516:
268:
502:
396:, but by far the most important variable in CIH's success in writing to a machine's BIOS is the type of Flash ROM chip in the machine. Different Flash ROM chips (or chip families) have different write-enable routines specific to those chips. CIH makes no attempt to test for the Flash ROM type in its victim machines and has only one write-enable sequence.
415:
of the first partition and the first copy of the FAT of the first partition. The MBR and boot sectors can simply be replaced with copies of the standard versions; the partition table can be rebuilt by scanning over the entire drive and the first copy of the FAT can be restored from the second copy.
343:
CIH infects
Portable Executable files by splitting the bulk of its code into small slivers inserted into the inter-section gaps commonly seen in PE files and writing a small re-assembly routine and table of its own code segments' locations into unused space in the tail of the PE header. This earned
145:
The name "Spacefiller" was introduced because most viruses write their code to the end of the infected file, with infected files being detectable because their file size increases. In contrast, CIH looks for gaps in the existing program code, where it then writes its code, preventing an increase in
133:
The name "Chernobyl Virus" was coined sometime after the virus was already well known as CIH and refers to the complete coincidence of the payload trigger date in some variants of the virus (actually the virus creation date in 1998, to trigger exactly a year later) and the
430:
If the second payload executes successfully, the computer will not start at all. Reprogramming or replacement of the Flash BIOS chip is then required, as most systems that CIH can affect predate BIOS restoration features.
386:. BIOSes that can be successfully written to by the virus have critical boot-time codes replaced with junk. This routine only works on some machines. Much emphasis has been put on machines with motherboards based on the
47:
117:
developers. Chen stated that after classmates at Tatung
University spread the virus, he apologized to the school and made an antivirus program available for public download. Weng Shi-hao (翁世豪), a student at
209:. Both of these payloads served to render the host computer inoperable, and for most ordinary users, the virus essentially destroyed the PC. Technically, however, it was possible to replace the
1062:
82:
that first emerged in 1998. Its payload is highly destructive to vulnerable systems, overwriting critical information on infected system drives and, in some cases, destroying the system
858:
884:
811:
816:
254:
A modified version of the virus called CIH.1106 was discovered in
December 2002, but it is not widespread and only affects Windows 9x-based systems.
670:
534:
289:
606:
584:
423:
If the first partition is not FAT32 or is smaller than 1 GB, the bulk of user data on that partition will still be intact, but without the
708:
851:
825:
348:, but due to its novel multiple-cavity infection method, infected files do not grow at all. It uses methods of jumping from processor
315:
557:
247:
file that contained a dropper routine for the CIH virus was circulated around the internet under the guise of a nude picture of
529:
293:
684:
1146:
1141:
1136:
1131:
1110:
889:
879:
844:
753:
620:
220:
Today, CIH is not as widespread as it once was, due to awareness of the threat and the fact that it only affects older
989:
278:
399:
For the first payload, any information that the virus has overwritten with zeros is lost. If the first partition is
162:
297:
282:
1105:
332:
file format under the
Windows 9x-based operating systems, Windows 95, 98, and ME. CIH does not spread under
193:
CIH's dual payload was delivered for the first time on April 26, 1999, with most of the damage occurring in
1047:
801:
390:
122:, co-authored with the antivirus program. Prosecutors in Taiwan could not charge Chen at the time because
731:
1095:
400:
416:
This means a complete recovery with no loss of user data can be performed automatically by a tool like
102:. It was believed to have infected sixty million computers internationally, resulting in an estimated
999:
931:
662:
376:
355:
The payload, which is considered extremely dangerous, first involves the virus overwriting the first
181:
113:
Chen claimed to have written the virus as a challenge against bold claims of antiviral efficiency by
107:
176:
shipped a software update to their CD-R400 drives that was infected with the virus. In July 1998, a
172:
7 attendees were discovered by the organizers to have been infected with CIH. On
December 31, 1999,
1037:
329:
161:
shipped with the CIH virus, just one month before the virus would trigger. In July 1999, copies of
915:
408:
368:
173:
135:
119:
114:
637:
592:
716:
614:
165:
103:
95:
31:
1017:
372:
427:
and FAT it will be difficult to find it, especially if there is significant fragmentation.
360:
349:
214:
1052:
1022:
947:
453:
This variant is the most common one and activates on April 26. It contains the string:
424:
248:
79:
1125:
1027:
565:
521:
123:
1042:
961:
507:
139:
694:
609:(in Chinese). 行政執行署嘉義行政執行處. 2005-12-10. Archived from the original on 2013-10-29.
1032:
969:
412:
364:
337:
267:
1057:
979:
974:
497:
333:
233:
229:
225:
221:
202:
158:
127:
76:
774:
745:
1067:
806:
210:
177:
17:
501:
1100:
404:
356:
345:
244:
240:
198:
475:
This variant activates on the 26th of any month. It contains the string
1090:
1077:
994:
836:
393:
169:
1009:
99:
87:
344:
CIH another name, "Spacefiller". The size of the virus is around 1
336:-based operating systems nor Win16-based operating systems such as
126:
came forward with a lawsuit. Nevertheless, these events led to new
984:
821:
689:
387:
464:
This variant also activates on April 26. It contains the string:
154:
The virus first emerged in 1998. In March 1999, several thousand
709:"US Report: Gamers believe Activision's 'SiN' carries CIH virus"
383:
206:
194:
83:
840:
685:"Back Orifice CDs infected with CIH virus - Tech News on ZDNet"
417:
261:
239:
The virus made another comeback in 2001 when a variant of the
186:
155:
46:
831:
487:
This variant activates on August 2 instead of April 26.
146:
file size; in that way, the virus avoids detection.
1076:
1008:
960:
940:
924:
908:
901:
39:
585:"從駭電腦到愛旅行─昔日網路小子陳盈豪 - 親子天下雜誌8期 - 陳盈豪,網路世界,宅男,網路沉迷"
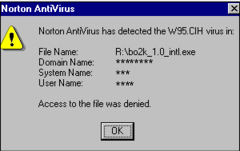
54:Antivirus intercept message on a Windows 95 system
382:The second payload tries to write to the Flash
30:For a similar signature in FAT OEM labels, see
638:"What is the Chernobyl Virus? (with pictures)"
205:with zeros and then attacked certain types of
86:. The virus was created by Chen Ing-hau (陳盈豪,
852:
8:
828:on how to repair most of the damage from CIH
817:News article about the Jennifer Lopez e-mail
579:
577:
575:
296:. Unsourced material may be challenged and
905:
859:
845:
837:
732:"Is the CIH virus on the endangered list?"
45:
316:Learn how and when to remove this message
190:was infected by one of its mirror sites.
591:(in Chinese). 2013-06-07. Archived from
564:(in Chinese). 2006-08-25. Archived from
552:
550:
438:
546:
407:, all that will get overwritten is the
632:
630:
612:
535:Timeline of computer viruses and worms
110:35,801,231.56) in commercial damages.
36:
663:"Some Aptivas shipped with CIH virus"
7:
367:0. This deletes the contents of the
294:adding citations to reliable sources
607:"打擊駭客,不再無法可施 - 安全常識 - 法務部行政執行署嘉義分署"
461:CIH v1.3/CIH.1010.A and CIH1010.B
25:
673:from the original on 2007-01-04.
514:
500:
266:
775:"Virus:DOS/CIH | F-Secure Labs"
756:from the original on 2001-01-28
693:. July 14, 1999. Archived from
371:, and may cause the machine to
730:Lemos, Robert (May 25, 1999).
530:Comparison of computer viruses
1:
715:. 28 Jul 1998. Archived from
352:3 to 0 to hook system calls.
213:, and methods for recovering
197:. CIH filled the first 1024
812:Symantec CIH Technical Page
807:F-Secure CIH Technical Page
411:, the partition table, the
1163:
661:Weil, Nancy (1999-04-07).
363:with zeroes, beginning at
163:remote administration tool
29:
872:
619:: CS1 maint: unfit URL (
58:
53:
44:
27:Windows 9x computer virus
138:, which happened in the
130:legislation in Taiwan.
328:CIH spreads under the
802:F-Secure CIH Database
403:, and over about one
236:) operating systems.
1147:Taiwanese inventions
1142:Hacking in the 1990s
1137:Hacking in the 2000s
1132:Windows file viruses
932:Operation CyberSnare
867:Hacking in the 1990s
558:"從CIH「重裝駭客」變身「除錯超人」"
377:blue screen of death
290:improve this section
217:data emerged later.
182:first-person shooter
77:Microsoft Windows 9x
832:CIH 1.4 source code
330:Portable Executable
142:on April 26, 1986.
916:Operation Sundevil
472:CIH v1.4/CIH.1019
450:CIH v1.2/CIH.1003
136:Chernobyl disaster
120:Tamkang University
115:antivirus software
1119:
1118:
956:
955:
896:
895:
491:
490:
326:
325:
318:
166:Back Orifice 2000
96:Tatung University
62:
61:
32:FAT IHC OEM label
16:(Redirected from
1154:
906:
875:
874:
861:
854:
847:
838:
789:
788:
786:
785:
779:www.f-secure.com
771:
765:
764:
762:
761:
742:
736:
735:
727:
721:
720:
705:
699:
698:
681:
675:
674:
658:
652:
651:
649:
648:
642:Easy Tech Junkie
634:
625:
624:
618:
610:
603:
597:
596:
589:parenting.com.tw
581:
570:
569:
554:
524:
519:
518:
517:
510:
505:
504:
478:
467:
456:
439:
359:(1024KB) of the
321:
314:
310:
307:
301:
270:
262:
94:), a student at
67:, also known as
49:
37:
21:
1162:
1161:
1157:
1156:
1155:
1153:
1152:
1151:
1122:
1121:
1120:
1115:
1072:
1004:
952:
936:
920:
897:
868:
865:
798:
793:
792:
783:
781:
773:
772:
768:
759:
757:
746:"Virus:DOS/CIH"
744:
743:
739:
729:
728:
724:
707:
706:
702:
683:
682:
678:
660:
659:
655:
646:
644:
636:
635:
628:
611:
605:
604:
600:
583:
582:
573:
556:
555:
548:
543:
520:
515:
513:
506:
499:
496:
477:CIH v1.4 TATUNG
476:
465:
454:
437:
369:partition table
322:
311:
305:
302:
287:
271:
260:
258:Virus specifics
241:LoveLetter Worm
180:version of the
152:
35:
28:
23:
22:
15:
12:
11:
5:
1160:
1158:
1150:
1149:
1144:
1139:
1134:
1124:
1123:
1117:
1116:
1114:
1113:
1108:
1103:
1098:
1093:
1088:
1082:
1080:
1074:
1073:
1071:
1070:
1065:
1060:
1055:
1053:Jonathan James
1050:
1045:
1040:
1035:
1030:
1025:
1020:
1014:
1012:
1006:
1005:
1003:
1002:
997:
992:
987:
982:
977:
972:
966:
964:
958:
957:
954:
953:
951:
950:
948:Moonlight Maze
944:
942:
938:
937:
935:
934:
928:
926:
922:
921:
919:
918:
912:
910:
903:
899:
898:
894:
893:
887:
882:
873:
870:
869:
866:
864:
863:
856:
849:
841:
835:
834:
829:
819:
814:
809:
804:
797:
796:External links
794:
791:
790:
766:
737:
722:
719:on 2009-04-17.
700:
697:on 2007-03-11.
676:
653:
626:
598:
595:on 2013-06-07.
571:
568:on 2013-04-17.
545:
544:
542:
539:
538:
537:
532:
526:
525:
511:
495:
492:
489:
488:
485:
481:
480:
473:
469:
468:
462:
458:
457:
451:
447:
446:
443:
436:
433:
425:root directory
324:
323:
274:
272:
265:
259:
256:
249:Jennifer Lopez
201:of the host's
151:
148:
128:computer crime
80:computer virus
60:
59:
56:
55:
51:
50:
42:
41:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
1159:
1148:
1145:
1143:
1140:
1138:
1135:
1133:
1130:
1129:
1127:
1112:
1109:
1107:
1104:
1102:
1099:
1097:
1094:
1092:
1089:
1087:
1084:
1083:
1081:
1079:
1075:
1069:
1066:
1064:
1061:
1059:
1056:
1054:
1051:
1049:
1048:Erik Bloodaxe
1046:
1044:
1041:
1039:
1036:
1034:
1031:
1029:
1026:
1024:
1021:
1019:
1016:
1015:
1013:
1011:
1007:
1001:
998:
996:
993:
991:
988:
986:
983:
981:
978:
976:
973:
971:
968:
967:
965:
963:
959:
949:
946:
945:
943:
939:
933:
930:
929:
927:
923:
917:
914:
913:
911:
907:
904:
900:
892: →
891:
888:
886:
883:
881:
878:←
877:
876:
871:
862:
857:
855:
850:
848:
843:
842:
839:
833:
830:
827:
823:
820:
818:
815:
813:
810:
808:
805:
803:
800:
799:
795:
780:
776:
770:
767:
755:
751:
750:F-Secure Labs
747:
741:
738:
733:
726:
723:
718:
714:
710:
704:
701:
696:
692:
691:
686:
680:
677:
672:
668:
664:
657:
654:
643:
639:
633:
631:
627:
622:
616:
608:
602:
599:
594:
590:
586:
580:
578:
576:
572:
567:
563:
562:iThome online
559:
553:
551:
547:
540:
536:
533:
531:
528:
527:
523:
522:Taiwan portal
512:
509:
503:
498:
493:
486:
483:
482:
474:
471:
470:
466:CIH v1.3 TTIT
463:
460:
459:
455:CIH v1.2 TTIT
452:
449:
448:
444:
441:
440:
434:
432:
428:
426:
421:
419:
414:
410:
406:
402:
397:
395:
392:
389:
385:
380:
378:
374:
370:
366:
362:
358:
353:
351:
347:
341:
339:
335:
331:
320:
317:
309:
299:
295:
291:
285:
284:
280:
275:This section
273:
269:
264:
263:
257:
255:
252:
250:
246:
242:
237:
235:
231:
227:
223:
218:
216:
212:
208:
204:
200:
196:
191:
189:
188:
183:
179:
175:
171:
168:given out to
167:
164:
160:
157:
149:
147:
143:
141:
137:
131:
129:
125:
121:
116:
111:
109:
105:
101:
97:
93:
89:
85:
81:
78:
74:
70:
66:
57:
52:
48:
43:
38:
33:
19:
1111:Michelangelo
1085:
1063:Steven Games
1058:Phiber Optik
1043:Dark Avenger
1023:The Analyzer
826:Steve Gibson
782:. Retrieved
778:
769:
758:. Retrieved
749:
740:
725:
717:the original
712:
703:
695:the original
688:
679:
666:
656:
645:. Retrieved
641:
601:
593:the original
588:
566:the original
561:
508:1990s portal
445:Description
429:
422:
398:
381:
354:
342:
327:
312:
306:October 2021
303:
288:Please help
276:
253:
238:
219:
192:
185:
153:
144:
140:Soviet Union
132:
112:
92:Chén Yíngháo
91:
72:
68:
64:
63:
18:Chen Ing Hau
1018:Acid Phreak
1010:Individuals
990:Level Seven
970:CyberThrill
713:ZDNet.co.uk
413:boot sector
375:or cue the
338:Windows 3.x
106:1 billion (
73:Spacefiller
1126:Categories
980:Global kOS
975:globalHell
824:- Site by
784:2023-11-05
760:2021-12-07
647:2023-02-16
541:References
361:hard drive
340:or below.
334:Windows NT
222:Windows 9x
203:boot drive
124:no victims
1068:YTCracker
902:Incidents
484:CIH.1049
277:does not
215:hard disk
211:BIOS chip
69:Chernobyl
1038:Cucumber
885:Timeline
754:Archived
671:Archived
615:cite web
494:See also
442:Moniker
435:Variants
405:gigabyte
357:megabyte
346:kilobyte
1106:Melissa
1091:Happy99
1078:Malware
1033:Corrupt
995:Milw0rm
822:FIX-CIH
418:Fix CIH
394:chipset
298:removed
283:sources
170:DEF CON
159:Aptivas
150:History
75:, is a
1028:Condor
962:Groups
365:sector
174:Yamaha
100:Taiwan
88:pinyin
985:L0pht
890:2000s
880:1980s
690:ZDNet
401:FAT32
391:430TX
388:Intel
243:in a
184:game
1096:Hare
941:1998
925:1995
909:1990
621:link
384:BIOS
373:hang
350:ring
281:any
279:cite
207:BIOS
195:Asia
178:demo
108:US$
104:NT$
84:BIOS
1101:KAK
1086:CIH
1000:MOD
667:CNN
409:MBR
292:by
245:VBS
187:SiN
156:IBM
98:in
71:or
65:CIH
40:CIH
1128::
777:.
752:.
748:.
711:.
687:.
669:.
665:.
640:.
629:^
617:}}
613:{{
587:.
574:^
560:.
549:^
479:.
420:.
379:.
251:.
234:ME
232:,
230:98
228:,
226:95
199:KB
90::
860:e
853:t
846:v
787:.
763:.
734:.
650:.
623:)
319:)
313:(
308:)
304:(
300:.
286:.
224:(
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.