464:
201:
512:
37:
112:
816:
346:
623:(SDLC). The SDLC typically involves five phases: initiation, development or acquisition, implementation, operation or maintenance, and disposal. Risk management activities remain consistent throughout these phases, ensuring that potential risks are identified, assessed, and mitigated during each stage.
524:
Risk mitigation involves prioritizing and implementing risk-reducing measures recommended during risk assessment. Since eliminating all risk is impractical, organizations must apply the most cost-effective controls to reduce risk to an acceptable level while minimizing the impact on other operations.
353:
Risk assessment, a critical component of IT risk management, is performed at specific points in time (e.g., annually or on-demand) and provides a snapshot of assessed risks. It forms the foundation for ongoing risk management, which includes analysis, planning, implementation, control, and monitoring
308:
framework is context establishment. This step involves gathering relevant information about the organization and defining the criteria, scope, and boundaries of the risk management activities. This includes complying with legal requirements, ensuring due diligence, and supporting the establishment of
559:
Risk communication is a continuous, bidirectional process that ensures a common understanding of risk among all stakeholders. Effective communication influences decision-making and promotes a culture of risk awareness across the organization. One method to achieve this is the Risk
Reduction Overview
706:
Incorporating security into the SDLC is essential to prevent costly vulnerabilities from emerging later in the system’s life. Early integration of security measures during the initiation and development phases can significantly reduce the cost of mitigating security vulnerabilities. It also enables
739:
Risk management as a methodology has been criticized for its subjectivity, particularly in assessing the value of assets and the likelihood and impact of threats. The probabilistic models often used may oversimplify complex risks. Despite these criticisms, risk management remains an essential tool
128:
The total process to identify, control, and minimize the impact of uncertain events. The objective of the risk management program is to reduce risk and obtain and maintain DAA approval. The process facilitates the management of security risks by each level of management throughout the system life
507:
In this step, the results from the risk analysis are compared against the organization's risk acceptance criteria. The risk list is prioritized, and recommendations are made for risk treatment. Risks that are too costly to mitigate may be accepted or transferred (e.g., through
174:
The total process of identifying, controlling, and eliminating or minimizing uncertain events that may affect system resources. lt includes risk analysis, cost benefit analysis, selection, implementation and test, security evaluation of safeguards, and overall security
459:
that may affect the organization. Additionally, it involves identifying business processes and existing or planned security measures. The result of this step is a list of risks, threats, and potential consequences related to the assets and business processes.
336:
Establishing the organization’s mission, values, structure, strategy, locations, and cultural environment is crucial, along with documenting constraints such as budgetary, cultural, political, and technical factors that will guide the risk management process.
730:
By incorporating these practices, organizations can ensure that their IT systems are secure from the outset, reducing the likelihood of vulnerabilities and costly security incidents later in the system's life cycle.
568:
Risk management is an ongoing process that requires regular monitoring and review to ensure that implemented security measures remain effective as business conditions, threats, and vulnerabilities change. Regular
357:
Risk assessments may be iterative, beginning with high-level evaluations to identify major risks, followed by more detailed analysis in subsequent iterations. The following steps are typically involved:
138:
An element of managerial science concerned with the identification, measurement, control, and minimization of uncertain events. An effective risk management program encompasses the following four phases:
185:
While specific methods may vary, risk management processes generally include establishing context, conducting risk assessments, and managing risks. Risk management methodologies from standards such as
611:(SDLC) to ensure that risks are addressed throughout the life cycle of IT systems. Each phase of the SDLC benefits from specific risk management activities, from initial planning to system disposal.
120:
70:(ISMS). The continuous update and maintenance of an ISMS is in turn part of an organisation's systematic approach for identifying, assessing, and managing information security risks.
939:
604:
are common methods for verifying the effectiveness of security controls. Regular reviews and reauthorization of systems are necessary when significant changes are made.
909:
596:
To ensure the effectiveness of security measures, controls should be continuously tested and validated, including both technical systems and procedural controls.
491:
Qualitative risk assessment – Descriptive methods, such as interviews and expert judgment, which are faster and less data-intensive but less precise.
67:
310:
545:
Residual risks, those remaining after treatment, are estimated to ensure adequate protection, and further measures may be taken if necessary.
962:
893:
570:
79:
841:
106:
allows IT managers to balance the operational and economic costs of protective measures with mission goals by securing IT systems and data.
768:
197:, and Risk IT emphasize a structured approach to these processes. The following table compares key processes across leading frameworks:
726:
Technical vulnerability management: Monitoring for vulnerabilities and applying timely patches to protect against emerging threats.
662:
Risk assessments help guide security decisions during the system's development, influencing architecture and design trade-offs.
831:
588:
and engaging in professional development activities are important for maintaining state-of-the-art risk management practices.
96:, if any, to take in reducing risk to an acceptable level, based on the value of the information resource to the organization.
620:
608:
916:
821:
684:
Continuous risk assessments are performed whenever significant changes occur or at regular intervals for reauthorization.
169:, cost benefit analysis, safeguard selection, security test and evaluation, safeguard implementation, and systems review.
1253:
714:
Security requirements for information systems: Security needs are incorporated into the system's design from the start.
1243:
1054:
ISO/IEC, "Information technology -- Security techniques-Information security risk management" ISO/IEC FIDIS 27005:2008
166:
130:
651:
Identified risks support the development of system requirements, including security needs and concept of operations.
778:
720:
Cryptographic controls: Ensuring that data is encrypted both at rest and in transit to prevent unauthorized access.
485:
63:
723:
Security of system files: Implementing version control, access restrictions, and thorough testing of system files.
165:
The total process of identifying, measuring, and minimizing uncertain events affecting AIS resources. It includes
1188:
Gulick, Jessica; Fahlsing, Jim; Rossman, Hart; Scholl, Matthew; Stine, Kevin; Kissel, Richard (16 October 2008).
1096:
Gulick, Jessica; Fahlsing, Jim; Rossman, Hart; Scholl, Matthew; Stine, Kevin; Kissel, Richard (16 October 2008).
856:
456:
371:
93:
85:
313:(ISMS). The scope can encompass incident reporting plans, business continuity plans, or product certifications.
695:
Risks are managed to ensure secure disposal, including data sanitization and system migration where necessary.
601:
388:
Risk evaluation – Comparing risk levels to predefined acceptance criteria and prioritizing risks for treatment.
476:
Risk estimation assesses the likelihood and consequences of the identified risks. Two common approaches are:
707:
the reuse of established security strategies and tools, resulting in improved security and cost efficiency.
326:
1248:
481:
52:
1143:
984:
92:
to the information resources used by an organization in achieving business objectives, and deciding what
1207:
1161:
1115:
1002:
673:
Risk management ensures that security requirements are met and assessed before system operations begin.
378:
597:
1032:
797:
382:
194:
1189:
1097:
717:
Correct processing in applications: Protecting against errors and ensuring the integrity of data.
316:
The key criteria include risk evaluation, risk acceptance, and impact assessment, influenced by:
30:
463:
377:
Risk estimation – Evaluating the likelihood and impact of identified risks, often using either
59:. Various methodologies exist to manage IT risks, each involving specific processes and steps.
958:
889:
851:
748:
Various methods support the IT risk management process. Some of the most widely used include:
495:
For both methods, risk values are calculated for each asset and the output is documented in a
452:
367:
200:
89:
480:
Quantitative risk assessment – A mathematical calculation based on security metrics, such as
1193:
1147:
1101:
988:
846:
581:
541:
Risk transference – Using other options, such as purchasing insurance, to transfer the risk.
511:
1220:
1174:
1128:
1015:
577:
554:
103:
48:
36:
29:"Information risk management" redirects here. For the risk of inaccurate information, see
560:
method, which presents risks, measures, and residual risks in a comprehensible manner.
1237:
836:
756:
585:
496:
305:
186:
573:
and reviews are essential to validate security controls and assess residual risks.
111:
17:
811:
765:– Developed by the French government, compliant with major security standards.
143:
Risk assessment, as derived from an evaluation of threats and vulnerabilities.
1198:
1106:
393:
1152:
993:
815:
82:
Review Manual 2006 by ISACA provides this definition of risk management: "
532:
Risk assumption – Accepting the potential risk and continuing operations.
538:
Risk limitation – Implementing controls to minimize the impact of risks.
535:
Risk avoidance – Eliminating the risk by avoiding risk-prone activities.
345:
791:
771:(FAIR) – A rigorous approach to defining and analyzing IT risk factors.
190:
56:
416:
RE2 Analyse risk, including risk scenario development and peer review
796:
Various standards provide guidance for IT risk management, including
774:
363:
710:
The following security considerations are integrated into the SDLC:
204:
ENISA: The Risk
Management Process, according to ISO Standard 13335
762:
752:
510:
451:
This process identifies the assets (both primary and supporting),
344:
237:
RG and RE Domains, including IT risk tolerance and risk practices
199:
110:
35:
1142:
Feringa, Alexis; Goguen, Alice; Stoneburner, Gary (1 July 2002).
983:
Feringa, Alexis; Goguen, Alice; Stoneburner, Gary (1 July 2002).
957:. Information Systems Audit and Control Association. p. 85.
362:
Risk identification – Recognizing potential loss sources such as
62:
An IT risk management system (ITRMS) is a component of a broader
801:
1190:"Security Considerations in the System Development Life Cycle"
1098:"Security Considerations in the System Development Life Cycle"
1078:
1067:. Risk Management: Auerbach Publications. 2007. p. 1065.
323:
The strategic value of information processes for the business
467:
OWASP: relationship between threat agent and business impact
121:
National
Information Assurance Training and Education Center
888:. Morgan Kaufmann Publications. Elsevier Inc. p. 605.
1144:"Risk Management Guide for Information Technology Systems"
1027:
1025:
985:"Risk Management Guide for Information Technology Systems"
884:
Katsicas, Sokratis K. (2009). "35". In Vacca, John (ed.).
940:
Enisa Risk management, Risk assessment inventory, page 46
396:
framework divides the process into the following stages:
952:
781:, it is widely used for risk-based security assessments.
129:
cycle. The approval process consists of three elements:
619:
Effective risk management is fully integrated into the
332:
Negative consequences for the organization's reputation
265:
Selection of risk response options and treatment plans
755:– Developed by the British government, compliant with
910:"ISACA THE RISK IT FRAMEWORK (registration required)"
66:(ERM) system. ITRMS are also integrated into broader
792:
IT risk § Standards organizations and standards
607:Risk management should also be integrated into the
580:, must be addressed through continuous monitoring,
528:The following strategies are typically considered:
515:
Risk assessment according NIST SP 800-30 Figure 3-1
615:Integration into the system development life cycle
584:, and updating of controls. Benchmarking against
648:Defines the need for an IT system and its scope
84:Risk management is the process of identifying
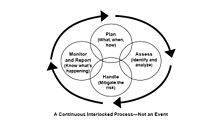
349:ENISA: Risk assessment inside risk management
8:
735:Critique of risk management as a methodology
628:Integration of Risk Management into the SDLC
293:Independent assurance of IT risk management
123:defines risk management in the IT field as:
1050:
1048:
1046:
670:System is configured, tested, and verified
251:Processes for risk analysis and evaluation
886:Computer and Information Security Handbook
1197:
1151:
1105:
992:
978:
976:
974:
659:System design, purchase, or construction
555:Risk management § Risk communication
625:
462:
398:
207:
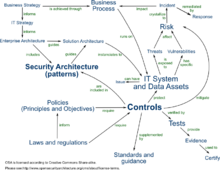
115:Relationships between IT security entity
879:
877:
875:
873:
871:
867:
68:information security management systems
1216:
1205:
1170:
1159:
1124:
1113:
1011:
1000:
681:The system is operational and updated
400:Risk assessment constituent processes
311:information security management system
209:Risk management constituent processes
80:Certified Information Systems Auditor
7:
842:Vulnerability assessment (computing)
769:Factor Analysis of Information Risk
424:Included in RE2.2 Estimate IT risk
1065:Official (ISC)2 Guide to CISSP CBK
25:
320:Legal and regulatory requirements
814:
832:Information security management
621:Systems Development Life Cycle
609:Systems Development Life Cycle
133:, certification, and approval.
1:
822:Business and economics portal
692:The system is decommissioned
576:New vulnerabilities, such as
287:Ongoing management activities
592:IT evaluation and assessment
656:Development or Acquisition
640:Risk Management Activities
1270:
1202:– via csrc.nist.gov.
1156:– via csrc.nist.gov.
1110:– via csrc.nist.gov.
997:– via csrc.nist.gov.
789:
779:Carnegie Mellon University
564:Risk monitoring and review
552:
486:Annualized Loss Expectancy
64:enterprise risk management
28:
1079:"Risk Reduction Overview"
857:Vulnerability (computing)
678:Operation or Maintenance
602:vulnerability assessments
374:, and business processes.
1199:10.6028/NIST.SP.800-64r2
1107:10.6028/NIST.SP.800-64r2
101:According to the NIST, "
40:Risk management elements
954:CISA Review Manual 2006
744:Risk management methods
740:for managing IT risks.
440:RE2.2 Estimate IT risk
432:RE2.2 Estimate IT risk
153:Control implementation.
1215:Cite journal requires
1169:Cite journal requires
1153:10.6028/NIST.SP.800-30
1123:Cite journal requires
1037:www.niatec.iri.isu.edu
1010:Cite journal requires
994:10.6028/NIST.SP.800-30
637:Phase Characteristics
516:
482:Single loss expectancy
468:
354:of security measures.
350:
304:The first step in the
231:Organizational context
205:
116:
53:information technology
47:is the application of
41:
514:
466:
348:
300:Context establishment
279:RG3.4 Accept IT risk
228:Context establishment
203:
158:Effectiveness review.
114:
39:
798:ISO/IEC 27000-series
759:and other standards.
702:Security in the SDLC
421:Risk identification
148:Management decision.
1254:Security compliance
1083:rro.sourceforge.net
1033:"Glossary of Terms"
630:
447:Risk identification
401:
210:
55:in order to manage
1244:IT risk management
626:
549:Risk communication
517:
469:
399:
351:
214:ISO/IEC 27005:2008
208:
206:
117:
45:IT risk management
42:
31:Assurance services
964:978-1-933284-15-6
895:978-0-12-374354-1
699:
698:
598:Penetration tests
444:
443:
297:
296:
16:(Redirected from
1261:
1225:
1224:
1218:
1213:
1211:
1203:
1201:
1185:
1179:
1178:
1172:
1167:
1165:
1157:
1155:
1139:
1133:
1132:
1126:
1121:
1119:
1111:
1109:
1093:
1087:
1086:
1075:
1069:
1068:
1061:
1055:
1052:
1041:
1040:
1029:
1020:
1019:
1013:
1008:
1006:
998:
996:
980:
969:
968:
948:
942:
937:
931:
930:
928:
927:
921:
915:. Archived from
914:
906:
900:
899:
881:
847:Penetration test
824:
819:
818:
631:
582:patch management
578:zero-day attacks
437:Risk evaluation
429:Risk estimation
402:
211:
21:
1269:
1268:
1264:
1263:
1262:
1260:
1259:
1258:
1234:
1233:
1228:
1214:
1204:
1187:
1186:
1182:
1168:
1158:
1141:
1140:
1136:
1122:
1112:
1095:
1094:
1090:
1077:
1076:
1072:
1063:
1062:
1058:
1053:
1044:
1031:
1030:
1023:
1009:
999:
982:
981:
972:
965:
950:
949:
945:
938:
934:
925:
923:
919:
912:
908:
907:
903:
896:
883:
882:
869:
865:
820:
813:
810:
794:
788:
777:– Developed by
746:
737:
704:
667:Implementation
617:
594:
571:security audits
566:
557:
551:
522:
520:Risk mitigation
505:
503:Risk evaluation
474:
472:Risk estimation
457:vulnerabilities
449:
372:vulnerabilities
343:
341:Risk assessment
302:
284:Risk monitoring
270:Risk acceptance
245:Risk assessment
242:Risk assessment
183:
104:Risk management
94:countermeasures
86:vulnerabilities
76:
49:risk management
34:
23:
22:
18:Risk acceptance
15:
12:
11:
5:
1267:
1265:
1257:
1256:
1251:
1246:
1236:
1235:
1232:
1231:
1227:
1226:
1217:|journal=
1180:
1171:|journal=
1134:
1125:|journal=
1088:
1070:
1056:
1042:
1021:
1012:|journal=
970:
963:
951:ISACA (2006).
943:
932:
901:
894:
866:
864:
861:
860:
859:
854:
849:
844:
839:
834:
829:
826:
825:
809:
806:
790:Main article:
787:
784:
783:
782:
772:
766:
760:
745:
742:
736:
733:
728:
727:
724:
721:
718:
715:
703:
700:
697:
696:
693:
690:
686:
685:
682:
679:
675:
674:
671:
668:
664:
663:
660:
657:
653:
652:
649:
646:
642:
641:
638:
635:
616:
613:
593:
590:
586:best practices
565:
562:
553:Main article:
550:
547:
543:
542:
539:
536:
533:
521:
518:
504:
501:
493:
492:
489:
473:
470:
448:
445:
442:
441:
438:
434:
433:
430:
426:
425:
422:
418:
417:
414:
413:Risk analysis
410:
409:
406:
390:
389:
386:
375:
342:
339:
334:
333:
330:
324:
321:
301:
298:
295:
294:
291:
288:
285:
281:
280:
277:
274:
271:
267:
266:
263:
260:
259:Risk treatment
257:
256:Risk treatment
253:
252:
249:
246:
243:
239:
238:
235:
232:
229:
225:
224:
221:
220:NIST SP 800-39
218:
217:BS 7799-3:2006
215:
195:NIST SP 800-39
182:
179:
178:
177:
171:
162:
161:
160:
155:
150:
145:
135:
75:
72:
24:
14:
13:
10:
9:
6:
4:
3:
2:
1266:
1255:
1252:
1250:
1249:Data security
1247:
1245:
1242:
1241:
1239:
1230:
1229:
1222:
1209:
1200:
1195:
1191:
1184:
1181:
1176:
1163:
1154:
1149:
1145:
1138:
1135:
1130:
1117:
1108:
1103:
1099:
1092:
1089:
1084:
1080:
1074:
1071:
1066:
1060:
1057:
1051:
1049:
1047:
1043:
1038:
1034:
1028:
1026:
1022:
1017:
1004:
995:
990:
986:
979:
977:
975:
971:
966:
960:
956:
955:
947:
944:
941:
936:
933:
922:on 2010-07-05
918:
911:
905:
902:
897:
891:
887:
880:
878:
876:
874:
872:
868:
862:
858:
855:
853:
850:
848:
845:
843:
840:
838:
837:ISO/IEC 27001
835:
833:
830:
828:
827:
823:
817:
812:
807:
805:
803:
799:
793:
785:
780:
776:
773:
770:
767:
764:
761:
758:
757:ISO/IEC 17799
754:
751:
750:
749:
743:
741:
734:
732:
725:
722:
719:
716:
713:
712:
711:
708:
701:
694:
691:
688:
687:
683:
680:
677:
676:
672:
669:
666:
665:
661:
658:
655:
654:
650:
647:
644:
643:
639:
636:
633:
632:
629:
624:
622:
614:
612:
610:
605:
603:
599:
591:
589:
587:
583:
579:
574:
572:
563:
561:
556:
548:
546:
540:
537:
534:
531:
530:
529:
526:
519:
513:
509:
502:
500:
498:
497:risk register
490:
487:
483:
479:
478:
477:
471:
465:
461:
458:
454:
446:
439:
436:
435:
431:
428:
427:
423:
420:
419:
415:
412:
411:
407:
404:
403:
397:
395:
387:
384:
380:
376:
373:
369:
365:
361:
360:
359:
355:
347:
340:
338:
331:
328:
325:
322:
319:
318:
317:
314:
312:
307:
306:ISO/IEC 27005
299:
292:
289:
286:
283:
282:
278:
276:Not specified
275:
273:Not specified
272:
269:
268:
264:
261:
258:
255:
254:
250:
247:
244:
241:
240:
236:
233:
230:
227:
226:
222:
219:
216:
213:
212:
202:
198:
196:
192:
188:
187:ISO/IEC 27005
180:
176:
172:
170:
168:
167:risk analysis
163:
159:
156:
154:
151:
149:
146:
144:
141:
140:
139:
136:
134:
132:
131:risk analysis
126:
125:
124:
122:
119:The American
113:
109:
107:
105:
99:
97:
95:
91:
87:
81:
73:
71:
69:
65:
60:
58:
54:
50:
46:
38:
32:
27:
19:
1208:cite journal
1183:
1162:cite journal
1137:
1116:cite journal
1091:
1082:
1073:
1064:
1059:
1036:
1003:cite journal
953:
946:
935:
924:. Retrieved
917:the original
904:
885:
795:
747:
738:
729:
709:
705:
627:
618:
606:
595:
575:
567:
558:
544:
527:
523:
506:
494:
475:
450:
391:
379:quantitative
356:
352:
335:
329:expectations
315:
303:
184:
173:
164:
157:
152:
147:
142:
137:
127:
118:
102:
100:
83:
77:
61:
44:
43:
26:
804:SP 800-30.
645:Initiation
634:SDLC Phase
508:insurance).
383:qualitative
327:Stakeholder
181:Methodology
74:Definitions
51:methods to
1238:Categories
926:2010-12-14
863:References
484:(SLE) and
405:ISO 27005
786:Standards
689:Disposal
394:ISO 27005
1192:. NIST.
1146:. NIST.
808:See also
408:Risk IT
385:methods.
223:Risk IT
453:threats
368:threats
290:Monitor
262:Respond
191:BS 7799
175:review.
90:threats
57:IT risk
961:
892:
852:Threat
775:Octave
488:(ALE).
455:, and
364:assets
248:Assess
920:(PDF)
913:(PDF)
763:EBIOS
753:CRAMM
234:Frame
1221:help
1175:help
1129:help
1016:help
959:ISBN
890:ISBN
802:NIST
800:and
600:and
392:The
88:and
78:The
1194:doi
1148:doi
1102:doi
989:doi
381:or
309:an
1240::
1212::
1210:}}
1206:{{
1166::
1164:}}
1160:{{
1120::
1118:}}
1114:{{
1100:.
1081:.
1045:^
1035:.
1024:^
1007::
1005:}}
1001:{{
987:.
973:^
870:^
499:.
370:,
366:,
193:,
189:,
108:"
98:"
1223:)
1219:(
1196::
1177:)
1173:(
1150::
1131:)
1127:(
1104::
1085:.
1039:.
1018:)
1014:(
991::
967:.
929:.
898:.
33:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.