89:(NIST) posed the "Key Wrap" problem: to develop secure and efficient cipher-based key encryption algorithms. The resulting algorithms would be formally evaluated by NIST, and eventually approved for use in NIST-certified cryptographic modules. NIST did not precisely define the security goals of the resulting algorithm, and left further refinement to the algorithm developers. Based on the resulting algorithms, the design requirements appear to be (1) confidentiality, (2) integrity protection (authentication), (3) efficiency, (4) use of standard (approved) underlying primitives such as the
178:, while the AKW2 algorithm is designed to be secure only under known-plaintext (or weaker) attacks. (The stated goal of AKW2 is for use in legacy systems and computationally limited devices where use of the other algorithms would be impractical.) AESKW, TDKW and AKW2 also provide the ability to authenticate cleartext "header", an associated block of data that is not encrypted.
105:
50:(encrypt) cryptographic key material. The Key Wrap algorithms are intended for applications such as protecting keys while in untrusted storage or transmitting keys over untrusted communications networks. The constructions are typically built from standard primitives such as
184:
and
Shrimpton evaluated the design of the ANSX9.102 algorithms with respect to the stated security goals. Among their general findings, they noted the lack of clearly stated design goals for the algorithms, and the absence of security proofs for all constructions.
97:), and (5) consideration of additional circumstances (e.g., resilience to operator error, low-quality random number generators). Goals (3) and (5) are particularly important, given that many widely deployed
192:
and
Shrimpton proposed a provable key-wrapping algorithm (SIV—the Synthetic Initialization Vector mode) that authenticates and encrypts an arbitrary string and authenticates, but does not encrypt,
86:
77:). Key Wrap algorithms can be used in a similar application: to securely transport a session key by encrypting it under a long-term encryption key.
174:
messages such as cryptographic keys. The AES Key Wrap
Specification, AESKW, TDKW, and AKW1 are intended to maintain confidentiality under
375:
175:
240:
228:
90:
275:"RFC 5297: Synthetic Initialization Vector (SIV) Authenticated Encryption Using the Advanced Encryption Standard (AES)"
55:
28:
218:
213:
167:
98:
258:
344:
293:
43:
249:
117:
288:
323:
171:
74:
70:
62:
47:
197:
122:
196:
which can be bound into the wrapped key. This has been standardized as a new AES mode in
189:
181:
223:
369:
101:
algorithms (e.g., AES-CCM) are already sufficient to accomplish the remaining goals.
51:
35:
201:
126:
104:
151:
261:
Recommendation for Block Cipher Modes of
Operation: Methods for Key Wrapping
65:
algorithm, although it should not be confused with the more commonly known
17:
268:
American
Standards Committee, Request for Review of Key Wrap Algorithms
267:
137:
274:
103:
94:
283:
193:
166:
Each of the proposed algorithms can be considered as a form of
112:
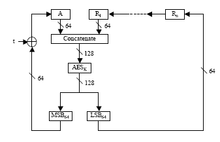
Several constructions have been proposed. These include:
243:
A Provable-Security
Treatment of the Key-Wrap Problem
170:algorithm providing confidentiality for highly
87:National Institute of Standards and Technology
8:
132:Implemented by the WebCrypto subtle API.
61:Key Wrap may be considered as a form of
315:
138:American Standards Committee ANSX9.102
93:(AES) and the Secure Hash Algorithm (
7:
150:TDKW (similar to AESKW, built from
259:NIST Special Publication 800-38F,
176:adaptive chosen ciphertext attacks
25:
140:, which defines four algorithms:
296:from the original on 3 June 2015
108:NIST AES Key Wrap Specification
157:AKW1 (TDES, two rounds of CBC)
1:
160:AKW2 (TDES, CBC then CBC-MAC)
42:constructions are a class of
273:Dan Harkins (October 2008).
229:Offline private key protocol
91:Advanced Encryption Standard
56:cryptographic hash functions
241:P. Rogaway, T. Shrimpton.
29:key encapsulation mechanism
392:
282:Krohn, Max; Coyne, Chris.
252:AES Key Wrap Specification
145:AES Key Wrap Specification
118:AES Key Wrap Specification
27:Not to be confused with a
26:
376:Cryptographic algorithms
219:Deterministic encryption
214:Authenticated encryption
168:authenticated encryption
143:AESKW (a variant of the
99:authenticated encryption
85:In the late 1990s, the
46:algorithms designed to
345:"Web Cryptography API"
109:
107:
324:"Key wrap algorithm"
44:symmetric encryption
110:
73:algorithms (e.g.,
154:rather than AES).
71:key encapsulation
63:key encapsulation
16:(Redirected from
383:
360:
359:
357:
355:
341:
335:
334:
332:
330:
320:
305:
303:
301:
278:
188:In their paper,
121:(November 2001,
21:
391:
390:
386:
385:
384:
382:
381:
380:
366:
365:
364:
363:
353:
351:
343:
342:
338:
328:
326:
322:
321:
317:
312:
299:
297:
281:
272:
263:(December 2012)
254:(November 2001)
237:
235:Further reading
210:
194:associated data
83:
32:
23:
22:
15:
12:
11:
5:
389:
387:
379:
378:
368:
367:
362:
361:
336:
314:
313:
311:
308:
307:
306:
279:
270:
265:
256:
247:
236:
233:
232:
231:
226:
224:Key management
221:
216:
209:
206:
164:
163:
162:
161:
158:
155:
148:
135:
134:
133:
82:
79:
24:
14:
13:
10:
9:
6:
4:
3:
2:
388:
377:
374:
373:
371:
350:
346:
340:
337:
325:
319:
316:
309:
295:
291:
290:
285:
280:
276:
271:
269:
266:
264:
262:
257:
255:
253:
248:
246:
244:
239:
238:
234:
230:
227:
225:
222:
220:
217:
215:
212:
211:
207:
205:
203:
199:
195:
191:
186:
183:
179:
177:
173:
169:
159:
156:
153:
149:
146:
142:
141:
139:
136:
131:
130:
128:
124:
120:
119:
115:
114:
113:
106:
102:
100:
96:
92:
88:
80:
78:
76:
72:
69:(public-key)
68:
64:
59:
57:
53:
52:block ciphers
49:
45:
41:
37:
30:
19:
352:. Retrieved
348:
339:
327:. Retrieved
318:
298:. Retrieved
287:
260:
251:
242:
187:
180:
165:
144:
116:
111:
84:
66:
60:
39:
36:cryptography
33:
284:"TripleSec"
48:encapsulate
354:16 October
349:www.w3.org
310:References
152:Triple DES
81:Background
67:asymmetric
370:Category
294:Archived
208:See also
172:entropic
75:PSEC-KEM
40:key wrap
18:Key Wrap
289:Keybase
277:. IETF.
190:Rogaway
182:Rogaway
329:26 May
250:NIST,
200:
125:
300:2 Jan
95:SHA-1
356:2019
331:2016
302:2021
202:5297
127:3394
54:and
198:RFC
123:RFC
34:In
372::
347:.
292:.
286:.
204:.
129:)
58:.
38:,
358:.
333:.
304:.
245:.
147:)
31:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.