118:. However, in the 1980s, and especially in the mid-to-late 1990s and the early 2000s, everyday, regular people began using computer devices and software for personal and work use. IT specialists needed to cope with this trend in various ways. In the 2010s, users now want to have more control over the systems they operate, to solve their own problems, and be able to customize the systems to suit their needs. The apparent drawbacks were the risk of corruption of the systems and data the users had control of, due to their lack of knowledge on how to properly operate the computer/software at an advanced level.
38:
162:
173:(e.g., manuals and guidebooks for products) is to help the user understand certain aspects of the systems and to provide all the answers in one place. A lot of documentation is available for users to help them understand and properly use a certain product or service. Due to the fact that the information available is usually very vast, inconsistent or ambiguous (e.g., a user manual with hundreds of pages, including guidance on using advanced features), many users suffer from an
154:
231:
pre-existing knowledge of computers and software, and thus the directions may skip over these initial steps (from the users' point of view). Thus, frustrated user may report false problems because of their inability to understand the software or computer hardware. This in turn causes the company to focus on perceived problems instead of focusing on the actual problems of the software.
308:. As well, even with a well-secured system, if a worker decides to put the company's electronic files on a USB drive to take them home to work on them over the weekend (against many companies' policies), and then loses this USB drive, the company's data may be compromised. Therefore, developers need to make systems that are intuitive to the user in order to have
65:(IT) experts, software professionals, and computer technicians. End users typically do not possess the technical understanding or skill of the product designers, a fact easily overlooked and forgotten by designers: leading to features creating low customer satisfaction. In information technology, end users are not
366:
Andersson have conducted a number of studies on end-user security habits and found that the same type of repeated education/training in security best practices can have a marked effect on the perception of compliance with good end-user network security habits, especially concerning malware and ransomware.
315:
Another key step to end user security is informing the people and employees about the security threats and what they can do to avoid them or protect themselves and the organization. Clearly underlining, the capabilities and risks makes users more aware and informed whilst they are using the products.
109:
The concept of end-user first surfaced in the late 1980s and has since then raised many debates. One challenge was the goal to give both the user more freedom, by adding advanced features and functions (for more advanced users) and adding more constraints (to prevent a neophyte user from accidentally
121:
For companies to appeal to the user, it took primary care to accommodate and think of end-users in their new products, software launches, and updates. A partnership needed to be formed between the programmer-developers and the everyday end users so both parties could maximize the use of the products
360:
Even if the security measures in place are strong, the choices the user makes and his/her behavior have a major impact on how secure their information really is. Therefore, an informed user is one who can protect and achieve the best security out of the system they use. Because of the importance of
365:
learn how to be more security aware when using government networks and computers. While this is targeted to a certain sector, this type of educational effort can be informative to any type of user. This helps developers meet security norms and end users be aware of the risks involved. Reimers and
230:
At times users do not refer to the documentation available to them due to various reasons, ranging from finding the manual too large or due to not understanding the jargon and acronyms it contains. In other cases, the users may find that the manual makes too many assumptions about a user having
253:
with them and using them for scheduling appointments, making online purchases using credit cards and searching for information. These activities can potentially be observed by companies, governments or individuals, which can lead to breaches of privacy,
300:). The complexities of creating such a secure system come from the fact that the behaviour of humans is not always rational or predictable. Even in a very-well secured computer system, a malicious individual can telephone a worker and pretend to be a
122:
effectively. A major example of the public's effects on end user's requirements were the public libraries. They have been affected by new technologies in many ways, ranging from the digitalization of their card catalog, the shift to
768:
A party that ultimately uses a delivered product or that receives the benefit of a delivered service. (See also "customer".) End users may or may not also be customers (who can establish and accept agreements or authorize
281:, etc.). As such, it is important for people and organizations to need know that the information and data they are storing, using, or sending over computer networks or storing on computer systems is secure.
288:, accessible 24/7 on almost any device and be truly secure. Security leaks happen, even to individuals and organizations that have security measures in place to protect their data and information (e.g.,
202:, progressing to the information that intermediate or advanced users will need (these sections can include jargon and acronyms, but each new term should be defined or spelled out upon its first use)
97:
and
Information Technology department about his or her needs regarding the system or product. This raises new questions, such as: Who manages each resource?, What is the role of the
1188:
269:
to huge corporations are using computers and software to design, manufacture, market and sell their products and services, and businesses also use computers and software in their
177:. Therefore, they become unable to take the right course of action. This needs to be kept in mind when developing products and services and the necessary documentation for them.
1052:
619:
The end users are persons who perform the application functions. End users include "parametric" and generalized function users, but they are not system support personnel.
892:
Seidler-de Alwis, Ragna; Fühles-Ubach, Simone (2010). "Success factors for the future of information centres, commercial and public libraries: a study from
Germany".
245:
In the 2010s, there is a lot of emphasis on user's security and privacy. With the increasing role that computers are playing in people's lives, people are carrying
53:) is a person who ultimately uses or is intended to ultimately use a product. The end user stands in contrast to users who support or maintain the product, such as
606:
208:
Clear end results are described to the reader (e.g., "When the program is installed properly, an icon will appear in the left-hand corner of your screen and the
1075:
K. Reimers, D. Andersson (2017) POST-SECONDARY EDUCATION NETWORK SECURITY: THE END USER CHALLENGE AND EVOLVING THREATS, ICERI2017 Proceedings, pp. 1787–1796.
170:
582:
The term "end-user", with respect to a good, service, or technology, means the person that receives and ultimately uses the good, service, or technology.
382:
378:, the end user is distinguished from the value-added reseller, who installs the software or the organization that purchases and manages the software.
594:
215:
Detailed, numbered steps, to enable users with a range of proficiency levels (from novice to advanced) to go step-by-step to install, use and
1242:
790:
1196:
1145:
130:, and offering online services. Libraries have had to undergo many changes in order to cope, including training existing librarians in
1271:
693:
644:
496:
1160:
1125:
963:
753:
386:
996:
Stanton, Jeffrey M.; Stam, Kathryn R.; Mastrangelo, Paul; Jolton, Jeffrey (2005-03-01). "Analysis of end user security behaviors".
361:
end-user security and the impact it can have on organizations the UK government set out a guidance for the public sector, to help
194:
Structured provision of information, which goes from the most basic instructions, written in plain language, without specialist
165:
NATO official and Afghan colonel going through end-user documentation to transfer control of barracks to the Afghan army in 2009
381:
Certain
American defense-related products and information require export approval from the United States Government under the
93:; computer experts programmed and ran the mainframe) to one in the 2010s where the end user collaborates with and advises the
1266:
737:
488:
480:
841:
716:
at the terminal keyboard, requesting the database system to display the answer on a terminal screen or on a printed sheet.
389:. In order to obtain a license to export, the exporter must specify both the end user and the end use for undertaking an
98:
94:
946:
Strother, Judith B.; Ulijn, Jan M.; Fazal, Zohra (2012-01-01). Strother, Judith B.; Ulijn, Jan M.; Fazal, Zohra (eds.).
147:
396:
In the UK, there exist documents that accompany licenses for products named in the end user undertaking statements.
353:(using a person's own name, own birthdate, name or birthdate of children, or easy-to-guess passwords such as "1234")
284:
However, developers of software and hardware are faced with many challenges in developing a system that can be both
681:
375:
1110:
1024:
114:
of computer products and software. In the 1960s and 1970s, computer users were generally programming experts and
31:
77:
that purchased the software, the end users are the employees of the company, who will use the software at work.
223:
73:
corporation buys a software package for its employees to use, even though the large retail corporation was the
89:. The end user's position has changed from a position in the 1950s (where end users did not interact with the
37:
180:
Well-written documentation is needed for a user to reference. Some key aspects of such a documentation are:
1189:"Frequently asked questions on End-User Undertakings | Find Laws, Legal Information, News & Solicitors"
806:
LUPTON, CAROL (1998-02-01). "User
Empowerment or Family Self-Reliance? The Family Group Conference Model".
922:
62:
874:
415:
948:
Information
Overload: An International Challenge to Professional Engineers and Technical Communicators
410:
390:
309:
301:
289:
174:
58:
304:
working for the software company, and ask for the individual's password, a dishonest process called
484:
336:
emails of suspicious emails and/or opening/running attachments or computer files contained in these
161:
86:
444:
823:
636:
571:
405:
115:
90:
745:
1276:
1238:
1164:
959:
786:
759:
749:
699:
689:
685:
650:
640:
610:
502:
492:
326:
Auto-fill options, in which a computer or program remembers a user's personal information and
146:
This section is about generic system users materials. For consumable guides to software, see
1230:
1156:
1121:
1005:
951:
901:
815:
729:
708:
One of the most important features of a DBMS is that relatively inexperienced users, called
602:
567:
240:
226:(URLs) so that the user can go to the product website to find additional help and resources.
297:
274:
266:
111:
69:
in the usual sense—they are typically employees of the customer. For example, if a large
819:
865:
Kappelman, Leon A; Guynes, Carl
Stephen (1995). "End-user training & empowerment".
741:
670:
263:
255:
153:
452:
110:
erasing an entire company's database). This phenomenon appeared as a consequence of
1260:
730:
677:
362:
285:
101:? and What is the optimal relationship between the end-user and the MIS Department?
546:
The person who uses a computer application, as opposed to those who developed or it.
259:
216:
184:
Specific titles and subtitles for subsections to aid the reader in finding sections
559:
878:
732:
CMMI for
Development: Guidelines for Process Integration and Product Improvement
339:
Email can be monitored by third parties, especially when using Wi-Fi connections
333:
327:
270:
1009:
191:, text and links to help the reader understand how to use the device or program
85:
End users are one of the three major factors contributing to the complexity of
955:
905:
420:
293:
250:
188:
1222:
763:
1234:
712:, are empowered to retrieve information from the database. The user poses a
703:
654:
506:
455:. Thus, "good end-user experience" versus "good experience to the end user".
127:
783:
Introduction to
Information Systems. Supporting and Transforming Businesses
614:
350:
305:
135:
66:
827:
1085:
278:
199:
131:
17:
205:
Easy to search the help guide, find information and access information
535:
246:
195:
123:
70:
262:
and other serious concerns. As well, many businesses, ranging from
343:
160:
152:
54:
36:
980:
1223:"Teaching University Student End-Users about Online Searching"
209:
781:
Rainer Jr., R. Kelly; Prince, Brad; Cegielski, Casey (2014).
527:
1053:"End User Devices Security Guidance: Introduction – GOV.UK"
985:(Doctoral). Durham theses, Durham University. pp. 2–6.
597:
Task Group on
Database Management System Standards (1979).
346:
or use of a public Wi-Fi network at a coffee shop or hotel
728:
Chrissis, Mary Beth; Konrad, Mike; Shrum, Sandy (2011).
599:
Recommendations for
Database Management System Standards
157:
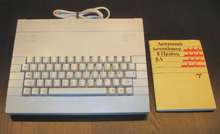
1980s-era personal computer with end-user documentation
319:
Some situations that could put the user at risk are:
1221:Ward, Sandra N.; Osegueda, Laura M. (2019-12-06),
669:
511:the person ultimately intended to use a product
30:"End-user" redirects here. For other uses, see
950:. John Wiley & Sons, Inc. pp. 1–12.
923:"10 Examples of Great End User Documentation"
639:: Irwin Professional Publishing. p. 20.
8:
672:Database Principles Programming Performance
633:Database Management: Theory and Application
138:skills, to hiring IT and software experts.
785:(Fifth ed.). Wiley. pp. 12–13.
477:Dictionary of Computer and Internet Terms
383:International Traffic in Arms Regulations
521:
519:
1227:Serving End-Users in Sci-Tech Libraries
842:"Can IT Cope With Empowered End-Users?"
468:
432:
41:Nurses as information systems end users
917:
915:
7:
1092:. Black's Law Dictionary. 2012-10-19
820:10.1093/oxfordjournals.bjsw.a011302
323:Auto-logon as administrator options
894:Interlending & Document Supply
808:The British Journal of Social Work
356:Malicious programs such as viruses
25:
1161:United States Department of State
1146:"Nontransfer and use certificate"
1126:United States Department of State
1111:"Defense trade controls overview"
979:Wilkinson, Paul Johnston (2003).
387:Export Administration Regulations
560:"U.S. Code § 8541 - Definitions"
738:Upper Saddle River, New Jersey
483:Business Guides (8 ed.).
1:
1229:, Routledge, pp. 17–32,
867:Journal of Systems Management
558:Legal Information Institute.
528:"FOLDOC entry for "end-user""
95:management information system
607:National Bureau of Standards
87:managing information systems
489:Barron's Educational Series
439:When used as an adjective,
376:end-user license agreements
148:Software user documentation
61:, database administrators,
45:In product development, an
1293:
1010:10.1016/j.cose.2004.07.001
682:Morgan Kaufmann Publishers
631:Shepherd, John C. (1990).
526:Howe, Denis (1997-03-29).
238:
145:
29:
1272:Export and import control
956:10.1002/9781118360491.ch1
906:10.1108/02641611011072387
187:Use of videos, annotated
32:End-user (disambiguation)
27:Regular user of a product
1023:Tribelhorn, Ben (2007).
998:Computers & Security
668:O'Neil, Patrick (1994).
224:Uniform Resource Locator
1235:10.4324/9780429346101-3
447:; when used as a noun,
982:End-user documentation
219:the product or service
166:
158:
142:End user documentation
63:information technology
42:
1267:Computing terminology
1034:. Harvey Mudd College
491:. 2003. p. 171.
416:Voice of the customer
312:and system security.
164:
156:
59:system administrators
40:
1153:www.pmddtc.state.gov
1118:www.pmddtc.state.gov
1090:thelawdictionary.org
927:blog.screensteps.com
873:(5). Cleveland: 36.
411:End-user development
391:end-user certificate
310:information security
302:private investigator
175:information overload
169:The aim of end user
1086:"What is END USER?"
1025:"End user security"
564:www.law.cornell.edu
485:Hauppauge, New York
116:computer scientists
637:Homewood, Illinois
572:Cornell Law School
406:End-user computing
167:
159:
43:
1244:978-0-429-34610-1
1032:Computer Security
792:978-1-118-67436-9
453:left unhyphenated
273:processes (e.g.,
212:will turn on...")
16:(Redirected from
1284:
1253:
1252:
1251:
1208:
1207:
1205:
1204:
1195:. Archived from
1185:
1179:
1178:
1176:
1175:
1169:
1163:. Archived from
1157:Washington, D.C.
1150:
1142:
1136:
1135:
1133:
1132:
1122:Washington, D.C.
1115:
1107:
1101:
1100:
1098:
1097:
1082:
1076:
1073:
1067:
1066:
1064:
1063:
1049:
1043:
1042:
1040:
1039:
1029:
1020:
1014:
1013:
993:
987:
986:
976:
970:
969:
943:
937:
936:
934:
933:
919:
910:
909:
889:
883:
882:
862:
856:
855:
853:
852:
838:
832:
831:
803:
797:
796:
778:
772:
771:
735:
725:
719:
718:
675:
665:
659:
658:
628:
622:
621:
603:Washington, D.C.
591:
585:
584:
579:
578:
568:Ithaca, New York
555:
549:
548:
543:
542:
523:
514:
513:
473:
456:
437:
298:strong passwords
241:User (computing)
21:
1292:
1291:
1287:
1286:
1285:
1283:
1282:
1281:
1257:
1256:
1249:
1247:
1245:
1220:
1217:
1212:
1211:
1202:
1200:
1187:
1186:
1182:
1173:
1171:
1167:
1148:
1144:
1143:
1139:
1130:
1128:
1113:
1109:
1108:
1104:
1095:
1093:
1084:
1083:
1079:
1074:
1070:
1061:
1059:
1051:
1050:
1046:
1037:
1035:
1027:
1022:
1021:
1017:
995:
994:
990:
978:
977:
973:
966:
945:
944:
940:
931:
929:
921:
920:
913:
891:
890:
886:
864:
863:
859:
850:
848:
840:
839:
835:
805:
804:
800:
793:
780:
779:
775:
756:
727:
726:
722:
696:
667:
666:
662:
647:
630:
629:
625:
593:
592:
588:
576:
574:
557:
556:
552:
540:
538:
525:
524:
517:
499:
475:
474:
470:
465:
460:
459:
438:
434:
429:
402:
372:
275:human resources
243:
237:
151:
144:
112:consumerization
107:
83:
35:
28:
23:
22:
15:
12:
11:
5:
1290:
1288:
1280:
1279:
1274:
1269:
1259:
1258:
1255:
1254:
1243:
1216:
1215:External links
1213:
1210:
1209:
1180:
1137:
1102:
1077:
1068:
1044:
1015:
1004:(2): 124–133.
988:
971:
964:
938:
911:
900:(3): 183–188.
884:
857:
833:
814:(1): 107–128.
798:
791:
773:
754:
742:Addison-Wesley
720:
695:978-1558602199
694:
660:
646:978-0256078299
645:
623:
609:. p. 58.
586:
550:
515:
498:978-0764121661
497:
467:
466:
464:
461:
458:
457:
431:
430:
428:
425:
424:
423:
418:
413:
408:
401:
398:
371:
368:
363:civil servants
358:
357:
354:
347:
340:
337:
330:
324:
264:small business
256:identity theft
236:
233:
228:
227:
220:
213:
206:
203:
192:
185:
143:
140:
106:
103:
99:MIS Department
82:
79:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
1289:
1278:
1275:
1273:
1270:
1268:
1265:
1264:
1262:
1246:
1240:
1236:
1232:
1228:
1224:
1219:
1218:
1214:
1199:on 2016-03-04
1198:
1194:
1190:
1184:
1181:
1170:on 2018-10-27
1166:
1162:
1158:
1154:
1147:
1141:
1138:
1127:
1123:
1119:
1112:
1106:
1103:
1091:
1087:
1081:
1078:
1072:
1069:
1058:
1054:
1048:
1045:
1033:
1026:
1019:
1016:
1011:
1007:
1003:
999:
992:
989:
984:
983:
975:
972:
967:
965:9781118360491
961:
957:
953:
949:
942:
939:
928:
924:
918:
916:
912:
907:
903:
899:
895:
888:
885:
880:
876:
872:
868:
861:
858:
847:
843:
837:
834:
829:
825:
821:
817:
813:
809:
802:
799:
794:
788:
784:
777:
774:
770:
765:
761:
757:
755:9780321711502
751:
747:
743:
739:
734:
733:
724:
721:
717:
715:
711:
705:
701:
697:
691:
687:
683:
679:
678:San Francisco
674:
673:
664:
661:
656:
652:
648:
642:
638:
634:
627:
624:
620:
616:
612:
608:
604:
600:
596:
590:
587:
583:
573:
569:
565:
561:
554:
551:
547:
537:
533:
529:
522:
520:
516:
512:
508:
504:
500:
494:
490:
486:
482:
478:
472:
469:
462:
454:
450:
446:
443:is generally
442:
436:
433:
426:
422:
419:
417:
414:
412:
409:
407:
404:
403:
399:
397:
394:
392:
388:
384:
379:
377:
369:
367:
364:
355:
352:
348:
345:
341:
338:
335:
331:
329:
325:
322:
321:
320:
317:
313:
311:
307:
303:
299:
295:
291:
287:
286:user friendly
282:
280:
276:
272:
268:
265:
261:
257:
252:
248:
242:
234:
232:
225:
221:
218:
214:
211:
207:
204:
201:
197:
193:
190:
186:
183:
182:
181:
178:
176:
172:
171:documentation
163:
155:
149:
141:
139:
137:
133:
129:
125:
119:
117:
113:
104:
102:
100:
96:
92:
88:
80:
78:
76:
72:
68:
64:
60:
56:
52:
48:
39:
33:
19:
1248:, retrieved
1226:
1201:. Retrieved
1197:the original
1192:
1183:
1172:. Retrieved
1165:the original
1152:
1140:
1129:. Retrieved
1117:
1105:
1094:. Retrieved
1089:
1080:
1071:
1060:. Retrieved
1056:
1047:
1036:. Retrieved
1031:
1018:
1001:
997:
991:
981:
974:
947:
941:
930:. Retrieved
926:
897:
893:
887:
870:
866:
860:
849:. Retrieved
845:
836:
811:
807:
801:
782:
776:
767:
731:
723:
713:
709:
707:
671:
663:
632:
626:
618:
598:
589:
581:
575:. Retrieved
563:
553:
545:
539:. Retrieved
531:
510:
476:
471:
448:
440:
435:
395:
380:
373:
359:
328:HTTP cookies
318:
314:
283:
260:blackmailing
244:
229:
217:troubleshoot
179:
168:
120:
108:
84:
74:
50:
46:
44:
684:. pp.
271:back office
251:smartphones
189:screenshots
105:Empowerment
49:(sometimes
1261:Categories
1250:2023-12-23
1203:2015-11-04
1193:Findlaw UK
1174:2015-06-28
1131:2015-06-28
1096:2015-06-28
1062:2015-11-04
1057:www.gov.uk
1038:2015-11-04
932:2015-11-03
851:2015-11-03
769:payments).
744:. p.
577:2015-06-28
541:2015-06-28
532:foldoc.org
463:References
445:hyphenated
421:User guide
294:encryption
239:See also:
128:e-journals
879:199819277
764:884168009
710:end users
351:passwords
342:Unsecure
290:firewalls
91:mainframe
67:customers
1277:Consumer
875:ProQuest
828:23714792
704:30777731
655:20491157
507:50480181
481:Barron's
449:end user
441:end-user
400:See also
332:Opening
306:phishing
267:startups
235:Security
200:acronyms
136:database
75:customer
51:end-user
47:end user
615:6862471
279:payroll
247:laptops
222:Unique
132:Web 2.0
124:e-books
81:Context
18:Enduser
1241:
962:
877:
846:Forbes
826:
789:
762:
752:
702:
692:
653:
643:
613:
536:London
505:
495:
258:, by,
196:jargon
71:retail
55:sysops
1168:(PDF)
1149:(PDF)
1114:(PDF)
1028:(PDF)
824:JSTOR
714:query
427:Notes
349:Weak
344:Wi-Fi
1239:ISBN
960:ISBN
787:ISBN
760:OCLC
750:ISBN
700:OCLC
690:ISBN
651:OCLC
641:ISBN
611:OCLC
595:FIPS
503:OCLC
493:ISBN
385:and
334:junk
249:and
134:and
1231:doi
1006:doi
952:doi
902:doi
816:doi
746:581
686:4–5
451:is
374:In
370:Law
210:LED
198:or
1263::
1237:,
1225:,
1191:.
1159::
1155:.
1151:.
1124::
1120:.
1116:.
1088:.
1055:.
1030:.
1002:24
1000:.
958:.
925:.
914:^
898:38
896:.
871:46
869:.
844:.
822:.
812:28
810:.
766:.
758:.
748:.
740::
736:.
706:.
698:.
688:.
680::
676:.
649:.
635:.
617:.
605::
601:.
580:.
570::
566:.
562:.
544:.
534:.
530:.
518:^
509:.
501:.
487::
479:.
393:.
296:,
292:,
277:,
126:,
57:,
1233::
1206:.
1177:.
1134:.
1099:.
1065:.
1041:.
1012:.
1008::
968:.
954::
935:.
908:.
904::
881:.
854:.
830:.
818::
795:.
657:.
150:.
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.