414:
within this networked system (a network system referred to as BudNET). Improving the overall security of an operating system is commonly referred to as "OS Hardening." The member of the team that was charged with this was SSgt. Donald R. Woeltje Jr. and the concept he came up with was the installation of special software (firewall software) on every BudNET server, workstation, and perimeter security device. Indeed, every single
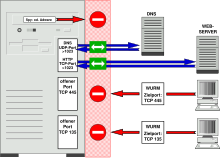
Windows system on the BudNET network. This is a concept that is now commonly referred to as "personal firewall" software. So, while SSgt. Woeltje did not invent personal firewall software, he did invent the idea of the "personal firewall." Evidence of this fact exists in the Anheuser-Busch Security Model Proposal document made by SSgt. Woeltje, at the time. When SSgt. Woeltje brought in all the leading firewall vendors for meetings concerning the products being considered for use for the perimeter security of the BudNET network, SSgt. Woeltje brought up the concept of the "personal firewall" with the vendors and asked them if they had any firewall product that could be used in this way. With the exception of the representatives from the Cyberguard Corporation, every vendor said that not only did that not have any firewall software that could be used in this way but they also said that the idea was crazy and unworkable. But, today we know they were wrong because the use of personal firewall software has become a de facto computer security standard. The companies that SSgt. Woeltje discussed "personal firewall" software with were, among others, Cisco, Checkpoint, Axent Technologies, Milkyway Networks, Cyberguard, Network ONE, Trusted Information Systems, and Secure Computing Corporation.
17:
172:
70:
29:
291:
on the secured computer. When an application attempts an outbound connection, the firewall may block it if blacklisted, or ask the user whether to blacklist it if it is not yet known. This protects against malware implemented as an executable program. Personal firewalls may also provide some level of
413:
architecture project for a
Fortune 100 corporation in the United States (the Anheuser-Busch Corporation), one of the members of the three-man architectural development team came up with a concept with regards to improving the overall security of the operating system to be used on all the computers
259:
in terms of scale. A personal firewall will usually protect only the computer on which it is installed, as compared to a conventional firewall which is normally installed on a designated interface between two or more networks, such as a
279:
at a workplace where minimal protection is needed as a conventional firewall is already in place, and services that require open ports such as file and printer sharing are useful. The same laptop could be used at public
284:, where it may be necessary to decide the level of trust and reconfigure firewall settings to limit traffic to and from the computer. A firewall can be configured to allow different security policies for each network.
373:
or similar software, these programs can also manipulate the firewall, because both are running on the same system. It may be possible to bypass or even completely shut down software firewalls in such a
268:. Hence, personal firewalls allow a security policy to be defined for individual computers, whereas a conventional firewall controls the policy between the networks that it connects.
387:
are not the only solution to secure private documents and emails that are either sent within an organization or to other business contacts that are outside the organization.
857:
543:
973:
469:
87:
42:
182:
271:
The per-computer scope of personal firewalls is useful to protect machines that are moved across different networks. For example, a
219:
153:
56:
380:
Firewall may limit access from the
Internet, but it may not protect your network from wireless and other access to your systems.
134:
536:
106:
91:
887:
852:
113:
882:
568:
501:
497:
390:
The alerts generated can possibly desensitize users to alerts by warning the user of actions that may not be malicious.
847:
341:
Track recent incoming events, outgoing events, and intrusion events to see who has accessed or tried to access your
994:
529:
358:
293:
249:
120:
80:
925:
872:
867:
515:
509:
384:
296:, allowing the software to terminate or block connectivity where it suspects an intrusion is being attempted.
102:
968:
428:
660:
613:
194:
48:
842:
897:
877:
563:
552:
410:
288:
256:
237:
670:
423:
335:
312:
287:
Unlike network firewalls, many personal firewalls are able to control network traffic allowed to
261:
127:
827:
578:
505:
473:
433:
397:
892:
655:
583:
438:
241:
400:
at the kernel mode level may potentially cause instability and/or introduce security flaws.
319:
and provide the user with information about an application that makes a connection attempt.
678:
281:
245:
457:
747:
308:
Block or alert the user about all unauthorized inbound or outbound connection attempts.
988:
807:
802:
752:
951:
812:
322:
Hide the computer from port scans by not responding to unsolicited network traffic.
265:
244:
traffic to and from a computer, permitting or denying communications based on a
69:
16:
862:
742:
698:
396:
firewalls that interface with the operating system or with other firewalls or
946:
930:
708:
650:
623:
618:
193:
by adding information on neglected viewpoints, or discuss the issue on the
917:
907:
775:
737:
633:
628:
393:
342:
316:
276:
902:
780:
693:
645:
640:
608:
370:
366:
817:
757:
683:
331:
Prevent unwanted network traffic from locally installed applications.
272:
521:
311:
Allows the user to control which programs can and cannot access the
794:
593:
15:
325:
Monitor applications that are listening for incoming connections.
703:
688:
525:
377:
A firewall can't notify, if it has been incorrectly configured.
722:
328:
Monitor and regulate all incoming and outgoing
Internet users.
165:
63:
22:
504:– explanation of design, and discussion of susceptibility on
348:
Blocks and prevents hacking attempt or attack from hackers.
338:
with which an application is attempting to communicate.
190:
939:
916:
835:
826:
793:
768:
730:
721:
669:
601:
592:
94:. Unsourced material may be challenged and removed.
357:Firewalls help protecting internal network from
255:A personal firewall differs from a conventional
858:Microsoft Forefront Threat Management Gateway
537:
361:, However firewall do have some limitations.
8:
57:Learn how and when to remove these messages
832:
727:
598:
544:
530:
522:
334:Provide information about the destination
498:Software Firewalls: Made of Straw? Part 1
220:Learn how and when to remove this message
154:Learn how and when to remove this message
974:List of router or firewall distributions
472:. Brighthub. 2010-12-14. Archived from
450:
365:If the system has been compromised by
7:
92:adding citations to reliable sources
409:In the mid 1990s, as a part of the
304:Common personal firewall features:
459:Personal Firewall – Make IT Secure
275:computer may be used on a trusted
14:
38:This article has multiple issues.
508:computers to circumvention by a
170:
68:
27:
516:Software Firewall Test Rankings
79:needs additional citations for
46:or discuss these issues on the
1:
888:Trend Micro Internet Security
853:McAfee Personal Firewall Plus
883:Symantec Endpoint Protection
569:Context-based access control
848:Kaspersky Internet Security
248:. Typically it works as an
1011:
250:application layer firewall
964:
559:
185:toward certain viewpoints
926:Comodo Internet Security
873:Norton Personal Firewall
868:Norton Internet Security
510:Layered Service Provider
385:Virtual Private Networks
969:Comparison of firewalls
429:Comparison of firewalls
661:Uncomplicated Firewall
470:"Firewall Limitations"
20:
843:Check Point Integrity
19:
898:Windows Live OneCare
878:Outpost Firewall Pro
564:Application firewall
411:information security
88:improve this article
294:intrusion detection
191:improve the article
103:"Personal firewall"
424:Antivirus software
234:personal firewall
21:
995:Firewall software
982:
981:
960:
959:
789:
788:
717:
716:
579:Stateful firewall
574:Personal firewall
553:Firewall software
434:Computer security
398:security software
230:
229:
222:
212:
211:
164:
163:
156:
138:
61:
1002:
893:Windows Firewall
833:
728:
599:
584:Virtual firewall
546:
539:
532:
523:
518:, Matousec, 2014
485:
484:
482:
481:
466:
460:
455:
439:Network security
225:
218:
207:
204:
198:
174:
173:
166:
159:
152:
148:
145:
139:
137:
96:
72:
64:
53:
31:
30:
23:
1010:
1009:
1005:
1004:
1003:
1001:
1000:
999:
985:
984:
983:
978:
956:
935:
912:
822:
818:VirusBarrier X6
785:
764:
713:
679:Endian Firewall
665:
588:
555:
550:
494:
489:
488:
479:
477:
468:
467:
463:
456:
452:
447:
420:
407:
355:
302:
246:security policy
240:which controls
226:
215:
214:
213:
208:
202:
199:
188:
175:
171:
160:
149:
143:
140:
97:
95:
85:
73:
32:
28:
12:
11:
5:
1008:
1006:
998:
997:
987:
986:
980:
979:
977:
976:
971:
965:
962:
961:
958:
957:
955:
954:
949:
943:
941:
937:
936:
934:
933:
928:
922:
920:
914:
913:
911:
910:
905:
900:
895:
890:
885:
880:
875:
870:
865:
860:
855:
850:
845:
839:
837:
830:
824:
823:
821:
820:
815:
810:
805:
799:
797:
791:
790:
787:
786:
784:
783:
778:
772:
770:
766:
765:
763:
762:
761:
760:
750:
745:
740:
734:
732:
725:
719:
718:
715:
714:
712:
711:
706:
701:
696:
691:
686:
681:
675:
673:
667:
666:
664:
663:
658:
653:
648:
643:
638:
637:
636:
631:
621:
616:
611:
605:
603:
596:
590:
589:
587:
586:
581:
576:
571:
566:
560:
557:
556:
551:
549:
548:
541:
534:
526:
520:
519:
513:
493:
492:External links
490:
487:
486:
461:
449:
448:
446:
443:
442:
441:
436:
431:
426:
419:
416:
406:
403:
402:
401:
391:
388:
383:Firewalls and
381:
378:
375:
354:
351:
350:
349:
346:
339:
332:
329:
326:
323:
320:
309:
301:
298:
282:Wi-Fi hotspots
228:
227:
210:
209:
178:
176:
169:
162:
161:
76:
74:
67:
62:
36:
35:
33:
26:
13:
10:
9:
6:
4:
3:
2:
1007:
996:
993:
992:
990:
975:
972:
970:
967:
966:
963:
953:
950:
948:
945:
944:
942:
938:
932:
929:
927:
924:
923:
921:
919:
915:
909:
906:
904:
901:
899:
896:
894:
891:
889:
886:
884:
881:
879:
876:
874:
871:
869:
866:
864:
861:
859:
856:
854:
851:
849:
846:
844:
841:
840:
838:
834:
831:
829:
825:
819:
816:
814:
811:
809:
808:NetBarrier X4
806:
804:
803:Little Snitch
801:
800:
798:
796:
792:
782:
779:
777:
774:
773:
771:
767:
759:
756:
755:
754:
751:
749:
746:
744:
741:
739:
736:
735:
733:
729:
726:
724:
720:
710:
707:
705:
702:
700:
697:
695:
692:
690:
687:
685:
682:
680:
677:
676:
674:
672:
668:
662:
659:
657:
654:
652:
649:
647:
644:
642:
639:
635:
632:
630:
627:
626:
625:
622:
620:
617:
615:
612:
610:
607:
606:
604:
600:
597:
595:
591:
585:
582:
580:
577:
575:
572:
570:
567:
565:
562:
561:
558:
554:
547:
542:
540:
535:
533:
528:
527:
524:
517:
514:
511:
507:
503:
499:
496:
495:
491:
476:on 2014-08-14
475:
471:
465:
462:
458:
454:
451:
444:
440:
437:
435:
432:
430:
427:
425:
422:
421:
417:
415:
412:
404:
399:
395:
392:
389:
386:
382:
379:
376:
372:
368:
364:
363:
362:
360:
352:
347:
344:
340:
337:
333:
330:
327:
324:
321:
318:
314:
313:local network
310:
307:
306:
305:
299:
297:
295:
290:
285:
283:
278:
274:
269:
267:
263:
258:
253:
251:
247:
243:
239:
235:
224:
221:
206:
196:
192:
186:
184:
179:This article
177:
168:
167:
158:
155:
147:
144:November 2008
136:
133:
129:
126:
122:
119:
115:
112:
108:
105: –
104:
100:
99:Find sources:
93:
89:
83:
82:
77:This article
75:
71:
66:
65:
60:
58:
51:
50:
45:
44:
39:
34:
25:
24:
18:
952:PeerGuardian
813:PeerGuardian
573:
478:. Retrieved
474:the original
464:
453:
408:
356:
303:
286:
270:
266:proxy server
254:
233:
231:
216:
200:
180:
150:
141:
131:
124:
117:
110:
98:
86:Please help
81:verification
78:
54:
47:
41:
40:Please help
37:
940:Open-source
614:Firestarter
353:Limitations
238:application
863:Norton 360
836:Commercial
743:ipfirewall
699:SmoothWall
480:2014-03-28
445:References
203:April 2009
183:unbalanced
114:newspapers
43:improve it
947:PeerBlock
931:ZoneAlarm
709:Zeroshell
651:Shorewall
624:Netfilter
619:firewalld
195:talk page
49:talk page
989:Category
918:Freemium
908:WinRoute
776:OPNsense
738:IPFilter
634:nftables
629:iptables
418:See also
394:Software
343:computer
317:Internet
300:Features
289:programs
277:intranet
257:firewall
903:WinGate
828:Windows
781:pfSense
769:Distros
694:OpenWrt
671:Distros
646:Privoxy
641:MoBlock
609:FireHOL
506:Windows
405:History
374:manner.
371:spyware
367:malware
359:hackers
315:and/or
242:network
189:Please
181:may be
128:scholar
758:pfsync
684:IPFire
502:Part 2
336:server
273:laptop
262:router
236:is an
130:
123:
116:
109:
101:
795:macOS
656:Squid
594:Linux
135:JSTOR
121:books
731:Apps
704:VyOS
689:LEDE
602:Apps
500:and
107:news
748:NPF
723:BSD
264:or
90:by
991::
753:PF
369:,
252:.
232:A
52:.
545:e
538:t
531:v
512:.
483:.
345:.
223:)
217:(
205:)
201:(
197:.
187:.
157:)
151:(
146:)
142:(
132:·
125:·
118:·
111:·
84:.
59:)
55:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.