43:
451:
351:
236:, and this limited advances in mathematics. In this transition, the word was adopted into Medieval Latin as cifra, and then into Middle French as cifre. This eventually led to the English word cipher (minority spelling cypher). One theory for how the term came to refer to encoding is that the concept of zero was confusing to Europeans, and so the term came to refer to a message or communication that was not easily understood.
408:) which changed the substitution alphabet for every letter. For example, "GOOD DOG" can be encrypted as "PLSX TWF" where "L", "S", and "W" substitute for "O". With even a small amount of known or estimated plaintext, simple polyalphabetic substitution ciphers and letter transposition ciphers designed for pen and paper encryption are easy to crack. It is possible to create a secure pen and paper cipher based on a
100:
1560:
223:). If the algorithm is symmetric, the key must be known to the recipient and sender and to no one else. If the algorithm is an asymmetric one, the enciphering key is different from, but closely related to, the deciphering key. If one key cannot be deduced from the other, the asymmetric key algorithm has the public/private key property and one of the keys may be made public without loss of confidentiality.
420:, several rotor disks provided polyalphabetic substitution, while plug boards provided another substitution. Keys were easily changed by changing the rotor disks and the plugboard wires. Although these encryption methods were more complex than previous schemes and required machines to encrypt and decrypt, other machines such as the British
197:). The encrypting procedure is varied depending on the key, which changes the detailed operation of the algorithm. A key must be selected before using a cipher to encrypt a message. Without knowledge of the key, it should be extremely difficult, if not impossible, to decrypt the resulting ciphertext into readable plaintext.
497:
Computational power available, i.e., the computing power which can be brought to bear on the problem. It is important to note that average performance/capacity of a single computer is not the only factor to consider. An adversary can use multiple computers at once, for instance, to increase the speed
165:
Codes generally substitute different length strings of characters in the output, while ciphers generally substitute the same number of characters as are input. A code maps one meaning with another. Words and phrases can be coded as letters or numbers. Codes typically have direct meaning from input to
467:
In a symmetric key algorithm (e.g., DES and AES), the sender and receiver must have a shared key set up in advance and kept secret from all other parties; the sender uses this key for encryption, and the receiver uses the same key for decryption. The design of AES (Advanced
Encryption System) was
386:). For example, "GOOD DOG" can be encrypted as "PLLX XLP" where "L" substitutes for "O", "P" for "G", and "X" for "D" in the message. Transposition of the letters "GOOD DOG" can result in "DGOGDOO". These simple ciphers and examples are easy to crack, even without plaintext-ciphertext pairs.
276:(meaning Chinese characters in Japanese) characters to supplement the native Japanese characters representing syllables. An example using English language with Kanji could be to replace "The quick brown fox jumps over the lazy dog" by "The quick brown 狐 jumps 上 the lazy 犬".
257:
In casual contexts, "code" and "cipher" can typically be used interchangeably; however, the technical usages of the words refer to different concepts. Codes contain meaning; words and phrases are assigned to numbers or symbols, creating a shorter message.
468:
beneficial because it aimed to overcome the flaws in the design of the DES (Data encryption standard). AES's designer's claim that the common means of modern cipher cryptanalytic attacks are ineffective against AES due to its design structure.
362:
is one of the earliest known cryptographic systems. Julius Caesar used a cipher that shifts the letters in the alphabet in place by three and wrapping the remaining letters to the front to write to Marcus
Tullius Cicero in approximately 50 BC.
283:
Ciphers, on the other hand, work at a lower level: the level of individual letters, small groups of letters, or, in modern schemes, individual bits and blocks of bits. Some systems used both codes and ciphers in one system, using
173:
which linked a random string of characters or numbers to a word or phrase. For example, "UQJHSE" could be the code for "Proceed to the following coordinates." When using a cipher the original information is known as
415:
During the early twentieth century, electro-mechanical machines were invented to do encryption and decryption using transposition, polyalphabetic substitution, and a kind of "additive" substitution. In
232:
Originating from the Arabic word for zero صفر (sifr), the word "cipher" spread to Europe as part of the Arabic numeral system during the Middle Ages. The Roman numeral system lacked the concept of
166:
key. Codes primarily function to save time. Ciphers are algorithmic. The given input must follow the cipher's process to be solved. Ciphers are commonly used to encrypt written information.
1540:
1370:
182:. The ciphertext message contains all the information of the plaintext message, but is not in a format readable by a human or computer without the proper mechanism to decrypt it.
243:
was later also used to refer to any Arabic digit, or to calculation using them, so encoding text in the form of Arabic numerals is literally converting the text to "ciphers".
1000:
541:
proved, using information theory considerations, that any theoretically unbreakable cipher must have keys which are at least as long as the plaintext, and used only once:
921:. 2005 13th IEEE International Conference on Networks, Jointly held with the 2005 IEEE 7th Malaysia International Conference on Communication. Vol. 2. Kuala Lumpur:
1130:
848:
272:
Another example is given by whole word ciphers, which allow the user to replace an entire word with a symbol or character, much like the way written
Japanese utilizes
982:
1019:
1223:
342:
are substantially different from modern methods, and modern ciphers can be classified according to how they operate and whether they use one or two keys.
307:
Historically, cryptography was split into a dichotomy of codes and ciphers, while coding had its own terminology analogous to that of ciphers: "
390:
1176:
1144:
824:
64:
1100:
608:
739:
1216:
1108:
1033:
958:
895:
724:
86:
990:
686:
262:
1049:
1419:
265:
which was used to shorten long telegraph messages which resulted from entering into commercial contracts using exchanges of
158:", as they are both a set of steps that encrypt a message; however, the concepts are distinct in cryptography, especially
493:
In a pure mathematical attack, (i.e., lacking any other information to help break a cipher) two factors above all count:
1209:
154:. To encipher or encode is to convert information into cipher or code. In common parlance, "cipher" is synonymous with "
1535:
1490:
1303:
532:
401:
57:
51:
1414:
1192:
1530:
1015:
330:. Because of this, codes have fallen into disuse in modern cryptography, and ciphers are the dominant technique.
68:
1520:
1510:
1365:
456:
443:
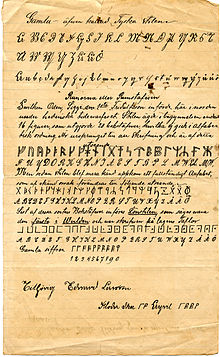
220:
150:—a series of well-defined steps that can be followed as a procedure. An alternative, less common term is
1515:
1505:
1308:
1268:
1261:
1251:
1246:
460:
439:
339:
216:
31:
1256:
877:
432:
Modern encryption methods can be divided by two criteria: by type of key used, and by type of input data.
159:
1588:
1563:
1409:
1355:
508:, i.e., the size of key used to encrypt a message. As the key size increases, so does the complexity of
626:"Vt hkskdkxt: Early Medieval Cryptography, Textual Errors, and Scribal Agency (Speculum, forthcoming)"
1525:
1449:
1025:
379:
111:
103:
1288:
944:
569:
564:
371:
252:
155:
1394:
1378:
1325:
1074:
1066:
976:
887:
806:
794:
653:
645:
186:
450:
405:
350:
1454:
1444:
1315:
1172:
1140:
1126:
1104:
1029:
964:
954:
891:
865:
830:
820:
720:
604:
509:
499:
394:
383:
285:
1593:
1389:
1058:
948:
926:
857:
816:
786:
637:
367:
1114:
901:
746:
185:
The operation of a cipher usually depends on a piece of auxiliary information, called a
1464:
1384:
1345:
1293:
1278:
1092:
810:
579:
554:
538:
99:
1582:
1545:
1500:
1459:
1439:
1335:
1298:
1273:
657:
574:
481:
417:
359:
338:
There are a variety of different types of encryption. Algorithms used earlier in the
323:
209:
119:
1078:
798:
516:
Since the desired effect is computational difficulty, in theory one would choose an
1495:
1340:
1330:
1320:
1283:
1232:
1160:
1062:
995:
712:
559:
542:
528:
475:
409:
205:
127:
107:
881:
1044:
1474:
1136:
777:
115:
915:
1434:
1404:
1399:
1360:
930:
790:
179:
147:
143:
869:
834:
775:
Al-Kadi, Ibrahim A. (1992). "Origins of
Cryptology: The Arab Contributions".
1424:
1168:
968:
517:
277:
175:
139:
905:
1118:
861:
527:
which uses multiple reports to suggest that a symmetrical cipher with 128
17:
1469:
1429:
505:
366:
Historical pen and paper ciphers used in the past are sometimes known as
327:
266:
170:
1021:
The
Ciphers of the Monks: A Forgotten Number-notation of the Middle Ages
649:
322:
However, codes have a variety of drawbacks, including susceptibility to
1070:
812:
GCHQ: The
Uncensored Story of Britain's Most Secret Intelligence Agency
512:
to the point where it becomes impractical to crack encryption directly.
471:
Ciphers can be distinguished into two types by the type of input data:
520:
and desired difficulty level, thus decide the key length accordingly.
1350:
687:"English Civil War cipher belonging to Cromwell ally goes on display"
625:
393:, developed ciphers to send coded messages to his allies during the
215:
By whether the same key is used for both encryption and decryption (
641:
463:), where two different keys are used for encryption and decryption.
204:
By whether they work on blocks of symbols usually of a fixed size (
449:
421:
375:
349:
273:
98:
922:
601:
The Muslim Next Door: The Qur'an, the Media, and That Veil Thing
446:), where one same key is used for encryption and decryption, and
1205:
190:
36:
1045:"Cryptology: From Caesar Ciphers to Public-key Cryptosystems"
524:
1132:
Cryptography and
Network Security: Principles and Practices
280:
sometimes use specific symbols to abbreviate whole words.
233:
200:
Most modern ciphers can be categorized in several ways:
917:
535:
with 256 bits, all have similar difficulty at present.
1371:
Cryptographically secure pseudorandom number generator
913:
Ho, Yean Li; Samsudin, Azman; Belaton, Bahari (2005).
502:
for a key (i.e., "brute force" attack) substantially.
1197:
169:
Codes operated by substituting according to a large
1483:
1239:
354:
Visual representation of how Caesar's Cipher works.
27:
Algorithm for encrypting and decrypting information
914:
531:, an asymmetric cipher with 3072 bit keys, and an
288:to increase the security. In some cases the terms
1097:Elementary Cryptanalysis: A Mathematical Approach
424:were invented to crack these encryption methods.
478:, which encrypt block of data of fixed size, and
842:Caldwell, William Casey (2022). "Shakespeare's
950:The Codebreakers – The Story of Secret Writing
435:By type of key used ciphers are divided into:
1217:
389:In the 1640s, the Parliamentarian commander,
8:
849:SEL: Studies in English Literature 1500–1900
326:and the difficulty of managing a cumbersome
523:An example of this process can be found at
484:, which encrypt continuous streams of data.
219:), or if a different key is used for each (
1224:
1210:
1202:
1198:
1043:Luciano, Dennis; Prichett, Gordon (1987).
981:: CS1 maint: location missing publisher (
1101:Mathematical Association of America Press
740:"Communication Theory of Secrecy Systems"
208:), or on a continuous stream of symbols (
87:Learn how and when to remove this message
50:This article includes a list of general
603:. White Cloud Press. pp. 240–241.
591:
974:
412:, but these have other disadvantages.
391:Edward Montagu, 2nd Earl of Manchester
7:
114:. Also includes runically unrelated
717:Cryptogtaphy / Theory and Practice
56:it lacks sufficient corresponding
25:
1165:Cryptography: Theory and Practice
1559:
1558:
1163:; Paterson, Maura (2023-01-09).
886:(Corrected ed.). New York:
400:Simple ciphers were replaced by
41:
1050:The College Mathematics Journal
1003:from the original on 2024-01-17
1420:Information-theoretic security
1063:10.1080/07468342.1987.11973000
953:(Revised ed.). New York.
624:Saltzman, Benjamin A. (2018).
1:
846:and the Ciphers of History".
599:Ali-Karamali, Sumbul (2008).
110:resembling that found on the
178:, and the encrypted form as
1536:Message authentication code
1491:Cryptographic hash function
1304:Cryptographic hash function
402:polyalphabetic substitution
296:are used synonymously with
1610:
1415:Harvest now, decrypt later
489:Key size and vulnerability
261:An example of this is the
250:
29:
1554:
1531:Post-quantum cryptography
1201:
931:10.1109/ICON.2005.1635595
791:10.1080/0161-119291866801
719:, CRC Press, p. 45,
671:Janeczko, Paul B (2004).
457:asymmetric key algorithms
263:commercial telegraph code
221:asymmetric key algorithms
1521:Quantum key distribution
1511:Authenticated encryption
1366:Random number generation
444:Private-key cryptography
440:symmetric key algorithms
217:symmetric key algorithms
1516:Public-key cryptography
1506:Symmetric-key algorithm
1309:Key derivation function
1269:Cryptographic primitive
1262:Authentication protocol
1252:Outline of cryptography
1247:History of cryptography
1161:Stinson, Douglas Robert
461:Public-key cryptography
340:history of cryptography
71:more precise citations.
32:Cipher (disambiguation)
1257:Cryptographic protocol
807:Aldrich, Richard James
454:
370:. They include simple
355:
160:classical cryptography
123:
1410:End-to-end encryption
1356:Cryptojacking malware
862:10.1353/sel.2022.0003
533:elliptic curve cipher
453:
404:ciphers (such as the
380:transposition ciphers
353:
102:
1526:Quantum cryptography
1450:Trusted timestamping
1026:Franz Steiner Verlag
925:. pp. 710–715.
878:Gaines, Helen Fouché
372:substitution ciphers
189:(or, in traditional
112:Kensington Runestone
30:For other uses, see
1289:Cryptographic nonce
991:"Ciphers vs. codes"
713:Stinson, Douglas R.
570:List of ciphertexts
565:Encryption software
253:Code (cryptography)
1395:Subliminal channel
1379:Pseudorandom noise
1326:Key (cryptography)
1127:Stallings, William
888:Dover Publications
455:
356:
124:
118:writing style and
1576:
1575:
1572:
1571:
1455:Key-based routing
1445:Trapdoor function
1316:Digital signature
1178:978-1-032-47604-9
1146:978-0-13-670722-6
826:978-0-00-727847-3
510:exhaustive search
500:exhaustive search
395:English Civil War
384:Rail Fence Cipher
368:classical ciphers
286:superencipherment
97:
96:
89:
16:(Redirected from
1601:
1562:
1561:
1390:Insecure channel
1226:
1219:
1212:
1203:
1199:
1182:
1167:(6th ed.).
1156:
1154:
1153:
1135:(8th ed.).
1122:
1088:
1086:
1085:
1039:
1011:
1009:
1008:
986:
980:
972:
940:
938:
937:
920:
909:
873:
838:
817:HarperCollins UK
802:
762:
761:
759:
757:
751:
745:. Archived from
744:
736:
730:
729:
709:
703:
702:
700:
698:
683:
677:
676:
668:
662:
661:
621:
615:
614:
596:
304:, respectively.
92:
85:
81:
78:
72:
67:this article by
58:inline citations
45:
44:
37:
21:
1609:
1608:
1604:
1603:
1602:
1600:
1599:
1598:
1579:
1578:
1577:
1568:
1550:
1479:
1235:
1230:
1189:
1179:
1159:
1151:
1149:
1147:
1125:
1111:
1093:Sinkov, Abraham
1091:
1083:
1081:
1042:
1036:
1014:
1006:
1004:
989:
973:
961:
943:
935:
933:
912:
898:
876:
841:
827:
805:
774:
771:
766:
765:
755:
753:
752:on June 5, 2007
749:
742:
738:
737:
733:
727:
711:
710:
706:
696:
694:
685:
684:
680:
670:
669:
665:
623:
622:
618:
611:
598:
597:
593:
588:
551:
491:
430:
348:
336:
255:
249:
230:
142:for performing
93:
82:
76:
73:
63:Please help to
62:
46:
42:
35:
28:
23:
22:
15:
12:
11:
5:
1607:
1605:
1597:
1596:
1591:
1581:
1580:
1574:
1573:
1570:
1569:
1567:
1566:
1555:
1552:
1551:
1549:
1548:
1543:
1541:Random numbers
1538:
1533:
1528:
1523:
1518:
1513:
1508:
1503:
1498:
1493:
1487:
1485:
1481:
1480:
1478:
1477:
1472:
1467:
1465:Garlic routing
1462:
1457:
1452:
1447:
1442:
1437:
1432:
1427:
1422:
1417:
1412:
1407:
1402:
1397:
1392:
1387:
1385:Secure channel
1382:
1376:
1375:
1374:
1363:
1358:
1353:
1348:
1346:Key stretching
1343:
1338:
1333:
1328:
1323:
1318:
1313:
1312:
1311:
1306:
1296:
1294:Cryptovirology
1291:
1286:
1281:
1279:Cryptocurrency
1276:
1271:
1266:
1265:
1264:
1254:
1249:
1243:
1241:
1237:
1236:
1231:
1229:
1228:
1221:
1214:
1206:
1196:
1195:
1188:
1187:External links
1185:
1184:
1183:
1177:
1157:
1145:
1129:(2020-01-03).
1123:
1109:
1089:
1040:
1034:
1016:King, David A.
1012:
987:
959:
941:
910:
896:
874:
856:(2): 241–268.
839:
825:
803:
770:
767:
764:
763:
731:
725:
704:
693:. 12 July 2023
678:
663:
642:10.1086/698861
616:
610:978-0974524566
609:
590:
589:
587:
584:
583:
582:
580:Telegraph code
577:
572:
567:
562:
557:
555:Autokey cipher
550:
547:
539:Claude Shannon
514:
513:
503:
490:
487:
486:
485:
482:stream ciphers
479:
465:
464:
447:
429:
426:
418:rotor machines
347:
344:
335:
332:
251:Main article:
248:
245:
229:
226:
225:
224:
213:
210:stream ciphers
195:cryptovariable
104:Edward Larsson
95:
94:
49:
47:
40:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
1606:
1595:
1592:
1590:
1587:
1586:
1584:
1565:
1557:
1556:
1553:
1547:
1546:Steganography
1544:
1542:
1539:
1537:
1534:
1532:
1529:
1527:
1524:
1522:
1519:
1517:
1514:
1512:
1509:
1507:
1504:
1502:
1501:Stream cipher
1499:
1497:
1494:
1492:
1489:
1488:
1486:
1482:
1476:
1473:
1471:
1468:
1466:
1463:
1461:
1460:Onion routing
1458:
1456:
1453:
1451:
1448:
1446:
1443:
1441:
1440:Shared secret
1438:
1436:
1433:
1431:
1428:
1426:
1423:
1421:
1418:
1416:
1413:
1411:
1408:
1406:
1403:
1401:
1398:
1396:
1393:
1391:
1388:
1386:
1383:
1380:
1377:
1372:
1369:
1368:
1367:
1364:
1362:
1359:
1357:
1354:
1352:
1349:
1347:
1344:
1342:
1339:
1337:
1336:Key generator
1334:
1332:
1329:
1327:
1324:
1322:
1319:
1317:
1314:
1310:
1307:
1305:
1302:
1301:
1300:
1299:Hash function
1297:
1295:
1292:
1290:
1287:
1285:
1282:
1280:
1277:
1275:
1274:Cryptanalysis
1272:
1270:
1267:
1263:
1260:
1259:
1258:
1255:
1253:
1250:
1248:
1245:
1244:
1242:
1238:
1234:
1227:
1222:
1220:
1215:
1213:
1208:
1207:
1204:
1200:
1194:
1191:
1190:
1186:
1180:
1174:
1170:
1166:
1162:
1158:
1148:
1142:
1138:
1134:
1133:
1128:
1124:
1120:
1116:
1112:
1110:0-88385-622-0
1106:
1102:
1098:
1094:
1090:
1080:
1076:
1072:
1068:
1064:
1060:
1056:
1052:
1051:
1046:
1041:
1037:
1035:3-515-07640-9
1031:
1027:
1024:. Stuttgart:
1023:
1022:
1017:
1013:
1002:
998:
997:
992:
988:
984:
978:
970:
966:
962:
960:0-684-83130-9
956:
952:
951:
946:
942:
932:
928:
924:
919:
918:
911:
907:
903:
899:
897:0-486-20097-3
893:
889:
885:
884:
883:Cryptanalysis
879:
875:
871:
867:
863:
859:
855:
851:
850:
845:
840:
836:
832:
828:
822:
818:
814:
813:
808:
804:
800:
796:
792:
788:
785:(2): 97–126.
784:
780:
779:
773:
772:
768:
748:
741:
735:
732:
728:
726:0-8493-8521-0
722:
718:
714:
708:
705:
692:
688:
682:
679:
674:
667:
664:
659:
655:
651:
647:
643:
639:
635:
631:
627:
620:
617:
612:
606:
602:
595:
592:
585:
581:
578:
576:
575:Steganography
573:
571:
568:
566:
563:
561:
558:
556:
553:
552:
548:
546:
544:
540:
536:
534:
530:
526:
521:
519:
511:
507:
504:
501:
496:
495:
494:
488:
483:
480:
477:
476:block ciphers
474:
473:
472:
469:
462:
458:
452:
448:
445:
441:
438:
437:
436:
433:
427:
425:
423:
419:
413:
411:
407:
403:
398:
396:
392:
387:
385:
381:
377:
373:
369:
364:
361:
360:Caesar Cipher
352:
345:
343:
341:
333:
331:
329:
325:
324:cryptanalysis
320:
319:" and so on.
318:
314:
310:
305:
303:
302:transposition
299:
295:
291:
287:
281:
279:
278:Stenographers
275:
270:
268:
264:
259:
254:
246:
244:
242:
237:
235:
227:
222:
218:
214:
211:
207:
206:block ciphers
203:
202:
201:
198:
196:
192:
188:
183:
181:
177:
172:
167:
163:
161:
157:
153:
149:
145:
141:
137:
133:
129:
121:
120:pigpen cipher
117:
113:
109:
105:
101:
91:
88:
80:
70:
66:
60:
59:
53:
48:
39:
38:
33:
19:
1589:Cryptography
1496:Block cipher
1341:Key schedule
1331:Key exchange
1321:Kleptography
1284:Cryptosystem
1233:Cryptography
1164:
1150:. Retrieved
1131:
1099:. New York:
1096:
1082:. Retrieved
1054:
1048:
1020:
1005:. Retrieved
996:Khan Academy
994:
949:
934:. Retrieved
916:
882:
853:
847:
843:
811:
782:
776:
754:. Retrieved
747:the original
734:
716:
707:
695:. Retrieved
690:
681:
672:
666:
633:
629:
619:
600:
594:
560:Cover-coding
543:one-time pad
537:
522:
515:
492:
470:
466:
434:
431:
414:
410:one-time pad
399:
388:
365:
357:
337:
321:
316:
312:
308:
306:
301:
298:substitution
297:
293:
289:
282:
271:
260:
256:
247:Versus codes
240:
238:
231:
199:
194:
193:parlance, a
184:
168:
164:
152:encipherment
151:
135:
131:
128:cryptography
125:
83:
74:
55:
1484:Mathematics
1475:Mix network
1193:Kish cypher
1057:(1): 2–17.
945:Kahn, David
778:Cryptologia
756:February 3,
382:(such as a
116:blackletter
108:rune cipher
69:introducing
1583:Categories
1435:Ciphertext
1405:Decryption
1400:Encryption
1361:Ransomware
1152:2024-06-30
1084:2023-02-19
1007:2024-06-30
936:2024-06-30
815:. London:
769:References
673:Top Secret
636:(4): 975.
525:Key Length
346:Historical
180:ciphertext
148:decryption
144:encryption
77:March 2009
52:references
18:Enciphered
1425:Plaintext
1169:CRC Press
977:cite book
947:(1996) .
880:(1956) .
870:1522-9270
835:503638180
658:165362817
518:algorithm
374:(such as
267:telegrams
239:The term
228:Etymology
176:plaintext
140:algorithm
1564:Category
1470:Kademlia
1430:Codetext
1373:(CSPRNG)
1095:(1968).
1079:14686417
1018:(2001).
1001:Archived
969:35159231
906:7634764M
809:(2010).
799:62601575
715:(1995),
697:4 August
691:The Past
650:26584834
630:Speculum
549:See also
506:Key size
406:Vigenère
328:codebook
317:decoding
313:codetext
309:encoding
171:codebook
138:) is an
1594:Ciphers
1240:General
1137:Pearson
1119:149668W
1071:2686311
844:Henry V
294:ciphers
65:improve
1351:Keygen
1175:
1143:
1117:
1107:
1077:
1069:
1032:
967:
957:
904:
894:
868:
833:
823:
797:
723:
656:
648:
607:
428:Modern
378:) and
241:cipher
136:cypher
132:cipher
54:, but
1381:(PRN)
1075:S2CID
1067:JSTOR
795:S2CID
750:(PDF)
743:(PDF)
654:S2CID
646:JSTOR
586:Notes
422:Bombe
376:ROT13
334:Types
290:codes
274:Kanji
1173:ISBN
1141:ISBN
1105:ISBN
1030:ISBN
983:link
965:OCLC
955:ISBN
923:IEEE
892:ISBN
866:ISSN
831:OCLC
821:ISBN
758:2019
721:ISBN
699:2023
605:ISBN
529:bits
358:The
300:and
292:and
234:zero
156:code
134:(or
130:, a
1059:doi
927:doi
858:doi
787:doi
638:doi
498:of
191:NSA
187:key
146:or
126:In
106:'s
1585::
1171:.
1139:.
1115:OL
1113:.
1103:.
1073:.
1065:.
1055:18
1053:.
1047:.
1028:.
999:.
993:.
979:}}
975:{{
963:.
902:OL
900:.
890:.
864:.
854:61
852:.
829:.
819:.
793:.
783:16
781:.
689:.
652:.
644:.
634:93
632:.
628:.
545:.
397:.
315:,
311:,
269:.
212:).
162:.
1225:e
1218:t
1211:v
1181:.
1155:.
1121:.
1087:.
1061::
1038:.
1010:.
985:)
971:.
939:.
929::
908:.
872:.
860::
837:.
801:.
789::
760:.
701:.
675:.
660:.
640::
613:.
459:(
442:(
122:.
90:)
84:(
79:)
75:(
61:.
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.