180:
168:
51:
which will increase the number of message collisions and will provide several copies of the same information from similarly located nodes. However, the administrator has control over some parameters of the network: transmission power of the nodes, state of the nodes (active or sleeping), role of the nodes (Clusterhead, gateway, regular), etc. By modifying these parameters, the topology of the network can change.
156:
55:
in wireless sensor networks with multihopping, intensive packet forwarding causes nodes that are closer to the sink to spend higher amounts of energy than nodes that are farther away. Topology control has to be executed periodically in order to preserve the desired properties such as connectivity, coverage, density.
54:
Upon the same time a topology is reduced and the network starts serving its purpose, the selected nodes start spending energy: Reduced topology starts losing its "optimality as soon as full network activity evolves. After some time being active, some nodes will start to run out of energy. Especially
26:
The term "topology control" is used mostly by the wireless ad hoc and sensor networks research community. The main aim of topology control in this domain is to save energy, reduce interference between nodes and extend lifetime of the network. However, recently the term has also been gaining traction
271:
In all of the above protocols can be found in. In
Atarraya, two version of each of these protocols are implemented with different triggers: one by time, and the other one by energy. In addition, Atarraya allows the pairing of all the topology construction and topology maintenance protocols in order
22:
is a technique used in distributed computing to alter the underlying network (modeled as a graph) to reduce the cost of distributed algorithms if run over the resulting graphs. It is a basic technique in distributed algorithms. For instance, a (minimum) spanning tree is used as a backbone to reduce
311:
Atarraya is an event-driven simulator developed in Java that present a new framework for designing and testing topology control algorithms. It is an open source application, distributed under the GNU V.3 license. It was developed by Pedro
Wightman, a Ph.D. candidate at University of South Florida,
50:
This is the first stage of a topology control protocol. Once the initial topology is deployed, specially when the location of the nodes is random, the administrator has no control over the design of the network; for example, some areas may be very dense, showing a high number of redundant nodes,
237:
Initially, the topology construction protocol must create more than one reduced topology (hopefully as disjoint as possible). Then, periodically, wake up all inactive nodes, and change the current active reduced topology to the next, like in a
Christmas tree.
248:
Work as the SGTRot, but when the current active reduced topology detects a certain level of disconnection, reset the reduced topology and invoke the topology construction protocol to recreate that particular reduced topology.
179:
272:
to test the optimal maintenance policy for a particular construction protocol; it is important to mention that many papers on topology construction have not performed any study on this regard.
458:
317:
308:
There are many networking simulation tools, however there is one specifically designed for testing, design and teaching topology control algorithms: Atarraya.
287:
Topology
Control in Wireless Sensor Networks: with a companion simulation tool for teaching and research. Miguel Labrador and Pedro Wightman. Springer. 2009.
400:
167:
140:
536:
425:
185:
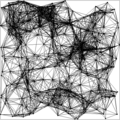
Reduced network topology via
Connected Dominating Set (Select a subset of nodes that cover all the network and turn off non-selected nodes)
226:
Periodically, wake up all inactive nodes, reset the existing reduced topology in the network and apply a topology construction protocol.
357:
559:
502:, Proc. ACM Int'l Conf. on Mobile Comp. and Netw. (MobiCom'03), pp. 286--299, San Diego, California, USA, Sept. 14--19, 2003.
47:, in charge of the maintenance of the reduced topology so that characteristics like connectivity and coverage are preserved.
369:
23:
the cost of broadcast from O(m) to O(n), where m and n are the number of edges and vertices in the graph, respectively.
312:
with the collaboration of Dr. Miguel
Labrador. A paper with the detailed description of the simulator was presented in
104:
293:
Protocols and
Architectures for Wireless Sensor Networks. Holger Karl and Andreas Willig. Wiley-Interscience. 2007.
554:
155:
265:
117:
28:
414:
195:
In the same manner as topology construction, there are many ways to perform topology maintenance:
83:
394:
335:
524:
Protocols and
Architectures for Wireless Sensor Networks by Holger Karl and Andreas Willig
108:
268:(DSR) routing algorithm, recreates the paths of disconnected nodes when a node fails.
548:
296:
Capacity-Optimized
Topology Control for MANETs with Cooperative Communications. 2011.
100:
290:
Topology
Control in Wireless Ad Hoc and Sensor Networks. Paolo Santi. Wiley. 2005.
376:
447:
436:
346:
499:
537:
Capacity-Optimized Topology Control for MANETs with Cooperative Communications
487:
39:
Lately, topology control algorithms have been divided into two subproblems:
539:,” IEEE Trans. Wireless Comm., vol. 10, no. 7, pp. 2162-2170, July 2011.
489:, Atarraya, a simulator for topology control in wireless sensor networks
523:
511:
472:
173:
Reduced network topology via Minimal Spanning Tree (Change in Tx Range)
299:
Robust Topology control for indoor wireless sensor networks. 2008 .
313:
284:
Topology Control for Wireless Sensor Networks. ACM MobiCom 2003.
526:, Protocols and Architectures for Wireless Sensor Networks
243:
HGTRotRec (Hybrid Global Topology Rotation and Recreation)
82:
Adding new nodes to the network to preserve connectivity (
514:, Topology Control in Wireless Ad Hoc and Sensor Networks
67:
Optimizing the node locations during the deployment phase
90:
Some examples of topology construction algorithms are:
280:
Many books and papers have been written in the topic:
210:
Some examples of topology maintenance algorithms are:
63:
There are many ways to perform topology construction:
120:, Cone Based Topology Control (CBTC), Distributed RNG
27:
with regards to control of the network structure of
205:Triggered by time, energy, density, random, etc.
535:Q. Guan, F.R. Yu, S. Jiang, and V.C.M. Leung, “
475:, Topology Control in Wireless Sensor Networks
427:, A3: A topology construction protocol for WSN
500:Topology control for wireless sensor networks
498:J. Pan, Y. Hou, L. Cai, Y. Shi, and X. Shen,
8:
483:
481:
220:DGTRec (Dynamic Global Topology Recreation)
70:Change the transmission range of the nodes
43:, in charge of the initial reduction, and
473:Topology Control by Labrador and Wightman
468:
466:
231:SGTRot (Static Global Topology Rotation)
141:Low Energy Adaptive Clustering Hierarchy
328:
151:
399:: CS1 maint: archived copy as title (
392:
35:Topology construction and maintenance
7:
259:DL-DSR (Dynamic Local DSR-based TM)
14:
348:, Iterative Minimum Spanning Tree
316:. The paper can be found in this
178:
166:
154:
136:CDS-based: A3, EECDS, CDS-Rule K
59:Topology construction algorithms
191:Topology maintenance algorithms
116:Direction Based: Yao graph and
113:Spanning Tree Based: LMST, iMST
76:Create a communication backbone
73:Turn off nodes from the network
304:Simulation of topology control
1:
337:, Local Minimal Spanning Tree
202:Dynamic Vs. Static Vs. Hybrid
264:This protocol, based on the
161:Full power network topology
123:Neighbor based: KNeigh, XTC
105:Relative neighborhood graph
576:
512:Topology Control by Santi
560:Wireless sensor network
266:Dynamic Source Routing
118:Nearest neighbor graph
29:electric power systems
126:Routing based: COMPOW
41:topology construction
45:topology maintenance
16:Computing technique
148:Graphical examples
84:Federated Wireless
567:
555:Network topology
540:
533:
527:
521:
515:
509:
503:
496:
490:
485:
476:
470:
461:
456:
450:
445:
439:
434:
428:
423:
417:
412:
406:
404:
398:
390:
388:
387:
381:
375:. Archived from
374:
366:
360:
355:
349:
344:
338:
333:
199:Global Vs. Local
182:
170:
158:
99:Geometry-based:
86:sensor networks)
20:Topology control
575:
574:
570:
569:
568:
566:
565:
564:
545:
544:
543:
534:
530:
522:
518:
510:
506:
497:
493:
486:
479:
471:
464:
457:
453:
446:
442:
435:
431:
424:
420:
413:
409:
391:
385:
383:
379:
372:
370:"Archived copy"
368:
367:
363:
356:
352:
345:
341:
334:
330:
326:
306:
278:
276:Further reading
255:
216:
209:
193:
186:
183:
174:
171:
162:
159:
150:
139:Cluster-based:
133:
109:Voronoi diagram
96:
61:
37:
17:
12:
11:
5:
573:
571:
563:
562:
557:
547:
546:
542:
541:
528:
516:
504:
491:
477:
462:
451:
440:
429:
418:
407:
361:
350:
339:
327:
325:
322:
314:SIMUTools 2009
305:
302:
301:
300:
297:
294:
291:
288:
285:
277:
274:
262:
261:
254:
251:
246:
245:
235:
234:
224:
223:
215:
212:
207:
206:
203:
200:
192:
189:
188:
187:
184:
177:
175:
172:
165:
163:
160:
153:
149:
146:
145:
144:
137:
132:
129:
128:
127:
124:
121:
114:
111:
95:
94:Tx range-based
92:
88:
87:
80:
77:
74:
71:
68:
60:
57:
36:
33:
15:
13:
10:
9:
6:
4:
3:
2:
572:
561:
558:
556:
553:
552:
550:
538:
532:
529:
525:
520:
517:
513:
508:
505:
501:
495:
492:
488:
484:
482:
478:
474:
469:
467:
463:
459:
455:
452:
448:
444:
441:
437:
433:
430:
426:
422:
419:
416:, COMPOW , Hi
415:
411:
408:
402:
396:
382:on 2007-07-05
378:
371:
365:
362:
358:
354:
351:
347:
343:
340:
336:
332:
329:
323:
321:
319:
315:
309:
303:
298:
295:
292:
289:
286:
283:
282:
281:
275:
273:
269:
267:
260:
257:
256:
252:
250:
244:
241:
240:
239:
232:
229:
228:
227:
221:
218:
217:
213:
211:
204:
201:
198:
197:
196:
190:
181:
176:
169:
164:
157:
152:
147:
143:(LEACH), HEED
142:
138:
135:
134:
130:
125:
122:
119:
115:
112:
110:
106:
102:
101:Gabriel graph
98:
97:
93:
91:
85:
81:
78:
75:
72:
69:
66:
65:
64:
58:
56:
52:
48:
46:
42:
34:
32:
30:
24:
21:
531:
519:
507:
494:
454:
449:, CDS-Rule K
443:
432:
421:
410:
384:. Retrieved
377:the original
364:
353:
342:
331:
310:
307:
279:
270:
263:
258:
247:
242:
236:
230:
225:
219:
208:
194:
131:Hierarchical
89:
62:
53:
49:
44:
40:
38:
25:
19:
18:
549:Categories
386:2009-04-30
324:References
79:Clustering
395:cite web
359:, KNEIGH
438:, EECDS
107:(RNG),
460:, HEED
214:Global
103:(GG),
405:, XTC
380:(PDF)
373:(PDF)
253:Local
401:link
318:link
551::
480:^
465:^
397:}}
393:{{
320:.
31:.
403:)
389:.
233::
222::
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.