306:, although these vulnerabilities can be compensated for by doubling key length. For example, a 128 bit AES cipher would not be secure against such an attack as it would reduce the time required to test all possible iterations from over 10 quintillion years to about six months. By contrast, it would still take a quantum computer the same amount of time to decode a 256 bit AES cipher as it would a conventional computer to decode a 128 bit AES cipher. For this reason, AES-256 is believed to be "quantum resistant".
31:
3066:
383:
286:
can greatly reduce the chances of a successful attack. It is also possible to increase the key length or the rounds in the encryption process to better protect against attack. This, however, tends to increase the processing power and decrease the speed at which the process runs due to the amount of
331:
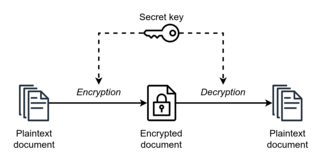
Symmetric-key algorithms require both the sender and the recipient of a message to have the same secret key. All early cryptographic systems required either the sender or the recipient to somehow receive a copy of that secret key over a physically secure channel.
77:
they have a smaller key size, which means less storage space and faster transmission. Due to this, asymmetric-key encryption is often used to exchange the secret key for symmetric-key encryption.
335:
Nearly all modern cryptographic systems still use symmetric-key algorithms internally to encrypt the bulk of the messages, but they eliminate the need for a physically secure channel by using
458:
on each typed-in letter. Instead of designing two kinds of machines, one for encrypting and one for decrypting, all the machines can be identical and can be set up (keyed) the same way.
3046:
2876:
358:
65:
between two or more parties that can be used to maintain a private information link. The requirement that both parties have access to the secret key is one of the main drawbacks of
2714:
2332:
2271:
1352:
210:
is added to a ciphertext to ensure that changes to the ciphertext will be noted by the receiver. Message authentication codes can be constructed from an
2577:
73:(also known as asymmetric-key encryption). However, symmetric-key encryption algorithms are usually better for bulk encryption. With exception of the
400:
315:
2098:
1454:
188:
2088:
1582:
1145:
1989:
2251:
2225:
2093:
447:, one could enter the ciphertext into the same place in the system to get the plaintext. A reciprocal cipher is also sometimes referred as
1009:
115:
Block ciphers take a number of bits and encrypt them in a single unit, padding the plaintext to achieve a multiple of the block size. The
2066:
365:
is disastrous and has led to cryptanalytic breaks in the past. Therefore, it is essential that an implementation use a source of high
1169:. January 1996 Dr. Dobb's Journal. quote: "it is vital that the secret keys be generated from an unpredictable random-number source."
3094:
2707:
2639:
2325:
981:
721:
670:
643:
614:
422:
61:. The keys may be identical, or there may be a simple transformation to go between the two keys. The keys, in practice, represent a
361:
are nearly always used to generate the symmetric cipher session keys. However, lack of randomness in those generators or in their
258:. Feistel's construction makes it possible to build invertible functions from other functions that are themselves not invertible.
2235:
1345:
602:
336:
2114:
2925:
2856:
2634:
2624:
2292:
1122:
Weissbaum, François; Lugrin, Thomas (2023), Mulder, Valentin; Mermoud, Alain; Lenders, Vincent; Tellenbach, Bernhard (eds.),
948:
404:
686:
1073:
2700:
2318:
1382:
366:
237:
226:
140:
116:
3041:
2996:
2799:
2178:
1338:
577:
481:
207:
2920:
2608:
2467:
2195:
2105:
2083:
1396:
275:
3036:
2200:
2056:
2009:
1484:
1098:
291:
3026:
3016:
2871:
2603:
2266:
2148:
2023:
1392:
455:
172:
3021:
2804:
2764:
2757:
2742:
2737:
2205:
1994:
1365:
1231:
573:
393:
340:
271:
200:
2809:
2752:
2297:
2173:
2168:
2120:
267:
1969:
904:
533:
343:
to securely come to agreement on a fresh new secret key for each session/conversation (forward secrecy).
3069:
2915:
2861:
2675:
2649:
2502:
2287:
2110:
1547:
1181:"When Good Randomness Goes Bad: Virtual Machine Reset Vulnerabilities and Hedging Deployed Cryptography"
1045:
362:
70:
299:
924:
206:
Encrypting a message does not guarantee that it will remain unchanged while encrypted. Hence, often a
3031:
2955:
2670:
2190:
2073:
1999:
1682:
1662:
1180:
885:
822:
283:
279:
2784:
2598:
2153:
2130:
1449:
1030:
1005:
105:
572:
encryption. Use of the last and first terms can create ambiguity with similar terminology used in
2900:
2884:
2826:
2665:
2138:
2046:
1758:
1687:
1657:
1602:
854:
727:
303:
50:
1192:
Random number generators (RNGs) are consistently a weak link in the secure use of cryptography.
2960:
2950:
2816:
1858:
1557:
1517:
1512:
1479:
1439:
1387:
1141:
987:
977:
881:
846:
838:
791:
773:
717:
666:
660:
639:
610:
510:
326:
295:
180:
156:
144:
30:
631:
2895:
2747:
2447:
2230:
2125:
2004:
1863:
1743:
1712:
1406:
1204:
1131:
873:
830:
781:
763:
709:
136:
1166:
2567:
2562:
2537:
2411:
2077:
2061:
2050:
1984:
1943:
1908:
1838:
1818:
1692:
1572:
1567:
1522:
1058:
470:
222:
109:
17:
889:
826:
701:
2970:
2890:
2846:
2789:
2774:
2629:
2482:
2437:
2215:
2163:
1974:
1959:
1898:
1893:
1778:
1527:
786:
751:
750:
Alvarez, Rafael; Caballero-Gil, Cándido; Santonja, Juan; Zamora, Antonio (2017-06-27).
713:
529:
475:
352:
298:
would exponentially increase the speed at which these ciphers can be decoded; notably,
249:
3088:
3051:
3006:
2965:
2945:
2836:
2794:
2769:
2582:
2542:
2522:
2512:
2477:
2341:
2210:
2158:
2037:
2019:
1808:
1783:
1773:
1597:
1587:
1434:
1260:; encipherment and decipherment are identically the same thing." -- Helen F. Gaines.
874:
517:
490:
255:
233:
86:
62:
731:
3001:
2841:
2831:
2821:
2779:
2723:
2143:
1964:
1928:
1793:
1672:
1627:
1459:
1411:
1361:
858:
525:
440:
90:
74:
46:
1218:
603:"Applying Encryption Algorithms for Data Security in Cloud Storage, Kartit, et al"
100:), or letters (in substitution ciphers) of a message one at a time. An example is
1300:
1287:
1261:
34:
Symmetric-key encryption: the same key is used for both encryption and decryption
2980:
2517:
2375:
1753:
1748:
1632:
1136:
1034:
382:
2940:
2910:
2905:
2866:
2644:
2185:
1903:
1843:
1727:
1722:
1667:
1537:
1400:
1123:
521:
505:
444:
176:
164:
58:
842:
810:
777:
290:
Most modern symmetric-key algorithms appear to be resistant to the threat of
2930:
2557:
2487:
2421:
1918:
1913:
1803:
1717:
1612:
1592:
991:
454:
Practically all mechanical cipher machines implement a reciprocal cipher, a
436:
66:
54:
42:
850:
795:
1313:
1274:
1244:
2975:
2935:
2370:
2256:
2220:
2014:
1677:
1552:
1532:
1444:
152:
101:
834:
2416:
2390:
2365:
1923:
1873:
1833:
1823:
1768:
1763:
1607:
1416:
407: in this section. Unsourced material may be challenged and removed.
215:
148:
132:
768:
2851:
2507:
2472:
2442:
2406:
2261:
1883:
1878:
1813:
1798:
1788:
1733:
1707:
1702:
1697:
1577:
1562:
465:
302:
would take the square-root of the time traditionally required for a
2552:
1979:
1938:
1888:
1868:
1853:
1642:
1622:
1542:
1507:
500:
254:
Many modern block ciphers are based on a construction proposed by
184:
160:
516:
The majority of all modern ciphers can be classified as either a
2572:
2547:
2497:
2492:
2360:
2355:
1828:
1737:
1652:
1647:
1637:
1617:
1489:
1474:
211:
120:
97:
2696:
2314:
1334:
2532:
2527:
2380:
1933:
1848:
1469:
1464:
706:
Security
Controls Evaluation, Testing, and Assessment Handbook
495:
435:
A reciprocal cipher is a cipher where, just as one enters the
376:
168:
687:"Demystifying symmetric and asymmetric methods of encryption"
108:
are well-known ciphers, but can be easily decrypted using a
976:(2nd ed.). Rockland, MA: Syngress. pp. 165–203.
636:
Introduction to cryptography: principles and applications
225:
purposes except by involving additional parties. See the
607:
Advances in
Ubiquitous Networking: Proceedings of UNet15
266:
Symmetric ciphers have historically been susceptible to
2877:
Cryptographically secure pseudorandom number generator
1262:"Cryptanalysis: A Study of Ciphers and Their Solution"
576:. Symmetric-key cryptography is to be contrasted with
1288:"Decrypted Secrets: Methods and Maxims of Cryptology"
1128:
Trends in Data
Protection and Encryption Technologies
199:
Symmetric ciphers are commonly used to achieve other
131:
Examples of popular symmetric-key algorithms include
1322:
1130:, Cham: Springer Nature Switzerland, pp. 7–10,
357:
When used with asymmetric ciphers for key transfer,
2989:
2730:
2658:
2617:
2591:
2460:
2430:
2399:
2389:
2348:
2280:
2244:
2033:
1952:
1498:
1425:
1373:
1256:"... the true Beaufort cipher. Notice that we have
487:
the Porta polyalphabetic cipher is self-reciprocal.
809:Bernstein, Daniel J.; Lange, Tanja (2017-09-14).
282:. Careful construction of the functions for each
702:"Security Component Fundamentals for Assessment"
536:with a reciprocal transformation in each round.
665:. American Mathematical Society. p. 112.
221:However, symmetric ciphers cannot be used for
2708:
2326:
1346:
1301:"Coding for Data and Computer Communications"
1217:Paul Reuvers and Marc Simons. Crypto Museum.
552:Other terms for symmetric-key encryption are
96:Stream ciphers encrypt the digits (typically
8:
1010:"Introduction to post-quantum cryptography"
972:David R. Mirza Ahmad; Ryan Russell (2002).
484:communicated with a self-reciprocal cipher.
2715:
2701:
2693:
2396:
2333:
2319:
2311:
1353:
1339:
1331:
1327:
1323:
240:for descriptions of several such methods.
1179:Ristenpart, Thomas; Yilek, Scott (2010).
1135:
903:Bellare, Mihir; Rogaway, Phillip (2005).
785:
767:
752:"Algorithms for Lightweight Key Exchange"
423:Learn how and when to remove this message
461:Examples of reciprocal ciphers include:
316:Key Management Interoperability Protocol
85:Symmetric-key encryption can use either
29:
593:
545:
123:in December 2001, uses 128-bit blocks.
1314:"US Codebreakers In The Shadow Of War"
1099:"AES-256 joins the quantum resistance"
1054:
1043:
1167:"Randomness and the Netscape Browser"
1074:"The Clock Is Ticking for Encryption"
7:
659:Mullen, Gary; Mummert, Carl (2007).
405:adding citations to reliable sources
906:Introduction to Modern Cryptography
880:. Berlin: Springer-Verlag. p.
630:Delfs, Hans; Knebl, Helmut (2007).
287:operations the system needs to do.
714:10.1016/b978-0-12-802324-2.00011-7
69:-key encryption, in comparison to
25:
520:, most of which use a reciprocal
244:Construction of symmetric ciphers
3065:
3064:
381:
232:Another application is to build
195:Use as a cryptographic primitive
1165:Ian Goldberg and David Wagner.
392:needs additional citations for
2926:Information-theoretic security
1275:"The Mechanization of Ciphers"
1245:"The Mechanization of Ciphers"
708:, Elsevier, pp. 531–627,
689:. Geeks for Geeks. 2017-09-28.
662:Finite fields and applications
601:Kartit, Zaid (February 2016).
1:
1232:"Simple Substitution Ciphers"
262:Security of symmetric ciphers
119:(AES) algorithm, approved by
2625:block ciphers in stream mode
925:"Symmetric-Key Cryptography"
238:one-way compression function
117:Advanced Encryption Standard
3042:Message authentication code
2997:Cryptographic hash function
2800:Cryptographic hash function
1137:10.1007/978-3-031-33386-6_2
1072:Wood, Lamont (2011-03-21).
811:"Post-quantum cryptography"
578:asymmetric-key cryptography
359:pseudorandom key generators
337:Diffie–Hellman key exchange
208:message authentication code
53:for both the encryption of
3111:
2921:Harvest now, decrypt later
2609:alternating step generator
1097:O'Shea, Dan (2022-04-29).
974:Hack proofing your network
876:Understanding Cryptography
700:Johnson, Leighton (2016),
632:"Symmetric-key encryption"
350:
324:
313:
276:differential cryptanalysis
247:
18:Symmetric-key cryptography
3060:
3037:Post-quantum cryptography
2692:
2310:
2236:Time/memory/data tradeoff
1330:
1326:
1017:Post-Quantum Cryptography
872:Pelzl & Paar (2010).
292:post-quantum cryptography
3095:Cryptographic algorithms
3027:Quantum key distribution
3017:Authenticated encryption
2872:Random number generation
2604:self-shrinking generator
2024:Whitening transformation
1205:"Symmetric Cryptography"
1124:"Symmetric Cryptography"
369:for its initialization.
272:chosen-plaintext attacks
236:from block ciphers. See
227:ISO/IEC 13888-2 standard
201:cryptographic primitives
39:Symmetric-key algorithms
3022:Public-key cryptography
3012:Symmetric-key algorithm
2805:Key derivation function
2765:Cryptographic primitive
2758:Authentication protocol
2743:Outline of cryptography
2738:History of cryptography
1995:Confusion and diffusion
1258:reciprocal encipherment
574:public-key cryptography
456:mathematical involution
268:known-plaintext attacks
2810:Secure Hash Algorithms
2753:Cryptographic protocol
1053:Cite journal requires
949:"ISO/IEC 13888-2:2010"
528:, most of which use a
449:self-reciprocal cipher
363:initialization vectors
203:than just encryption.
57:and the decryption of
35:
2916:End-to-end encryption
2862:Cryptojacking malware
2676:stream cipher attacks
2288:Initialization vector
1035:"Grover vs. McEliece"
480:Marie Antoinette and
71:public-key encryption
33:
3032:Quantum cryptography
2956:Trusted timestamping
2671:correlation immunity
2067:3-subset MITM attack
1683:Intel Cascade Cipher
1663:Hasty Pudding cipher
1286:Friedrich L. Bauer.
1207:. James. 2006-03-11.
401:improve this article
280:linear cryptanalysis
106:Substitution ciphers
2785:Cryptographic nonce
2599:shrinking generator
2349:Widely used ciphers
2106:Differential-linear
1230:Chris Christensen.
1188:NDSS Symposium 2010
1031:Daniel J. Bernstein
1006:Daniel J. Bernstein
890:2010uncr.book.....P
835:10.1038/nature23461
827:2017Natur.549..188B
341:public-key protocol
2901:Subliminal channel
2885:Pseudorandom noise
2827:Key (cryptography)
2666:correlation attack
2179:Differential-fault
1397:internal mechanics
1103:Fierce Electronics
929:www.cs.cornell.edu
443:system to get the
304:brute-force attack
300:Grover's algorithm
51:cryptographic keys
49:that use the same
36:
3082:
3081:
3078:
3077:
2961:Key-based routing
2951:Trapdoor function
2817:Digital signature
2688:
2687:
2684:
2683:
2456:
2455:
2306:
2305:
2293:Mode of operation
1970:Lai–Massey scheme
1147:978-3-031-33386-6
821:(7671): 188–194.
769:10.3390/s17071517
534:Lai–Massey scheme
511:Vatsyayana cipher
433:
432:
425:
373:Reciprocal cipher
327:key establishment
321:Key establishment
296:Quantum computers
16:(Redirected from
3102:
3068:
3067:
2896:Insecure channel
2748:Classical cipher
2717:
2710:
2703:
2694:
2397:
2335:
2328:
2321:
2312:
2164:Power-monitoring
2005:Avalanche effect
1713:Khufu and Khafre
1366:security summary
1355:
1348:
1341:
1332:
1328:
1324:
1317:
1310:
1304:
1297:
1291:
1284:
1278:
1271:
1265:
1254:
1248:
1241:
1235:
1228:
1222:
1215:
1209:
1208:
1201:
1195:
1194:
1185:
1176:
1170:
1163:
1157:
1156:
1155:
1154:
1139:
1119:
1113:
1112:
1110:
1109:
1094:
1088:
1087:
1085:
1084:
1069:
1063:
1062:
1056:
1051:
1049:
1041:
1039:
1027:
1021:
1020:
1014:
1002:
996:
995:
969:
963:
962:
960:
959:
945:
939:
938:
936:
935:
920:
914:
913:
911:
900:
894:
893:
879:
869:
863:
862:
806:
800:
799:
789:
771:
747:
741:
740:
739:
738:
697:
691:
690:
683:
677:
676:
656:
650:
649:
627:
621:
620:
598:
581:
550:
428:
421:
417:
414:
408:
385:
377:
21:
3110:
3109:
3105:
3104:
3103:
3101:
3100:
3099:
3085:
3084:
3083:
3074:
3056:
2985:
2726:
2721:
2680:
2654:
2613:
2587:
2452:
2426:
2385:
2344:
2339:
2302:
2276:
2245:Standardization
2240:
2169:Electromagnetic
2121:Integral/Square
2078:Piling-up lemma
2062:Biclique attack
2051:EFF DES cracker
2035:
2029:
1960:Feistel network
1948:
1573:CIPHERUNICORN-E
1568:CIPHERUNICORN-A
1500:
1494:
1427:
1421:
1375:
1369:
1359:
1321:
1320:
1311:
1307:
1299:David Salomon.
1298:
1294:
1285:
1281:
1272:
1268:
1264:. 2014. p. 121.
1255:
1251:
1242:
1238:
1229:
1225:
1216:
1212:
1203:
1202:
1198:
1183:
1178:
1177:
1173:
1164:
1160:
1152:
1150:
1148:
1121:
1120:
1116:
1107:
1105:
1096:
1095:
1091:
1082:
1080:
1071:
1070:
1066:
1052:
1042:
1037:
1029:
1028:
1024:
1012:
1004:
1003:
999:
984:
971:
970:
966:
957:
955:
947:
946:
942:
933:
931:
922:
921:
917:
909:
902:
901:
897:
871:
870:
866:
808:
807:
803:
749:
748:
744:
736:
734:
724:
699:
698:
694:
685:
684:
680:
673:
658:
657:
653:
646:
629:
628:
624:
617:
600:
599:
595:
590:
585:
584:
551:
547:
542:
524:combiner, or a
482:Axel von Fersen
471:Beaufort cipher
429:
418:
412:
409:
398:
386:
375:
355:
349:
329:
323:
318:
312:
264:
252:
246:
223:non-repudiation
197:
129:
127:Implementations
110:frequency table
83:
28:
23:
22:
15:
12:
11:
5:
3108:
3106:
3098:
3097:
3087:
3086:
3080:
3079:
3076:
3075:
3073:
3072:
3061:
3058:
3057:
3055:
3054:
3049:
3047:Random numbers
3044:
3039:
3034:
3029:
3024:
3019:
3014:
3009:
3004:
2999:
2993:
2991:
2987:
2986:
2984:
2983:
2978:
2973:
2971:Garlic routing
2968:
2963:
2958:
2953:
2948:
2943:
2938:
2933:
2928:
2923:
2918:
2913:
2908:
2903:
2898:
2893:
2891:Secure channel
2888:
2882:
2881:
2880:
2869:
2864:
2859:
2854:
2849:
2847:Key stretching
2844:
2839:
2834:
2829:
2824:
2819:
2814:
2813:
2812:
2807:
2802:
2792:
2790:Cryptovirology
2787:
2782:
2777:
2775:Cryptocurrency
2772:
2767:
2762:
2761:
2760:
2750:
2745:
2740:
2734:
2732:
2728:
2727:
2722:
2720:
2719:
2712:
2705:
2697:
2690:
2689:
2686:
2685:
2682:
2681:
2679:
2678:
2673:
2668:
2662:
2660:
2656:
2655:
2653:
2652:
2647:
2642:
2637:
2632:
2630:shift register
2627:
2621:
2619:
2615:
2614:
2612:
2611:
2606:
2601:
2595:
2593:
2589:
2588:
2586:
2585:
2580:
2575:
2570:
2565:
2560:
2555:
2550:
2545:
2540:
2535:
2530:
2525:
2520:
2515:
2510:
2505:
2500:
2495:
2490:
2485:
2480:
2475:
2470:
2464:
2462:
2458:
2457:
2454:
2453:
2451:
2450:
2445:
2440:
2434:
2432:
2428:
2427:
2425:
2424:
2419:
2414:
2409:
2403:
2401:
2394:
2387:
2386:
2384:
2383:
2378:
2373:
2368:
2363:
2358:
2352:
2350:
2346:
2345:
2342:Stream ciphers
2340:
2338:
2337:
2330:
2323:
2315:
2308:
2307:
2304:
2303:
2301:
2300:
2295:
2290:
2284:
2282:
2278:
2277:
2275:
2274:
2269:
2264:
2259:
2254:
2248:
2246:
2242:
2241:
2239:
2238:
2233:
2228:
2223:
2218:
2213:
2208:
2203:
2198:
2193:
2188:
2183:
2182:
2181:
2176:
2171:
2166:
2161:
2151:
2146:
2141:
2136:
2128:
2123:
2118:
2111:Distinguishing
2108:
2103:
2102:
2101:
2096:
2091:
2081:
2071:
2070:
2069:
2064:
2054:
2043:
2041:
2031:
2030:
2028:
2027:
2017:
2012:
2007:
2002:
1997:
1992:
1987:
1982:
1977:
1975:Product cipher
1972:
1967:
1962:
1956:
1954:
1950:
1949:
1947:
1946:
1941:
1936:
1931:
1926:
1921:
1916:
1911:
1906:
1901:
1896:
1891:
1886:
1881:
1876:
1871:
1866:
1861:
1856:
1851:
1846:
1841:
1836:
1831:
1826:
1821:
1816:
1811:
1806:
1801:
1796:
1791:
1786:
1781:
1776:
1771:
1766:
1761:
1756:
1751:
1746:
1741:
1730:
1725:
1720:
1715:
1710:
1705:
1700:
1695:
1690:
1685:
1680:
1675:
1670:
1665:
1660:
1655:
1650:
1645:
1640:
1635:
1630:
1625:
1620:
1615:
1610:
1605:
1603:Cryptomeria/C2
1600:
1595:
1590:
1585:
1580:
1575:
1570:
1565:
1560:
1555:
1550:
1545:
1540:
1535:
1530:
1525:
1520:
1515:
1510:
1504:
1502:
1496:
1495:
1493:
1492:
1487:
1482:
1477:
1472:
1467:
1462:
1457:
1452:
1447:
1442:
1437:
1431:
1429:
1423:
1422:
1420:
1419:
1414:
1409:
1404:
1390:
1385:
1379:
1377:
1371:
1370:
1360:
1358:
1357:
1350:
1343:
1335:
1319:
1318:
1305:
1303:. 2006. p. 245
1292:
1290:. 2006. p. 144
1279:
1266:
1249:
1236:
1223:
1210:
1196:
1171:
1158:
1146:
1114:
1089:
1064:
1055:|journal=
1033:(2010-03-03).
1022:
997:
982:
964:
940:
915:
895:
864:
801:
742:
722:
692:
678:
671:
651:
644:
622:
615:
592:
591:
589:
586:
583:
582:
544:
543:
541:
538:
530:Feistel cipher
514:
513:
508:
503:
498:
493:
488:
485:
478:
476:Enigma machine
473:
468:
431:
430:
389:
387:
380:
374:
371:
353:key generation
351:Main article:
348:
347:Key generation
345:
339:or some other
325:Main article:
322:
319:
314:Main article:
311:
310:Key management
308:
263:
260:
250:Feistel cipher
248:Main article:
245:
242:
234:hash functions
196:
193:
128:
125:
87:stream ciphers
82:
79:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
3107:
3096:
3093:
3092:
3090:
3071:
3063:
3062:
3059:
3053:
3052:Steganography
3050:
3048:
3045:
3043:
3040:
3038:
3035:
3033:
3030:
3028:
3025:
3023:
3020:
3018:
3015:
3013:
3010:
3008:
3007:Stream cipher
3005:
3003:
3000:
2998:
2995:
2994:
2992:
2988:
2982:
2979:
2977:
2974:
2972:
2969:
2967:
2966:Onion routing
2964:
2962:
2959:
2957:
2954:
2952:
2949:
2947:
2946:Shared secret
2944:
2942:
2939:
2937:
2934:
2932:
2929:
2927:
2924:
2922:
2919:
2917:
2914:
2912:
2909:
2907:
2904:
2902:
2899:
2897:
2894:
2892:
2889:
2886:
2883:
2878:
2875:
2874:
2873:
2870:
2868:
2865:
2863:
2860:
2858:
2855:
2853:
2850:
2848:
2845:
2843:
2840:
2838:
2837:Key generator
2835:
2833:
2830:
2828:
2825:
2823:
2820:
2818:
2815:
2811:
2808:
2806:
2803:
2801:
2798:
2797:
2796:
2795:Hash function
2793:
2791:
2788:
2786:
2783:
2781:
2778:
2776:
2773:
2771:
2770:Cryptanalysis
2768:
2766:
2763:
2759:
2756:
2755:
2754:
2751:
2749:
2746:
2744:
2741:
2739:
2736:
2735:
2733:
2729:
2725:
2718:
2713:
2711:
2706:
2704:
2699:
2698:
2695:
2691:
2677:
2674:
2672:
2669:
2667:
2664:
2663:
2661:
2657:
2651:
2648:
2646:
2643:
2641:
2638:
2636:
2633:
2631:
2628:
2626:
2623:
2622:
2620:
2616:
2610:
2607:
2605:
2602:
2600:
2597:
2596:
2594:
2590:
2584:
2581:
2579:
2576:
2574:
2571:
2569:
2566:
2564:
2561:
2559:
2556:
2554:
2551:
2549:
2546:
2544:
2541:
2539:
2536:
2534:
2531:
2529:
2526:
2524:
2521:
2519:
2516:
2514:
2511:
2509:
2506:
2504:
2501:
2499:
2496:
2494:
2491:
2489:
2486:
2484:
2481:
2479:
2476:
2474:
2471:
2469:
2466:
2465:
2463:
2461:Other ciphers
2459:
2449:
2446:
2444:
2441:
2439:
2436:
2435:
2433:
2429:
2423:
2420:
2418:
2415:
2413:
2410:
2408:
2405:
2404:
2402:
2398:
2395:
2392:
2388:
2382:
2379:
2377:
2374:
2372:
2369:
2367:
2364:
2362:
2359:
2357:
2354:
2353:
2351:
2347:
2343:
2336:
2331:
2329:
2324:
2322:
2317:
2316:
2313:
2309:
2299:
2296:
2294:
2291:
2289:
2286:
2285:
2283:
2279:
2273:
2270:
2268:
2265:
2263:
2260:
2258:
2255:
2253:
2250:
2249:
2247:
2243:
2237:
2234:
2232:
2229:
2227:
2224:
2222:
2219:
2217:
2214:
2212:
2209:
2207:
2204:
2202:
2199:
2197:
2194:
2192:
2191:Interpolation
2189:
2187:
2184:
2180:
2177:
2175:
2172:
2170:
2167:
2165:
2162:
2160:
2157:
2156:
2155:
2152:
2150:
2147:
2145:
2142:
2140:
2137:
2135:
2134:
2129:
2127:
2124:
2122:
2119:
2116:
2112:
2109:
2107:
2104:
2100:
2097:
2095:
2092:
2090:
2087:
2086:
2085:
2082:
2079:
2075:
2072:
2068:
2065:
2063:
2060:
2059:
2058:
2055:
2052:
2048:
2045:
2044:
2042:
2039:
2038:cryptanalysis
2032:
2025:
2021:
2020:Key whitening
2018:
2016:
2013:
2011:
2008:
2006:
2003:
2001:
1998:
1996:
1993:
1991:
1988:
1986:
1983:
1981:
1978:
1976:
1973:
1971:
1968:
1966:
1963:
1961:
1958:
1957:
1955:
1951:
1945:
1942:
1940:
1937:
1935:
1932:
1930:
1927:
1925:
1922:
1920:
1917:
1915:
1912:
1910:
1907:
1905:
1902:
1900:
1897:
1895:
1892:
1890:
1887:
1885:
1882:
1880:
1877:
1875:
1872:
1870:
1867:
1865:
1862:
1860:
1857:
1855:
1852:
1850:
1847:
1845:
1842:
1840:
1837:
1835:
1832:
1830:
1827:
1825:
1822:
1820:
1817:
1815:
1812:
1810:
1809:New Data Seal
1807:
1805:
1802:
1800:
1797:
1795:
1792:
1790:
1787:
1785:
1782:
1780:
1777:
1775:
1772:
1770:
1767:
1765:
1762:
1760:
1757:
1755:
1752:
1750:
1747:
1745:
1742:
1739:
1735:
1731:
1729:
1726:
1724:
1721:
1719:
1716:
1714:
1711:
1709:
1706:
1704:
1701:
1699:
1696:
1694:
1691:
1689:
1686:
1684:
1681:
1679:
1676:
1674:
1671:
1669:
1666:
1664:
1661:
1659:
1656:
1654:
1651:
1649:
1646:
1644:
1641:
1639:
1636:
1634:
1631:
1629:
1626:
1624:
1621:
1619:
1616:
1614:
1611:
1609:
1606:
1604:
1601:
1599:
1596:
1594:
1591:
1589:
1586:
1584:
1581:
1579:
1576:
1574:
1571:
1569:
1566:
1564:
1561:
1559:
1556:
1554:
1551:
1549:
1548:BEAR and LION
1546:
1544:
1541:
1539:
1536:
1534:
1531:
1529:
1526:
1524:
1521:
1519:
1516:
1514:
1511:
1509:
1506:
1505:
1503:
1497:
1491:
1488:
1486:
1483:
1481:
1478:
1476:
1473:
1471:
1468:
1466:
1463:
1461:
1458:
1456:
1453:
1451:
1448:
1446:
1443:
1441:
1438:
1436:
1433:
1432:
1430:
1424:
1418:
1415:
1413:
1410:
1408:
1405:
1402:
1398:
1394:
1391:
1389:
1386:
1384:
1381:
1380:
1378:
1372:
1367:
1363:
1362:Block ciphers
1356:
1351:
1349:
1344:
1342:
1337:
1336:
1333:
1329:
1325:
1315:
1312:Greg Goebel.
1309:
1306:
1302:
1296:
1293:
1289:
1283:
1280:
1276:
1273:Greg Goebel.
1270:
1267:
1263:
1259:
1253:
1250:
1246:
1243:Greg Goebel.
1240:
1237:
1233:
1227:
1224:
1220:
1214:
1211:
1206:
1200:
1197:
1193:
1189:
1182:
1175:
1172:
1168:
1162:
1159:
1149:
1143:
1138:
1133:
1129:
1125:
1118:
1115:
1104:
1100:
1093:
1090:
1079:
1078:Computerworld
1075:
1068:
1065:
1060:
1047:
1036:
1032:
1026:
1023:
1018:
1011:
1007:
1001:
998:
993:
989:
985:
983:1-932266-18-6
979:
975:
968:
965:
954:
950:
944:
941:
930:
926:
923:Roeder, Tom.
919:
916:
908:
907:
899:
896:
891:
887:
883:
878:
877:
868:
865:
860:
856:
852:
848:
844:
840:
836:
832:
828:
824:
820:
816:
812:
805:
802:
797:
793:
788:
783:
779:
775:
770:
765:
761:
757:
753:
746:
743:
733:
729:
725:
723:9780128023242
719:
715:
711:
707:
703:
696:
693:
688:
682:
679:
674:
672:9780821844182
668:
664:
663:
655:
652:
647:
645:9783540492436
641:
637:
633:
626:
623:
618:
616:9789812879905
612:
608:
604:
597:
594:
587:
579:
575:
571:
567:
563:
559:
555:
549:
546:
539:
537:
535:
531:
527:
523:
519:
518:stream cipher
512:
509:
507:
504:
502:
499:
497:
494:
492:
491:Purple cipher
489:
486:
483:
479:
477:
474:
472:
469:
467:
464:
463:
462:
459:
457:
452:
450:
446:
442:
438:
427:
424:
416:
413:December 2015
406:
402:
396:
395:
390:This section
388:
384:
379:
378:
372:
370:
368:
364:
360:
354:
346:
344:
342:
338:
333:
328:
320:
317:
309:
307:
305:
301:
297:
293:
288:
285:
281:
277:
273:
269:
261:
259:
257:
256:Horst Feistel
251:
243:
241:
239:
235:
230:
228:
224:
219:
217:
214:cipher (e.g.
213:
209:
204:
202:
194:
192:
190:
186:
182:
178:
174:
170:
166:
162:
158:
154:
150:
146:
142:
138:
134:
126:
124:
122:
118:
113:
111:
107:
103:
99:
94:
92:
91:block ciphers
88:
80:
78:
76:
72:
68:
64:
63:shared secret
60:
56:
52:
48:
44:
40:
32:
19:
3011:
3002:Block cipher
2842:Key schedule
2832:Key exchange
2822:Kleptography
2780:Cryptosystem
2724:Cryptography
2196:Partitioning
2154:Side-channel
2132:
2099:Higher-order
2084:Differential
1965:Key schedule
1308:
1295:
1282:
1269:
1257:
1252:
1239:
1226:
1219:"Enigma Uhr"
1213:
1199:
1191:
1187:
1174:
1161:
1151:, retrieved
1127:
1117:
1106:. Retrieved
1102:
1092:
1081:. Retrieved
1077:
1067:
1046:cite journal
1025:
1016:
1000:
973:
967:
956:. Retrieved
952:
943:
932:. Retrieved
928:
918:
905:
898:
875:
867:
818:
814:
804:
759:
755:
745:
735:, retrieved
705:
695:
681:
661:
654:
638:. Springer.
635:
625:
606:
596:
569:
565:
561:
557:
553:
548:
526:block cipher
515:
460:
453:
448:
441:cryptography
434:
419:
410:
399:Please help
394:verification
391:
356:
334:
330:
289:
265:
253:
231:
220:
205:
198:
143:(Rijndael),
130:
114:
95:
84:
75:one-time pad
47:cryptography
38:
37:
2990:Mathematics
2981:Mix network
2281:Utilization
2267:NSA Suite B
2252:AES process
2201:Rubber-hose
2139:Related-key
2047:Brute-force
1426:Less common
762:(7): 1517.
570:private-key
2941:Ciphertext
2911:Decryption
2906:Encryption
2867:Ransomware
2645:T-function
2592:Generators
2468:Achterbahn
2231:Chi-square
2149:Rotational
2089:Impossible
2010:Block size
1904:Spectr-H64
1728:Ladder-DES
1723:Kuznyechik
1668:Hierocrypt
1538:BassOmatic
1501:algorithms
1428:algorithms
1401:Triple DES
1376:algorithms
1153:2023-09-12
1108:2022-12-05
1083:2022-12-05
958:2020-02-04
934:2017-02-05
737:2021-12-06
588:References
562:shared-key
558:single-key
554:secret-key
522:XOR cipher
506:XOR cipher
445:ciphertext
165:Kuznyechik
59:ciphertext
43:algorithms
2931:Plaintext
2558:SOBER-128
2488:KCipher-2
2422:SOSEMANUK
2393:Portfolio
2206:Black-bag
2126:Boomerang
2115:Known-key
2094:Truncated
1919:Threefish
1914:SXAL/MBAL
1804:MultiSwap
1759:MacGuffin
1718:KN-Cipher
1658:Grand Cru
1613:CS-Cipher
1593:COCONUT98
843:0028-0836
778:1424-8220
439:into the
437:plaintext
67:symmetric
55:plaintext
27:Algorithm
3089:Category
3070:Category
2976:Kademlia
2936:Codetext
2879:(CSPRNG)
2857:Machines
2431:Hardware
2400:Software
2371:Crypto-1
2257:CRYPTREC
2221:Weak key
2174:Acoustic
2015:Key size
1859:Red Pike
1678:IDEA NXT
1558:Chiasmus
1553:CAST-256
1533:BaseKing
1518:Akelarre
1513:Adiantum
1480:Skipjack
1445:CAST-128
1440:Camellia
1388:Blowfish
1008:(2009).
992:51564102
851:28905891
796:28654006
732:63087943
181:Skipjack
157:Blowfish
153:ChaCha20
145:Camellia
102:ChaCha20
2731:General
2659:Attacks
2448:Trivium
2417:Salsa20
2391:eSTREAM
2298:Padding
2216:Rebound
1924:Treyfer
1874:SAVILLE
1834:PRESENT
1824:NOEKEON
1769:MAGENTA
1764:Madryga
1744:Lucifer
1608:CRYPTON
1417:Twofish
1407:Serpent
1316:. 2018.
1277:. 2018.
1247:. 2018.
1234:. 2006.
1221:. 2009.
886:Bibcode
859:4446249
823:Bibcode
787:5551094
756:Sensors
609:: 147.
566:one-key
367:entropy
216:AES-GCM
149:Salsa20
137:Serpent
133:Twofish
2852:Keygen
2618:Theory
2568:Turing
2563:Spritz
2538:Scream
2508:Phelix
2503:Panama
2473:F-FCSR
2443:MICKEY
2412:Rabbit
2407:HC-128
2366:ChaCha
2262:NESSIE
2211:Davies
2159:Timing
2074:Linear
2034:Attack
1953:Design
1944:Zodiac
1909:Square
1884:SHACAL
1879:SC2000
1839:Prince
1819:Nimbus
1814:NewDES
1799:MULTI2
1789:MISTY1
1732:LOKI (
1708:KHAZAD
1703:KeeLoq
1698:KASUMI
1693:Kalyna
1578:CLEFIA
1563:CIKS-1
1523:Anubis
1374:Common
1144:
990:
980:
857:
849:
841:
815:Nature
794:
784:
776:
730:
720:
669:
642:
613:
568:, and
466:Atbash
187:, and
2887:(PRN)
2640:NLFSR
2553:SOBER
2483:ISAAC
2438:Grain
2144:Slide
2000:Round
1985:P-box
1980:S-box
1939:XXTEA
1899:Speck
1894:Simon
1889:SHARK
1869:SAFER
1854:REDOC
1779:Mercy
1738:89/91
1688:Iraqi
1653:G-DES
1643:FEA-M
1623:DES-X
1588:Cobra
1543:BATON
1528:Ascon
1508:3-Way
1499:Other
1184:(PDF)
1038:(PDF)
1013:(PDF)
910:(PDF)
855:S2CID
728:S2CID
540:Notes
501:ROT13
284:round
185:Safer
161:CAST5
98:bytes
81:Types
2635:LFSR
2583:WAKE
2578:VMPC
2573:VEST
2548:SNOW
2543:SEAL
2533:RC4A
2528:RC4+
2523:QUAD
2513:Pike
2498:ORYX
2493:MUGI
2478:FISH
2361:A5/2
2356:A5/1
2272:CNSA
2131:Mod
2057:MITM
1829:NUSH
1784:MESH
1774:MARS
1648:FROG
1638:FEAL
1618:DEAL
1598:Crab
1583:CMEA
1490:XTEA
1475:SEED
1455:IDEA
1450:GOST
1435:ARIA
1142:ISBN
1059:help
988:OCLC
978:ISBN
847:PMID
839:ISSN
792:PMID
774:ISSN
718:ISBN
667:ISBN
640:ISBN
611:ISBN
278:and
212:AEAD
189:IDEA
177:3DES
121:NIST
45:for
41:are
2381:RC4
2226:Tau
2186:XSL
1990:SPN
1934:xmx
1929:UES
1864:S-1
1849:RC2
1794:MMB
1673:ICE
1628:DFC
1485:TEA
1470:RC6
1465:RC5
1460:LEA
1412:SM4
1393:DES
1383:AES
1132:doi
953:ISO
831:doi
819:549
782:PMC
764:doi
710:doi
532:or
496:RC4
403:by
218:).
173:DES
169:RC4
141:AES
93:.
89:or
3091::
2650:IV
2518:Py
2376:E0
1754:M8
1749:M6
1736:,
1734:97
1633:E2
1399:,
1190:.
1186:.
1140:,
1126:,
1101:.
1076:.
1050::
1048:}}
1044:{{
1015:.
986:.
951:.
927:.
884:.
882:30
853:.
845:.
837:.
829:.
817:.
813:.
790:.
780:.
772:.
760:17
758:.
754:.
726:,
716:,
704:,
634:.
605:.
564:,
560:,
556:,
451:.
294:.
274:,
270:,
229:.
191:.
183:,
179:,
175:,
171:,
167:,
163:,
159:,
155:,
151:,
147:,
139:,
135:,
112:.
104:.
2716:e
2709:t
2702:v
2334:e
2327:t
2320:v
2133:n
2117:)
2113:(
2080:)
2076:(
2053:)
2049:(
2040:)
2036:(
2026:)
2022:(
1844:Q
1740:)
1403:)
1395:(
1368:)
1364:(
1354:e
1347:t
1340:v
1134::
1111:.
1086:.
1061:)
1057:(
1040:.
1019:.
994:.
961:.
937:.
912:.
892:.
888::
861:.
833::
825::
798:.
766::
712::
675:.
648:.
619:.
580:.
426:)
420:(
415:)
411:(
397:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.