2339:-ary bent functions, bent functions over a finite field, generalized Boolean bent functions of Schmidt, bent functions from a finite Abelian group into the set of complex numbers on the unit circle, bent functions from a finite Abelian group into a finite Abelian group, non-Abelian bent functions, vectorial G-bent functions, multidimensional bent functions on a finite Abelian group), combinatorial generalizations (symmetric bent functions, homogeneous bent functions, rotation symmetric bent functions, normal bent functions, self-dual and anti-self-dual bent functions, partially defined bent functions, plateaued functions, Z-bent functions and quantum bent functions) and cryptographic generalizations (semi-bent functions, balanced bent functions, partially bent functions, hyper-bent functions, bent functions of higher order,
2278:. Instead, one might start with a bent function and randomly complement appropriate values until the result is balanced. The modified function still has high nonlinearity, and as such functions are very rare the process should be much faster than a brute-force search. But functions produced in this way may lose other desirable properties, even failing to satisfy the SAC – so careful testing is necessary. A number of cryptographers have worked on techniques for generating balanced functions that preserve as many of the good cryptographic qualities of bent functions as possible.
20:
116:
2270:, bent functions might at first seem the ideal choice for secure cryptographic functions such as S-boxes. Their fatal flaw is that they fail to be balanced. In particular, an invertible S-box cannot be constructed directly from bent functions, and a
967:
2539:
614:
1225:
2090:
Although bent functions are vanishingly rare among
Boolean functions of many variables, they come in many different kinds. There has been detailed research into special classes of bent functions, such as the
493:
2853:
1714:
2715:
2601:
2410:
1381:
436:
1584:
1065:
2115:
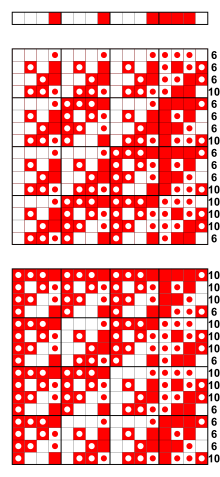
Combinatorial constructions: iterative constructions, Maiorana–McFarland construction, partial spreads, Dillon's and
Dobbertin's bent functions, minterm bent functions, bent iterative functions
1809:
260:
108:
2005:
1914:
2769:
form a large class defined by a condition on the Walsh transform and autocorrelation functions. All affine and bent functions are partially bent. This is in turn a proper subclass of the
177:
2756:
363:) boolean functions. Certain functions that are as close as possible to perfect nonlinearity (e.g. for functions of an odd number of bits, or vectorial functions) are known as
2174:. Indeed, the functions satisfying the SAC to the highest possible order are always bent. Furthermore, the bent functions are as far as possible from having what are called
819:
1284:
2418:
2162:, which seeks to obscure relationships between input and output. By 1988 Forré recognized that the Walsh transform of a function can be used to show that it satisfies the
501:
345:. The definition can be extended in several ways, leading to different classes of generalized bent functions that share many of the useful properties of the original.
2863:. While not bent functions themselves (these are not even Boolean functions), they are closely related to the bent functions and have good nonlinearity properties.
2118:
Algebraic constructions: monomial bent functions with exponents of Gold, Dillon, Kasami, Canteaut–Leander and
Canteaut–Charpin–Kuyreghyan; Niho bent functions, etc.
318:. In addition, detecting a change in the output of the function yields no information about what change occurred in the inputs, making the function immune to
3147:
2788:
monomials on the finite field GF(2), not just the affine functions. For these functions this distance is constant, which may make them resistant to an
3204:
3209:
314:
The maximal nonlinearity means approximating a bent function by an affine (linear) function is hard, a useful property in the defence against
3696:
3456:
Proceedings 2006 IEEE International
Symposium on Information Theory, ISIT 2006, The Westin Seattle, Seattle, Washington, USA, July 9–14, 2006
1391:. Bent functions are in a sense equidistant from all the affine functions, so they are equally hard to approximate with any affine function.
2331:
More than 25 different generalizations of bent functions are described in
Tokareva's 2015 monograph. There are algebraic generalizations (
3744:
1119:
441:
3715:
2946:
2798:
3286:
2266:
Given such good diffusion properties, apparently perfect resistance to differential cryptanalysis, and resistance by definition to
1626:
2762:. They also have good cryptographic characteristics, and some of them are balanced, taking on all possible values equally often.
2665:
2551:
2360:
1331:
386:
3749:
1540:
311:
Boolean functions, so for any change in the input variables there is a 50 percent chance that the output value will change.
1620:; bent functions and bent sequences have equivalent properties. In this ±1 form, the Walsh transform is easily computed as
1000:
1745:
188:
36:
2305:
1923:
1832:
2202:
2163:
319:
2254:
308:
122:
3734:
19:
2724:
3178:
2171:
2128:
300:
3739:
3648:
3551:
3337:
3290:
2092:
2047:
3608:. Second International Conference on Information and Communication Security (ICICS '99). pp. 284–300
3230:
2016:
1613:
1395:
3492:
Shashi Kant Pandey; B.K. Dass (September 2017). "On Walsh
Spectrum of Cryptographic Boolean Function".
2656:, even and odd. They have many of the same good cryptographic properties as the binary bent functions.
962:{\displaystyle {\hat {f}}(a)=\left|S_{0}(a)\right|-\left|S_{1}(a)\right|=2\left|S_{0}(a)\right|-2^{n}.}
3361:
2103:, but so far the bent functions have defied all attempts at a complete enumeration or classification.
2872:
2789:
2534:{\displaystyle {\hat {f}}(a)=\sum _{x\in \mathbb {Z} _{m}^{n}}e^{{\frac {2\pi i}{m}}(f(x)-a\cdot x)}}
2323:
whose nonlinear feedback polynomial is, by design, the sum of a bent function and a linear function.
2267:
342:
315:
3639:
J. Seberry; X. Zhang (March 1994). "Constructions of Bent
Functions from Two Known Bent Functions".
115:
29:(these Hadamard matrices show the Hamming distance to each of the eight linear and affine functions)
3556:
3448:
3342:
3295:
3254:
The Strict
Avalanche Criterion: Spectral Properties of Boolean Functions and an Extended Definition
1251:
609:{\displaystyle {\hat {f}}(a)=\sum _{\scriptstyle {x\in \mathbb {Z} _{2}^{n}}}(-1)^{f(x)+a\cdot x},}
329:
in research not published until 1976. They have been extensively studied for their applications in
326:
3653:
3532:
3577:
3389:
2351:
2275:
304:
3688:
3678:
2281:
Some of this theoretical research has been incorporated into real cryptographic algorithms. The
2166:(SAC) and higher-order generalizations, and recommended this tool to select candidates for good
348:
It is known that V. A. Eliseev and O. P. Stepchenkov studied bent functions, which they called
3711:
3692:
3658:
3569:
3509:
3381:
3222:
3170:
3118:
3072:. Fourth International Workshop on Boolean Functions: Cryptography and Applications (BFCA '08)
2985:
2942:
2914:
2312:
2132:
3670:
3561:
3501:
3459:
3373:
3283:
The Use of Bent
Sequences to Achieve Higher-Order Strict Avalanche Criterion in S-box Design
3278:
3214:
3162:
3108:
3009:
2975:
2904:
2290:
2030:, and in fact agrees with any affine function at one of those two numbers of points. So the
292:
280:
2152:
2136:
1384:
380:
334:
288:
183:. The following formula shows that a 4-ary function is bent when its nonlinearity is 6:
2259:
Boolean function, taking on each value exactly half of the time. This property is called
31:. The following formula shows that a 2-ary function is bent when its nonlinearity is 1:
2795:
Other related names have been given to cryptographically important classes of functions
3274:
3092:
2316:
2286:
2023:
1388:
24:
303:
between the output of the function and a linear function is minimal. In addition, the
3728:
3419:
3330:
Highly
Nonlinear 0–1 Balanced Boolean Functions Satisfying Strict Avalanche Criterion
3143:
2909:
2892:
2294:
2271:
1728:
338:
272:
3581:
3393:
3528:
3310:
2641:
2159:
2100:
1724:
330:
3097:"Homogeneous bent functions of degree n in 2n variables do not exist for n > 3"
283:
that is maximally non-linear; it is as different as possible from the set of all
3674:
2144:
674:
352:, in the USSR in 1962. However, their results have still not been declassified.
296:
268:
3603:
3565:
3537:
3377:
3166:
3113:
3013:
2980:
2963:
284:
3662:
3573:
3513:
3463:
3385:
3226:
3218:
3174:
3122:
2989:
2918:
2158:
The properties of bent functions are naturally of interest in modern digital
3684:
3064:
3046:
2785:
2140:
2042:, the maximum possible. Conversely, any Boolean function with nonlinearity
3505:
3447:
Hell, Martin; Johansson, Thomas; Maximov, Alexander; Meier, Willi (2006).
3533:"A new characterization of semi-bent and bent functions on finite fields"
3423:
3333:
2301:
2297:
2096:
2662:
are an odd-order counterpart to bent functions. A semi-bent function is
3096:
3257:
2311:
uses Boolean functions built from representatives of all four of the
3425:
HAVAL – a one-way hashing algorithm with variable length of output
2320:
2308:
2167:
1220:{\displaystyle {\hat {f}}_{0}(a)=2^{n},~{\hat {f}}_{1}(a)=-2^{n}.}
114:
18:
3362:"Constructing Symmetric Ciphers Using the CAST Design Procedure"
2148:
3063:
C. Carlet; L.E. Danielsen; M.G. Parker; P. Solé (19 May 2008).
488:{\displaystyle {\hat {f}}:\mathbb {Z} _{2}^{n}\to \mathbb {Z} }
2848:{\displaystyle f:\mathbb {Z} _{2}^{n}\to \mathbb {Z} _{2}^{n}}
2111:
There are several types of constructions for bent functions.
1709:{\displaystyle {\hat {f}}(a)=W\left(2^{n}\right)(-1)^{f(a)},}
3397:
2038:(minimum number of times it equals any affine function) is
2710:{\displaystyle f:\mathbb {Z} _{m}^{n}\to \mathbb {Z} _{m}}
2652:, there are generalized bent functions for every positive
2596:{\displaystyle f:\mathbb {Z} _{m}^{n}\to \mathbb {Z} _{m}}
2405:{\displaystyle f:\mathbb {Z} _{m}^{n}\to \mathbb {Z} _{m}}
1376:{\displaystyle f:\mathbb {Z} _{2}^{n}\to \mathbb {Z} _{2}}
431:{\displaystyle f:\mathbb {Z} _{2}^{n}\to \mathbb {Z} _{2}}
1590:, but there is a wide variety of other bent functions as
2939:
Bent functions: results and applications to cryptography
1579:{\displaystyle \mathbb {Z} _{2}^{n}\to \mathbb {Z} _{2}}
1734:
Rothaus proved that bent functions exist only for even
2315:
of bent functions on six variables. The stream cipher
534:
325:
Bent functions were defined and named in the 1960s by
2801:
2727:
2668:
2554:
2421:
2363:
1926:
1835:
1748:
1629:
1543:
1334:
1254:
1122:
1003:
822:
504:
444:
389:
191:
125:
39:
2205:(introduced after this property was discovered) the
1394:
The simplest examples of bent functions, written in
3479:
Constructions of bent functions and difference sets
2274:using a bent combining function is vulnerable to a
1060:{\displaystyle -2^{n}\leq {\hat {f}}(a)\leq 2^{n}.}
2847:
2750:
2709:
2595:
2533:
2404:
1999:
1908:
1804:{\displaystyle \left|{\hat {f}}(a)\right|=2^{n/2}}
1803:
1708:
1578:
1375:
1278:
1219:
1059:
961:
608:
487:
430:
255:{\displaystyle 2^{4-1}-2^{{\frac {4}{2}}-1}=8-2=6}
254:
171:
103:{\displaystyle 2^{2-1}-2^{{\frac {2}{2}}-1}=2-1=1}
102:
3043:Nonlinearity Criteria for Cryptographic Functions
2644:, the converse is true. In most cases only prime
3708:Cryptographic Boolean Functions and Applications
3203:J. Olsen; R. Scholtz; L. Welch (November 1982).
2000:{\displaystyle {\hat {g}}(a)=2^{n/2}(-1)^{f(a)}}
1909:{\displaystyle {\hat {f}}(a)=2^{n/2}(-1)^{g(a)}}
2151:. These sequences have several applications in
2964:"Perfect nonlinear functions and cryptography"
1594:increases. The sequence of values (−1), with
8:
3146:; P. Charpin; G. Kyureghyan (January 2008).
383:. The Walsh transform of a Boolean function
181:(which is what these Hadamard Matrices show)
3422:; J. Pieprzyk; J. Seberry (December 1992).
2932:
2930:
2928:
1113:correspond to the two extreme cases, since
379:Bent functions are defined in terms of the
172:{\displaystyle x_{1}x_{2}\oplus x_{3}x_{4}}
2026:(number of times it takes the value 1) of
27:1 are bent; i.e., their nonlinearity is 1
3652:
3555:
3341:
3294:
3112:
2979:
2908:
2897:Journal of Combinatorial Theory, Series A
2839:
2834:
2830:
2829:
2819:
2814:
2810:
2809:
2800:
2733:
2732:
2726:
2701:
2697:
2696:
2686:
2681:
2677:
2676:
2667:
2587:
2583:
2582:
2572:
2567:
2563:
2562:
2553:
2481:
2480:
2468:
2463:
2459:
2458:
2450:
2423:
2422:
2420:
2396:
2392:
2391:
2381:
2376:
2372:
2371:
2362:
1982:
1959:
1955:
1928:
1927:
1925:
1891:
1868:
1864:
1837:
1836:
1834:
1791:
1787:
1755:
1754:
1747:
1688:
1665:
1631:
1630:
1628:
1570:
1566:
1565:
1555:
1550:
1546:
1545:
1542:
1367:
1363:
1362:
1352:
1347:
1343:
1342:
1333:
1256:
1255:
1253:
1208:
1183:
1172:
1171:
1158:
1136:
1125:
1124:
1121:
1048:
1021:
1020:
1011:
1002:
950:
923:
888:
856:
824:
823:
821:
576:
553:
548:
544:
543:
535:
533:
506:
505:
503:
481:
480:
471:
466:
462:
461:
446:
445:
443:
422:
418:
417:
407:
402:
398:
397:
388:
216:
215:
196:
190:
163:
153:
140:
130:
124:
64:
63:
44:
38:
3148:"A new class of monomial bent functions"
3036:
3034:
3032:
3030:
2127:As early as 1982 it was discovered that
3355:
3353:
3210:IEEE Transactions on Information Theory
3041:W. Meier; O. Staffelbach (April 1989).
2883:
2780:is to maximize the minimum distance to
2751:{\displaystyle \left|{\hat {f}}\right|}
3328:J. Seberry; X. Zhang (December 1992).
3269:
3267:
3058:
3056:
3003:
3001:
2999:
23:The four 2-ary Boolean functions with
3641:Australasian Journal of Combinatorics
3449:"A Stream Cipher Proposal: Grain-128"
2054:in algebraic normal form (called the
299:. Concretely, this means the maximum
179:is bent; i.e., its nonlinearity is 6
7:
3602:Y. Zheng; X. Zhang (November 1999).
3155:Finite Fields and Their Applications
2968:Finite Fields and Their Applications
184:
32:
3014:"Boolean Functions in Cryptography"
2304:, makes use of bent functions. The
3706:Cusick, T.W.; Stanica, P. (2009).
3481:. Eurocrypt '90. pp. 151–160.
3317:. Eurocrypt '91. pp. 378–386.
2603:, those such that for all nonzero
2201:is a constant. In the language of
2139:properties rivalling those of the
994:, the transform lies in the range
14:
3680:Handbook of Combinatorial Designs
3634:. Eurocrypt '93. pp. 77–101.
3632:Two New Classes of Bent Functions
2293:to construct the S-boxes for the
1727:and the sequence is treated as a
1286:characterizes where the function
355:Bent functions are also known as
2636:times, are generalized bent. If
333:, but have also been applied to
16:Special type of Boolean function
3544:Designs, Codes and Cryptography
3428:. AUSCRYPT '92. pp. 83–104
3366:Designs, Codes and Cryptography
2962:Blondeau; Nyberg (2015-03-01).
1738:, and that for a bent function
3285:. Technical Report TR 90-013.
2825:
2784:Boolean functions coming from
2738:
2692:
2648:are considered. For odd prime
2578:
2548:. Perfect nonlinear functions
2526:
2511:
2505:
2499:
2440:
2434:
2428:
2387:
2178:, nonzero vectors a such that
1992:
1986:
1979:
1969:
1945:
1939:
1933:
1901:
1895:
1888:
1878:
1854:
1848:
1842:
1772:
1766:
1760:
1698:
1692:
1685:
1675:
1648:
1642:
1636:
1561:
1358:
1273:
1267:
1261:
1195:
1189:
1177:
1148:
1142:
1130:
1070:Moreover, the linear function
1038:
1032:
1026:
935:
929:
900:
894:
868:
862:
841:
835:
829:
586:
580:
573:
563:
523:
517:
511:
477:
451:
413:
1:
3012:; T. Xia (29 December 2001).
2131:based on bent functions have
2095:ones or those arising from a
1279:{\displaystyle {\hat {f}}(a)}
3458:. IEEE. pp. 1614–1618.
3101:Discrete Applied Mathematics
2910:10.1016/0097-3165(76)90024-8
2758:takes only the values 0 and
2544:has constant absolute value
1920:is also bent. In this case,
2306:cryptographic hash function
1723:(2) is the natural-ordered
3766:
3745:Symmetric-key cryptography
3360:C. Adams (November 1997).
3095:; C. Charnes (June 2004).
2891:O. S. Rothaus (May 1976).
2348:generalized bent functions
2285:design procedure, used by
2203:differential cryptanalysis
2164:strict avalanche criterion
2022:Every bent function has a
1491:. This pattern continues:
365:almost perfectly nonlinear
320:differential cryptanalysis
3566:10.1007/s10623-005-6345-x
3315:Perfect nonlinear S-boxes
3205:"Bent-Function Sequences"
3167:10.1016/j.ffa.2007.02.004
3114:10.1016/j.dam.2004.02.006
2981:10.1016/j.ffa.2014.10.007
2346:The most common class of
1320:Definition and properties
1294:) lies in the range from
972:For any Boolean function
3464:10.1109/ISIT.2006.261549
3252:R. Forré (August 1988).
3219:10.1109/tit.1982.1056589
3066:Self Dual Bent Functions
2767:partially bent functions
2335:-valued bent functions,
2129:maximum length sequences
1091:and the affine function
3494:Defence Science Journal
3378:10.1023/A:1008229029587
3336:'92. pp. 143–155.
2213:at every nonzero point
2170:achieving near-perfect
307:of a bent function are
3750:Theory of cryptography
3630:C. Carlet (May 1993).
3477:K. Nyberg (May 1990).
3260:'88. pp. 450–468.
3213:. IT-28 (6): 858–864.
3049:'89. pp. 549–562.
2849:
2752:
2711:
2597:
2535:
2406:
2001:
1910:
1805:
1710:
1580:
1377:
1328:as a Boolean function
1280:
1221:
1061:
963:
610:
489:
432:
264:
256:
173:
112:
104:
3506:10.14429/dsj.67.10638
2893:"On "Bent" Functions"
2857:almost bent functions
2850:
2753:
2712:
2598:
2536:
2407:
2002:
1911:
1806:
1711:
1614:lexicographical order
1581:
1396:algebraic normal form
1378:
1281:
1222:
1062:
964:
689:. Alternatively, let
611:
490:
433:
257:
174:
119:The Boolean function
118:
105:
22:
3671:Colbourn, Charles J.
3091:T. Xia; J. Seberry;
2937:N. Tokareva (2015).
2873:Correlation immunity
2799:
2790:interpolation attack
2778:hyper-bent functions
2776:The idea behind the
2725:
2666:
2630:takes on each value
2552:
2419:
2361:
2268:linear cryptanalysis
2261:perfect nonlinearity
1924:
1833:
1746:
1627:
1541:
1332:
1252:
1120:
1001:
820:
502:
442:
387:
343:combinatorial design
316:linear cryptanalysis
189:
123:
37:
3605:Plateaued Functions
2844:
2824:
2771:plateaued functions
2691:
2660:Semi-bent functions
2577:
2473:
2386:
2313:equivalence classes
2209:of a bent function
1560:
1537:is a bent function
1357:
558:
476:
412:
357:perfectly nonlinear
3710:. Academic Press.
3675:Dinitz, Jeffrey H.
3527:K. Khoo; G. Gong;
3400:on 26 October 2008
3287:Queen's University
2941:. Academic Press.
2845:
2828:
2808:
2748:
2707:
2675:
2593:
2561:
2531:
2475:
2457:
2402:
2370:
2343:-bent functions).
2276:correlation attack
1997:
1906:
1801:
1706:
1576:
1544:
1373:
1341:
1324:Rothaus defined a
1276:
1217:
1057:
959:
606:
562:
560:
542:
485:
460:
428:
396:
265:
252:
169:
113:
100:
3698:978-1-58488-506-1
3531:(February 2006).
2861:crooked functions
2741:
2497:
2446:
2431:
2176:linear structures
2133:cross-correlation
1936:
1845:
1763:
1639:
1264:
1180:
1169:
1133:
1029:
832:
529:
514:
454:
350:minimal functions
291:when measured by
224:
182:
72:
30:
3757:
3721:
3702:
3683:(2nd ed.).
3666:
3656:
3635:
3618:
3617:
3615:
3613:
3599:
3593:
3592:
3590:
3588:
3559:
3541:
3524:
3518:
3517:
3489:
3483:
3482:
3474:
3468:
3467:
3453:
3444:
3438:
3437:
3435:
3433:
3416:
3410:
3409:
3407:
3405:
3396:. Archived from
3357:
3348:
3347:
3345:
3325:
3319:
3318:
3307:
3301:
3300:
3298:
3281:(January 1990).
3271:
3262:
3261:
3249:
3243:
3242:
3240:
3238:
3229:. Archived from
3200:
3194:
3193:
3191:
3189:
3183:
3177:. Archived from
3152:
3140:
3134:
3133:
3131:
3129:
3116:
3107:(1–3): 127–132.
3088:
3082:
3081:
3079:
3077:
3071:
3060:
3051:
3050:
3038:
3025:
3024:
3022:
3020:
3005:
2994:
2993:
2983:
2959:
2953:
2952:
2934:
2923:
2922:
2912:
2888:
2854:
2852:
2851:
2846:
2843:
2838:
2833:
2823:
2818:
2813:
2757:
2755:
2754:
2749:
2747:
2743:
2742:
2734:
2716:
2714:
2713:
2708:
2706:
2705:
2700:
2690:
2685:
2680:
2635:
2629:
2602:
2600:
2599:
2594:
2592:
2591:
2586:
2576:
2571:
2566:
2540:
2538:
2537:
2532:
2530:
2529:
2498:
2493:
2482:
2474:
2472:
2467:
2462:
2433:
2432:
2424:
2411:
2409:
2408:
2403:
2401:
2400:
2395:
2385:
2380:
2375:
2291:Stafford Tavares
2252:
2200:
2086:
2079:
2077:
2076:
2073:
2070:
2045:
2041:
2029:
2006:
2004:
2003:
1998:
1996:
1995:
1968:
1967:
1963:
1938:
1937:
1929:
1915:
1913:
1912:
1907:
1905:
1904:
1877:
1876:
1872:
1847:
1846:
1838:
1828:
1827:
1826:
1810:
1808:
1807:
1802:
1800:
1799:
1795:
1779:
1775:
1765:
1764:
1756:
1715:
1713:
1712:
1707:
1702:
1701:
1674:
1670:
1669:
1641:
1640:
1632:
1611:
1610:
1609:
1585:
1583:
1582:
1577:
1575:
1574:
1569:
1559:
1554:
1549:
1536:
1490:
1430:
1382:
1380:
1379:
1374:
1372:
1371:
1366:
1356:
1351:
1346:
1285:
1283:
1282:
1277:
1266:
1265:
1257:
1247:
1246:
1245:
1226:
1224:
1223:
1218:
1213:
1212:
1188:
1187:
1182:
1181:
1173:
1167:
1163:
1162:
1141:
1140:
1135:
1134:
1126:
1112:
1090:
1066:
1064:
1063:
1058:
1053:
1052:
1031:
1030:
1022:
1016:
1015:
993:
992:
991:
968:
966:
965:
960:
955:
954:
942:
938:
928:
927:
907:
903:
893:
892:
875:
871:
861:
860:
834:
833:
825:
812:
810:
796:
780:
762:
761:
734:
716:
715:
688:
687:
672:
615:
613:
612:
607:
602:
601:
561:
559:
557:
552:
547:
516:
515:
507:
494:
492:
491:
486:
484:
475:
470:
465:
456:
455:
447:
438:is the function
437:
435:
434:
429:
427:
426:
421:
411:
406:
401:
293:Hamming distance
289:affine functions
281:Boolean function
261:
259:
258:
253:
233:
232:
225:
217:
207:
206:
180:
178:
176:
175:
170:
168:
167:
158:
157:
145:
144:
135:
134:
109:
107:
106:
101:
81:
80:
73:
65:
55:
54:
28:
3765:
3764:
3760:
3759:
3758:
3756:
3755:
3754:
3735:Boolean algebra
3725:
3724:
3718:
3705:
3699:
3669:
3638:
3629:
3626:
3624:Further reading
3621:
3611:
3609:
3601:
3600:
3596:
3586:
3584:
3535:
3526:
3525:
3521:
3491:
3490:
3486:
3476:
3475:
3471:
3451:
3446:
3445:
3441:
3431:
3429:
3418:
3417:
3413:
3403:
3401:
3359:
3358:
3351:
3327:
3326:
3322:
3309:
3308:
3304:
3273:
3272:
3265:
3251:
3250:
3246:
3236:
3234:
3233:on 22 July 2011
3202:
3201:
3197:
3187:
3185:
3184:on 21 July 2011
3181:
3150:
3142:
3141:
3137:
3127:
3125:
3090:
3089:
3085:
3075:
3073:
3069:
3062:
3061:
3054:
3040:
3039:
3028:
3018:
3016:
3007:
3006:
2997:
2961:
2960:
2956:
2949:
2936:
2935:
2926:
2890:
2889:
2885:
2881:
2869:
2797:
2796:
2728:
2723:
2722:
2721:odd, such that
2695:
2664:
2663:
2631:
2608:
2581:
2550:
2549:
2483:
2476:
2417:
2416:
2390:
2359:
2358:
2329:
2327:Generalizations
2226:
2218:
2179:
2153:spread spectrum
2137:autocorrelation
2125:
2109:
2081:
2074:
2071:
2066:
2065:
2063:
2056:nonlinear order
2043:
2039:
2027:
2015:are considered
1978:
1951:
1922:
1921:
1887:
1860:
1831:
1830:
1825:
1822:
1821:
1820:
1812:
1783:
1753:
1749:
1744:
1743:
1684:
1661:
1657:
1625:
1624:
1608:
1605:
1604:
1603:
1595:
1586:for every even
1564:
1539:
1538:
1535:
1527:
1517:
1511:
1504:
1498:
1492:
1489:
1483:
1476:
1470:
1463:
1456:
1449:
1442:
1432:
1429:
1423:
1416:
1409:
1399:
1385:Walsh transform
1361:
1330:
1329:
1322:
1311:
1300:
1250:
1249:
1244:
1241:
1240:
1239:
1231:
1230:Thus, for each
1204:
1170:
1154:
1123:
1118:
1117:
1098:
1092:
1077:
1071:
1044:
1007:
999:
998:
990:
987:
986:
985:
977:
946:
919:
918:
914:
884:
883:
879:
852:
851:
847:
818:
817:
804:
798:
797:| + |
790:
784:
782:
760:
757:
756:
755:
742:
736:
714:
711:
710:
709:
696:
690:
686:
683:
682:
681:
670:
662:
653:
647:
640:
634:
620:
572:
500:
499:
440:
439:
416:
385:
384:
381:Walsh transform
377:
375:Walsh transform
335:spread spectrum
211:
192:
187:
186:
159:
149:
136:
126:
121:
120:
59:
40:
35:
34:
17:
12:
11:
5:
3763:
3761:
3753:
3752:
3747:
3742:
3737:
3727:
3726:
3723:
3722:
3716:
3703:
3697:
3667:
3636:
3625:
3622:
3620:
3619:
3594:
3557:10.1.1.10.6303
3550:(2): 279–295.
3519:
3500:(5): 536–541.
3484:
3469:
3439:
3411:
3372:(3): 283–316.
3349:
3343:10.1.1.57.4992
3320:
3313:(April 1991).
3302:
3296:10.1.1.41.8374
3263:
3244:
3195:
3161:(1): 221–241.
3135:
3083:
3052:
3026:
2995:
2954:
2947:
2924:
2903:(3): 300–305.
2882:
2880:
2877:
2876:
2875:
2868:
2865:
2842:
2837:
2832:
2827:
2822:
2817:
2812:
2807:
2804:
2746:
2740:
2737:
2731:
2704:
2699:
2694:
2689:
2684:
2679:
2674:
2671:
2590:
2585:
2580:
2575:
2570:
2565:
2560:
2557:
2542:
2541:
2528:
2525:
2522:
2519:
2516:
2513:
2510:
2507:
2504:
2501:
2496:
2492:
2489:
2486:
2479:
2471:
2466:
2461:
2456:
2453:
2449:
2445:
2442:
2439:
2436:
2430:
2427:
2399:
2394:
2389:
2384:
2379:
2374:
2369:
2366:
2328:
2325:
2287:Carlisle Adams
2222:
2124:
2121:
2120:
2119:
2116:
2108:
2105:
2024:Hamming weight
1994:
1991:
1988:
1985:
1981:
1977:
1974:
1971:
1966:
1962:
1958:
1954:
1950:
1947:
1944:
1941:
1935:
1932:
1903:
1900:
1897:
1894:
1890:
1886:
1883:
1880:
1875:
1871:
1867:
1863:
1859:
1856:
1853:
1850:
1844:
1841:
1823:
1798:
1794:
1790:
1786:
1782:
1778:
1774:
1771:
1768:
1762:
1759:
1752:
1717:
1716:
1705:
1700:
1697:
1694:
1691:
1687:
1683:
1680:
1677:
1673:
1668:
1664:
1660:
1656:
1653:
1650:
1647:
1644:
1638:
1635:
1616:, is called a
1606:
1573:
1568:
1563:
1558:
1553:
1548:
1531:
1522:
1515:
1509:
1502:
1496:
1487:
1481:
1474:
1468:
1461:
1454:
1447:
1440:
1427:
1421:
1414:
1407:
1389:absolute value
1370:
1365:
1360:
1355:
1350:
1345:
1340:
1337:
1321:
1318:
1309:
1298:
1275:
1272:
1269:
1263:
1260:
1242:
1228:
1227:
1216:
1211:
1207:
1203:
1200:
1197:
1194:
1191:
1186:
1179:
1176:
1166:
1161:
1157:
1153:
1150:
1147:
1144:
1139:
1132:
1129:
1096:
1075:
1068:
1067:
1056:
1051:
1047:
1043:
1040:
1037:
1034:
1028:
1025:
1019:
1014:
1010:
1006:
988:
970:
969:
958:
953:
949:
945:
941:
937:
934:
931:
926:
922:
917:
913:
910:
906:
902:
899:
896:
891:
887:
882:
878:
874:
870:
867:
864:
859:
855:
850:
846:
843:
840:
837:
831:
828:
802:
788:
758:
740:
712:
694:
684:
666:
658:
651:
645:
638:
632:
617:
616:
605:
600:
597:
594:
591:
588:
585:
582:
579:
575:
571:
568:
565:
556:
551:
546:
541:
538:
532:
528:
525:
522:
519:
513:
510:
483:
479:
474:
469:
464:
459:
453:
450:
425:
420:
415:
410:
405:
400:
395:
392:
376:
373:
263:
262:
251:
248:
245:
242:
239:
236:
231:
228:
223:
220:
214:
210:
205:
202:
199:
195:
166:
162:
156:
152:
148:
143:
139:
133:
129:
111:
110:
99:
96:
93:
90:
87:
84:
79:
76:
71:
68:
62:
58:
53:
50:
47:
43:
25:Hamming weight
15:
13:
10:
9:
6:
4:
3:
2:
3762:
3751:
3748:
3746:
3743:
3741:
3740:Combinatorics
3738:
3736:
3733:
3732:
3730:
3719:
3717:9780123748904
3713:
3709:
3704:
3700:
3694:
3690:
3686:
3682:
3681:
3676:
3672:
3668:
3664:
3660:
3655:
3654:10.1.1.55.531
3650:
3646:
3642:
3637:
3633:
3628:
3627:
3623:
3607:
3606:
3598:
3595:
3583:
3579:
3575:
3571:
3567:
3563:
3558:
3553:
3549:
3545:
3539:
3534:
3530:
3523:
3520:
3515:
3511:
3507:
3503:
3499:
3495:
3488:
3485:
3480:
3473:
3470:
3465:
3461:
3457:
3450:
3443:
3440:
3427:
3426:
3421:
3415:
3412:
3399:
3395:
3391:
3387:
3383:
3379:
3375:
3371:
3367:
3363:
3356:
3354:
3350:
3344:
3339:
3335:
3331:
3324:
3321:
3316:
3312:
3306:
3303:
3297:
3292:
3288:
3284:
3280:
3276:
3270:
3268:
3264:
3259:
3255:
3248:
3245:
3232:
3228:
3224:
3220:
3216:
3212:
3211:
3206:
3199:
3196:
3180:
3176:
3172:
3168:
3164:
3160:
3156:
3149:
3145:
3139:
3136:
3124:
3120:
3115:
3110:
3106:
3102:
3098:
3094:
3087:
3084:
3068:
3067:
3059:
3057:
3053:
3048:
3044:
3037:
3035:
3033:
3031:
3027:
3015:
3011:
3004:
3002:
3000:
2996:
2991:
2987:
2982:
2977:
2973:
2969:
2965:
2958:
2955:
2950:
2948:9780128023181
2944:
2940:
2933:
2931:
2929:
2925:
2920:
2916:
2911:
2906:
2902:
2898:
2894:
2887:
2884:
2878:
2874:
2871:
2870:
2866:
2864:
2862:
2858:
2840:
2835:
2820:
2815:
2805:
2802:
2793:
2791:
2787:
2783:
2779:
2774:
2772:
2768:
2763:
2761:
2744:
2735:
2729:
2720:
2702:
2687:
2682:
2672:
2669:
2661:
2657:
2655:
2651:
2647:
2643:
2639:
2634:
2627:
2623:
2619:
2615:
2611:
2606:
2588:
2573:
2568:
2558:
2555:
2547:
2523:
2520:
2517:
2514:
2508:
2502:
2494:
2490:
2487:
2484:
2477:
2469:
2464:
2454:
2451:
2447:
2443:
2437:
2425:
2415:
2414:
2413:
2397:
2382:
2377:
2367:
2364:
2356:
2355:
2349:
2344:
2342:
2338:
2334:
2326:
2324:
2322:
2318:
2314:
2310:
2307:
2303:
2299:
2296:
2295:block ciphers
2292:
2288:
2284:
2279:
2277:
2273:
2272:stream cipher
2269:
2264:
2262:
2258:
2257:
2250:
2246:
2242:
2238:
2234:
2230:
2225:
2221:
2216:
2212:
2208:
2204:
2198:
2194:
2190:
2186:
2182:
2177:
2173:
2169:
2165:
2161:
2156:
2154:
2150:
2146:
2142:
2138:
2134:
2130:
2122:
2117:
2114:
2113:
2112:
2107:Constructions
2106:
2104:
2102:
2098:
2094:
2088:
2084:
2069:
2062:) is at most
2061:
2057:
2053:
2049:
2046:is bent. The
2037:
2033:
2025:
2020:
2018:
2014:
2010:
1989:
1983:
1975:
1972:
1964:
1960:
1956:
1952:
1948:
1942:
1930:
1919:
1898:
1892:
1884:
1881:
1873:
1869:
1865:
1861:
1857:
1851:
1839:
1819:
1815:
1796:
1792:
1788:
1784:
1780:
1776:
1769:
1757:
1750:
1741:
1737:
1732:
1730:
1729:column vector
1726:
1722:
1703:
1695:
1689:
1681:
1678:
1671:
1666:
1662:
1658:
1654:
1651:
1645:
1633:
1623:
1622:
1621:
1619:
1618:bent sequence
1615:
1602:
1598:
1593:
1589:
1571:
1556:
1551:
1534:
1530:
1525:
1521:
1514:
1508:
1501:
1495:
1486:
1480:
1473:
1467:
1460:
1453:
1446:
1439:
1435:
1426:
1420:
1413:
1406:
1402:
1397:
1392:
1390:
1387:has constant
1386:
1368:
1353:
1348:
1338:
1335:
1327:
1326:bent function
1319:
1317:
1315:
1308:
1304:
1297:
1293:
1289:
1270:
1258:
1248:the value of
1238:
1234:
1214:
1209:
1205:
1201:
1198:
1192:
1184:
1174:
1164:
1159:
1155:
1151:
1145:
1137:
1127:
1116:
1115:
1114:
1110:
1106:
1102:
1095:
1089:
1085:
1081:
1074:
1054:
1049:
1045:
1041:
1035:
1023:
1017:
1012:
1008:
1004:
997:
996:
995:
984:
980:
975:
956:
951:
947:
943:
939:
932:
924:
920:
915:
911:
908:
904:
897:
889:
885:
880:
876:
872:
865:
857:
853:
848:
844:
838:
826:
816:
815:
814:
808:
801:
794:
787:
778:
774:
770:
766:
754:
750:
746:
739:
732:
728:
724:
720:
708:
704:
700:
693:
680:
676:
669:
665:
661:
657:
650:
644:
637:
631:
627:
623:
603:
598:
595:
592:
589:
583:
577:
569:
566:
554:
549:
539:
536:
530:
526:
520:
508:
498:
497:
496:
472:
467:
457:
448:
423:
408:
403:
393:
390:
382:
374:
372:
370:
366:
362:
358:
353:
351:
346:
344:
340:
339:coding theory
336:
332:
328:
327:Oscar Rothaus
323:
321:
317:
312:
310:
306:
302:
298:
294:
290:
286:
282:
278:
277:bent function
274:
273:combinatorics
270:
249:
246:
243:
240:
237:
234:
229:
226:
221:
218:
212:
208:
203:
200:
197:
193:
185:
164:
160:
154:
150:
146:
141:
137:
131:
127:
117:
97:
94:
91:
88:
85:
82:
77:
74:
69:
66:
60:
56:
51:
48:
45:
41:
33:
26:
21:
3707:
3679:
3644:
3640:
3631:
3612:24 September
3610:. Retrieved
3604:
3597:
3587:24 September
3585:. Retrieved
3547:
3543:
3522:
3497:
3493:
3487:
3478:
3472:
3455:
3442:
3430:. Retrieved
3424:
3414:
3404:20 September
3402:. Retrieved
3398:the original
3369:
3365:
3329:
3323:
3314:
3305:
3282:
3253:
3247:
3237:24 September
3235:. Retrieved
3231:the original
3208:
3198:
3188:21 September
3186:. Retrieved
3179:the original
3158:
3154:
3138:
3128:21 September
3126:. Retrieved
3104:
3100:
3086:
3076:21 September
3074:. Retrieved
3065:
3042:
3019:14 September
3017:. Retrieved
2971:
2967:
2957:
2938:
2900:
2896:
2886:
2860:
2856:
2794:
2781:
2777:
2775:
2770:
2766:
2764:
2759:
2718:
2659:
2658:
2653:
2649:
2645:
2637:
2632:
2625:
2621:
2617:
2613:
2609:
2604:
2545:
2543:
2353:
2347:
2345:
2340:
2336:
2332:
2330:
2282:
2280:
2265:
2260:
2255:
2248:
2244:
2240:
2236:
2232:
2228:
2223:
2219:
2214:
2210:
2206:
2196:
2192:
2188:
2184:
2180:
2175:
2160:cryptography
2157:
2155:techniques.
2145:Kasami codes
2126:
2123:Applications
2110:
2101:finite field
2089:
2082:
2067:
2059:
2055:
2051:
2035:
2032:nonlinearity
2031:
2021:
2012:
2008:
1917:
1817:
1813:
1739:
1735:
1733:
1725:Walsh matrix
1720:
1718:
1617:
1600:
1596:
1591:
1587:
1532:
1528:
1523:
1519:
1512:
1506:
1499:
1493:
1484:
1478:
1471:
1465:
1458:
1451:
1444:
1437:
1433:
1424:
1418:
1411:
1404:
1400:
1393:
1325:
1323:
1313:
1306:
1302:
1295:
1291:
1287:
1236:
1232:
1229:
1108:
1104:
1100:
1093:
1087:
1083:
1079:
1072:
1069:
982:
978:
973:
971:
806:
799:
792:
785:
776:
772:
768:
764:
752:
748:
744:
737:
730:
726:
722:
718:
706:
702:
698:
691:
678:
667:
663:
659:
655:
648:
642:
635:
629:
625:
621:
618:
378:
368:
364:
360:
356:
354:
349:
347:
331:cryptography
324:
313:
297:truth tables
276:
269:mathematical
266:
3687:. pp.
3144:A. Canteaut
3093:J. Pieprzyk
2974:: 120–147.
2147:for use in
2093:homogeneous
2019:functions.
1829:. In fact,
675:dot product
305:derivatives
301:correlation
3729:Categories
3538:PostScript
3529:D. Stinson
3279:S. Tavares
3010:J. Seberry
2879:References
2855:, such as
2412:such that
2217:(that is,
2207:derivative
2141:Gold codes
813:and hence
811:| = 2
3685:CRC Press
3663:1034-4942
3649:CiteSeerX
3647:: 21–35.
3574:0925-1022
3552:CiteSeerX
3514:0011-748X
3386:0925-1022
3338:CiteSeerX
3311:K. Nyberg
3291:CiteSeerX
3227:0018-9448
3175:1071-5797
3123:0166-218X
3047:Eurocrypt
2990:1071-5797
2919:0097-3165
2826:→
2786:bijective
2739:^
2693:→
2579:→
2521:⋅
2515:−
2488:π
2455:∈
2448:∑
2429:^
2388:→
2172:diffusion
1973:−
1934:^
1882:−
1843:^
1761:^
1679:−
1637:^
1612:taken in
1562:→
1359:→
1262:^
1202:−
1178:^
1131:^
1042:≤
1027:^
1018:≤
1005:−
944:−
877:−
830:^
596:⋅
567:−
540:∈
531:∑
512:^
495:given by
478:→
452:^
414:→
271:field of
241:−
227:−
209:−
201:−
147:⊕
89:−
75:−
57:−
49:−
3677:(2006).
3582:10572850
3420:Y. Zheng
3394:14365543
3334:AUSCRYPT
3275:C. Adams
2867:See also
2319:uses an
2302:CAST-256
2298:CAST-128
2256:balanced
2097:monomial
1916:, where
1811:for all
763: :
717: :
309:balanced
295:between
3689:337–339
3432:20 June
3008:C. Qu;
2350:is the
2168:S-boxes
2099:over a
2078:
2064:
781:. Then
673:is the
671:(mod 2)
267:In the
3714:
3695:
3661:
3651:
3580:
3572:
3554:
3512:
3392:
3384:
3340:
3293:
3258:CRYPTO
3225:
3173:
3121:
2988:
2945:
2917:
2357:type,
2085:> 2
2048:degree
1719:where
1518:⊕ … ⊕
1398:, are
1383:whose
1168:
783:|
747:) = {
701:) = {
654:+ … +
619:where
341:, and
285:linear
3578:S2CID
3452:(PDF)
3390:S2CID
3182:(PDF)
3151:(PDF)
3070:(PDF)
2717:with
2642:prime
2321:NLFSR
2317:Grain
2309:HAVAL
2253:is a
2080:(for
2044:2 − 2
2040:2 − 2
2028:2 ± 2
2007:, so
1305:) to
279:is a
3712:ISBN
3693:ISBN
3659:ISSN
3614:2009
3589:2009
3570:ISSN
3510:ISSN
3434:2015
3406:2009
3382:ISSN
3239:2009
3223:ISSN
3190:2009
3171:ISSN
3130:2009
3119:ISSN
3078:2009
3021:2009
2986:ISSN
2943:ISBN
2915:ISSN
2859:and
2765:The
2620:) −
2352:mod
2300:and
2289:and
2283:CAST
2243:) +
2231:) =
2191:) +
2149:CDMA
2143:and
2135:and
2017:dual
2011:and
1464:) =
1431:and
1417:) =
1103:) =
1082:) =
976:and
771:) ≠
735:and
725:) =
287:and
275:, a
3562:doi
3502:doi
3460:doi
3374:doi
3215:doi
3163:doi
3109:doi
3105:142
2976:doi
2905:doi
2782:all
2640:is
2087:).
2058:of
2050:of
2034:of
1316:).
1111:+ 1
677:in
371:).
369:APN
3731::
3691:.
3673:;
3657:.
3643:.
3576:.
3568:.
3560:.
3548:38
3546:.
3542:.
3508:.
3498:67
3496:.
3454:.
3388:.
3380:.
3370:12
3368:.
3364:.
3352:^
3332:.
3289:.
3277:;
3266:^
3256:.
3221:.
3207:.
3169:.
3159:14
3157:.
3153:.
3117:.
3103:.
3099:.
3055:^
3045:.
3029:^
2998:^
2984:.
2972:32
2970:.
2966:.
2927:^
2913:.
2901:20
2899:.
2895:.
2792:.
2773:.
2616:+
2607:,
2263:.
2251:))
2239:+
2187:+
1816:∈
1742:,
1731:.
1599:∈
1526:−1
1505:⊕
1477:⊕
1457:,
1450:,
1443:,
1410:,
1235:∈
1107:·
1086:·
981:∈
775:·
751:∈
729:·
705:∈
641:+
628:=
624:·
361:PN
337:,
322:.
3720:.
3701:.
3665:.
3645:9
3616:.
3591:.
3564::
3540:)
3536:(
3516:.
3504::
3466:.
3462::
3436:.
3408:.
3376::
3346:.
3299:.
3241:.
3217::
3192:.
3165::
3132:.
3111::
3080:.
3023:.
2992:.
2978::
2951:.
2921:.
2907::
2841:n
2836:2
2831:Z
2821:n
2816:2
2811:Z
2806::
2803:f
2760:m
2745:|
2736:f
2730:|
2719:n
2703:m
2698:Z
2688:n
2683:m
2678:Z
2673::
2670:f
2654:n
2650:m
2646:m
2638:m
2633:m
2628:)
2626:a
2624:(
2622:f
2618:a
2614:x
2612:(
2610:f
2605:a
2589:m
2584:Z
2574:n
2569:m
2564:Z
2559::
2556:f
2546:m
2527:)
2524:x
2518:a
2512:)
2509:x
2506:(
2503:f
2500:(
2495:m
2491:i
2485:2
2478:e
2470:n
2465:m
2460:Z
2452:x
2444:=
2441:)
2438:a
2435:(
2426:f
2398:m
2393:Z
2383:n
2378:m
2373:Z
2368::
2365:f
2354:m
2341:k
2337:p
2333:q
2249:x
2247:(
2245:f
2241:a
2237:x
2235:(
2233:f
2229:x
2227:(
2224:a
2220:f
2215:a
2211:f
2199:)
2197:x
2195:(
2193:f
2189:a
2185:x
2183:(
2181:f
2083:n
2075:2
2072:/
2068:n
2060:f
2052:f
2036:f
2013:g
2009:f
1993:)
1990:a
1987:(
1984:f
1980:)
1976:1
1970:(
1965:2
1961:/
1957:n
1953:2
1949:=
1946:)
1943:a
1940:(
1931:g
1918:g
1902:)
1899:a
1896:(
1893:g
1889:)
1885:1
1879:(
1874:2
1870:/
1866:n
1862:2
1858:=
1855:)
1852:a
1849:(
1840:f
1824:2
1818:Z
1814:a
1797:2
1793:/
1789:n
1785:2
1781:=
1777:|
1773:)
1770:a
1767:(
1758:f
1751:|
1740:f
1736:n
1721:W
1704:,
1699:)
1696:a
1693:(
1690:f
1686:)
1682:1
1676:(
1672:)
1667:n
1663:2
1659:(
1655:W
1652:=
1649:)
1646:a
1643:(
1634:f
1607:2
1601:Z
1597:x
1592:n
1588:n
1572:2
1567:Z
1557:n
1552:2
1547:Z
1533:n
1529:x
1524:n
1520:x
1516:4
1513:x
1510:3
1507:x
1503:2
1500:x
1497:1
1494:x
1488:4
1485:x
1482:3
1479:x
1475:2
1472:x
1469:1
1466:x
1462:4
1459:x
1455:3
1452:x
1448:2
1445:x
1441:1
1438:x
1436:(
1434:G
1428:2
1425:x
1422:1
1419:x
1415:2
1412:x
1408:1
1405:x
1403:(
1401:F
1369:2
1364:Z
1354:n
1349:2
1344:Z
1339::
1336:f
1314:x
1312:(
1310:1
1307:f
1303:x
1301:(
1299:0
1296:f
1292:x
1290:(
1288:f
1274:)
1271:a
1268:(
1259:f
1243:2
1237:Z
1233:a
1215:.
1210:n
1206:2
1199:=
1196:)
1193:a
1190:(
1185:1
1175:f
1165:,
1160:n
1156:2
1152:=
1149:)
1146:a
1143:(
1138:0
1128:f
1109:x
1105:a
1101:x
1099:(
1097:1
1094:f
1088:x
1084:a
1080:x
1078:(
1076:0
1073:f
1055:.
1050:n
1046:2
1039:)
1036:a
1033:(
1024:f
1013:n
1009:2
989:2
983:Z
979:a
974:f
957:.
952:n
948:2
940:|
936:)
933:a
930:(
925:0
921:S
916:|
912:2
909:=
905:|
901:)
898:a
895:(
890:1
886:S
881:|
873:|
869:)
866:a
863:(
858:0
854:S
849:|
845:=
842:)
839:a
836:(
827:f
809:)
807:a
805:(
803:1
800:S
795:)
793:a
791:(
789:0
786:S
779:}
777:x
773:a
769:x
767:(
765:f
759:2
753:Z
749:x
745:a
743:(
741:1
738:S
733:}
731:x
727:a
723:x
721:(
719:f
713:2
707:Z
703:x
699:a
697:(
695:0
692:S
685:2
679:Z
668:n
664:x
660:n
656:a
652:2
649:x
646:2
643:a
639:1
636:x
633:1
630:a
626:x
622:a
604:,
599:x
593:a
590:+
587:)
584:x
581:(
578:f
574:)
570:1
564:(
555:n
550:2
545:Z
537:x
527:=
524:)
521:a
518:(
509:f
482:Z
473:n
468:2
463:Z
458::
449:f
424:2
419:Z
409:n
404:2
399:Z
394::
391:f
367:(
359:(
250:6
247:=
244:2
238:8
235:=
230:1
222:2
219:4
213:2
204:1
198:4
194:2
165:4
161:x
155:3
151:x
142:2
138:x
132:1
128:x
98:1
95:=
92:1
86:2
83:=
78:1
70:2
67:2
61:2
52:1
46:2
42:2
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.