:
1833:
1813:
1680:
1660:
1409:
1291:
161:
4852:
3855:
1186:
attacks. On 3 August 2000, Canadian federal prosecutors charged MafiaBoy with 54 counts of illegal access to computers.
1117:
In 1983, a 19-year-old UCLA student used his PC to break into a Defense Department International Communications system.
7387:
6958:
6750:
6539:
6504:
6446:
6359:
6197:
6118:
5918:
4745:
3358:
1521:
1517:
1005:
559:
192:
3201:
5298:", in B. Hebenton, SY Shou, & J. Liu (eds), Asian Handbook of Criminology (pp. 49–64). New York: Springer (
4228:
2565:
1578:
The increasing prevalence of cybercrime has resulted in more attention to computer crime detection and prosecution.
1074:
The FBI has cracked down on these markets. In July 2017, the FBI seized one of the biggest markets, commonly called
7995:
7883:
7873:
7843:
7598:
7482:
6920:
6586:
6521:
6510:
6174:
6132:
5788:
5442:
4161:
Barnard-Wills, David; Ashenden, Debi (21 March 2012). "Securing Virtual Space: Cyber War, Cyber Terror, and Risk".
3793:
3504:
2241:
1792:
1787:
1705:
1385:
dynamic and constantly improving, whether in closed police units or in the framework of international cooperation.
1374:
997:
5380:
7934:
7913:
7858:
7352:
6596:
6035:
5753:
5271:
1636:
954:
391:
concerns surrounding cybercrime when confidential information is intercepted or disclosed, legally or otherwise.
317:
278:
237:
1260:
were compromised. Thirty thousand passwords were cracked, and 1.5 million eHarmony passwords were posted online.
7908:
7713:
7502:
6875:
6745:
6669:
6336:
6331:
6020:
5898:
5793:
4084:
1700:
1695:
1642:
1503:
1201:
1151:
1140:
1048:
1044:
804:
571:
437:
242:
90:
75:
3089:
375:
has said that cybercrime is the "number one problem with mankind" and that it "poses real risks to humanity".
2778:
2340:
1958:
7878:
7733:
7562:
6840:
6734:
6531:
6461:
6380:
6108:
6060:
5723:
5289:
5095:
5090:
3555:
3115:
2443:"IJM Seeks to End Cybersex Trafficking of Children and #RestartFreedom this Cyber Monday and Giving Tuesday"
2285:
1563:
1298:
index, and the temporary suspension of AP's Twitter account. The Dow Jones later restored its session gains.
1096:
1032:
100:
80:
5161:
4635:
7990:
7808:
7572:
7537:
7512:
7392:
7357:
7292:
7039:
6781:
6466:
5327:
5312:
Cybercrime in the Greater China Region: Regulatory Responses and Crime Prevention across the Taiwan Strait
5277:
Bowker, Art (2012) "The Cybercrime Handbook for Community Corrections: Managing Risk in the 21st Century"
3690:
3411:
3381:
1513:
551:
484:
298:
85:
7079:
5295:
3064:"China has more internet users than any other country, according to Mary Meeker's Internet Trends Report"
1463:
Do not give out personal information over the internet unless you can verify that the destination is safe
7964:
7775:
7372:
7362:
7004:
6925:
6880:
6724:
6535:
6484:
6451:
6149:
5883:
5631:
1802:
1782:
1772:
1591:
1434:
approves the private partners that provide intrusion detection and prevention services through the ECS.
1028:
1020:
247:
197:
136:
5395:
2809:"Cybersex trafficking spreads across Southeast Asia, fuelled by internet boom. And the law lags behind"
1132:
between a pan-European hacking group and Newscorp. The original motivation of the hackers was to watch
1039:
that used the Silk Road name in order to get more exposure from the Silk Road brand's earlier success.
624:
Cybersex trafficking is the transportation of victims for such purposes as coerced prostitution or the
5622:
4981:
Feinberg, T (2008). "Whether it happens at school or off-campus, cyberbullying disrupts and affects".
4519:
7848:
7668:
7658:
7527:
7024:
6994:
6568:
6563:
6547:
6257:
6169:
6081:
6030:
5975:
5843:
5816:
5798:
5763:
5696:
5667:
5582:
3960:
1828:
1761:
1710:
1438:
1335:
1136:
reruns in Germany, which was something which Newscorp did not have the copyright permission to allow.
988:
for mass surveillance and a campaign of harassment of prominent activists and journalists, including
977:
778:
619:
408:
379:
310:
217:
212:
202:
151:
3695:
2392:
1102:
A hacking group called MOD (Masters of Deception) allegedly stole passwords and technical data from
50:
7985:
7929:
7603:
7577:
7542:
7467:
7402:
7327:
7049:
6807:
6766:
6659:
6415:
6351:
6346:
5953:
5728:
5686:
4288:
3494:
2422:
Carback, Joshua T. (2018). "Cybersex Trafficking: Toward a More Effective Prosecutorial Response".
1745:
1175:
383:
262:
4917:
4888:
3171:
927:
Committing a crime using a computer can lead to an enhanced sentence. For example, in the case of
7903:
7798:
7738:
7317:
7312:
7131:
6796:
6679:
6626:
6341:
6296:
6286:
6271:
6137:
6065:
5970:
5513:
5229:
4174:
3231:
3141:
2164:
2112:
2025:
1898:
1843:
1818:
1797:
1326:
657:
544:
257:
232:
126:
95:
6494:
5577:
2983:
5266:
Balkin, J., Grimmelmann, J., Katz, E., Kozlovski, N., Wagman, S. & Zarsky, T. (2006) (eds)
4396:
2906:"War is War? The utility of cyberspace operations in the contemporary operational environment."
1988:
1043:
identities a secret while online. Commonly used tools for hiding their online presence include
920:
directs obscenities and derogatory comments at specific individuals, often focusing on gender,
7944:
7653:
7552:
7417:
7069:
6999:
6702:
6558:
6477:
6185:
5943:
5878:
5828:
5775:
5733:
5681:
5505:
5461:
5399:
5384:
5360:
5316:
5299:
5191:
Richet, Jean-Loup (2011). "Adoption of deviant behavior and cybercrime 'Know how' diffusion".
5100:
4949:
4772:
4690:
4643:
4307:
4210:
4200:
4131:
3003:
2207:
2187:
2156:
1888:
1777:
1690:
1685:
1499:
1366:
1314:
1111:
985:
965:
782:
743:
691:
502:
146:
65:
4959:
4835:
3291:
1498:
The European Union adopted cybercrime directive 2013/40/EU, which was elaborated upon in the
501:
Fraud factory is a collection of large fraud organizations usually involving cyber fraud and
7803:
7765:
7693:
7628:
7557:
7547:
7507:
7437:
7377:
7277:
7262:
7257:
7252:
7044:
6935:
6885:
6756:
6692:
6553:
6154:
6094:
5858:
5848:
5743:
5495:
5420:
4682:
4166:
4123:
3700:
3499:
2995:
2146:
2104:
1880:
1808:
1740:
1533:
1393:
1213:
943:
650:
606:
532:
528:
461:
388:
345:
121:
4544:
3262:"'I will not be silenced': Women targeted in hack-and-leak attacks speak out about spyware"
1380:
There are many ways for cybercrime to take place, and investigations tend to start with an
7863:
7833:
7760:
7743:
7608:
7412:
7272:
6740:
6621:
6611:
6319:
6281:
6045:
6025:
5748:
5738:
5431:
1823:
1586:
1397:
1268:
1179:
1024:
885:
840:
812:
715:
472:
404:
341:
252:
70:
5484:"How cybercriminal communities grow and change: An investigation of ad-fraud communities"
3726:
2255:"Botnets, Cybercrime, and Cyberterrorism: Vulnerabilities and Policy Issues for Congress"
2135:"How cybercriminal communities grow and change: An investigation of ad-fraud communities"
1234:
Dreamboard. The website had approximately 600 members and may have distributed up to 123
1031:
messaging tools to communicate with drug mules or potential customers. The dark web site
5026:
4028:"Phone hackers for hire: A peek into the discreet, lucrative business tapped by the FBI"
3873:
3041:
2874:
1178:, along with computers at the University of California at Santa Barbara, were among the
7785:
7770:
7587:
7492:
7472:
7407:
7126:
7074:
7009:
6915:
6910:
6905:
6835:
6817:
6776:
6664:
6578:
6472:
6430:
6276:
6215:
6113:
5963:
5913:
5888:
5853:
5833:
5713:
5701:
5354:
5247:
Cyber Crime. (n.d.). . Federal Bureau of Investigation. Retrieved April 24, 2024, from
4996:
4255:
3704:
1877:
Proceedings of the 1st annual conference on Information security curriculum development
1444:
On a personal level, there are some strategies available to defend against cybercrime:
1231:
1036:
1016:
852:
703:
646:
638:
625:
514:
487:. These types of crimes often result in the loss of personal or financial information.
476:
445:
430:
424:
372:
2475:
2254:
7979:
7898:
7868:
7698:
7497:
7462:
7447:
7302:
7282:
7214:
7034:
6489:
6291:
6125:
6086:
6055:
6050:
5903:
5893:
5863:
5517:
5374:
4178:
3296:
2168:
1838:
1756:
1725:
1257:
989:
844:
836:
661:
536:
527:
committed through the use of cyberspace or computer resources. Acts of disruption of
496:
441:
141:
31:
4945:
The Cybercrime Handbook for Community Corrections: Managing Risk in the 21st Century
2095:
Gordon, Sarah (25 July 2006). "On the definition and classification of cybercrime".
1902:
7888:
7853:
7790:
7728:
7723:
7708:
7678:
7623:
7567:
7477:
7427:
7322:
7287:
7121:
7107:
6930:
6159:
6015:
5718:
5500:
5483:
2930:
2151:
2134:
2116:
1750:
1541:
1287:
1276:
1272:
1230:
In August 2010, the US Department of Homeland Security shut down the international
1224:
1217:
1103:
921:
848:
677:
634:
583:
368:
1448:
Keeping your software and operating system update to benefit from security patches
403:
Computer crime encompasses a broad range of activities, including computer fraud,
359:
Internationally, both state and non-state actors engage in cybercrimes, including
5409:
4358:
353:
United Nations Congress on the Prevention of Crime and the Treatment of Offenders
7813:
7755:
7673:
7663:
7643:
7618:
7532:
7457:
7452:
7442:
7432:
7342:
7267:
7229:
6385:
6099:
5933:
5908:
5873:
5708:
5030:
4605:"Report: 74% of security leaders say that prevention-first strategies will fail"
4582:
1476:
1331:
1264:
1052:
1001:
798:
770:
The content of websites and other electronic communications may be distasteful,
737:
665:
207:
131:
42:
4421:
1430:
damage is done, the DHS created the Enhanced Cybersecurity Services (ECS). The
1377:
are required by law to keep their logfiles for a predetermined amount of time.
7750:
7703:
7648:
7613:
7487:
7422:
7347:
7307:
7297:
7166:
7145:
7112:
7089:
6830:
6616:
6313:
6164:
5980:
5928:
5811:
4451:
2719:"Webcam slavery: tech turns Filipino families into cybersex child traffickers"
2108:
1720:
1381:
1302:
1295:
1242:
1159:
938:
917:
599:
468:
227:
171:
5509:
5104:
4647:
4214:
4170:
4135:
3007:
2629:"Cheap tech and widespread internet access fuel rise in cybersex trafficking"
2160:
1872:
7332:
7117:
7064:
6895:
6890:
6860:
6040:
5995:
5990:
5838:
5806:
1884:
1848:
1357:
received 351,937 complaints of cybercrime, which led to $ 2.7 billion lost.
1339:
1129:
981:
724:
Crimes that use computer networks or devices to advance other ends include:
524:
480:
360:
17:
4737:
3354:
2999:
1454:
Use strong passwords with a variety of characters that aren't easy to guess
340:
encompasses a wide range of criminal activities that are carried out using
4674:
7718:
7688:
7517:
7382:
7367:
7097:
7059:
6963:
6865:
6325:
6000:
5958:
5821:
5396:
Cybercrime and the Victimization of Women: Laws, Rights, and Regulations.
5330:", in M. Gill (ed) Handbook of Security (pp. 321–339). NY: Palgrave.
4686:
4127:
1735:
1631:
1365:
In a criminal investigation, a computer can be a source of evidence (see
1306:
1280:
1253:
1249:
1235:
1205:
1147:
1079:
1075:
1008:
along with other defendants, accusing them of sharing her photos online.
794:
711:
707:
642:
540:
457:
440:
into computers to alter information, distributing malicious code such as
412:
5534:, Latin American's New Security Thinking, Clacso, 2014, pp. 167/182
5248:
4330:
2689:"Global taskforce tackles cybersex child trafficking in the Philippines"
1290:
injured. The hoax tweet resulted in a brief plunge of 130 points in the
467:
Other forms of fraud may be committed using computer systems, including
7224:
6984:
6979:
6953:
6845:
6801:
6641:
6591:
6425:
6226:
6010:
5985:
5948:
5636:
4115:
3670:. Upper Saddle River, New Jersey: Pearson Education Press. p. 150.
1730:
1626:
1370:
1194:
1190:
1163:
1083:
771:
687:
547:, hardware, or programming scripts can all be forms of cyberterrorism.
453:
449:
6583:
Attempting to choke, &c. in order to commit any indictable offence
4116:"Global Cyberspace Is Safer than You Think: Real Trends in Cybercrime"
2839:"Global Estimates of Modern Slavery Forced Labour and Forced Marriage"
1451:
Using anti-virus software that can detect and remove malicious threats
7823:
7683:
6697:
5923:
5868:
5783:
3232:"All the Latest Cyber Bullying Statistics and What They Mean In 2021"
2749:"How the internet fuels sexual exploitation and forced labor in Asia"
1715:
1193:
worm corrupted SCADA microprocessors, particularly the types used in
1155:
1056:
820:
579:
3856:"Cyber attacks against Wells Fargo "significant," handled well: CFO"
3355:"Guide: What is Bitcoin and how does Bitcoin work? - CBBC Newsround"
781:
that has been the target of the strongest efforts at curtailment is
5572:
5410:
Cyber Criminology: Exploring Internet Crimes and Criminal behavior.
5255:
1227:
companies and more than 40 major banks, according to investigators.
7219:
6850:
6825:
4911:"Managing the Risks Posed by Offender Computer Use - Perspectives"
3443:"Did A Bitcoin Exit Scam Cause Dark Web Wall Street Market Crash?"
2066:"Cybercrime To Cost The World $ 9.5 trillion USD annually in 2024"
1604:
1387:
1107:
751:
364:
5476:
International Journal of Technology and Human Interaction (IJTHI)
4681:. Institution of Engineering and Technology. pp. 01 (43 .).
3976:"Researchers find hints of Israeli spyware around globe - SFGate"
3825:"Like LinkedIn, eHarmony is hacked; 1.5 million passwords stolen"
3681:
Mann, David; Sutton, Mike (6 November 2011). ">>Netcrime".
3202:"U.S. internet users who have experienced online harassment 2020"
2596:"Norwegian national, partner nabbed; 4 rescued from cybersex den"
1128:
service was hacked several times during an ongoing technological
7209:
7102:
6771:
6687:
5546:
Cybercrimes: The transformation of crime in the information age,
5027:"Dridex: Tidal waves of spam pushing dangerous financial Trojan"
4857:
3956:"Israeli spyware found on phones in 45 countries, U.S. included"
1183:
1167:
1064:
1060:
933:, the defendant was given an enhanced sentence according to the
629:
7170:
6230:
5640:
5460:(3 November 1999 ed.). Routledge; 1 edition. p. 200.
5132:"This company uses A.I. to stop cyberattacks before they start"
3582:"The Consequences of Mailing Drugs and Other Banned Substances"
2286:"Cybercrime To Cost The World $ 10.5 Trillion Annually By 2025"
1466:
Contact companies about suspicious requests of your information
5594:
4712:"Diffusion and Effects of Cyber Crime in Developing Countries"
1171:
856:
4794:"U.S. Creates First Sanctions Program Against Cybercriminals"
4482:"The Importance of Understanding Encryption in Cybersecurity"
3325:"Council Post: Five Key Reasons Dark Web Markets Are Booming"
2337:"Latest Sony Pictures Breach : A Deadly Cyber Extortion"
5762:
4675:"ICS Threats. A Kaspersky Lab view, predictions and reality"
3896:"Fake Tweet Erasing $ 136 Billion Shows Markets Need Humans"
3292:"We talked to the opportunist imitator behind Silk Road 3.0"
1512:
In Australia, legislation to combat cybercrime includes the
4771:. Nutshell series. St. Paul, MN: West Academic Publishing.
4512:"Continuous Diagnostics and Mitigation Program | CISA"
4511:
2536:"Senator warns of possible surge in child cybersex traffic"
5553:
Virtually Criminal: Crime, Deviance and Regulation Online,
3874:"AP Twitter Hack Falsely Claims Explosions at White House"
3090:"Chinese Authorities Address Online Bullying – Cybersmile"
578:. However, other cyberextortion techniques exist, such as
5412:
Boca Raton, FL, US: CRC Press, Taylor, and Francis Group.
2393:"100+ ransomware statistics for 2023 and beyond - Norton"
5532:
Control, vigilancia y respuesta penal en el ciberespacio
4738:"NIST Cybersecurity Program History and Timeline | CSRC"
3749:"Spanish police crack massive 'zombie computer' network"
1929:"BUFFETT: This is 'the number one problem with mankind'"
916:
Whereas content may be offensive in a non-specific way,
5450:
Information Technology and the Criminal Justice System,
3495:"He Escaped the Dark Web's Biggest Bust. Now He's Back"
1099:
embezzled over $ 1.5 million from hundreds of accounts.
881:
785:, which is illegal in most jurisdictions in the world.
5604:
National Institute of Justice Electronic Crime Program
2363:"The Growing Ransomware Threat: 4 Trends and Insights"
1959:"Warren Buffett: 'Cyber poses real risks to humanity'"
1585:
Furthermore, hacking is cheaper than ever. Before the
1146:
In February 2000, an individual going by the alias of
660:. An example of cybersex trafficking is the 2018–2020
4636:"You Can't Secure 100% of Your Data 100% of the Time"
3632:"Feds Crack Down on Darknet Vendors of Illicit Goods"
2779:"1st Session, 42nd Parliament, Volume 150, Issue 194"
395:
over 9 trillion in damages worldwide in 2024.
5474:
Richet, J.L. (2013) From Young Hackers to Crackers,
5222:"ASEAN Declaration to Prevent and Combat Cybercrime"
2659:"Senate to probe rise in child cybersex trafficking"
1396:
touring the National Computer Forensic Institute in
7922:
7784:
7586:
7238:
7202:
7088:
7020:
Assaulting a constable in the execution of his duty
6972:
6944:
6816:
6678:
6650:
6607:
Assaulting a constable in the execution of his duty
6520:
6439:
6401:
6373:
6305:
6264:
6074:
5774:
5674:
5268:
Cybercrime: Digital Cops in a Networked Environment
4229:"Facts + Statistics: Identity theft and cybercrime"
4002:"Your Smartphone could be running Israeli Spyware!"
2566:"Duterte's drug war and child cybersex trafficking"
5356:DarkMarket : cyberthieves, cybercops, and you
4853:"China's new cybersecurity law takes effect today"
4197:Cybercrime : criminal threats from cyberspace
3607:"Darknet drug vendor sentenced to 10 years prison"
3556:"America's Drug Overdose Epidemic: Data to Action"
2186:(2 ed.). Detroit: Thomson/Gale. p. 137.
7015:Assault with intent to resist lawful apprehension
6602:Assault with intent to resist lawful apprehension
5348:Computer Misuse: Response, regulation and the law
4055:"Israeli firm accused of creating iPhone spyware"
3469:"The golden age of dark web drug markets is over"
2911:. Center for Strategic Leadership. Archived from
1457:Refrain from opening attachments from spam emails
1432:Cyber Security and Infrastructure Security Agency
5328:Cybercrime and establishing a secure cyber world
4997:"The Ultimate List of Cyber Attack Stats (2024)"
4549:Cybersecurity and Infrastructure Security Agency
3926:"Unprecedented cyber attacks wreak global havoc"
3412:"The 'Exit Scam' Is the Darknet's Perfect Crime"
3382:"The 'Exit Scam' Is the Darknet's Perfect Crime"
2024:Heading, Sophie; Zahidi, Saadia (January 2023).
1866:
1864:
924:, religion, nationality, or sexual orientation.
5326:Chang, Lennon Y.C., & Grabosky, P. (2014) "
5294:Broadhurst, R., and Chang, Lennon Y.C. (2013) "
5054:
5052:
3526:"7 Ways the Cops Will Bust You on the Dark Web"
2982:Wilbur, Kenneth C.; Zhu, Yi (24 October 2008).
2506:"Cyber-sex trafficking: A 21st century scourge"
605:the average ransom demand in cases handled by
7182:
6242:
5652:
5359:, New York, NY : Alfred A. Knopf, 2011.
4679:Cyber Security for Industrial Control Systems
4085:"Chat App ToTok Is Spy Tool For UAE – Report"
1334:, a messaging application widely used in the
870:The examples and perspective in this section
827:and scam pages impersonating a famous brand.
318:
8:
2875:"What is 'Nth Room' case and why it matters"
2312:"Cyberextortion by Denial-of-Service Attack"
2026:"The Global Risks Report 2023, 18th Edition"
1879:. New York, NY, USA: ACM. pp. 128–132.
1566:in the future development of cybersecurity.
5539:Computer Crimes and Digital Investigations,
5488:Technological Forecasting and Social Change
4885:"Criminal Justice System for Adults in NYS"
4769:Cybersecurity and privacy law in a nutshell
2184:West's Encyclopedia of American Law, Vol. 3
2139:Technological Forecasting and Social Change
1216:and an alleged operator of the now defunct
754:for commercial purposes (spam) is unlawful
7940:Criminal enterprises, gangs and syndicates
7189:
7175:
7167:
6249:
6235:
6227:
5659:
5645:
5637:
5573:International Journal of Cyber Criminology
4832:Journal of Law and Administrative Sciences
3661:
3659:
3657:
3560:Centers for Disease Control and Prevention
2182:Lehman, Jeffrey; Phelps, Shirelle (2005).
888:, or create a new section, as appropriate.
325:
311:
49:
38:
6203:Security information and event management
5499:
5379:Halder, D., & Jaishankar, K. (2016).
5296:Cybercrime in Asia: trends and challenges
4634:Ghosemajumder, Shuman (4 December 2017).
3694:
2150:
1570:security agencies in over 150 countries.
1532:Penalties for computer-related crimes in
1154:against high-profile websites, including
904:Learn how and when to remove this message
641:, dating pages, online chat rooms, apps,
6569:Wounding or causing grievous bodily harm
5394:Halder, D., & Jaishankar, K. (2011)
5342:Computer Crime Investigation and the Law
4539:
4537:
2470:
2468:
1294:, the removal of $ 136 billion from the
27:Type of crime based in computer networks
4767:Kesan, Jay P.; Hayes, Carol M. (2019).
4545:"Enhanced Cybersecurity Services (ECS)"
3511:from the original on 23 September 2021.
2623:
2621:
2128:
2126:
1860:
270:
179:
108:
57:
41:
6762:Preventing the lawful burial of a body
6574:Assault occasioning actual bodily harm
5417:Understanding and Managing Cybercrime,
5111:from the original on 20 September 2018
4432:from the original on 16 September 2017
4312:: CS1 maint: archived copy as title (
4305:
4008:from the original on 24 September 2018
3520:
3518:
2729:from the original on 12 September 2018
2265:from the original on 29 September 2022
2005:from the original on 27 September 2023
1998:. 15th Edition: 102. 15 January 2020.
1871:Sukhai, Nataliya B. (8 October 2004).
1460:Do not click on links from spam emails
1404:In the United States, the FBI and the
6730:Incitement to ethnic or racial hatred
6180:Host-based intrusion detection system
5458:Hackers: Crime in the Digital Sublime
5249:https://www.fbi.gov/investigate/cyber
4555:from the original on 23 February 2023
4416:
4414:
4353:
4351:
4325:
4323:
4262:from the original on 17 December 2018
4190:
4188:
4095:from the original on 27 December 2019
3493:Greenberg, Andy (23 September 2021).
3467:Brandom, Russell (17 February 2019).
2855:from the original on 22 December 2022
2669:from the original on 13 November 2019
2639:from the original on 24 November 2020
645:sites, and other platforms. They use
7:
7839:High-yield investment program (HYIP)
6637:Offences Against the Person Act 1861
5089:Janofsky, Adam (19 September 2018).
4492:from the original on 4 December 2019
4256:"Mandatory Data Retention Worldwide"
3835:from the original on 28 October 2018
3668:Current Controversies in Criminology
2929:Joseph, Aghatise E. (28 June 2006).
2335:Mohanta, Abhijit (6 December 2014).
2133:Richet, Jean-Loup (1 January 2022).
2076:from the original on 1 February 2024
2059:
2057:
2042:from the original on 5 February 2024
1212:for resale. It is the originator of
742:Propagation of illegal, obscene, or
576:distributed denial-of-service attack
7829:Foundation for New Era Philanthropy
6211:Runtime application self-protection
5608:United States Department of Justice
5599:United States Department of Justice
5381:Cyber Crimes against Women in India
5091:"How AI Can Help Stop Cyberattacks"
5070:from the original on 6 October 2019
5037:from the original on 6 January 2024
4654:from the original on 28 August 2023
3854:Rothacker, Rick (12 October 2012).
3823:Rodriguez, Salvador (6 June 2012).
3725:. 30 September 2007. Archived from
3304:from the original on 5 October 2016
3142:"Malicious Communications Act 1988"
3014:from the original on 5 October 2022
2789:from the original on 27 August 2021
2218:from the original on 10 August 2022
1767:Immigration and Customs Enforcement
1301:In May 2017, 74 countries logged a
586:. An example of cyberextortion was
5335:Computer Law & Security Report
5286:Law in an Era of Smart Technology,
5279:Charles C. Thomas Publishers, Ltd.
5228:. 14 November 2017. Archived from
5172:from the original on 28 April 2023
5007:from the original on 23 March 2024
4199:. Santa Barbara, Calif.: Praeger.
4053:Beaumont, Peter (26 August 2016).
3906:from the original on 23 April 2013
3804:from the original on 18 April 2012
3705:10.1093/oxfordjournals.bjc.a014232
3380:Christian, Jon (4 February 2015).
3272:from the original on 1 August 2021
3242:from the original on 23 April 2021
2941:from the original on 18 July 2024.
2759:from the original on 29 April 2020
2699:from the original on 16 April 2019
2546:from the original on 18 April 2020
2453:from the original on 17 April 2017
2284:cybercrimemag (21 February 2018).
1655:National White Collar Crime Center
1621:Cyber Crime Unit (Hellenic Police)
930:United States v. Neil Scott Kramer
746:, including harassment and threats
180:Subfields and other major theories
25:
6143:Security-focused operating system
5623:Australian High Tech Crime Centre
5613:FBI Cyber Investigators home page
4865:from the original on 18 July 2024
4804:from the original on 18 July 2024
4748:from the original on 18 July 2024
4615:from the original on 28 July 2022
4575:"Detection and Prevention | CISA"
4522:from the original on 6 April 2022
4462:from the original on 18 July 2024
4369:from the original on 18 July 2024
4235:from the original on 18 July 2024
4142:from the original on 18 July 2024
4065:from the original on 18 July 2024
3936:from the original on 18 July 2024
3773:from the original on 17 June 2023
3642:from the original on 14 July 2020
3536:from the original on 15 July 2020
3422:from the original on 24 June 2020
3392:from the original on 18 July 2024
3361:from the original on 7 April 2023
3335:from the original on 29 July 2020
3212:from the original on 18 July 2024
3182:from the original on 18 July 2024
3152:from the original on 18 July 2024
3122:from the original on 18 July 2024
3096:from the original on 18 July 2024
3034:"Federal CyberStalking Bill Info"
2963:from the original on 5 March 2016
2846:International Labour Organization
2516:from the original on 18 July 2013
2403:from the original on 18 July 2024
2373:from the original on 18 July 2024
2212:LII / Legal Information Institute
1909:from the original on 18 July 2024
1762:Economic and industrial espionage
1610:Australian High Tech Crime Centre
935:U.S. Sentencing Guidelines Manual
7030:Encouraging or assisting a crime
6990:Perverting the course of justice
6411:Encouraging or assisting a crime
5939:Insecure direct object reference
5618:US Secret Service Computer Fraud
5541:Oxford: Oxford University Press.
5256:https://doi.org/10.5093/pi2022a3
4034:from the original on 16 May 2017
3876:. Samantha Murphy. 23 April 2013
3792:Li, David K. (17 January 2012).
3116:"Legal Perspective – Cybersmile"
2904:Murphy, Dennis (February 2010).
2885:from the original on 19 May 2020
2819:from the original on 16 May 2020
2576:from the original on 22 May 2020
2486:from the original on 21 May 2020
1969:from the original on 2 June 2023
1939:from the original on 9 June 2023
1617:, a wing of Mumbai Police, India
1522:Enhancing Online Safety Act 2015
1315:2018 Pegasus spyware revelations
1124:satellite pay-to-view encrypted
980:was found to have purchased the
861:
750:The unsolicited sending of bulk
436:Forms of computer fraud include
7894:Saradha Group financial scandal
7154:History of English criminal law
7045:Obstruction of a police officer
6708:Fear or provocation of violence
6193:Information security management
5428:The Encyclopedia of Cybercrime,
4916:. December 2011. Archived from
4823:Moise, Adrian Cristian (2015).
4452:"Combatting Cyber Crime | CISA"
4363:Department of Homeland Security
4335:Federal Bureau of Investigation
1623:, established in Greece in 2004
1406:Department of Homeland Security
1355:Internet Crime Complaint Center
1114:, suffered losses of $ 370,000.
1045:virtual private networks (VPNs)
556:Federal Bureau of Investigation
531:and personal computers through
485:theft of classified information
7055:Refusing to assist a constable
6871:Taking without owner's consent
5501:10.1016/j.techfore.2021.121282
5383:. New Delhi: SAGE Publishing.
4792:Northam, Jackie (April 2015).
3683:British Journal of Criminology
2152:10.1016/j.techfore.2021.121282
2064:Freeze, Di (12 October 2023).
1669:- Japan National Police Agency
1663:- Korea National Police Agency
1615:Cyber Crime Investigation Cell
1256:were attacked, and 65 million
937:§2G1.3(b)(3) for his use of a
1:
7248:1992 Indian stock market scam
7075:Fabrication of false evidence
6787:Misconduct in a public office
6713:Harassment, alarm or distress
6287:Regulatory (lowered mens rea)
5583:Countering ransomware attacks
5578:Common types of cyber attacks
5408:Jaishankar, K. (Ed.) (2011).
5398:Hershey, PA, US: IGI Global.
5315:. Cheltenham: Edward Elgar. (
4254:Zehra Ali (21 January 2018).
2208:"Computer and Internet Fraud"
1989:"The Global Risk Report 2020"
1184:distributed denial-of-service
7523:Strip search phone call scam
7338:Extraterrestrial real estate
6792:Misfeasance in public office
6392:Ignorantia juris non excusat
5628:UK National Cyber Crime Unit
5162:"Cybercrime threat response"
2602:. 1 May 2020. Archived from
2097:Journal in Computer Virology
1834:United States Secret Service
1814:Police National E-Crime Unit
1681:Computer Fraud and Abuse Act
1661:Cyber Terror Response Center
1292:Dow Jones Industrial Average
959:Malicious Communications Act
950:sentence of up to 20 years.
766:Obscene or offensive content
7398:Intellectual property scams
7388:Indian coal allocation scam
7197:Scams and confidence tricks
6959:Cheating the public revenue
6751:Effecting a public mischief
6597:Assault with intent to rape
6198:Information risk management
6119:Multi-factor authentication
5675:Related security categories
1649:National Special Crime Unit
1518:Telecommunications Act 1997
1006:Mohamed bin Zayed Al Nahyan
884:, discuss the issue on the
560:Central Intelligence Agency
8022:
7884:Pyramid schemes in Albania
7844:Investors Overseas Service
7776:Website reputation ratings
7035:Escape from lawful custody
6921:Fraud by abuse of position
6587:Assault with intent to rob
6511:Category:Criminal defences
6175:Intrusion detection system
6133:Computer security software
5789:Advanced persistent threat
4195:Brenner, Susan W. (2010).
3769:. Dhs.gov. 3 August 2011.
1793:List of computer criminals
1788:Legal aspects of computing
1706:Cybercrime countermeasures
1375:Internet Service Providers
1120:Between 1995 and 1998 the
1059:as opposed to the typical
834:
792:
701:
675:
628:of coerced sexual acts or
617:
597:
512:
494:
422:
29:
7914:Welsh Thrasher faith scam
7859:Madoff investment scandal
7353:Foreclosure rescue scheme
7151:For obsolete aspects see
7140:
6886:Misappropriation of funds
6818:Offences against property
6500:Diminished responsibility
5760:
5754:Digital rights management
5272:New York University Press
3719:"A walk on the dark side"
2109:10.1007/s11416-006-0015-z
1637:National Cyber Crime Unit
1322:US intelligence officials
1152:denial-of-service attacks
1019:are used to buy and sell
955:Human Flesh Search Engine
572:denial-of-service attacks
550:Government officials and
8001:Organized crime activity
7909:Stanford Financial Group
7714:Russian Business Network
7503:Slavery reparations scam
6973:Offences against justice
6746:Outraging public decency
6670:Sexual Offences Act 2003
6471:inc. participation in a
6381:Lesser included offences
6337:Intention in English law
6332:Intention (criminal law)
5899:Denial-of-service attack
5794:Arbitrary code execution
5452:Thousand Oaks, CA: Sage.
5439:Fighting Computer Crime,
5426:McQuade, S. (ed) (2009)
5193:York Deviancy Conference
4171:10.1177/1206331211430016
3666:Weitzer, Ronald (2003).
3636:www.bankinfosecurity.com
3172:"Criminal Code Act 1995"
2813:South China Morning Post
2753:South China Morning Post
2238:Fighting Computer Crime,
1873:"Hacking and cybercrime"
1701:Convention on Cybercrime
1696:Cloud computing security
1643:National Security Agency
1504:Convention on Cybercrime
1348:Combating computer crime
1202:Russian Business Network
1174:. About 50 computers at
805:Sorbonne Business School
91:Structural functionalism
76:Differential association
30:Not to be confused with
8006:Harassment and bullying
7879:Petters Group Worldwide
6109:Computer access control
6061:Rogue security software
5724:Electromagnetic warfare
5560:Cybercrime and Society,
5443:Charles Scribner's Sons
5290:Oxford University Press
5096:The Wall Street Journal
4948:. Springfield: Thomas.
4640:Harvard Business Review
4359:"Combating Cyber Crime"
4120:SSRN Electronic Journal
3505:Condé Nast Publications
2931:"Cybercrime definition"
2242:Charles Scribner's Sons
1885:10.1145/1059524.1059553
1667:Cyber Police Department
1639:, in the United Kingdom
1564:artificial intelligence
1210:personal identity theft
1197:centrifuge controllers.
1097:Union Dime Savings Bank
101:Symbolic interactionism
81:Integrative criminology
7573:White van speaker scam
7538:Technical support scam
7513:SSA impersonation scam
7468:Redemption/A4V schemes
7393:IRS impersonation scam
7358:Foreign exchange fraud
7090:Other common law areas
7040:Obstruction of justice
6782:Accessory (legal term)
6544:Corporate manslaughter
6155:Obfuscation (software)
5884:Browser Helper Objects
5768:
5309:Chang, L.Y. C. (2012)
4114:Jardine, Eric (2015).
3176:www.legislation.gov.au
3146:www.legislation.gov.uk
3000:10.1287/mksc.1080.0397
2935:www.crime-research.org
2476:"Cybersex Trafficking"
2259:www.everycrsreport.com
1657:, in the United States
1645:, in the United States
1514:Criminal Code Act 1995
1401:
1281:PNC Financial Services
1263:In December 2012, the
1139:On 26 March 1999, the
682:According to the U.S.
647:online payment systems
552:information technology
380:World Economic Forum's
86:Rational choice theory
7373:Get-rich-quick scheme
7363:Fortune telling fraud
7005:Misprision of treason
6926:Conspiracy to defraud
6881:Handling stolen goods
6725:Public Order Act 1986
6680:Public order offences
6150:Data-centric security
6031:Remote access trojans
5766:
5632:National Crime Agency
5482:Richet, J.L. (2022).
5456:Taylor, Paul (1999).
4673:Nikishin, A. (2015).
4426:www.secretservice.gov
3794:"Zappos cyber attack"
2815:. 11 September 2019.
2424:Criminal Law Bulletin
1803:National Crime Agency
1783:Internet suicide pact
1773:Initial access broker
1592:software-as-a-service
1391:
1373:. In many countries,
1182:sending pings in the
756:in some jurisdictions
684:Department of Defense
588:the Sony Hack of 2014
198:Biosocial criminology
137:Uniform Crime Reports
7849:Kapa investment scam
7669:Internet vigilantism
7659:Email authentication
7634:Cryptocurrency scams
7528:Swampland in Florida
7025:Harboring a fugitive
6995:Witness intimidation
6945:Forgery, personation
6564:Concealment of birth
6258:English criminal law
6082:Application security
5976:Privilege escalation
5844:Cross-site scripting
5697:Cybersex trafficking
5668:Information security
5589:Government resources
5551:Williams, M. (2006)
5369:Grabosky, P. (2006)
5346:Fafinski, S. (2009)
5142:on 20 September 2018
5033:. 16 February 2016.
4942:Bowker, Art (2012).
4687:10.1049/ic.2015.0003
4128:10.2139/ssrn.2634590
4091:. 27 December 2019.
4089:Silicon UK Tech News
3982:on 24 September 2018
3961:The Washington Times
3068:World Economic Forum
2665:. 11 November 2019.
2449:. 28 November 2016.
2343:on 25 September 2015
2033:World Economic Forum
1996:World Economic Forum
1829:Trespass to chattels
1711:Cyber defamation law
1574:Spread of cybercrime
1439:Shuman Ghosemajumder
1336:United Arab Emirates
978:United Arab Emirates
882:improve this section
872:may not represent a
779:internet pornography
620:Cybersex trafficking
614:Cybersex trafficking
409:cybersex trafficking
7953:Film and television
7674:Lenny anti-scam bot
7578:Work-at-home scheme
7543:Telemarketing fraud
7403:Kansas City Shuffle
7328:Embarrassing cheque
7080:Rescuing a prisoner
7050:Wasting police time
6808:Dereliction of duty
6767:Breach of the peace
6485:Prevention of crime
6347:Criminal negligence
5729:Information warfare
5687:Automotive security
5448:Pattavina, A. (ed)
5415:McQuade, S. (2006)
5340:Easttom, C. (2010)
5284:Brenner, S. (2007)
5003:. 7 February 2022.
4891:on 17 December 2018
4841:on 8 December 2015.
4486:Florida Tech Online
4399:on 31 December 2019
3729:on 10 November 2007
3418:. 4 February 2015.
3300:. 7 November 2014.
3236:BroadbandSearch.net
2663:The Philippine Star
2572:. 18 October 2019.
2540:The Philippine Star
2290:Cybercrime Magazine
2070:Cybercrime Magazine
1746:Electronic evidence
1542:perverse incentives
1305:cybercrime called "
1176:Stanford University
731:Information warfare
698:Computers as a tool
384:Global Risks Report
351:In 2000, the tenth
263:Radical criminology
7904:Scott W. Rothstein
7799:Aman Futures Group
7318:Coin rolling scams
7313:Coin-matching game
7146:English law portal
7132:Criminal procedure
6797:Abuse of authority
6627:False imprisonment
6478:Medical procedures
6306:Elements of crimes
6138:Antivirus software
6006:Social engineering
5971:Polymorphic engine
5924:Fraudulent dialers
5829:Hardware backdoors
5769:
5555:Routledge, London.
5548:Cambridge: Polity.
5544:Wall, D.S. (2007)
5537:Walden, I. (2007)
5494:(121282): 121282.
5350:Cullompton: Willan
5208:17th AIM Symposium
5130:Noyes, Katherine.
4923:on 5 November 2013
4718:on 18 October 2015
4585:on 7 November 2019
4488:. 18 August 2016.
4004:. September 2018.
3586:www.cottenfirm.com
2367:Palo Alto Networks
2145:(121282): 121282.
1844:White-collar crime
1819:Protected computer
1798:Metasploit Project
1402:
1327:The New York Times
1320:In December 2019,
1150:began a series of
1021:recreational drugs
984:'s mobile spyware
545:malicious software
523:refers to acts of
96:Subcultural theory
7996:Computer security
7973:
7972:
7935:Confidence tricks
7654:Domain name scams
7553:Thai zig zag scam
7418:Miracle cars scam
7241:confidence tricks
7239:Notable scams and
7164:
7163:
7070:Contempt of court
7000:Witness tampering
6718:intent aggravates
6703:Unlawful assembly
6559:Child destruction
6403:Inchoate offences
6265:Classes of crimes
6224:
6223:
6186:Anomaly detection
6091:Secure by default
5944:Keystroke loggers
5879:Drive-by download
5767:vectorial version
5734:Internet security
5682:Computer security
5467:978-0-415-18072-6
5421:Allyn & Bacon
5404:978-1-60960-830-9
5371:Electronic Crime,
5365:978-0-307-59293-4
5321:978-0-85793-667-7
5304:978-1-4614-5217-1
4778:978-1-63460-272-3
4696:978-1-78561-010-3
4611:. 26 April 2022.
4393:www.ncfi.usss.gov
4163:Space and Culture
4030:. 29 April 2016.
3902:. 23 April 2013.
3829:Los Angeles Times
3044:on 6 January 2020
3038:www.haltabuse.org
2988:Marketing Science
2918:on 20 March 2012.
2881:. 24 April 2020.
2785:. 18 April 2018.
2695:. 15 April 2019.
2542:. 13 April 2020.
2369:. 25 March 2022.
1965:. 30 April 2019.
1963:finance.yahoo.com
1778:Internet homicide
1691:Computer trespass
1686:Computer security
1500:Council of Europe
1367:digital forensics
1241:In January 2012,
1112:Southwestern Bell
1090:Notable incidents
966:freedom of speech
914:
913:
906:
831:Online harassment
783:child pornography
744:offensive content
639:video conferences
610:everyday people.
529:computer networks
503:human trafficking
462:advance-fee scams
335:
334:
147:Positivist school
16:(Redirected from
8013:
7804:Bernard Cornfeld
7766:Stock Generation
7694:Referer spoofing
7558:Three-card monte
7548:Thai tailor scam
7508:Spanish Prisoner
7438:Overpayment scam
7378:Green goods scam
7278:Black money scam
7263:Art student scam
7258:Advance-fee scam
7253:2G spectrum case
7191:
7184:
7177:
7168:
6936:Webcam blackmail
6757:disorderly house
6693:Violent disorder
6554:Unlawful killing
6522:Offences against
6360:Strict liability
6251:
6244:
6237:
6228:
6095:Secure by design
6026:Hardware Trojans
5859:History sniffing
5849:Cross-site leaks
5744:Network security
5661:
5654:
5647:
5638:
5521:
5503:
5471:
5437:Parker D (1983)
5242:
5241:
5239:
5237:
5218:
5212:
5211:
5203:
5197:
5196:
5188:
5182:
5181:
5179:
5177:
5166:www.interpol.int
5158:
5152:
5151:
5149:
5147:
5138:. Archived from
5127:
5121:
5120:
5118:
5116:
5086:
5080:
5079:
5077:
5075:
5056:
5047:
5046:
5044:
5042:
5023:
5017:
5016:
5014:
5012:
5001:Exploding Topics
4993:
4987:
4986:
4978:
4972:
4971:
4969:
4967:
4958:. Archived from
4939:
4933:
4932:
4930:
4928:
4922:
4915:
4907:
4901:
4900:
4898:
4896:
4887:. Archived from
4881:
4875:
4874:
4872:
4870:
4849:
4843:
4842:
4840:
4834:. Archived from
4829:
4820:
4814:
4813:
4811:
4809:
4789:
4783:
4782:
4764:
4758:
4757:
4755:
4753:
4734:
4728:
4727:
4725:
4723:
4714:. Archived from
4707:
4701:
4700:
4670:
4664:
4663:
4661:
4659:
4631:
4625:
4624:
4622:
4620:
4601:
4595:
4594:
4592:
4590:
4581:. Archived from
4571:
4565:
4564:
4562:
4560:
4541:
4532:
4531:
4529:
4527:
4508:
4502:
4501:
4499:
4497:
4478:
4472:
4471:
4469:
4467:
4448:
4442:
4441:
4439:
4437:
4418:
4409:
4408:
4406:
4404:
4395:. Archived from
4385:
4379:
4378:
4376:
4374:
4365:. 19 June 2012.
4355:
4346:
4345:
4343:
4341:
4327:
4318:
4317:
4311:
4303:
4301:
4299:
4294:on 19 March 2015
4293:
4287:. Archived from
4286:
4278:
4272:
4271:
4269:
4267:
4251:
4245:
4244:
4242:
4240:
4225:
4219:
4218:
4192:
4183:
4182:
4158:
4152:
4151:
4149:
4147:
4111:
4105:
4104:
4102:
4100:
4081:
4075:
4074:
4072:
4070:
4050:
4044:
4043:
4041:
4039:
4024:
4018:
4017:
4015:
4013:
3998:
3992:
3991:
3989:
3987:
3978:. Archived from
3972:
3966:
3965:
3952:
3946:
3945:
3943:
3941:
3922:
3916:
3915:
3913:
3911:
3892:
3886:
3885:
3883:
3881:
3870:
3864:
3863:
3851:
3845:
3844:
3842:
3840:
3820:
3814:
3813:
3811:
3809:
3789:
3783:
3782:
3780:
3778:
3763:
3757:
3756:
3745:
3739:
3738:
3736:
3734:
3715:
3709:
3708:
3698:
3678:
3672:
3671:
3663:
3652:
3651:
3649:
3647:
3628:
3622:
3621:
3619:
3617:
3603:
3597:
3596:
3594:
3592:
3578:
3572:
3571:
3569:
3567:
3552:
3546:
3545:
3543:
3541:
3532:. 26 June 2016.
3522:
3513:
3512:
3490:
3484:
3483:
3481:
3479:
3464:
3458:
3457:
3455:
3453:
3438:
3432:
3431:
3429:
3427:
3408:
3402:
3401:
3399:
3397:
3377:
3371:
3370:
3368:
3366:
3351:
3345:
3344:
3342:
3340:
3320:
3314:
3313:
3311:
3309:
3288:
3282:
3281:
3279:
3277:
3258:
3252:
3251:
3249:
3247:
3228:
3222:
3221:
3219:
3217:
3198:
3192:
3191:
3189:
3187:
3168:
3162:
3161:
3159:
3157:
3138:
3132:
3131:
3129:
3127:
3112:
3106:
3105:
3103:
3101:
3086:
3080:
3079:
3077:
3075:
3060:
3054:
3053:
3051:
3049:
3040:. Archived from
3030:
3024:
3023:
3021:
3019:
2979:
2973:
2972:
2970:
2968:
2949:
2943:
2942:
2926:
2920:
2919:
2917:
2910:
2901:
2895:
2894:
2892:
2890:
2871:
2865:
2864:
2862:
2860:
2854:
2843:
2835:
2829:
2828:
2826:
2824:
2805:
2799:
2798:
2796:
2794:
2783:Senate of Canada
2775:
2769:
2768:
2766:
2764:
2745:
2739:
2738:
2736:
2734:
2725:. 17 June 2018.
2715:
2709:
2708:
2706:
2704:
2685:
2679:
2678:
2676:
2674:
2655:
2649:
2648:
2646:
2644:
2635:. 30 June 2018.
2625:
2616:
2615:
2613:
2611:
2592:
2586:
2585:
2583:
2581:
2562:
2556:
2555:
2553:
2551:
2532:
2526:
2525:
2523:
2521:
2512:. 18 July 2013.
2502:
2496:
2495:
2493:
2491:
2472:
2463:
2462:
2460:
2458:
2439:
2433:
2431:
2419:
2413:
2412:
2410:
2408:
2389:
2383:
2382:
2380:
2378:
2359:
2353:
2352:
2350:
2348:
2339:. Archived from
2332:
2326:
2325:
2323:
2317:. Archived from
2316:
2307:
2301:
2300:
2298:
2296:
2281:
2275:
2274:
2272:
2270:
2251:
2245:
2236:Parker D (1983)
2234:
2228:
2227:
2225:
2223:
2204:
2198:
2197:
2179:
2173:
2172:
2154:
2130:
2121:
2120:
2092:
2086:
2085:
2083:
2081:
2061:
2052:
2051:
2049:
2047:
2041:
2030:
2021:
2015:
2014:
2012:
2010:
2004:
1993:
1985:
1979:
1978:
1976:
1974:
1955:
1949:
1948:
1946:
1944:
1933:Business Insider
1925:
1919:
1918:
1916:
1914:
1868:
1809:Penetration test
1741:Domain hijacking
1394:Tommy Tuberville
1180:zombie computers
1025:drug traffickers
1012:Drug trafficking
909:
902:
898:
895:
889:
865:
864:
857:
651:cryptocurrencies
405:financial crimes
327:
320:
313:
122:Crime statistics
53:
39:
21:
8021:
8020:
8016:
8015:
8014:
8012:
8011:
8010:
7976:
7975:
7974:
7969:
7918:
7864:Make Money Fast
7834:Franchise fraud
7789:
7780:
7761:Spoofing attack
7744:Scammer Payback
7592:countermeasures
7591:
7582:
7273:Bait-and-switch
7240:
7234:
7198:
7195:
7165:
7160:
7136:
7084:
6968:
6946:
6940:
6856:Criminal damage
6812:
6741:Public nuisance
6674:
6652:Sexual offences
6646:
6622:Child abduction
6523:
6516:
6462:Loss of control
6435:
6397:
6369:
6301:
6260:
6255:
6225:
6220:
6070:
5770:
5758:
5749:Copy protection
5739:Mobile security
5670:
5665:
5591:
5569:
5558:Yar, M. (2006)
5481:
5468:
5455:
5432:Greenwood Press
5263:
5261:Further reading
5245:
5235:
5233:
5220:
5219:
5215:
5205:
5204:
5200:
5190:
5189:
5185:
5175:
5173:
5160:
5159:
5155:
5145:
5143:
5129:
5128:
5124:
5114:
5112:
5088:
5087:
5083:
5073:
5071:
5058:
5057:
5050:
5040:
5038:
5025:
5024:
5020:
5010:
5008:
4995:
4994:
4990:
4980:
4979:
4975:
4965:
4963:
4962:on 2 April 2015
4956:
4941:
4940:
4936:
4926:
4924:
4920:
4913:
4909:
4908:
4904:
4894:
4892:
4883:
4882:
4878:
4868:
4866:
4851:
4850:
4846:
4838:
4827:
4822:
4821:
4817:
4807:
4805:
4791:
4790:
4786:
4779:
4766:
4765:
4761:
4751:
4749:
4736:
4735:
4731:
4721:
4719:
4709:
4708:
4704:
4697:
4672:
4671:
4667:
4657:
4655:
4633:
4632:
4628:
4618:
4616:
4603:
4602:
4598:
4588:
4586:
4573:
4572:
4568:
4558:
4556:
4543:
4542:
4535:
4525:
4523:
4510:
4509:
4505:
4495:
4493:
4480:
4479:
4475:
4465:
4463:
4450:
4449:
4445:
4435:
4433:
4422:"Investigation"
4420:
4419:
4412:
4402:
4400:
4387:
4386:
4382:
4372:
4370:
4357:
4356:
4349:
4339:
4337:
4329:
4328:
4321:
4304:
4297:
4295:
4291:
4284:
4282:"Archived copy"
4280:
4279:
4275:
4265:
4263:
4253:
4252:
4248:
4238:
4236:
4227:
4226:
4222:
4207:
4194:
4193:
4186:
4160:
4159:
4155:
4145:
4143:
4113:
4112:
4108:
4098:
4096:
4083:
4082:
4078:
4068:
4066:
4052:
4051:
4047:
4037:
4035:
4026:
4025:
4021:
4011:
4009:
4000:
3999:
3995:
3985:
3983:
3974:
3973:
3969:
3954:
3953:
3949:
3939:
3937:
3932:. 13 May 2017.
3924:
3923:
3919:
3909:
3907:
3894:
3893:
3889:
3879:
3877:
3872:
3871:
3867:
3853:
3852:
3848:
3838:
3836:
3822:
3821:
3817:
3807:
3805:
3791:
3790:
3786:
3776:
3774:
3765:
3764:
3760:
3755:. 3 March 2010.
3747:
3746:
3742:
3732:
3730:
3717:
3716:
3712:
3696:10.1.1.133.3861
3680:
3679:
3675:
3665:
3664:
3655:
3645:
3643:
3630:
3629:
3625:
3615:
3613:
3605:
3604:
3600:
3590:
3588:
3580:
3579:
3575:
3565:
3563:
3562:. 24 March 2020
3554:
3553:
3549:
3539:
3537:
3524:
3523:
3516:
3492:
3491:
3487:
3477:
3475:
3466:
3465:
3461:
3451:
3449:
3441:Winder, Davey.
3440:
3439:
3435:
3425:
3423:
3410:
3409:
3405:
3395:
3393:
3379:
3378:
3374:
3364:
3362:
3353:
3352:
3348:
3338:
3336:
3322:
3321:
3317:
3307:
3305:
3290:
3289:
3285:
3275:
3273:
3268:. August 2021.
3260:
3259:
3255:
3245:
3243:
3230:
3229:
3225:
3215:
3213:
3200:
3199:
3195:
3185:
3183:
3170:
3169:
3165:
3155:
3153:
3140:
3139:
3135:
3125:
3123:
3114:
3113:
3109:
3099:
3097:
3088:
3087:
3083:
3073:
3071:
3062:
3061:
3057:
3047:
3045:
3032:
3031:
3027:
3017:
3015:
2981:
2980:
2976:
2966:
2964:
2953:"Save browsing"
2951:
2950:
2946:
2928:
2927:
2923:
2915:
2908:
2903:
2902:
2898:
2888:
2886:
2873:
2872:
2868:
2858:
2856:
2852:
2841:
2837:
2836:
2832:
2822:
2820:
2807:
2806:
2802:
2792:
2790:
2777:
2776:
2772:
2762:
2760:
2747:
2746:
2742:
2732:
2730:
2717:
2716:
2712:
2702:
2700:
2687:
2686:
2682:
2672:
2670:
2657:
2656:
2652:
2642:
2640:
2627:
2626:
2619:
2609:
2607:
2606:on 29 July 2020
2600:Manila Bulletin
2594:
2593:
2589:
2579:
2577:
2564:
2563:
2559:
2549:
2547:
2534:
2533:
2529:
2519:
2517:
2504:
2503:
2499:
2489:
2487:
2474:
2473:
2466:
2456:
2454:
2441:
2440:
2436:
2421:
2420:
2416:
2406:
2404:
2391:
2390:
2386:
2376:
2374:
2361:
2360:
2356:
2346:
2344:
2334:
2333:
2329:
2324:on 6 July 2011.
2321:
2314:
2310:Lepofsky, Ron.
2309:
2308:
2304:
2294:
2292:
2283:
2282:
2278:
2268:
2266:
2253:
2252:
2248:
2235:
2231:
2221:
2219:
2206:
2205:
2201:
2194:
2181:
2180:
2176:
2132:
2131:
2124:
2094:
2093:
2089:
2079:
2077:
2063:
2062:
2055:
2045:
2043:
2039:
2028:
2023:
2022:
2018:
2008:
2006:
2002:
1991:
1987:
1986:
1982:
1972:
1970:
1957:
1956:
1952:
1942:
1940:
1927:
1926:
1922:
1912:
1910:
1895:
1870:
1869:
1862:
1858:
1853:
1824:Techno-thriller
1676:
1601:
1587:cloud computing
1576:
1559:
1550:
1530:
1473:
1427:
1398:Hoover, Alabama
1363:
1350:
1288:President Obama
1269:Bank of America
1258:password hashes
1092:
1037:Diabolus Market
1017:Darknet markets
1014:
994:Princess Latifa
944:electrochemical
910:
899:
893:
890:
879:
866:
862:
855:
841:Online predator
833:
813:cookie stuffing
801:
791:
768:
718:
716:Carding (fraud)
702:Main articles:
700:
680:
674:
622:
616:
602:
596:
568:
517:
511:
499:
493:
456:to steal data,
427:
421:
401:
399:Classifications
365:financial theft
342:digital devices
331:
193:Anthropological
71:Criminalization
66:Conflict theory
35:
28:
23:
22:
15:
12:
11:
5:
8019:
8017:
8009:
8008:
8003:
7998:
7993:
7988:
7978:
7977:
7971:
7970:
7968:
7967:
7962:
7961:
7960:
7955:
7947:
7942:
7937:
7932:
7926:
7924:
7920:
7919:
7917:
7916:
7911:
7906:
7901:
7896:
7891:
7886:
7881:
7876:
7871:
7866:
7861:
7856:
7851:
7846:
7841:
7836:
7831:
7826:
7821:
7816:
7811:
7806:
7801:
7795:
7793:
7782:
7781:
7779:
7778:
7773:
7771:Voice phishing
7768:
7763:
7758:
7753:
7748:
7747:
7746:
7741:
7736:
7731:
7721:
7716:
7711:
7706:
7701:
7696:
7691:
7686:
7681:
7676:
7671:
7666:
7661:
7656:
7651:
7646:
7641:
7636:
7631:
7626:
7621:
7616:
7611:
7606:
7604:Pig Butchering
7601:
7595:
7593:
7588:Internet scams
7584:
7583:
7581:
7580:
7575:
7570:
7565:
7560:
7555:
7550:
7545:
7540:
7535:
7530:
7525:
7520:
7515:
7510:
7505:
7500:
7495:
7493:Sick baby hoax
7490:
7485:
7480:
7475:
7473:Reloading scam
7470:
7465:
7460:
7455:
7450:
7445:
7440:
7435:
7430:
7425:
7420:
7415:
7410:
7408:Locksmith scam
7405:
7400:
7395:
7390:
7385:
7380:
7375:
7370:
7365:
7360:
7355:
7350:
7345:
7340:
7335:
7330:
7325:
7320:
7315:
7310:
7305:
7300:
7295:
7290:
7285:
7280:
7275:
7270:
7265:
7260:
7255:
7250:
7244:
7242:
7236:
7235:
7233:
7232:
7227:
7222:
7217:
7212:
7206:
7204:
7200:
7199:
7196:
7194:
7193:
7186:
7179:
7171:
7162:
7161:
7159:
7158:
7149:
7141:
7138:
7137:
7135:
7134:
7129:
7124:
7115:
7110:
7105:
7100:
7094:
7092:
7086:
7085:
7083:
7082:
7077:
7072:
7067:
7062:
7057:
7052:
7047:
7042:
7037:
7032:
7027:
7022:
7017:
7012:
7010:Jury tampering
7007:
7002:
6997:
6992:
6987:
6982:
6976:
6974:
6970:
6969:
6967:
6966:
6961:
6956:
6950:
6948:
6942:
6941:
6939:
6938:
6933:
6928:
6923:
6918:
6916:Fraud Act 2006
6913:
6911:Theft Act 1978
6908:
6906:Theft Act 1968
6903:
6898:
6893:
6888:
6883:
6878:
6873:
6868:
6863:
6858:
6853:
6848:
6843:
6838:
6836:Cheating (law)
6833:
6828:
6822:
6820:
6814:
6813:
6811:
6810:
6805:
6799:
6794:
6789:
6784:
6779:
6777:Forcible entry
6774:
6769:
6764:
6759:
6753:
6748:
6743:
6737:
6732:
6727:
6722:
6721:
6720:
6710:
6705:
6700:
6695:
6690:
6684:
6682:
6676:
6675:
6673:
6672:
6667:
6665:Sexual assault
6662:
6656:
6654:
6648:
6647:
6645:
6644:
6639:
6634:
6629:
6624:
6619:
6614:
6609:
6604:
6599:
6594:
6589:
6584:
6581:
6579:Common assault
6576:
6571:
6566:
6561:
6556:
6551:
6528:
6526:
6518:
6517:
6515:
6514:
6507:
6502:
6497:
6492:
6487:
6482:
6481:
6480:
6475:
6473:sporting event
6464:
6459:
6454:
6449:
6443:
6441:
6437:
6436:
6434:
6433:
6431:Common purpose
6428:
6423:
6418:
6413:
6407:
6405:
6399:
6398:
6396:
6395:
6388:
6383:
6377:
6375:
6371:
6370:
6368:
6367:
6362:
6349:
6344:
6339:
6334:
6329:
6322:
6317:
6309:
6307:
6303:
6302:
6300:
6299:
6294:
6289:
6284:
6279:
6274:
6268:
6266:
6262:
6261:
6256:
6254:
6253:
6246:
6239:
6231:
6222:
6221:
6219:
6218:
6216:Site isolation
6213:
6208:
6207:
6206:
6200:
6190:
6189:
6188:
6183:
6172:
6167:
6162:
6157:
6152:
6147:
6146:
6145:
6140:
6130:
6129:
6128:
6123:
6122:
6121:
6114:Authentication
6106:
6105:
6104:
6103:
6102:
6092:
6089:
6078:
6076:
6072:
6071:
6069:
6068:
6063:
6058:
6053:
6048:
6043:
6038:
6033:
6028:
6023:
6018:
6013:
6008:
6003:
5998:
5993:
5988:
5983:
5978:
5973:
5968:
5967:
5966:
5956:
5951:
5946:
5941:
5936:
5931:
5926:
5921:
5916:
5914:Email spoofing
5911:
5906:
5901:
5896:
5891:
5886:
5881:
5876:
5871:
5866:
5861:
5856:
5854:DOM clobbering
5851:
5846:
5841:
5836:
5834:Code injection
5831:
5826:
5825:
5824:
5819:
5814:
5809:
5801:
5796:
5791:
5786:
5780:
5778:
5772:
5771:
5761:
5759:
5757:
5756:
5751:
5746:
5741:
5736:
5731:
5726:
5721:
5716:
5714:Cyberterrorism
5711:
5706:
5705:
5704:
5702:Computer fraud
5699:
5689:
5684:
5678:
5676:
5672:
5671:
5666:
5664:
5663:
5656:
5649:
5641:
5635:
5634:
5625:
5620:
5615:
5610:
5601:
5595:Cybercrime.gov
5590:
5587:
5586:
5585:
5580:
5575:
5568:
5567:External links
5565:
5564:
5563:
5556:
5549:
5542:
5535:
5528:
5522:
5479:
5478:, 9(3), 53–62.
5472:
5466:
5453:
5446:
5435:
5430:Westport, CT:
5424:
5413:
5406:
5392:
5389:978-9385985775
5377:
5367:
5351:
5344:
5338:
5331:
5324:
5307:
5292:
5282:
5275:
5262:
5259:
5244:
5243:
5232:on 3 July 2021
5213:
5198:
5183:
5153:
5122:
5081:
5048:
5018:
4988:
4973:
4954:
4934:
4902:
4876:
4844:
4815:
4784:
4777:
4759:
4729:
4710:Kshetri, Nir.
4702:
4695:
4665:
4626:
4596:
4566:
4533:
4503:
4473:
4443:
4410:
4389:"NCFI - About"
4380:
4347:
4319:
4273:
4246:
4220:
4205:
4184:
4153:
4106:
4076:
4045:
4019:
3993:
3967:
3947:
3917:
3887:
3865:
3846:
3815:
3784:
3758:
3740:
3710:
3689:(2): 201–229.
3673:
3653:
3623:
3598:
3573:
3547:
3514:
3485:
3459:
3433:
3403:
3372:
3346:
3323:Arora, Beenu.
3315:
3283:
3253:
3223:
3193:
3163:
3133:
3107:
3081:
3070:. 27 June 2019
3055:
3025:
2994:(2): 293–308.
2974:
2944:
2921:
2896:
2866:
2830:
2800:
2770:
2755:. 2 May 2019.
2740:
2710:
2680:
2650:
2617:
2587:
2570:The ASEAN Post
2557:
2527:
2497:
2464:
2434:
2414:
2384:
2354:
2327:
2302:
2276:
2246:
2229:
2199:
2192:
2174:
2122:
2087:
2053:
2016:
1980:
1950:
1920:
1893:
1859:
1857:
1854:
1852:
1851:
1846:
1841:
1836:
1831:
1826:
1821:
1816:
1811:
1806:
1800:
1795:
1790:
1785:
1780:
1775:
1770:
1764:
1759:
1753:
1748:
1743:
1738:
1733:
1728:
1723:
1718:
1713:
1708:
1703:
1698:
1693:
1688:
1683:
1677:
1675:
1672:
1671:
1670:
1664:
1658:
1652:
1646:
1640:
1634:
1629:
1624:
1618:
1612:
1607:
1600:
1597:
1575:
1572:
1558:
1555:
1549:
1546:
1534:New York State
1529:
1526:
1472:
1469:
1468:
1467:
1464:
1461:
1458:
1455:
1452:
1449:
1426:
1423:
1410:Secret Service
1362:
1359:
1349:
1346:
1345:
1344:
1330:revealed that
1318:
1310:
1299:
1284:
1261:
1248:In June 2012,
1246:
1239:
1232:pedophile ring
1228:
1221:
1198:
1187:
1144:
1137:
1118:
1115:
1100:
1091:
1088:
1013:
1010:
1000:, and others.
912:
911:
876:of the subject
874:worldwide view
869:
867:
860:
853:Internet troll
832:
829:
790:
787:
767:
764:
748:
747:
740:
735:
734:Phishing scams
732:
729:
704:Internet fraud
699:
696:
676:Main article:
673:
670:
626:live streaming
618:Main article:
615:
612:
598:Main article:
595:
592:
567:
566:Cyberextortion
564:
558:(FBI) and the
521:cyberterrorism
515:Cyberterrorism
513:Main article:
510:
509:Cyberterrorism
507:
495:Main article:
492:
489:
477:identity theft
442:computer worms
431:internet fraud
425:Computer fraud
423:Main article:
420:
419:Computer fraud
417:
400:
397:
373:Warren Buffett
333:
332:
330:
329:
322:
315:
307:
304:
303:
302:
301:
296:
291:
286:
281:
273:
272:
268:
267:
266:
265:
260:
255:
250:
248:Organizational
245:
240:
235:
230:
225:
220:
215:
210:
205:
200:
195:
190:
182:
181:
177:
176:
175:
174:
169:
164:
159:
154:
149:
144:
139:
134:
129:
124:
119:
111:
110:
106:
105:
104:
103:
98:
93:
88:
83:
78:
73:
68:
60:
59:
55:
54:
46:
45:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
8018:
8007:
8004:
8002:
7999:
7997:
7994:
7992:
7991:Crime by type
7989:
7987:
7984:
7983:
7981:
7966:
7965:Ponzi schemes
7963:
7959:
7956:
7954:
7951:
7950:
7949:In the media
7948:
7946:
7943:
7941:
7938:
7936:
7933:
7931:
7928:
7927:
7925:
7921:
7915:
7912:
7910:
7907:
7905:
7902:
7900:
7899:Secret Sister
7897:
7895:
7892:
7890:
7887:
7885:
7882:
7880:
7877:
7875:
7872:
7870:
7869:Matrix scheme
7867:
7865:
7862:
7860:
7857:
7855:
7852:
7850:
7847:
7845:
7842:
7840:
7837:
7835:
7832:
7830:
7827:
7825:
7822:
7820:
7817:
7815:
7812:
7810:
7807:
7805:
7802:
7800:
7797:
7796:
7794:
7792:
7791:Ponzi schemes
7787:
7783:
7777:
7774:
7772:
7769:
7767:
7764:
7762:
7759:
7757:
7754:
7752:
7749:
7745:
7742:
7740:
7737:
7735:
7732:
7730:
7727:
7726:
7725:
7722:
7720:
7717:
7715:
7712:
7710:
7707:
7705:
7702:
7700:
7699:Ripoff Report
7697:
7695:
7692:
7690:
7687:
7685:
7682:
7680:
7677:
7675:
7672:
7670:
7667:
7665:
7662:
7660:
7657:
7655:
7652:
7650:
7647:
7645:
7642:
7640:
7637:
7635:
7632:
7630:
7627:
7625:
7622:
7620:
7617:
7615:
7612:
7610:
7607:
7605:
7602:
7600:
7597:
7596:
7594:
7589:
7585:
7579:
7576:
7574:
7571:
7569:
7566:
7564:
7561:
7559:
7556:
7554:
7551:
7549:
7546:
7544:
7541:
7539:
7536:
7534:
7531:
7529:
7526:
7524:
7521:
7519:
7516:
7514:
7511:
7509:
7506:
7504:
7501:
7499:
7498:SIM swap scam
7496:
7494:
7491:
7489:
7486:
7484:
7481:
7479:
7476:
7474:
7471:
7469:
7466:
7464:
7463:Pump and dump
7461:
7459:
7456:
7454:
7451:
7449:
7448:Pig in a poke
7446:
7444:
7441:
7439:
7436:
7434:
7431:
7429:
7426:
7424:
7421:
7419:
7416:
7414:
7411:
7409:
7406:
7404:
7401:
7399:
7396:
7394:
7391:
7389:
7386:
7384:
7381:
7379:
7376:
7374:
7371:
7369:
7366:
7364:
7361:
7359:
7356:
7354:
7351:
7349:
7346:
7344:
7341:
7339:
7336:
7334:
7331:
7329:
7326:
7324:
7321:
7319:
7316:
7314:
7311:
7309:
7306:
7304:
7303:Charity fraud
7301:
7299:
7296:
7294:
7291:
7289:
7286:
7284:
7283:Blessing scam
7281:
7279:
7276:
7274:
7271:
7269:
7266:
7264:
7261:
7259:
7256:
7254:
7251:
7249:
7246:
7245:
7243:
7237:
7231:
7228:
7226:
7223:
7221:
7218:
7216:
7215:Error account
7213:
7211:
7208:
7207:
7205:
7201:
7192:
7187:
7185:
7180:
7178:
7173:
7172:
7169:
7157:
7155:
7150:
7148:
7147:
7143:
7142:
7139:
7133:
7130:
7128:
7125:
7123:
7119:
7116:
7114:
7111:
7109:
7106:
7104:
7101:
7099:
7096:
7095:
7093:
7091:
7087:
7081:
7078:
7076:
7073:
7071:
7068:
7066:
7063:
7061:
7058:
7056:
7053:
7051:
7048:
7046:
7043:
7041:
7038:
7036:
7033:
7031:
7028:
7026:
7023:
7021:
7018:
7016:
7013:
7011:
7008:
7006:
7003:
7001:
6998:
6996:
6993:
6991:
6988:
6986:
6983:
6981:
6978:
6977:
6975:
6971:
6965:
6962:
6960:
6957:
6955:
6952:
6951:
6949:
6943:
6937:
6934:
6932:
6929:
6927:
6924:
6922:
6919:
6917:
6914:
6912:
6909:
6907:
6904:
6902:
6899:
6897:
6894:
6892:
6889:
6887:
6884:
6882:
6879:
6877:
6874:
6872:
6869:
6867:
6864:
6862:
6859:
6857:
6854:
6852:
6849:
6847:
6844:
6842:
6839:
6837:
6834:
6832:
6829:
6827:
6824:
6823:
6821:
6819:
6815:
6809:
6806:
6803:
6800:
6798:
6795:
6793:
6790:
6788:
6785:
6783:
6780:
6778:
6775:
6773:
6770:
6768:
6765:
6763:
6760:
6758:
6754:
6752:
6749:
6747:
6744:
6742:
6738:
6736:
6733:
6731:
6728:
6726:
6723:
6719:
6716:
6715:
6714:
6711:
6709:
6706:
6704:
6701:
6699:
6696:
6694:
6691:
6689:
6686:
6685:
6683:
6681:
6677:
6671:
6668:
6666:
6663:
6661:
6658:
6657:
6655:
6653:
6649:
6643:
6640:
6638:
6635:
6633:
6630:
6628:
6625:
6623:
6620:
6618:
6615:
6613:
6610:
6608:
6605:
6603:
6600:
6598:
6595:
6593:
6590:
6588:
6585:
6582:
6580:
6577:
6575:
6572:
6570:
6567:
6565:
6562:
6560:
6557:
6555:
6552:
6549:
6545:
6541:
6537:
6533:
6530:
6529:
6527:
6525:
6519:
6513:
6512:
6508:
6506:
6503:
6501:
6498:
6496:
6493:
6491:
6490:Lawful excuse
6488:
6486:
6483:
6479:
6476:
6474:
6470:
6469:
6468:
6465:
6463:
6460:
6458:
6455:
6453:
6450:
6448:
6445:
6444:
6442:
6438:
6432:
6429:
6427:
6424:
6422:
6419:
6417:
6414:
6412:
6409:
6408:
6406:
6404:
6400:
6394:
6393:
6389:
6387:
6384:
6382:
6379:
6378:
6376:
6372:
6366:
6363:
6361:
6357:
6353:
6350:
6348:
6345:
6343:
6340:
6338:
6335:
6333:
6330:
6328:
6327:
6323:
6321:
6318:
6316:
6315:
6311:
6310:
6308:
6304:
6298:
6295:
6293:
6290:
6288:
6285:
6283:
6280:
6278:
6275:
6273:
6270:
6269:
6267:
6263:
6259:
6252:
6247:
6245:
6240:
6238:
6233:
6232:
6229:
6217:
6214:
6212:
6209:
6204:
6201:
6199:
6196:
6195:
6194:
6191:
6187:
6184:
6181:
6178:
6177:
6176:
6173:
6171:
6168:
6166:
6163:
6161:
6158:
6156:
6153:
6151:
6148:
6144:
6141:
6139:
6136:
6135:
6134:
6131:
6127:
6126:Authorization
6124:
6120:
6117:
6116:
6115:
6112:
6111:
6110:
6107:
6101:
6098:
6097:
6096:
6093:
6090:
6088:
6087:Secure coding
6085:
6084:
6083:
6080:
6079:
6077:
6073:
6067:
6064:
6062:
6059:
6057:
6056:SQL injection
6054:
6052:
6049:
6047:
6044:
6042:
6039:
6037:
6036:Vulnerability
6034:
6032:
6029:
6027:
6024:
6022:
6021:Trojan horses
6019:
6017:
6016:Software bugs
6014:
6012:
6009:
6007:
6004:
6002:
5999:
5997:
5994:
5992:
5989:
5987:
5984:
5982:
5979:
5977:
5974:
5972:
5969:
5965:
5962:
5961:
5960:
5957:
5955:
5952:
5950:
5947:
5945:
5942:
5940:
5937:
5935:
5932:
5930:
5927:
5925:
5922:
5920:
5917:
5915:
5912:
5910:
5907:
5905:
5904:Eavesdropping
5902:
5900:
5897:
5895:
5894:Data scraping
5892:
5890:
5887:
5885:
5882:
5880:
5877:
5875:
5872:
5870:
5867:
5865:
5864:Cryptojacking
5862:
5860:
5857:
5855:
5852:
5850:
5847:
5845:
5842:
5840:
5837:
5835:
5832:
5830:
5827:
5823:
5820:
5818:
5815:
5813:
5810:
5808:
5805:
5804:
5802:
5800:
5797:
5795:
5792:
5790:
5787:
5785:
5782:
5781:
5779:
5777:
5773:
5765:
5755:
5752:
5750:
5747:
5745:
5742:
5740:
5737:
5735:
5732:
5730:
5727:
5725:
5722:
5720:
5717:
5715:
5712:
5710:
5707:
5703:
5700:
5698:
5695:
5694:
5693:
5690:
5688:
5685:
5683:
5680:
5679:
5677:
5673:
5669:
5662:
5657:
5655:
5650:
5648:
5643:
5642:
5639:
5633:
5629:
5626:
5624:
5621:
5619:
5616:
5614:
5611:
5609:
5605:
5602:
5600:
5596:
5593:
5592:
5588:
5584:
5581:
5579:
5576:
5574:
5571:
5570:
5566:
5562:London: Sage.
5561:
5557:
5554:
5550:
5547:
5543:
5540:
5536:
5533:
5530:Rolón, D. N.
5529:
5527:
5523:
5519:
5515:
5511:
5507:
5502:
5497:
5493:
5489:
5485:
5480:
5477:
5473:
5469:
5463:
5459:
5454:
5451:
5447:
5444:
5440:
5436:
5433:
5429:
5425:
5422:
5418:
5414:
5411:
5407:
5405:
5401:
5397:
5393:
5390:
5386:
5382:
5378:
5376:
5375:Prentice Hall
5372:
5368:
5366:
5362:
5358:
5357:
5352:
5349:
5345:
5343:
5339:
5336:
5332:
5329:
5325:
5322:
5318:
5314:
5313:
5308:
5305:
5301:
5297:
5293:
5291:
5287:
5283:
5280:
5276:
5273:
5269:
5265:
5264:
5260:
5258:
5257:
5251:
5250:
5231:
5227:
5223:
5217:
5214:
5209:
5202:
5199:
5194:
5187:
5184:
5171:
5167:
5163:
5157:
5154:
5141:
5137:
5136:Computerworld
5133:
5126:
5123:
5110:
5106:
5102:
5098:
5097:
5092:
5085:
5082:
5069:
5065:
5061:
5055:
5053:
5049:
5036:
5032:
5028:
5022:
5019:
5006:
5002:
4998:
4992:
4989:
4984:
4983:Cyberbullying
4977:
4974:
4961:
4957:
4955:9780398087289
4951:
4947:
4946:
4938:
4935:
4919:
4912:
4906:
4903:
4890:
4886:
4880:
4877:
4864:
4861:. June 2017.
4860:
4859:
4854:
4848:
4845:
4837:
4833:
4826:
4819:
4816:
4803:
4799:
4795:
4788:
4785:
4780:
4774:
4770:
4763:
4760:
4747:
4743:
4742:csrc.nist.gov
4739:
4733:
4730:
4717:
4713:
4706:
4703:
4698:
4692:
4688:
4684:
4680:
4676:
4669:
4666:
4653:
4649:
4645:
4641:
4637:
4630:
4627:
4614:
4610:
4606:
4600:
4597:
4584:
4580:
4576:
4570:
4567:
4554:
4550:
4546:
4540:
4538:
4534:
4521:
4517:
4513:
4507:
4504:
4491:
4487:
4483:
4477:
4474:
4461:
4457:
4453:
4447:
4444:
4431:
4427:
4423:
4417:
4415:
4411:
4398:
4394:
4390:
4384:
4381:
4368:
4364:
4360:
4354:
4352:
4348:
4336:
4332:
4331:"Cyber Crime"
4326:
4324:
4320:
4315:
4309:
4290:
4283:
4277:
4274:
4261:
4257:
4250:
4247:
4234:
4230:
4224:
4221:
4216:
4212:
4208:
4206:9780313365461
4202:
4198:
4191:
4189:
4185:
4180:
4176:
4172:
4168:
4164:
4157:
4154:
4141:
4137:
4133:
4129:
4125:
4121:
4117:
4110:
4107:
4094:
4090:
4086:
4080:
4077:
4064:
4060:
4056:
4049:
4046:
4033:
4029:
4023:
4020:
4007:
4003:
3997:
3994:
3981:
3977:
3971:
3968:
3963:
3962:
3957:
3951:
3948:
3935:
3931:
3930:Straits Times
3927:
3921:
3918:
3905:
3901:
3897:
3891:
3888:
3875:
3869:
3866:
3861:
3857:
3850:
3847:
3834:
3830:
3826:
3819:
3816:
3803:
3799:
3798:New York Post
3795:
3788:
3785:
3772:
3768:
3762:
3759:
3754:
3750:
3744:
3741:
3728:
3724:
3723:The Economist
3720:
3714:
3711:
3706:
3702:
3697:
3692:
3688:
3684:
3677:
3674:
3669:
3662:
3660:
3658:
3654:
3641:
3637:
3633:
3627:
3624:
3612:
3608:
3602:
3599:
3587:
3583:
3577:
3574:
3561:
3557:
3551:
3548:
3535:
3531:
3527:
3521:
3519:
3515:
3510:
3506:
3502:
3501:
3496:
3489:
3486:
3474:
3470:
3463:
3460:
3448:
3444:
3437:
3434:
3421:
3417:
3413:
3407:
3404:
3391:
3387:
3383:
3376:
3373:
3360:
3356:
3350:
3347:
3334:
3330:
3326:
3319:
3316:
3303:
3299:
3298:
3297:The Daily Dot
3293:
3287:
3284:
3271:
3267:
3263:
3257:
3254:
3241:
3237:
3233:
3227:
3224:
3211:
3207:
3203:
3197:
3194:
3181:
3177:
3173:
3167:
3164:
3151:
3147:
3143:
3137:
3134:
3121:
3117:
3111:
3108:
3095:
3091:
3085:
3082:
3069:
3065:
3059:
3056:
3043:
3039:
3035:
3029:
3026:
3013:
3009:
3005:
3001:
2997:
2993:
2989:
2985:
2984:"Click Fraud"
2978:
2975:
2962:
2958:
2954:
2948:
2945:
2940:
2936:
2932:
2925:
2922:
2914:
2907:
2900:
2897:
2884:
2880:
2876:
2870:
2867:
2851:
2847:
2840:
2834:
2831:
2818:
2814:
2810:
2804:
2801:
2788:
2784:
2780:
2774:
2771:
2758:
2754:
2750:
2744:
2741:
2728:
2724:
2720:
2714:
2711:
2698:
2694:
2690:
2684:
2681:
2668:
2664:
2660:
2654:
2651:
2638:
2634:
2630:
2624:
2622:
2618:
2605:
2601:
2597:
2591:
2588:
2575:
2571:
2567:
2561:
2558:
2545:
2541:
2537:
2531:
2528:
2515:
2511:
2507:
2501:
2498:
2485:
2481:
2477:
2471:
2469:
2465:
2452:
2448:
2444:
2438:
2435:
2429:
2425:
2418:
2415:
2402:
2398:
2397:us.norton.com
2394:
2388:
2385:
2372:
2368:
2364:
2358:
2355:
2342:
2338:
2331:
2328:
2320:
2313:
2306:
2303:
2291:
2287:
2280:
2277:
2264:
2260:
2256:
2250:
2247:
2243:
2239:
2233:
2230:
2217:
2213:
2209:
2203:
2200:
2195:
2193:9780787663742
2189:
2185:
2178:
2175:
2170:
2166:
2162:
2158:
2153:
2148:
2144:
2140:
2136:
2129:
2127:
2123:
2118:
2114:
2110:
2106:
2102:
2098:
2091:
2088:
2075:
2071:
2067:
2060:
2058:
2054:
2038:
2034:
2027:
2020:
2017:
2001:
1997:
1990:
1984:
1981:
1968:
1964:
1960:
1954:
1951:
1938:
1934:
1930:
1924:
1921:
1908:
1904:
1900:
1896:
1894:1-59593-048-5
1890:
1886:
1882:
1878:
1874:
1867:
1865:
1861:
1855:
1850:
1847:
1845:
1842:
1840:
1839:Virtual crime
1837:
1835:
1832:
1830:
1827:
1825:
1822:
1820:
1817:
1815:
1812:
1810:
1807:
1804:
1801:
1799:
1796:
1794:
1791:
1789:
1786:
1784:
1781:
1779:
1776:
1774:
1771:
1768:
1765:
1763:
1760:
1758:
1757:drop catching
1754:
1752:
1749:
1747:
1744:
1742:
1739:
1737:
1734:
1732:
1729:
1727:
1726:Data diddling
1724:
1722:
1719:
1717:
1714:
1712:
1709:
1707:
1704:
1702:
1699:
1697:
1694:
1692:
1689:
1687:
1684:
1682:
1679:
1678:
1673:
1668:
1665:
1662:
1659:
1656:
1653:
1651:, in Denmark.
1650:
1647:
1644:
1641:
1638:
1635:
1633:
1630:
1628:
1625:
1622:
1619:
1616:
1613:
1611:
1608:
1606:
1603:
1602:
1598:
1596:
1593:
1588:
1583:
1579:
1573:
1571:
1567:
1565:
1556:
1554:
1547:
1545:
1543:
1538:
1535:
1527:
1525:
1523:
1519:
1515:
1510:
1507:
1505:
1501:
1496:
1493:
1489:
1485:
1482:
1478:
1470:
1465:
1462:
1459:
1456:
1453:
1450:
1447:
1446:
1445:
1442:
1440:
1435:
1433:
1424:
1422:
1418:
1414:
1411:
1407:
1399:
1395:
1390:
1386:
1383:
1378:
1376:
1372:
1368:
1361:Investigation
1360:
1358:
1356:
1347:
1341:
1337:
1333:
1329:
1328:
1323:
1319:
1316:
1311:
1308:
1304:
1300:
1297:
1293:
1289:
1285:
1282:
1278:
1274:
1270:
1266:
1262:
1259:
1255:
1251:
1247:
1244:
1240:
1237:
1233:
1229:
1226:
1222:
1219:
1215:
1211:
1207:
1203:
1199:
1196:
1192:
1188:
1185:
1181:
1177:
1173:
1169:
1165:
1161:
1157:
1153:
1149:
1145:
1142:
1138:
1135:
1131:
1127:
1123:
1119:
1116:
1113:
1109:
1105:
1101:
1098:
1094:
1093:
1089:
1087:
1085:
1081:
1077:
1072:
1068:
1066:
1062:
1058:
1054:
1050:
1046:
1040:
1038:
1034:
1030:
1026:
1023:online. Some
1022:
1018:
1011:
1009:
1007:
1003:
999:
998:Princess Haya
995:
991:
990:Ahmed Mansoor
987:
983:
979:
974:
970:
967:
962:
960:
956:
951:
947:
945:
940:
936:
932:
931:
925:
923:
919:
908:
905:
897:
887:
883:
877:
875:
868:
859:
858:
854:
850:
846:
845:Cyberstalking
842:
838:
837:Cyberbullying
830:
828:
824:
822:
816:
814:
808:
806:
800:
796:
788:
786:
784:
780:
775:
773:
765:
763:
759:
757:
753:
745:
741:
739:
736:
733:
730:
727:
726:
725:
722:
717:
713:
709:
705:
697:
695:
693:
689:
685:
679:
671:
669:
667:
663:
662:Nth room case
659:
658:child victims
654:
652:
648:
644:
640:
636:
631:
627:
621:
613:
611:
608:
601:
593:
591:
589:
585:
581:
577:
573:
565:
563:
561:
557:
553:
548:
546:
542:
538:
534:
530:
526:
522:
516:
508:
506:
504:
498:
497:Fraud Factory
491:Fraud Factory
490:
488:
486:
482:
478:
474:
470:
465:
463:
459:
455:
451:
448:, installing
447:
443:
439:
434:
432:
426:
418:
416:
414:
410:
406:
398:
396:
392:
390:
385:
381:
376:
374:
370:
366:
362:
357:
354:
349:
347:
343:
339:
328:
323:
321:
316:
314:
309:
308:
306:
305:
300:
297:
295:
294:Organizations
292:
290:
287:
285:
282:
280:
277:
276:
275:
274:
269:
264:
261:
259:
256:
254:
251:
249:
246:
244:
241:
239:
238:Environmental
236:
234:
231:
229:
226:
224:
221:
219:
216:
214:
211:
209:
206:
204:
201:
199:
196:
194:
191:
189:
186:
185:
184:
183:
178:
173:
170:
168:
165:
163:
160:
158:
155:
153:
150:
148:
145:
143:
142:Crime mapping
140:
138:
135:
133:
130:
128:
125:
123:
120:
118:
115:
114:
113:
112:
107:
102:
99:
97:
94:
92:
89:
87:
84:
82:
79:
77:
74:
72:
69:
67:
64:
63:
62:
61:
58:Main Theories
56:
52:
48:
47:
44:
40:
37:
33:
32:virtual crime
19:
7889:Reed Slatkin
7854:Kubus scheme
7734:Jim Browning
7729:419eater.com
7724:Scam baiting
7709:Romance scam
7679:Lottery scam
7638:
7624:Clickjacking
7568:Wash trading
7563:Trojan horse
7478:Return fraud
7428:Mock auction
7323:Drop swindle
7288:Bogus escrow
7152:
7144:
6947:and cheating
6931:Fare evasion
6900:
6540:Manslaughter
6509:
6505:Intoxication
6447:Self-defence
6390:
6342:Recklessness
6324:
6312:
6160:Data masking
5719:Cyberwarfare
5691:
5559:
5552:
5545:
5538:
5491:
5487:
5475:
5457:
5449:
5438:
5427:
5416:
5373:New Jersey:
5370:
5355:
5347:
5341:
5337:Vol.16 no.5.
5334:
5310:
5285:
5281:Springfield.
5267:
5252:
5246:
5234:. Retrieved
5230:the original
5225:
5216:
5207:
5201:
5192:
5186:
5174:. Retrieved
5165:
5156:
5146:20 September
5144:. Retrieved
5140:the original
5135:
5125:
5115:20 September
5113:. Retrieved
5094:
5084:
5072:. Retrieved
5063:
5039:. Retrieved
5021:
5009:. Retrieved
5000:
4991:
4982:
4976:
4964:. Retrieved
4960:the original
4944:
4937:
4925:. Retrieved
4918:the original
4905:
4893:. Retrieved
4889:the original
4879:
4867:. Retrieved
4856:
4847:
4836:the original
4831:
4818:
4806:. Retrieved
4797:
4787:
4768:
4762:
4750:. Retrieved
4741:
4732:
4720:. Retrieved
4716:the original
4705:
4678:
4668:
4656:. Retrieved
4639:
4629:
4617:. Retrieved
4608:
4599:
4587:. Retrieved
4583:the original
4579:www.cisa.gov
4578:
4569:
4557:. Retrieved
4524:. Retrieved
4516:www.cisa.gov
4515:
4506:
4494:. Retrieved
4485:
4476:
4464:. Retrieved
4456:www.cisa.gov
4455:
4446:
4434:. Retrieved
4425:
4401:. Retrieved
4397:the original
4392:
4383:
4371:. Retrieved
4362:
4338:. Retrieved
4334:
4296:. Retrieved
4289:the original
4276:
4264:. Retrieved
4249:
4237:. Retrieved
4223:
4196:
4162:
4156:
4144:. Retrieved
4119:
4109:
4097:. Retrieved
4088:
4079:
4069:24 September
4067:. Retrieved
4059:The Guardian
4058:
4048:
4038:24 September
4036:. Retrieved
4022:
4012:24 September
4010:. Retrieved
3996:
3986:24 September
3984:. Retrieved
3980:the original
3970:
3959:
3950:
3938:. Retrieved
3929:
3920:
3908:. Retrieved
3899:
3890:
3878:. Retrieved
3868:
3859:
3849:
3837:. Retrieved
3828:
3818:
3806:. Retrieved
3797:
3787:
3775:. Retrieved
3761:
3752:
3743:
3731:. Retrieved
3727:the original
3722:
3713:
3686:
3682:
3676:
3667:
3644:. Retrieved
3635:
3626:
3614:. Retrieved
3610:
3601:
3589:. Retrieved
3585:
3576:
3564:. Retrieved
3559:
3550:
3538:. Retrieved
3530:www.vice.com
3529:
3498:
3488:
3476:. Retrieved
3472:
3462:
3452:25 September
3450:. Retrieved
3446:
3436:
3424:. Retrieved
3416:www.vice.com
3415:
3406:
3394:. Retrieved
3385:
3375:
3363:. Retrieved
3349:
3337:. Retrieved
3328:
3318:
3306:. Retrieved
3295:
3286:
3274:. Retrieved
3265:
3256:
3244:. Retrieved
3235:
3226:
3214:. Retrieved
3205:
3196:
3184:. Retrieved
3175:
3166:
3154:. Retrieved
3145:
3136:
3124:. Retrieved
3110:
3098:. Retrieved
3084:
3072:. Retrieved
3067:
3058:
3046:. Retrieved
3042:the original
3037:
3028:
3016:. Retrieved
2991:
2987:
2977:
2965:. Retrieved
2956:
2947:
2934:
2924:
2913:the original
2899:
2887:. Retrieved
2879:Korea Herald
2878:
2869:
2857:. Retrieved
2845:
2833:
2821:. Retrieved
2812:
2803:
2791:. Retrieved
2782:
2773:
2761:. Retrieved
2752:
2743:
2731:. Retrieved
2722:
2713:
2701:. Retrieved
2692:
2683:
2671:. Retrieved
2662:
2653:
2641:. Retrieved
2632:
2608:. Retrieved
2604:the original
2599:
2590:
2578:. Retrieved
2569:
2560:
2548:. Retrieved
2539:
2530:
2518:. Retrieved
2509:
2500:
2488:. Retrieved
2479:
2455:. Retrieved
2446:
2437:
2430:(1): 64–183.
2427:
2423:
2417:
2405:. Retrieved
2396:
2387:
2375:. Retrieved
2366:
2357:
2347:20 September
2345:. Retrieved
2341:the original
2330:
2319:the original
2305:
2293:. Retrieved
2289:
2279:
2267:. Retrieved
2258:
2249:
2237:
2232:
2220:. Retrieved
2211:
2202:
2183:
2177:
2142:
2138:
2100:
2096:
2090:
2078:. Retrieved
2069:
2044:. Retrieved
2032:
2019:
2007:. Retrieved
1995:
1983:
1971:. Retrieved
1962:
1953:
1941:. Retrieved
1932:
1923:
1911:. Retrieved
1876:
1751:Hacking back
1584:
1580:
1577:
1568:
1560:
1557:Intelligence
1551:
1539:
1531:
1511:
1508:
1497:
1494:
1490:
1486:
1474:
1443:
1436:
1428:
1419:
1415:
1403:
1379:
1364:
1351:
1325:
1273:J. P. Morgan
1225:Fortune 1000
1218:Storm botnet
1141:Melissa worm
1133:
1104:Pacific Bell
1073:
1069:
1063:, .net, and
1041:
1015:
975:
971:
963:
952:
948:
928:
926:
915:
900:
891:
871:
849:Cyber Racism
825:
817:
809:
802:
777:One area of
776:
769:
760:
749:
723:
719:
681:
678:Cyberwarfare
672:Cyberwarfare
655:
635:social media
623:
603:
584:bug poaching
569:
549:
520:
518:
505:operations.
500:
466:
435:
428:
402:
393:
377:
369:cyberwarfare
358:
350:
337:
336:
279:Bibliography
243:Experimental
222:
157:Quantitative
36:
18:Cyber crimes
7930:Con artists
7814:Dona Branca
7756:Spoofed URL
7664:Email fraud
7644:CyberThrill
7619:Click fraud
7533:Tarmac scam
7458:Pork barrel
7453:Pigeon drop
7443:Patent safe
7433:Moving scam
7343:Fiddle game
7293:Boiler room
7268:Badger game
7230:Sucker list
7203:Terminology
6548:Infanticide
6386:Concurrence
6100:Misuse case
5934:Infostealer
5909:Email fraud
5874:Data breach
5709:Cybergeddon
5353:Glenny, M.
5274:, New York.
4895:17 December
4752:17 February
4609:VentureBeat
4466:17 February
4266:17 December
4146:10 December
4099:27 December
3839:20 February
3808:14 February
3777:10 November
3611:www.dea.gov
2859:22 December
2447:PR Newswire
2269:5 September
1913:10 December
1477:Philippines
1471:Legislation
1296:S&P 500
1265:Wells Fargo
1053:Tor Browser
1002:Ghada Owais
799:Click fraud
666:South Korea
382:(WEF) 2020
233:Development
208:Criminology
152:Qualitative
132:Ethnography
117:Comparative
43:Criminology
7986:Cybercrime
7980:Categories
7958:Literature
7819:Earl Jones
7751:ShadowCrew
7704:Rock Phish
7649:DarkMarket
7639:Cybercrime
7614:Catfishing
7488:Shell game
7423:Mismarking
7348:Fine print
7308:Clip joint
7298:Bride scam
6901:Cybercrime
6831:Dishonesty
6755:Keeping a
6632:Harassment
6617:Kidnapping
6524:the person
6416:Conspiracy
6314:Actus reus
6297:Common law
6277:Either way
6272:Indictable
6165:Encryption
6041:Web shells
5981:Ransomware
5929:Hacktivism
5692:Cybercrime
5526:Boston.com
4966:25 January
4927:25 January
4869:11 January
4589:1 November
4496:4 December
4436:3 December
4403:4 December
4373:1 November
4340:4 December
4239:2 December
3186:2 November
3156:2 November
3126:2 November
3100:2 November
3074:4 December
3048:4 December
3018:30 October
2222:1 November
2080:3 February
2046:3 February
1856:References
1755:(Illegal)
1721:Cyberheist
1520:, and the
1425:Prevention
1382:IP Address
1303:ransomware
1243:Zappos.com
1160:Dell, Inc.
1051:, and the
939:cell phone
918:harassment
894:March 2016
835:See also:
793:See also:
637:networks,
600:Ransomware
594:Ransomware
469:bank fraud
338:Cybercrime
228:Demography
172:Recidivism
7945:Impostors
7599:Avalanche
7413:Long firm
7333:Exit scam
7065:Espionage
6896:Extortion
6891:Blackmail
6876:Deception
6861:Squatting
6457:Necessity
6421:Accessory
6374:Doctrines
6365:Omissions
6356:Vicarious
6352:Corporate
6320:Causation
6292:Statutory
5996:Shellcode
5991:Scareware
5839:Crimeware
5799:Backdoors
5630:from the
5606:from the
5597:from the
5518:239962449
5510:0040-1625
5105:0099-9660
5074:3 January
5041:6 January
4648:0017-8012
4559:6 January
4215:464583250
4179:146501914
4136:1556-5068
3900:Bloomberg
3753:France 24
3691:CiteSeerX
3473:The Verge
3308:4 October
3008:0732-2399
2967:5 October
2169:239962449
2161:0040-1625
2103:: 13–20.
1849:Web shell
1548:Awareness
1528:Penalties
1400:, in 2021
1277:U.S. Bank
1236:terabytes
1134:Star Trek
1130:arms race
1033:Silk Road
1029:encrypted
982:NSO Group
964:Although
886:talk page
525:terrorism
519:The term
481:extortion
407:, scams,
361:espionage
253:Political
127:Profiling
7719:SaferNet
7689:Phishing
7629:Cramming
7518:SSC Scam
7383:Hustling
7368:Gem scam
7127:Evidence
7108:Property
7098:Contract
7060:Sedition
6964:Uttering
6866:Trespass
6841:Burglary
6739:Causing
6735:Nuisance
6532:Homicide
6495:Insanity
6440:Defences
6326:Mens rea
6170:Firewall
6075:Defenses
6001:Spamming
5986:Rootkits
5959:Phishing
5919:Exploits
5419:Boston:
5288:Oxford:
5170:Archived
5109:Archived
5068:Archived
5035:Archived
5031:Symantec
5011:23 March
5005:Archived
4863:Archived
4802:Archived
4746:Archived
4722:29 April
4652:Archived
4613:Archived
4553:Archived
4551:. 2024.
4520:Archived
4490:Archived
4460:Archived
4430:Archived
4367:Archived
4308:cite web
4260:Archived
4233:Archived
4140:Archived
4093:Archived
4063:Archived
4032:Archived
4006:Archived
3934:Archived
3910:23 April
3904:Archived
3880:23 April
3833:Archived
3802:Archived
3771:Archived
3640:Archived
3534:Archived
3509:Archived
3420:Archived
3390:Archived
3359:Archived
3333:Archived
3302:Archived
3276:1 August
3270:Archived
3266:NBC News
3240:Archived
3210:Archived
3206:Statista
3180:Archived
3150:Archived
3120:Archived
3094:Archived
3012:Archived
2961:Archived
2939:Archived
2883:Archived
2850:Archived
2817:Archived
2787:Archived
2757:Archived
2727:Archived
2697:Archived
2667:Archived
2637:Archived
2633:NBC News
2574:Archived
2544:Archived
2514:Archived
2484:Archived
2482:. 2020.
2451:Archived
2401:Archived
2371:Archived
2263:Archived
2216:Archived
2074:Archived
2037:Archived
2000:Archived
1967:Archived
1937:Archived
1907:Archived
1903:46562809
1736:Deep web
1674:See also
1632:INTERPOL
1599:Agencies
1392:Senator
1307:WannaCry
1254:eHarmony
1250:LinkedIn
1206:VeriSign
1148:MafiaBoy
1122:Newscorp
1080:fentanyl
1076:Alphabay
880:You may
795:Ad fraud
789:Ad-fraud
712:Phishing
708:Spamming
643:dark web
541:phishing
458:phishing
413:ad-fraud
346:networks
289:Journals
213:Critical
203:Conflict
188:American
7809:Caritas
7786:Pyramid
7739:Kitboga
7609:Carding
7483:Salting
7225:Shyster
7122:estates
6985:Perjury
6980:Bribery
6954:Forgery
6846:Robbery
6804:of oath
6802:Perjury
6642:Treason
6612:Battery
6592:Robbery
6467:Consent
6426:Attempt
6282:Summary
6011:Spyware
5954:Payload
5949:Malware
5889:Viruses
5869:Botnets
5776:Threats
5064:FireEye
4808:5 April
4526:1 April
4298:23 July
3860:Reuters
3646:14 July
3616:23 June
3591:23 June
3566:14 July
3540:14 July
3478:23 June
3426:14 July
3396:23 June
3365:23 June
3339:23 June
3246:5 April
3216:5 April
2723:Reuters
2693:Reuters
2295:19 July
2117:3334277
1731:Darknet
1627:EUROPOL
1371:logfile
1343:phones.
1338:, is a
1195:Siemens
1191:Stuxnet
1164:E*TRADE
1084:opiates
986:Pegasus
772:obscene
692:Georgia
688:Estonia
562:(CIA).
533:viruses
473:carding
454:spyware
450:malware
446:viruses
438:hacking
389:privacy
344:and/or
218:Culture
109:Methods
7824:Ezubao
7684:PayPai
7118:Trusts
6698:Affray
6536:Murder
6452:Duress
6205:(SIEM)
6182:(HIDS)
6066:Zombie
5803:Bombs
5784:Adware
5516:
5508:
5464:
5441:U.S.:
5402:
5387:
5363:
5319:
5302:
5236:5 June
5176:17 May
5103:
4952:
4775:
4693:
4646:
4213:
4203:
4177:
4134:
3940:13 May
3733:11 May
3693:
3447:Forbes
3329:Forbes
3006:
2957:google
2823:13 May
2793:29 May
2763:13 May
2733:13 May
2703:13 May
2673:13 May
2643:13 May
2610:13 May
2580:13 May
2550:13 May
2432:p. 64.
2407:11 May
2377:11 May
2240:U.S.:
2190:
2167:
2159:
2115:
2009:17 May
1973:17 May
1943:17 May
1901:
1891:
1716:Cyber-
1516:, the
1340:spying
1279:, and
1170:, and
1156:Yahoo!
1126:SKY-TV
1057:.onion
851:, and
821:botnet
714:, and
607:Norton
580:doxing
483:, and
460:, and
411:, and
299:People
271:Browse
258:Public
7923:Lists
7220:Shill
7156:table
7113:Wills
6851:Theft
6826:Arson
6051:Worms
6046:Wiper
5964:Voice
5812:Logic
5514:S2CID
5226:ASEAN
4985:: 10.
4921:(PDF)
4914:(PDF)
4839:(PDF)
4828:(PDF)
4658:3 May
4619:3 May
4292:(PDF)
4285:(PDF)
4175:S2CID
3500:Wired
2916:(PDF)
2909:(PDF)
2889:9 May
2853:(PDF)
2842:(PDF)
2520:9 May
2490:9 May
2457:9 May
2322:(PDF)
2315:(PDF)
2165:S2CID
2113:S2CID
2040:(PDF)
2029:(PDF)
2003:(PDF)
1992:(PDF)
1899:S2CID
1805:(NCA)
1769:(ICE)
1605:ASEAN
1332:ToTok
1214:MPack
1108:Nynex
1049:Tails
752:email
537:worms
284:Index
223:Cyber
167:NIBRS
7210:Scam
7120:and
7103:Tort
6772:Rout
6688:Riot
6660:Rape
5817:Time
5807:Fork
5506:ISSN
5462:ISBN
5400:ISBN
5385:ISBN
5361:ISBN
5317:ISBN
5300:ISBN
5238:2022
5178:2021
5148:2018
5117:2018
5101:ISSN
5076:2018
5043:2024
5013:2024
4968:2015
4950:ISBN
4929:2015
4897:2018
4871:2019
4858:CNBC
4810:2018
4773:ISBN
4754:2024
4724:2015
4691:ISBN
4660:2022
4644:ISSN
4621:2022
4591:2019
4561:2024
4528:2022
4498:2019
4468:2024
4438:2019
4405:2019
4375:2019
4342:2019
4314:link
4300:2017
4268:2018
4241:2019
4211:OCLC
4201:ISBN
4148:2023
4132:ISSN
4101:2019
4071:2018
4040:2018
4014:2018
3988:2018
3942:2017
3912:2013
3882:2013
3841:2020
3810:2013
3779:2011
3735:2011
3648:2020
3618:2020
3593:2020
3568:2020
3542:2020
3480:2020
3454:2021
3428:2020
3398:2020
3386:Vice
3367:2020
3341:2020
3310:2016
3278:2021
3248:2021
3218:2021
3188:2019
3158:2019
3128:2019
3102:2019
3076:2019
3050:2019
3020:2021
3004:ISSN
2969:2014
2891:2020
2861:2022
2825:2020
2795:2020
2765:2020
2735:2020
2705:2020
2675:2020
2645:2020
2612:2020
2582:2020
2552:2020
2522:2020
2492:2020
2459:2020
2409:2023
2379:2023
2349:2015
2297:2024
2271:2021
2224:2020
2188:ISBN
2157:ISSN
2082:2024
2048:2024
2011:2021
1975:2021
1945:2021
1915:2023
1889:ISBN
1324:and
1252:and
1200:The
1189:The
1168:eBay
1082:and
1065:.org
1061:.com
1027:use
976:The
922:race
797:and
738:Spam
649:and
630:rape
582:and
378:The
7874:MMM
7788:and
7590:and
5822:Zip
5496:doi
5492:174
4798:NPR
4683:doi
4167:doi
4124:doi
3701:doi
2996:doi
2510:CNN
2480:IJM
2147:doi
2143:174
2105:doi
1881:doi
1502:'s
1481:FBI
1172:CNN
664:in
452:or
444:or
162:BJS
7982::
6546:/
6542:/
6538:/
6358:/
6354:/
5512:.
5504:.
5490:.
5486:.
5270:,
5224:.
5168:.
5164:.
5134:.
5107:.
5099:.
5093:.
5066:.
5062:.
5051:^
5029:.
4999:.
4855:.
4830:.
4800:.
4796:.
4744:.
4740:.
4689:.
4677:.
4650:.
4642:.
4638:.
4607:.
4577:.
4547:.
4536:^
4518:.
4514:.
4484:.
4458:.
4454:.
4428:.
4424:.
4413:^
4391:.
4361:.
4350:^
4333:.
4322:^
4310:}}
4306:{{
4258:.
4231:.
4209:.
4187:^
4173:.
4165:.
4138:.
4130:.
4122:.
4118:.
4087:.
4061:.
4057:.
3958:.
3928:.
3898:.
3858:.
3831:.
3827:.
3800:.
3796:.
3751:.
3721:.
3699:.
3687:38
3685:.
3656:^
3638:.
3634:.
3609:.
3584:.
3558:.
3528:.
3517:^
3507:.
3503:.
3497:.
3471:.
3445:.
3414:.
3388:.
3384:.
3357:.
3331:.
3327:.
3294:.
3264:.
3238:.
3234:.
3208:.
3204:.
3178:.
3174:.
3148:.
3144:.
3118:.
3092:.
3066:.
3036:.
3010:.
3002:.
2992:28
2990:.
2986:.
2959:.
2955:.
2937:.
2933:.
2877:.
2848:.
2844:.
2811:.
2781:.
2751:.
2721:.
2691:.
2661:.
2631:.
2620:^
2598:.
2568:.
2538:.
2508:.
2478:.
2467:^
2445:.
2428:54
2426:.
2399:.
2395:.
2365:.
2288:.
2261:.
2257:.
2214:.
2210:.
2163:.
2155:.
2141:.
2137:.
2125:^
2111:.
2099:.
2072:.
2068:.
2056:^
2035:.
2031:.
1994:.
1961:.
1935:.
1931:.
1905:.
1897:.
1887:.
1875:.
1863:^
1524:.
1506:.
1309:".
1275:,
1271:,
1166:,
1162:,
1158:,
1106:,
1047:,
996:,
992:,
847:,
843:,
839:,
758:.
710:,
706:,
668:.
590:.
543:,
539:,
535:,
479:,
475:,
471:,
464:.
415:.
371:.
363:,
7190:e
7183:t
7176:v
6550:)
6534:(
6250:e
6243:t
6236:v
5660:e
5653:t
5646:v
5520:.
5498::
5470:.
5445:.
5434:.
5423:.
5391:.
5323:)
5306:)
5240:.
5210:.
5195:.
5180:.
5150:.
5119:.
5078:.
5045:.
5015:.
4970:.
4931:.
4899:.
4873:.
4812:.
4781:.
4756:.
4726:.
4699:.
4685::
4662:.
4623:.
4593:.
4563:.
4530:.
4500:.
4470:.
4440:.
4407:.
4377:.
4344:.
4316:)
4302:.
4270:.
4243:.
4217:.
4181:.
4169::
4150:.
4126::
4103:.
4073:.
4042:.
4016:.
3990:.
3964:.
3944:.
3914:.
3884:.
3862:.
3843:.
3812:.
3781:.
3737:.
3707:.
3703::
3650:.
3620:.
3595:.
3570:.
3544:.
3482:.
3456:.
3430:.
3400:.
3369:.
3343:.
3312:.
3280:.
3250:.
3220:.
3190:.
3160:.
3130:.
3104:.
3078:.
3052:.
3022:.
2998::
2971:.
2893:.
2863:.
2827:.
2797:.
2767:.
2737:.
2707:.
2677:.
2647:.
2614:.
2584:.
2554:.
2524:.
2494:.
2461:.
2411:.
2381:.
2351:.
2299:.
2273:.
2244:.
2226:.
2196:.
2171:.
2149::
2119:.
2107::
2101:2
2084:.
2050:.
2013:.
1977:.
1947:.
1917:.
1883::
1317:.
1283:.
1220:.
907:)
901:(
896:)
892:(
878:.
326:e
319:t
312:v
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.