22:
215:(NOC) complement each other and work in tandem. The NOC is usually responsible for monitoring and maintaining the overall network infrastructure, and its primary function is to ensure uninterrupted network service. The SOC is responsible for protecting networks, as well as web sites, applications, databases, servers and data centers, and other technologies. Likewise, the SOC and the physical security operations center coordinate and work together. The physical SOC is a facility in large organizations where security staff monitor and control security officers/guards, alarms, CCTV, physical access, lighting, vehicle barriers, etc.
88:
threatening IT incident, and will ensure that it is properly identified, analyzed, communicated, investigated and reported. The SOC also monitors applications to identify a possible cyber-attack or intrusion (event), and determines if it is a genuine malicious threat (incident), and if it could affect business.
269:
Processes and procedures within a SOC will clearly spell out roles and responsibilities as well as monitoring procedures. These processes include business, technology, operational and analytical processes. They lay out what steps are to be taken in the event of an alert or breach including escalation
119:
A security operations center (SOC) can also be called a security defense center (SDC), security analytics center (SAC), network security operations center (NSOC), security intelligence center, cyber security center, threat defense center, security intelligence and operations center (SIOC). In the
260:
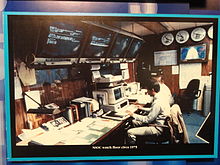
SOCs usually are well protected with physical, electronic, computer, and personnel security. Centers are often laid out with desks facing a video wall, which displays significant status, events and alarms; ongoing incidents; a corner of the wall is sometimes used for showing a news or weather TV
87:
A SOC is related to the people, processes and technologies that provide situational awareness through the detection, containment, and remediation of IT threats in order to manage and enhance an organization's security posture. A SOC will handle, on behalf of an institution or company, any
191:
SOC staffing plans range from eight hours a day, five days a week (8x5) to twenty four hours a day, seven days a week (24x7). Shifts should include at least two analysts and the responsibilities should be clearly defined.
302:
solution that utilizes leading-edge technology and tools, highly skilled and experienced human talent (composed of cyber intelligence gatherers, analysts, and security experts), and proactive
261:
channel, as this can keep the SOC staff aware of current events which may affect information systems. A security engineer or security analyst may have several computer monitors on their desk.
208:. The term SOC was traditionally used by governments and managed computer security providers, although a growing number of large corporations and other organizations also have such centers.
21:
252:. Typically, larger organizations maintain a separate SOC to ensure focus and expertise. The SOC then collaborates closely with network operations and physical security operations.
181:
429:
228:
Operational - focusing on the operational security administration such as identity & access management, key management, firewall administration, etc.
185:
287:
164:
SOC staff includes analysts, security engineers, and SOC managers who should be seasoned IT and networking professionals. They are usually trained in
129:
201:
218:
Not every SOC has the same role. There are three different focus areas in which a SOC may be active, and which can be combined in any combination:
156:
and unified threat management (UTM). The SIEM technology creates a "single pane of glass" for the security analysts to monitor the enterprise.
232:
In some cases the SOC, NOC or physical SOC may be housed in the same facility or organizationally combined, especially if the focus is on
480:
136:
systems; governance, risk and compliance (GRC) systems; web site assessment and monitoring systems, application and database scanners;
237:
96:
Establishing and operating a SOC is expensive and difficult; organisations should need a good reason to do it. This may include:
48:
278:
A cloud security operations center (CloudSOC) may be set up to monitor cloud service use within an enterprise (and keep the
314:
In addition, there are many other commonly referenced terms related to the original "ISOC" title including the following:
222:
Control - focusing on the state of the security with compliancy testing, penetration testing, vulnerability testing, etc.
504:
145:
141:
204:
or to provide redundancy in the event one site is unavailable. SOC work can be outsourced, for instance, by using a
514:
306:
principles to prevent and neutralize threats against an organization’s digital infrastructure, assets, and data.
212:
149:
225:
Monitoring - focusing on events and the response with log monitoring, SIEM administration, and incident response
342:
205:
133:
454:
403:
120:
Canadian
Federal Government the term, infrastructure protection center (IPC), is used to describe a SOC.
509:
249:
165:
132:(SIEM) system which aggregates and correlates data from security feeds such as network discovery and
56:
76:
68:
200:
Large organizations and governments may operate more than one SOC to manage different groups of
385:
299:
290:
technologies and machine data platforms to provide alerts and details of suspicious activity.
283:
375:
177:
173:
137:
72:
455:"Managed Services at the Tactical FLEX, Inc. Network Security Operations Center (NSOC)"
498:
303:
169:
64:
16:
Facility where enterprise information systems are monitored, assessed, and defended
298:
A Smart SOC (Security
Operations Center) is a comprehensive, technology agnostic
380:
363:
337:
389:
279:
153:
60:
52:
248:, in which case the SOC operates independently from the NOC to maintain
104:
364:"Security Operations Center: A Systematic Study and Open Challenges"
270:
procedures, reporting procedures, and breach response procedures.
20:
458:
152:; wireless intrusion prevention system; firewalls, enterprise
148:(IPS); log management systems; network behavior analysis and
362:
Vielberth, M.; Böhm, F.; Fichtinger, I.; Pernul, G. (2020).
79:
and other endpoints) are monitored, assessed, and defended.
430:"Transaction Monitoring for HMG Online Service Providers"
481:"What is a Virtual Security Operations Center (VSOC)?"
25:
The United States national security operations center
404:"PCI DSS 3.0: The Impact on Your Security Operations"
110:
Complying with government rules, such as CESG GPG53.
240:organisation, then the focus is usually more on
8:
282:problem under control), or parse and audit
379:
321:ASOC, Advanced Security Operations Center
130:security information and event management
327:vSOC, Virtual Security Operations Center
318:SNOC, Security Network Operations Center
202:information and communication technology
354:
324:GSOC, Global Security Operations Center
103:Complying with industry rules such as
37:information security operations center
7:
457:. Tactical FLEX, Inc. Archived from
236:tasks. If the SOC originates from a
128:SOCs typically are based around a
14:
180:and may have credentials such as
49:enterprise information systems
1:
26:
381:10.1109/ACCESS.2020.3045514
146:intrusion prevention system
142:intrusion detection systems
531:
310:Other types and references
286:and application logs via
213:network operations center
150:Cyber threat intelligence
100:Protecting sensitive data
343:Managed security service
206:managed security service
134:vulnerability assessment
92:Regulatory requirements
265:Process and procedures
47:) is a facility where
32:
485:cybersecurity.att.com
461:on September 24, 2014
24:
250:separation of duties
166:computer engineering
410:. December 31, 2013
174:network engineering
138:penetration testing
505:Network management
33:
515:Computer security
374:: 227756–227779.
284:IT infrastructure
115:Alternative names
522:
489:
488:
477:
471:
470:
468:
466:
451:
445:
444:
442:
440:
434:
426:
420:
419:
417:
415:
400:
394:
393:
383:
359:
211:The SOC and the
178:computer science
31:
28:
530:
529:
525:
524:
523:
521:
520:
519:
495:
494:
493:
492:
479:
478:
474:
464:
462:
453:
452:
448:
438:
436:
432:
428:
427:
423:
413:
411:
402:
401:
397:
361:
360:
356:
351:
334:
312:
296:
276:
267:
258:
198:
162:
126:
117:
94:
85:
29:
17:
12:
11:
5:
528:
526:
518:
517:
512:
507:
497:
496:
491:
490:
472:
446:
421:
395:
353:
352:
350:
347:
346:
345:
340:
333:
330:
329:
328:
325:
322:
319:
311:
308:
295:
292:
275:
272:
266:
263:
257:
254:
230:
229:
226:
223:
197:
194:
161:
158:
125:
122:
116:
113:
112:
111:
108:
101:
93:
90:
84:
81:
15:
13:
10:
9:
6:
4:
3:
2:
527:
516:
513:
511:
508:
506:
503:
502:
500:
486:
482:
476:
473:
465:September 20,
460:
456:
450:
447:
431:
425:
422:
409:
408:Security Week
405:
399:
396:
391:
387:
382:
377:
373:
369:
365:
358:
355:
348:
344:
341:
339:
336:
335:
331:
326:
323:
320:
317:
316:
315:
309:
307:
305:
301:
300:cybersecurity
293:
291:
289:
285:
281:
273:
271:
264:
262:
255:
253:
251:
247:
243:
239:
235:
227:
224:
221:
220:
219:
216:
214:
209:
207:
203:
195:
193:
189:
187:
183:
179:
175:
171:
167:
159:
157:
155:
151:
147:
143:
139:
135:
131:
123:
121:
114:
109:
106:
102:
99:
98:
97:
91:
89:
82:
80:
78:
74:
70:
66:
62:
58:
54:
50:
46:
42:
38:
23:
19:
510:Surveillance
484:
475:
463:. Retrieved
459:the original
449:
437:. Retrieved
424:
412:. Retrieved
407:
398:
371:
367:
357:
313:
304:cyberwarfare
297:
277:
268:
259:
245:
241:
233:
231:
217:
210:
199:
196:Organization
190:
170:cryptography
163:
127:
118:
95:
86:
65:data centers
57:applications
44:
40:
36:
34:
18:
368:IEEE Access
338:Data center
234:operational
30: 1975
499:Categories
349:References
256:Facilities
242:monitoring
124:Technology
390:2169-3536
294:Smart SOC
280:Shadow IT
154:antivirus
83:Objective
61:databases
53:web sites
439:June 22,
414:June 22,
332:See also
274:CloudSOC
77:desktops
73:networks
246:control
144:(IDS);
140:tools;
105:PCI DSS
69:servers
435:. CESG
388:
160:People
433:(PDF)
182:CISSP
176:, or
467:2014
441:2014
416:2014
386:ISSN
288:SIEM
244:and
238:CERT
186:GIAC
67:and
41:ISOC
376:doi
184:or
45:SOC
43:or
35:An
501::
483:.
406:.
384:.
370:.
366:.
188:.
172:,
168:,
75:,
71:,
63:,
59:,
55:,
27:c.
487:.
469:.
443:.
418:.
392:.
378::
372:8
107:.
51:(
39:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.