816:, and CD-ROM drives were involved. Mouse support was possible but often left out due to the limited space for drivers on a floppy disk. Some devices such as USB often did not work using newer features such as USB 2.0, instead only operating at 1.0 speeds and taking hours to do what should have taken only a few minutes. As widespread support for DOS went into decline, it became increasingly difficult to get hardware drivers for DOS for the newer hardware.
1566:
2355:
84:
43:
1570:
2367:
186:
1158:. This helped clarify the difference between the consumer and business editions of the product. According to Symantec, Symantec GHOST and Norton GHOST are two separate product lines based around different technologies developed by different teams. This was further defined in February 2006, with the release of Norton Save And Restore (also known as
1618:
1147:
609:. GHOST could clone a disk or partition to another disk or partition or to an image file. GHOST allows for writing a clone or image to a second disk in the same machine, another machine linked by a parallel or network cable, a network drive, or to a tape drive. 3.1 uses 286 with XMS and could still run on OS/2.
846:
Norton GHOST 2003, a consumer edition of Ghost, was released on
September 6, 2002. Available as an independent product, Norton GHOST 2003 was also included as a component of Norton SystemWorks 2003 Professional. A simpler, non-corporate version of Ghost, Norton GHOST 2003 does not include the console
1170:
GHOST Solution Suite 1.1 was released in
December 2005. GHOST Solution Suite 1.1 is a bundle of an updated version of Ghost, Symantec Client Migration (a user data and settings migration tool) and the former PowerQuest equivalent, DeployCenter (using PQI images). It can create an image file that is
1626:
1373:
1037:
This version no longer supports opening .gho image files. It stores images in .v2i format. Incremental backup images created with Norton GHOST are saved with .iv2i filename extensions alone the original full backup (with .v2i filename extension) on a regular basis. Older .gho image files can be
933:
The limitations of GHOST 9 compared to GHOST 2003 were not well-communicated by
Symantec, and resulted in many dissatisfied customers who purchased GHOST 9 expecting the previous version's features (like making images from the bootable GHOST environment, no installation required, and no product
757:
Released
December 14, 2001, GHOST 7.5 creates a virtual partition, a DOS partition which actually exists as a file within a normal Windows file system. This significantly eased systems management because the user no longer had to set up their own partition tables. GHOST 7.5 can write images to
871:
version 7, and provides Live imaging of a
Windows system. GHOST 9 continues to leverage the PowerQuest (v2i) file format, meaning it is not backward compatible with previous versions of Ghost. However, a version of GHOST 8.0 is included on the GHOST 9 recovery disk to support existing GHOST
1005:
NSR 2.0 has fewer features in comparison to Norton GHOST 12. NSR 2.0 offers one-time backups, file and folder backup, simplified schedule editor, Maxtor OneTouch integration and modifiable
Symantec recovery disc. This version supports 32-bit and 64-bit versions of Windows XP and Vista.
1132:
Norton GHOST was discontinued on April 30, 2013. Support via chat and knowledge base was available until June 30, 2014. Until it was removed, the
Symantec GHOST Web page invited GHOST customers to try Symantec System Recovery, described as software for backup and disaster recovery.
1171:
larger than 2 GB. (In GHOST 8.2 or earlier, such image files are automatically split into two or more segments, so that each segment has a maximum size of 2 GB.) Other new features include more comprehensive manufacturing tools, and the ability to create a "universal boot disk".
270:
1713:
1727:
831:, where they can draw on current driver development to be able to image newer models of disk controllers. Nevertheless, the DOS version of GHOST on compatible hardware configurations works much faster than most of the *nix based image and backup tools.
807:
environment. Driver selection and configuration within DOS was non-trivial from the beginning, and the limited space available on floppy disks made disk cloning of several different disk controllers a difficult task, where different
581:, New Zealand. After the Symantec acquisition, a few functions (such as translation into other languages) were moved elsewhere, but the main development remained in Auckland until October 2009 at which time much was moved to India.
592:
GHOST 1.0 and 1.1 were released in 1996, followed by 2.0 (2.07) in the same year. These versions supported only the cloning of entire disks. They could run on an IBM XT and without extended memory. They also worked with
802:
The off-line version of Ghost, which runs from bootable media in place of the installed operating system, originally faced a number of driver support difficulties due to limitations of the increasingly obsolete 16-bit
973:
Norton Save And
Restore 1.0, released in February 2006, was the renamed consumer version of Ghost. It used GHOST 10.0's engine, with the addition of features to allow backup and restoration of individual files.
740:
to refresh the disk of a machine remotely. As a DOS-based program, GHOST requires machines running
Windows to reboot to DOS to run it. GHOST 6.0 requires a separate DOS partition when used with the console.
1179:
GHOST Solution Suite 2.0 was released in
November 2006. This version provides significant improvements in performance, as well as the ability to edit NTFS images. This version also adds support for
993:, thereby allowing recovery without a bootable CD. Upon system startup, a menu asks whether start the operating system or the LightsOut recovery environment. LightsOut restore would augment the
875:
GHOST split into two code bases following the acquisition of PowerQuest. The consumer line uses PowerQuest's V2I technology, while the enterprise line builds upon the original GHO format.
652:. Until 2007, GHOST Explorer could not edit NTFS images. GHOST Explorer could work with images from older versions but only slowly; version 4 images contain indexes to find files rapidly.
930:
Since GHOST 9 does not support the older .gho format disk images, a separate CD containing GHOST 2003 is included in the retail packaging for users needing to access those older images.
633:
program which supports browsing the contents of a disk image file and extracting individual files from it. Explorer was subsequently enhanced to support adding and deleting files in a
736:
GHOST 6.0, released in 2000, includes a management console for managing large numbers of machines. The console communicates with client software on managed computers and allows a
629:
image simultaneously to other machines without putting greater stress on the network than by sending an image to a single machine. This version also introduced GHOST Explorer, a
1666:
1695:
1305:
GSS 3.2, including GHOST 12.0 and Deployment Solution 6.9, was released on 18 May 2017. Release Update 3, which was released 22 September 2017, added support for the
507:
environment. This can be accomplished by creating an ISO (to burn to a DVD) or a USB bootable disk, installed to a client as an automation folder or delivered by a
2176:
1276:
As of January 6, 2010, the latest build from Live Update is 11.5.1.2266 (Live Update 5 (LU5)). This updates GHOST Solution Suite to 2.5.1 and provides support for
1592:
1312:
GSS 3.3, including GHOST 12.0 and Deployment Solution 6.9, was released on 31 October 2018. This release added support for GHOST Solution Suite Web Console,
700:(GUI). The Binary Research logo, two stars revolving around each other, plays on the main screen when the program is idle. In 1998, Gdisk, a script-based
2398:
1648:
1475:
838:
or Hiren's BootCD and use the same plug and play hardware drivers as a standard desktop computer, making hardware support for GHOST much simpler.
1787:
56:
1549:
1325:
888:
GHOST 9.0 was released August 2, 2004. It represents a significant shift in the consumer product line from GHOST 2003, in several ways:
986:
support with an updated and more thorough user interface. It supports both full system backup and individual files or folders backup.
677:
for images, and to provide the file browser. In 1998, GHOST 4.1 supports password-protected images. This version dropped OS/2 support.
989:
This version provides a "LightsOut Restore" feature, which restores a system from an on-disk software recovery environment similar to
1401:
1082:
Creates independent recovery points (known as a cold backup or offline backup) without the need to install Norton GHOST or its agent
2253:
1674:
1289:
240:
222:
204:
196:
167:
70:
1699:
997:, which comes with Ghost. The latter contains a recovery environment that can recover a system without a working operating system.
926:
The bootable environment on the GHOST 9 CD is only useful for recovery of existing backups. It cannot be used to create new images.
851:. The machine still needs to reboot to the virtual partition, but the user does not need to interact with DOS. Symantec deprecated
261:
1760:
1533:
148:
503:
GHOST is marketed as an OS (Operating System) deployment solution. Its capture and deployment environment requires booting to a
120:
1046:
According to the Norton community on Symantec's site, the following features are available in Norton GHOST 15 of April 2010:
105:
98:
2393:
1192:
955:
508:
127:
2006:
1345:
1022:
site. GHOST can connect to ThreatCon, a Symantec service that monitors malware activity around the world, and performs
584:
Technologies developed by 20/20 Software were integrated into GHOST after their acquisition by Symantec in April 2000.
867:. On August 2, 2004, Norton GHOST 9.0 was released as a new consumer version of Ghost, which is based on PowerQuest's
819:
Disk imaging competitors to GHOST have dealt with the decline of DOS by moving to other recovery environments such as
323:
2062:
1596:
1652:
134:
2298:
2016:
1198:
GHOST 11.0 supports saving and restoring from native GHOST image format (.gho, .ghs) and raw images (.img, .raw).
2408:
2268:
2132:
1780:
787:
693:
62:
31:
2403:
2263:
2097:
2087:
1027:
962:
749:
Released March 31, 2001, Norton GHOST version 7.0 (retail) was marketed as Norton GHOST 2002 Personal Edition.
697:
116:
1754:
965:
with Maxtor OneTouch buttons. GHOST 10.0 is compatible with previous versions, but not with future versions.
1015:
721:
94:
1483:
2288:
2243:
2037:
2021:
1281:
868:
1206:
The GHOST software for enterprise, including GHOST 11.5, was released in May 2008. New features include:
2413:
2308:
2233:
2152:
1968:
1223:
Allows drivers to be injected during image deployment to lessen the need for hardware dependent images.
634:
538:
1034:
partitions up to 16TB. GHOST can manage other installations of version 12.0 or later across a network.
511:
server. This provides an environment to perform offline system recovery or image creation. GHOST can
2370:
2359:
2333:
2052:
1867:
1862:
1773:
1188:
737:
774:
GHOST 8.0 can run directly from Windows. It is well-suited for placement on bootable media, such as
2011:
1958:
897:
549:
later in 1996, and also provided a program, Ghostwalker, to change the Security ID (SID) that made
405:
394:
1231:
Allows live machines to be used as the source to keep images from becoming stale and out of date.
2107:
2082:
2057:
1023:
920:
913:
910:
Images can be made while Windows is running, rather than only when booted directly into DOS mode.
606:
519:
1239:
GHOST 11.5 supports saving to and restoring from native GHOST image format (.gho and .ghs) and
141:
622:
269:
2303:
2228:
2206:
2127:
2092:
2072:
1953:
1928:
1112:
1103:
1095:
701:
670:
630:
531:
512:
457:
553:
systems distinguishable from each other. Ghostwalker is capable of modifying the name of the
2339:
2278:
2258:
2201:
2137:
2112:
2077:
1996:
1975:
1938:
1874:
1514:
947:
943:
674:
417:
380:
794:. GHOST 8.0 supports NTFS file system, although NTFS is not accessible from a DOS program.
2218:
2147:
2102:
1963:
1857:
1828:
1413:
1026:
when a specific threat level is reached. Other features include the ability to back up to
479:
471:
1447:
1302:
GSS 3.1, including GHOST 12.0 and Deployment Solution 6.9, was released on 7 March 2016.
1619:"Brief overview of Symantec Ghost and Norton Ghost versions | Ghost Solution Suite"
1299:
GSS 3.0, including GHOST 12.0 and Deployment Solution 6.9, was announced in March 2015.
863:
At the end of 2003, Symantec acquired its largest competitor in the disk-cloning field,
2157:
2117:
2067:
1948:
1822:
1816:
1731:
1670:
1479:
1248:
717:
689:
666:
483:
475:
388:
297:
285:
2387:
2323:
2283:
1943:
1884:
1879:
1409:
1180:
983:
1810:
1116:
847:
but has a Windows front-end to script GHOST operations and create a bootable GHOST
467:
410:
1243:
format (.vmdk). It also supports restoring from DriveImage format (.v2i, .iv2i,)
541:
file system, but could only copy (not resize) other file systems by performing a
1991:
1796:
1154:
Released November 15, 2004, Symantec renamed the Enterprise version of GHOST to
649:
542:
489:
The backup and recovery feature was replaced by Symantec System Recovery (SSR).
260:
83:
17:
1714:"IT Management Suite 7.6 and Ghost Solution Suite 3.0 Launch Webcast - March 3"
1146:
2293:
2238:
2122:
1933:
1901:
1262:
1244:
1099:
990:
901:
893:
864:
852:
828:
554:
550:
523:
504:
292:
280:
834:
GHOST 8 and later are Windows programs; as such, they can run on Windows PE,
1918:
1350:
1277:
1071:
994:
951:
783:
673:. The additional memory available allows GHOST to provide several levels of
656:
618:
422:
30:
This article is about the backup software. For the blogging platform, see
2328:
2273:
2223:
1923:
1896:
1427:
1378:
848:
578:
492:
2318:
2313:
2248:
2191:
2142:
1316:, Windows Server 2016, Smart raw imaging, and 4K native drive support.
1191:(GPT) disks. However, the software does not fully support systems with
820:
779:
448:
2186:
2162:
2047:
1911:
1906:
1285:
959:
835:
791:
775:
626:
916:
images (containing only changes since the last image) are supported.
907:
It is a Windows program that must be installed on the target system.
1402:"Symantec™ Ghost Solution Suite 3.2 Installation and Upgrade guide"
2213:
2196:
1891:
1852:
1515:"Ghost HDD imaging history ... Knowledge ignores versions below 3"
1145:
824:
705:
686:
663:
1313:
1306:
1240:
1091:
1031:
809:
759:
646:
642:
638:
594:
566:
562:
558:
546:
527:
1769:
1765:
1184:
1019:
813:
804:
763:
725:
659:
179:
77:
36:
557:
computer from its own interface. GHOST added support for the
1649:"Brief overview of Symantec Ghost and Norton Ghost versions"
942:
Released circa 2005. Supports creating images on CDs, DVDs,
1121:
Recovery points may now be created or restored from either
1090:
Scheduled-based automatic conversion of recovery points to
1070:
Includes support for Windows 7, Windows Vista with SP2 and
704:, was integrated in Ghost. Gdisk serves a role similar to
605:
Version 3.1, released in 1997 supports cloning individual
1757:(previously Norton GHOST Enterprise Edition) product page
1087:
Convert recovery points to virtual disks using a schedule
1079:
Create recovery points from within Symantec Recovery Disk
495:
bought Symantec's Enterprise Security business in 2019.
1162:), a standalone backup application based on GHOST 10.0.
1728:"Symantec™ Ghost Solution Suite 3.2 RU3 Release Notes"
1374:"Symantec™ Ghost Solution Suite 3.3 RU4 Release Notes"
892:
It uses a totally different code base, based on the
2175:
2030:
1984:
1845:
1838:
1803:
1038:restored using GHOST Explorer, a separate utility.
433:
428:
416:
404:
379:
352:
334:
322:
303:
291:
279:
1018:(VSS) to make backups and can store backups to an
621:technology, following the lead of a competitor,
1561:
1559:
778:′s bootable CD. The corporate edition supports
569:was added in September 2017 (Enterprise only).
1295:Symantec GHOST Solution Suite 3.x (GHOST 12.0)
1202:Symantec GHOST Solution Suite 2.5 (GHOST 11.5)
1175:Symantec GHOST Solution Suite 2.0 (GHOST 11.0)
1781:
1284:. Furthermore, GHOST 11.5 is compatible with
1166:Symantec GHOST Solution Suite 1.1 (GHOST 8.3)
1142:Symantec GHOST Solution Suite 1.0 (GHOST 8.2)
855:support for Norton GHOST 2003 in early 2006.
720:(called 2.0), released around 1999, supports
515:a backup volume to recover individual files.
8:
1567:"An important update regarding Norton Ghost"
522:to another or copy a volume's contents to a
253:
1251:Backup Exec System Recovery (BESR) format.
71:Learn how and when to remove these messages
1842:
1788:
1774:
1766:
1001:Norton Save & Restore 2.0 (GHOST 13.0)
331:
268:
259:
252:
1593:"Symantec System Recovery Server Edition"
625:. Multicasting supports sending a single
453:general hardware-oriented system transfer
241:Learn how and when to remove this message
223:Learn how and when to remove this message
168:Learn how and when to remove this message
1508:
1506:
1504:
1502:
1500:
1290:PE Builder plug-in for Symantec GHOST 11
1208:
1048:
969:Norton Save And Restore 1.0 (GHOST 10.0)
1337:
482:. The technology was bought in 1998 by
1550:"Norton Ghost 15 SP1 is now available"
900:product via Symantec's acquisition of
884:Norton GHOST 9.0 (includes GHOST 2003)
104:Please improve this article by adding
7:
2366:
2001:
1448:"GHOST Solution Suite Product Brief"
1060:Improved support for virtual formats
537:Initially, GHOST supported only the
1326:Comparison of disk cloning software
577:Binary Research developed GHOST in
518:GHOST can copy the contents of one
2042:
1014:Version 14.0 (November 2007) uses
545:transfer. GHOST added support for
195:tone or style may not reflect the
25:
2399:Windows-only proprietary software
2254:Dynamic Microprocessor Associates
2002:Ghost Solution Suite (enterprise)
1156:Symantec GHOST Solution Suite 1.0
982:GHOST 12.0 (April 2007) includes
958:. Supports encrypting images and
637:-formatted image, and later with
338:15.0.1.36526 / April 1, 2010
52:This article has multiple issues.
2365:
2354:
2353:
1532:Spindler, Douglas (2000-01-17).
1428:"Radified Guide to Norton Ghost"
1265:with greatly enhanced driver set
762:discs. Later versions can write
724:partitions (although it runs in
708:, but has greater capabilities.
696:of earlier versions, 5.0 uses a
356:12.0.0.10695 / June 3, 2020
205:guide to writing better articles
184:
82:
41:
1755:Symantec GHOST – Solution suite
60:or discuss these issues on the
1412:. 3 April 2017. Archived from
1:
1193:Extensible Firmware Interface
106:secondary or tertiary sources
2007:Symantec Endpoint Protection
1651:. 5 May 2008. Archived from
1354:. SoftNews. 18 November 2013
1268:Linux (based on Thinstation)
655:Version 4.0 also moved from
561:file system in 1999 and for
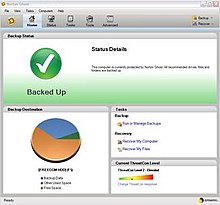
274:Norton Ghost v15 home screen
27:Disk cloning and backup tool
923:in order to function fully.
716:A Norton GHOST version for
617:Version 4.0 of GHOST added
2430:
2017:Veritas Storage Foundation
1696:"LiveUpdate for GSS 2.5.1"
565:subsequently. Support for
29:
2348:
2269:Leonard Development Group
1187:versions of Windows, and
1160:Norton Backup And Restore
1067:Improved platform support
963:external hard disk drives
859:Acquisition of PowerQuest
694:text-based user interface
375:
329:
318:
267:
258:
117:"Ghost" disk utility
32:Ghost (blogging platform)
2264:Fifth Generation Systems
2098:Norton Personal Firewall
2088:Norton Internet Security
1519:Peter's z80.eu site blog
1247:image format (.pqi) and
1030:devices and support for
1028:network-attached storage
956:USB mass storage devices
698:graphical user interface
474:originally developed by
1382:. Broadcom. 3 June 2020
1288:'s bootable CD using a
1016:Volume Snapshot Service
466:) for enterprise, is a
2289:Peter Norton Computing
2244:Central Point Software
2022:Veritas Volume Manager
1667:"Ghost Solution Suite"
1623:community.broadcom.com
1282:Windows Server 2008 R2
1151:
745:GHOST 7.0 / GHOST 2002
732:GHOST 6.0 (GHOST 2001)
681:GHOST 5.0 (GHOST 2000)
460:™ GHOST Solution Suite
340:; 14 years ago
93:relies excessively on
2309:Recourse Technologies
2234:Breakthrough Software
1969:Norton System Insight
1149:
685:Version 5.0 moved to
358:; 4 years ago
2394:Gen Digital software
1868:Avast SecureLine VPN
1863:Avast Secure Browser
1702:on January 11, 2010.
1655:on 17 December 2012.
1189:GUID Partition Table
738:system administrator
728:, like the others).
2350:† Demerged in 2016
2012:Veritas File System
1959:Norton Power Eraser
1486:on December 7, 2005
1074:-encrypted volumes
1024:incremental backups
798:Transition from DOS
395:Windows Server 2008
255:
2108:Norton SystemWorks
2083:Norton ConnectSafe
1416:on March 20, 2019.
1152:
1150:Symantec GHOST 8.2
921:Product Activation
770:Symantec GHOST 8.0
281:Original author(s)
2381:
2380:
2304:Quest Development
2229:Blue Coat Systems
2207:Piriform Software
2171:
2170:
2093:Norton PC Checkup
2073:Norton CleanSweep
1954:Norton LiveUpdate
1823:Frank E. Dangeard
1629:on 31 August 2020
1535:No cloning around
1274:
1273:
1125:
1124:
1113:Microsoft Hyper-V
1104:Microsoft Hyper-V
1042:Norton GHOST 15.0
1010:Norton GHOST 14.0
978:Norton GHOST 12.0
950:disks as well as
938:Norton GHOST 10.0
842:Norton GHOST 2003
712:GHOST for NetWare
702:partition manager
613:GHOST 4.0 and 4.1
588:GHOST 1.0 and 2.0
442:
441:
370:
369:
324:Stable release(s)
251:
250:
243:
233:
232:
225:
199:used on Knowledge
197:encyclopedic tone
178:
177:
170:
152:
75:
16:(Redirected from
2421:
2409:Storage software
2369:
2368:
2357:
2356:
2340:Whitewater Group
2334:Veritas Software
2279:LIRIC Associates
2202:AVG Technologies
2113:Norton Utilities
2078:Norton Commander
1997:Enterprise Vault
1939:Norton AntiVirus
1843:
1790:
1783:
1776:
1767:
1742:
1741:
1739:
1738:
1724:
1718:
1717:
1710:
1704:
1703:
1698:. Archived from
1692:
1686:
1685:
1683:
1682:
1677:on June 21, 2008
1673:. Archived from
1663:
1657:
1656:
1645:
1639:
1638:
1636:
1634:
1625:. Archived from
1615:
1609:
1608:
1606:
1604:
1599:on July 28, 2014
1595:. Archived from
1589:
1583:
1582:
1580:
1578:
1573:on 20 April 2017
1569:. Archived from
1563:
1554:
1553:
1552:. 20 April 2010.
1546:
1540:
1539:
1538:. Network world.
1529:
1523:
1522:
1510:
1495:
1494:
1492:
1491:
1482:. Archived from
1472:
1466:
1465:
1463:
1461:
1452:
1444:
1438:
1437:
1435:
1434:
1424:
1418:
1417:
1398:
1392:
1391:
1389:
1387:
1370:
1364:
1363:
1361:
1359:
1342:
1209:
1195:(EFI) firmware.
1049:
671:Pharlap Extender
543:sector-by-sector
438:
435:
381:Operating system
366:
364:
359:
348:
346:
341:
332:
314:
312:
272:
263:
256:
246:
239:
228:
221:
217:
214:
208:
207:for suggestions.
203:See Knowledge's
188:
187:
180:
173:
166:
162:
159:
153:
151:
110:
86:
78:
67:
45:
44:
37:
21:
18:Ghost (software)
2429:
2428:
2424:
2423:
2422:
2420:
2419:
2418:
2404:Backup software
2384:
2383:
2382:
2377:
2344:
2219:Binary Research
2178:
2167:
2148:THINK Reference
2103:Norton Security
2026:
1980:
1964:Norton Safe Web
1858:Avast Antivirus
1834:
1829:Vincent Pilette
1799:
1794:
1751:
1746:
1745:
1736:
1734:
1726:
1725:
1721:
1712:
1711:
1707:
1694:
1693:
1689:
1680:
1678:
1665:
1664:
1660:
1647:
1646:
1642:
1632:
1630:
1617:
1616:
1612:
1602:
1600:
1591:
1590:
1586:
1576:
1574:
1565:
1564:
1557:
1548:
1547:
1543:
1531:
1530:
1526:
1513:Dassow, Peter.
1512:
1511:
1498:
1489:
1487:
1474:
1473:
1469:
1459:
1457:
1450:
1446:
1445:
1441:
1432:
1430:
1426:
1425:
1421:
1400:
1399:
1395:
1385:
1383:
1372:
1371:
1367:
1357:
1355:
1344:
1343:
1339:
1334:
1322:
1297:
1256:PreOS boot disk
1204:
1177:
1168:
1144:
1139:
1137:Enterprise line
1130:
1128:Discontinuation
1098:files, or to a
1044:
1012:
1003:
980:
971:
954:(FireWire) and
940:
886:
881:
861:
844:
800:
772:
755:
747:
734:
714:
683:
615:
603:
590:
575:
501:
480:Binary Research
432:
400:
371:
362:
360:
357:
344:
342:
339:
310:
308:
304:Initial release
275:
247:
236:
235:
234:
229:
218:
212:
209:
202:
193:This article's
189:
185:
174:
163:
157:
154:
111:
109:
103:
99:primary sources
87:
46:
42:
35:
28:
23:
22:
15:
12:
11:
5:
2427:
2425:
2417:
2416:
2411:
2406:
2401:
2396:
2386:
2385:
2379:
2378:
2376:
2375:
2363:
2349:
2346:
2345:
2343:
2342:
2337:
2331:
2326:
2321:
2316:
2311:
2306:
2301:
2296:
2291:
2286:
2281:
2276:
2271:
2266:
2261:
2256:
2251:
2246:
2241:
2236:
2231:
2226:
2221:
2216:
2211:
2210:
2209:
2204:
2194:
2189:
2183:
2181:
2173:
2172:
2169:
2168:
2166:
2165:
2160:
2155:
2150:
2145:
2140:
2135:
2130:
2125:
2120:
2118:PartitionMagic
2115:
2110:
2105:
2100:
2095:
2090:
2085:
2080:
2075:
2070:
2068:Norton AntiBot
2065:
2060:
2055:
2050:
2045:
2040:
2034:
2032:
2028:
2027:
2025:
2024:
2019:
2014:
2009:
2004:
1999:
1994:
1988:
1986:
1982:
1981:
1979:
1978:
1973:
1972:
1971:
1966:
1961:
1956:
1951:
1949:Norton Insight
1946:
1941:
1936:
1926:
1921:
1916:
1915:
1914:
1909:
1904:
1894:
1889:
1888:
1887:
1882:
1872:
1871:
1870:
1865:
1860:
1849:
1847:
1840:
1836:
1835:
1833:
1832:
1826:
1820:
1817:Gordon Eubanks
1814:
1807:
1805:
1801:
1800:
1795:
1793:
1792:
1785:
1778:
1770:
1764:
1763:
1758:
1750:
1749:External links
1747:
1744:
1743:
1719:
1716:. 2 June 2015.
1705:
1687:
1658:
1640:
1610:
1584:
1555:
1541:
1524:
1496:
1476:"Acquisitions"
1467:
1439:
1419:
1393:
1365:
1346:"Norton Ghost"
1336:
1335:
1333:
1330:
1329:
1328:
1321:
1318:
1296:
1293:
1272:
1271:
1270:
1269:
1266:
1257:
1253:
1252:
1237:
1233:
1232:
1229:
1225:
1224:
1221:
1220:DeployAnywhere
1217:
1216:
1213:
1203:
1200:
1176:
1173:
1167:
1164:
1143:
1140:
1138:
1135:
1129:
1126:
1123:
1122:
1119:
1108:
1107:
1088:
1084:
1083:
1080:
1076:
1075:
1068:
1064:
1063:
1061:
1057:
1056:
1053:
1043:
1040:
1011:
1008:
1002:
999:
979:
976:
970:
967:
939:
936:
928:
927:
924:
917:
911:
908:
905:
885:
882:
880:
877:
860:
857:
843:
840:
799:
796:
790:transfers via
771:
768:
754:
751:
746:
743:
733:
730:
718:Novell NetWare
713:
710:
690:protected mode
682:
679:
667:protected mode
614:
611:
602:
599:
589:
586:
574:
573:Early versions
571:
500:
497:
476:Murray Haszard
455:), now called
440:
439:
430:
426:
425:
420:
414:
413:
408:
402:
401:
399:
398:
392:
389:Windows XP SP3
385:
383:
377:
376:
373:
372:
368:
367:
354:
350:
349:
336:
330:
327:
326:
320:
319:
316:
315:
305:
301:
300:
295:
289:
288:
286:Murray Haszard
283:
277:
276:
273:
265:
264:
249:
248:
231:
230:
192:
190:
183:
176:
175:
90:
88:
81:
76:
50:
49:
47:
40:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
2426:
2415:
2412:
2410:
2407:
2405:
2402:
2400:
2397:
2395:
2392:
2391:
2389:
2374:
2373:
2364:
2362:
2361:
2352:
2351:
2347:
2341:
2338:
2335:
2332:
2330:
2327:
2325:
2324:SecurityFocus
2322:
2320:
2317:
2315:
2312:
2310:
2307:
2305:
2302:
2300:
2297:
2295:
2292:
2290:
2287:
2285:
2284:ON Technology
2282:
2280:
2277:
2275:
2272:
2270:
2267:
2265:
2262:
2260:
2257:
2255:
2252:
2250:
2247:
2245:
2242:
2240:
2237:
2235:
2232:
2230:
2227:
2225:
2222:
2220:
2217:
2215:
2212:
2208:
2205:
2203:
2200:
2199:
2198:
2195:
2193:
2190:
2188:
2185:
2184:
2182:
2180:
2177:Acquisitions
2174:
2164:
2161:
2159:
2156:
2154:
2151:
2149:
2146:
2144:
2141:
2139:
2136:
2134:
2131:
2129:
2126:
2124:
2121:
2119:
2116:
2114:
2111:
2109:
2106:
2104:
2101:
2099:
2096:
2094:
2091:
2089:
2086:
2084:
2081:
2079:
2076:
2074:
2071:
2069:
2066:
2064:
2061:
2059:
2056:
2054:
2051:
2049:
2046:
2044:
2041:
2039:
2036:
2035:
2033:
2029:
2023:
2020:
2018:
2015:
2013:
2010:
2008:
2005:
2003:
2000:
1998:
1995:
1993:
1990:
1989:
1987:
1983:
1977:
1974:
1970:
1967:
1965:
1962:
1960:
1957:
1955:
1952:
1950:
1947:
1945:
1944:Norton Family
1942:
1940:
1937:
1935:
1932:
1931:
1930:
1927:
1925:
1922:
1920:
1917:
1913:
1910:
1908:
1905:
1903:
1900:
1899:
1898:
1895:
1893:
1890:
1886:
1885:AVG PC TuneUp
1883:
1881:
1880:AVG AntiVirus
1878:
1877:
1876:
1873:
1869:
1866:
1864:
1861:
1859:
1856:
1855:
1854:
1851:
1850:
1848:
1844:
1841:
1837:
1831:(current CEO)
1830:
1827:
1824:
1821:
1818:
1815:
1812:
1809:
1808:
1806:
1802:
1798:
1791:
1786:
1784:
1779:
1777:
1772:
1771:
1768:
1762:
1761:Symantec News
1759:
1756:
1753:
1752:
1748:
1733:
1729:
1723:
1720:
1715:
1709:
1706:
1701:
1697:
1691:
1688:
1676:
1672:
1668:
1662:
1659:
1654:
1650:
1644:
1641:
1628:
1624:
1620:
1614:
1611:
1598:
1594:
1588:
1585:
1572:
1568:
1562:
1560:
1556:
1551:
1545:
1542:
1537:
1536:
1528:
1525:
1520:
1516:
1509:
1507:
1505:
1503:
1501:
1497:
1485:
1481:
1477:
1471:
1468:
1456:
1449:
1443:
1440:
1429:
1423:
1420:
1415:
1411:
1407:
1403:
1397:
1394:
1381:
1380:
1375:
1369:
1366:
1353:
1352:
1347:
1341:
1338:
1331:
1327:
1324:
1323:
1319:
1317:
1315:
1310:
1308:
1303:
1300:
1294:
1292:
1291:
1287:
1283:
1279:
1267:
1264:
1260:
1259:
1258:
1255:
1254:
1250:
1246:
1242:
1238:
1236:Image formats
1235:
1234:
1230:
1227:
1226:
1222:
1219:
1218:
1214:
1211:
1210:
1207:
1201:
1199:
1196:
1194:
1190:
1186:
1182:
1181:Windows Vista
1174:
1172:
1165:
1163:
1161:
1157:
1148:
1141:
1136:
1134:
1127:
1120:
1118:
1114:
1110:
1109:
1105:
1101:
1097:
1093:
1089:
1086:
1085:
1081:
1078:
1077:
1073:
1069:
1066:
1065:
1062:
1059:
1058:
1054:
1051:
1050:
1047:
1041:
1039:
1035:
1033:
1029:
1025:
1021:
1017:
1009:
1007:
1000:
998:
996:
992:
987:
985:
984:Windows Vista
977:
975:
968:
966:
964:
961:
957:
953:
949:
945:
937:
935:
934:activation).
931:
925:
922:
918:
915:
912:
909:
906:
903:
899:
898:V2i Protector
895:
891:
890:
889:
883:
879:Consumer line
878:
876:
873:
870:
866:
858:
856:
854:
850:
841:
839:
837:
832:
830:
826:
822:
817:
815:
811:
806:
797:
795:
793:
789:
785:
781:
777:
769:
767:
765:
761:
752:
750:
744:
742:
739:
731:
729:
727:
723:
719:
711:
709:
707:
703:
699:
695:
692:. Unlike the
691:
688:
680:
678:
676:
672:
668:
665:
661:
658:
653:
651:
648:
644:
640:
636:
632:
628:
624:
620:
612:
610:
608:
600:
598:
596:
587:
585:
582:
580:
572:
570:
568:
564:
560:
556:
552:
548:
544:
540:
535:
533:
529:
525:
521:
516:
514:
510:
506:
498:
496:
494:
490:
487:
485:
481:
477:
473:
469:
465:
461:
459:
454:
450:
446:
437:
431:
427:
424:
421:
419:
415:
412:
409:
407:
403:
396:
393:
390:
387:
386:
384:
382:
378:
374:
355:
351:
337:
333:
328:
325:
321:
317:
306:
302:
299:
296:
294:
290:
287:
284:
282:
278:
271:
266:
262:
257:
245:
242:
227:
224:
216:
206:
200:
198:
191:
182:
181:
172:
169:
161:
150:
147:
143:
140:
136:
133:
129:
126:
122:
119: –
118:
114:
113:Find sources:
107:
101:
100:
96:
91:This article
89:
85:
80:
79:
74:
72:
65:
64:
59:
58:
53:
48:
39:
38:
33:
19:
2414:Disk cloning
2371:
2358:
2043:Norton Ghost
2031:Discontinued
1811:Gary Hendrix
1735:. Retrieved
1722:
1708:
1700:the original
1690:
1679:. Retrieved
1675:the original
1661:
1653:the original
1643:
1631:. Retrieved
1627:the original
1622:
1613:
1601:. Retrieved
1597:the original
1587:
1575:. Retrieved
1571:the original
1544:
1534:
1527:
1518:
1488:. Retrieved
1484:the original
1470:
1458:. Retrieved
1454:
1442:
1431:. Retrieved
1422:
1414:the original
1405:
1396:
1384:. Retrieved
1377:
1368:
1356:. Retrieved
1349:
1340:
1311:
1309:filesystem.
1304:
1301:
1298:
1275:
1215:Description
1205:
1197:
1178:
1169:
1159:
1155:
1153:
1131:
1117:Blu-ray Disc
1111:Support for
1055:Description
1045:
1036:
1013:
1004:
988:
981:
972:
941:
932:
929:
887:
874:
862:
845:
833:
818:
801:
788:peer-to-peer
773:
756:
748:
735:
715:
684:
654:
650:file systems
616:
604:
591:
583:
576:
536:
524:virtual disk
517:
502:
491:
488:
478:in 1995 for
468:disk cloning
463:
456:
452:
444:
443:
411:Disk cloning
293:Developer(s)
237:
219:
210:
194:
164:
155:
145:
138:
131:
124:
112:
92:
68:
61:
55:
54:Please help
51:
2299:Quarterdeck
2179:and mergers
2158:Visual Café
2038:Drive Image
1992:Backup Exec
1819:(1990s CEO)
1797:Gen Digital
1228:Hot imaging
914:Incremental
872:customers.
869:Drive Image
675:compression
472:backup tool
2388:Categories
2294:PowerQuest
2259:Fast Track
2239:Brightmail
2123:pcAnywhere
2063:Norton 360
1934:Norton 360
1902:Defraggler
1825:(Chairman)
1737:2017-12-12
1681:2008-10-16
1633:12 January
1490:2008-04-14
1433:2008-06-11
1358:1 December
1332:References
1263:Windows PE
1245:PowerQuest
1100:VMware ESX
991:Windows RE
944:Iomega Zip
902:PowerQuest
894:DriveImage
865:PowerQuest
853:LiveUpdate
829:Windows PE
607:partitions
555:Windows NT
551:Windows NT
505:Windows PE
363:2020-06-03
353:Enterprise
345:2010-04-01
213:March 2021
158:March 2021
128:newspapers
95:references
57:improve it
2053:GrandView
1813:(founder)
1351:Softpedia
1278:Windows 7
1072:BitLocker
995:ISO image
952:IEEE 1394
919:Requires
784:multicast
753:GHOST 7.5
657:real-mode
623:ImageCast
619:multicast
601:GHOST 3.1
423:Trialware
397:and later
391:and later
63:talk page
2360:Category
2329:TurnTide
2274:LifeLock
2224:BindView
2153:TimeLine
1985:Spin off
1924:LifeLock
1897:CCleaner
1839:Products
1732:Symantec
1671:Symantec
1480:Symantec
1455:Broadcom
1410:Symantec
1386:9 August
1379:Broadcom
1320:See also
1249:Symantec
849:diskette
579:Auckland
534:format.
499:Features
493:Broadcom
484:Symantec
458:Symantec
335:Consumer
298:Symantec
2372:Commons
2319:Riptech
2314:Revivio
2249:Delrina
2192:Altiris
2143:THINK C
2128:Q&A
1846:Current
1603:23 June
1577:8 March
1460:Oct 16,
1406:Support
1261:64-bit
1212:Feature
1106:server
1052:Feature
821:FreeBSD
780:unicast
631:Windows
449:acronym
429:Website
418:License
361: (
343: (
309: (
142:scholar
2187:@stake
2163:WinFax
2048:GoBack
1929:Norton
1912:Speccy
1907:Recuva
1804:People
1286:BartPE
960:Maxtor
836:BartPE
792:TCP/IP
776:BartPE
627:backup
520:volume
144:
137:
130:
123:
115:
2214:Avira
2197:Avast
1976:SONAR
1892:Avira
1853:Avast
1451:(PDF)
825:Linux
706:Fdisk
513:mount
445:GHOST
434:ghost
254:Ghost
149:JSTOR
135:books
2133:SQZ!
2058:MORE
1635:2022
1605:2014
1579:2014
1462:2023
1388:2020
1360:2013
1314:iPXE
1307:ext4
1280:and
1241:VMDK
1115:and
1092:VMDK
1032:NTFS
946:and
810:SCSI
786:and
764:DVDs
760:CD-R
669:via
647:NTFS
645:and
643:EXT3
639:EXT2
595:OS/2
567:EXT4
563:EXT3
559:EXT2
547:NTFS
528:VMDK
470:and
451:for
447:(an
436:.com
406:Type
311:1995
307:1995
121:news
2138:SUM
1919:HMA
1875:AVG
1185:x64
1102:or
1096:VHD
1094:or
1020:FTP
948:Jaz
827:or
814:USB
805:DOS
726:DOS
722:NSS
687:386
664:286
662:to
660:DOS
635:FAT
539:FAT
532:VHD
530:or
526:in
509:PXE
464:GSS
97:to
2390::
1730:.
1669:.
1621:.
1558:^
1517:.
1499:^
1478:.
1453:.
1408:.
1404:.
1376:.
1348:.
1183:,
823:,
812:,
782:,
766:.
641:,
597:.
486:.
108:.
66:.
2336:†
1789:e
1782:t
1775:v
1740:.
1684:.
1637:.
1607:.
1581:.
1521:.
1493:.
1464:.
1436:.
1390:.
1362:.
904:.
896:/
462:(
365:)
347:)
313:)
244:)
238:(
226:)
220:(
215:)
211:(
201:.
171:)
165:(
160:)
156:(
146:·
139:·
132:·
125:·
102:.
73:)
69:(
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.