794:
and Brent Waters in 2010. Until recently, however, most instantiations of
Functional Encryption supported only limited function classes such as boolean formulae. In 2012, several researchers developed Functional Encryption schemes that support arbitrary functions.
24:
189:
284:
444:
375:
233:
306:
211:
728:
768:
687:
627:
479:
576:
748:
667:
647:
547:
519:
499:
395:
326:
124:
848:. EUROCRYPT 2005: 24th Annual International Conference on the Theory and Applications of Cryptographic Techniques, Proceedings. Springer. pp. 457–473.
132:
240:
982:
853:
826:
1004:
818:
Reusable garbled circuits and succinct functional encryption - Stoc 13 Proceedings of the 2013 ACM Symposium on Theory of
Computing
402:
333:
591:
75:
91:
65:
899:
Gorbunov, Sergey; Hoeteck Wee; Vinod
Vaikuntanathan (2013). "Attribute-Based Encryption for Circuits".
815:
Goldwasser, Shafi; Kalai, Yael; Ada Popa, Raluca; Vaikuntanathan, Vinod; Zeldovich, Nickolai (2013).
587:
216:
942:
Goldwasser, Shafi; Yael Kalai; Raluca Ada Popa; Vinod
Vaikuntanathan; Nickolai Zeldovich (2013).
922:
289:
194:
978:
859:
849:
822:
816:
692:
526:
968:
958:
842:
Amit Sahai; Brent Waters (2005). "Fuzzy
Identity-Based Encryption". In Ronald Cramer (ed.).
753:
672:
597:
449:
51:
552:
733:
652:
632:
532:
504:
484:
380:
311:
109:
998:
184:{\displaystyle ({\text{pk}},{\text{msk}})\leftarrow {\textsf {Setup}}(1^{\lambda })}
783:
43:
963:
843:
791:
779:
529:
of FE requires that any information an adversary learns from an encryption of
95:
55:
39:
787:
94:
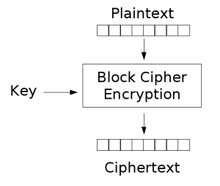
in which possessing a secret key allows one to learn a function of what the
47:
106:
More precisely, a functional encryption scheme for a given functionality
973:
586:
Functional encryption generalizes several existing primitives including
279:{\displaystyle {\text{sk}}\leftarrow {\textsf {Keygen}}({\text{msk}},f)}
957:. Lecture Notes in Computer Science. Vol. 8043. pp. 536–553.
23:
943:
915:
878:
927:
863:
916:"Attribute-Based Encryption for Circuits from Multilinear Maps"
886:
669:
corresponds to an identity that is allowed to decrypt, and
439:{\displaystyle y\leftarrow {\textsf {Dec}}({\text{sk}},c)}
370:{\displaystyle c\leftarrow {\textsf {Enc}}({\text{pk}},x)}
286:: uses the master secret key to generate a new secret key
756:
736:
695:
675:
655:
635:
600:
555:
535:
507:
487:
452:
405:
383:
336:
314:
292:
243:
219:
197:
135:
112:
879:"Functional Encryption: Definitions and Challenges"
71:
61:
35:
30:
762:
750:encodes attributes with permission to decrypt and
742:
722:
681:
661:
641:
621:
570:
541:
513:
493:
473:
438:
389:
369:
320:
300:
278:
227:
205:
183:
118:
944:"How to Run Turing Machines on Encrypted Data"
689:otherwise. Similarly, in the ABE case, define
877:Boneh, Dan; Amit Sahai; Brent Waters (2011).
8:
821:. New York, NY, USA: ACM. pp. 555–564.
16:
578:. Formally, this is defined by simulation.
377:: uses the public key to encrypt a message
126:consists of the following four algorithms:
22:
972:
962:
926:
755:
735:
694:
674:
654:
634:
599:
554:
534:
506:
486:
451:
422:
414:
413:
412:
404:
382:
353:
345:
344:
343:
335:
313:
293:
291:
262:
254:
253:
252:
244:
242:
220:
218:
198:
196:
172:
160:
159:
158:
147:
139:
134:
111:
804:
778:Functional encryption was proposed by
15:
7:
951:Advances in Cryptology – CRYPTO 2013
810:
808:
914:Sahai, Amit; Brent Waters (2012).
14:
594:(ABE). In the IBE case, define
446:: uses secret key to calculate
711:
699:
616:
604:
565:
559:
468:
462:
433:
419:
409:
364:
350:
340:
273:
259:
249:
178:
165:
155:
152:
136:
1:
964:10.1007/978-3-642-40084-1_30
228:{\displaystyle {\text{msk}}}
301:{\displaystyle {\text{sk}}}
206:{\displaystyle {\text{pk}}}
1021:
786:in 2005 and formalized by
592:attribute-based encryption
588:Identity-based encryption
90:) is a generalization of
21:
1005:Cryptographic primitives
723:{\displaystyle F(k,x)=x}
213:and a master secret key
191:: creates a public key
845:Advances in Cryptology
764:
763:{\displaystyle \perp }
744:
724:
683:
682:{\displaystyle \perp }
663:
643:
623:
622:{\displaystyle F(k,x)}
572:
543:
515:
495:
475:
474:{\displaystyle y=f(x)}
440:
391:
371:
322:
302:
280:
229:
207:
185:
120:
76:Homomorphic encryption
765:
745:
725:
684:
664:
644:
624:
573:
544:
516:
496:
476:
441:
392:
372:
323:
303:
281:
230:
208:
186:
121:
92:public-key encryption
84:Functional encryption
66:Public-key encryption
17:Functional encryption
754:
734:
693:
673:
653:
633:
598:
571:{\displaystyle f(x)}
553:
533:
505:
485:
450:
403:
381:
334:
312:
290:
241:
217:
195:
133:
110:
901:Proceedings of STOC
18:
760:
740:
720:
679:
659:
639:
619:
568:
539:
511:
501:is the value that
491:
471:
436:
387:
367:
318:
298:
276:
225:
203:
181:
116:
984:978-3-642-40083-4
855:978-3-540-25910-7
828:978-1-4503-2029-0
743:{\displaystyle k}
662:{\displaystyle k}
642:{\displaystyle x}
542:{\displaystyle x}
514:{\displaystyle c}
494:{\displaystyle x}
425:
416:
390:{\displaystyle x}
356:
347:
321:{\displaystyle f}
308:for the function
296:
265:
256:
247:
223:
201:
162:
150:
142:
119:{\displaystyle f}
102:Formal definition
81:
80:
1012:
989:
988:
976:
966:
948:
939:
933:
932:
930:
920:
911:
905:
904:
896:
890:
889:
883:
874:
868:
867:
839:
833:
832:
812:
769:
767:
766:
761:
749:
747:
746:
741:
729:
727:
726:
721:
688:
686:
685:
680:
668:
666:
665:
660:
648:
646:
645:
640:
628:
626:
625:
620:
577:
575:
574:
569:
548:
546:
545:
540:
520:
518:
517:
512:
500:
498:
497:
492:
480:
478:
477:
472:
445:
443:
442:
437:
426:
423:
418:
417:
396:
394:
393:
388:
376:
374:
373:
368:
357:
354:
349:
348:
327:
325:
324:
319:
307:
305:
304:
299:
297:
294:
285:
283:
282:
277:
266:
263:
258:
257:
248:
245:
234:
232:
231:
226:
224:
221:
212:
210:
209:
204:
202:
199:
190:
188:
187:
182:
177:
176:
164:
163:
151:
148:
143:
140:
125:
123:
122:
117:
52:Shafi Goldwasser
26:
19:
1020:
1019:
1015:
1014:
1013:
1011:
1010:
1009:
995:
994:
993:
992:
985:
946:
941:
940:
936:
918:
913:
912:
908:
898:
897:
893:
881:
876:
875:
871:
856:
841:
840:
836:
829:
814:
813:
806:
801:
776:
752:
751:
732:
731:
691:
690:
671:
670:
651:
650:
631:
630:
629:to be equal to
596:
595:
584:
551:
550:
549:is revealed by
531:
530:
503:
502:
483:
482:
448:
447:
401:
400:
379:
378:
332:
331:
310:
309:
288:
287:
239:
238:
215:
214:
193:
192:
168:
131:
130:
108:
107:
104:
98:is encrypting.
72:Related to
12:
11:
5:
1018:
1016:
1008:
1007:
997:
996:
991:
990:
983:
934:
906:
891:
869:
854:
834:
827:
803:
802:
800:
797:
775:
772:
759:
739:
719:
716:
713:
710:
707:
704:
701:
698:
678:
658:
638:
618:
615:
612:
609:
606:
603:
583:
580:
567:
564:
561:
558:
538:
523:
522:
510:
490:
470:
467:
464:
461:
458:
455:
435:
432:
429:
421:
411:
408:
398:
386:
366:
363:
360:
352:
342:
339:
329:
317:
275:
272:
269:
261:
251:
236:
180:
175:
171:
167:
157:
154:
146:
138:
115:
103:
100:
79:
78:
73:
69:
68:
63:
59:
58:
37:
33:
32:
28:
27:
13:
10:
9:
6:
4:
3:
2:
1017:
1006:
1003:
1002:
1000:
986:
980:
975:
970:
965:
960:
956:
952:
945:
938:
935:
929:
924:
917:
910:
907:
902:
895:
892:
887:
880:
873:
870:
865:
861:
857:
851:
847:
846:
838:
835:
830:
824:
820:
819:
811:
809:
805:
798:
796:
793:
789:
785:
781:
773:
771:
757:
737:
717:
714:
708:
705:
702:
696:
676:
656:
636:
613:
610:
607:
601:
593:
589:
581:
579:
562:
556:
536:
528:
508:
488:
465:
459:
456:
453:
430:
427:
406:
399:
384:
361:
358:
337:
330:
315:
270:
267:
237:
173:
169:
144:
129:
128:
127:
113:
101:
99:
97:
93:
89:
85:
77:
74:
70:
67:
64:
60:
57:
53:
49:
45:
41:
38:
34:
29:
25:
20:
974:1721.1/91472
954:
950:
937:
909:
900:
894:
885:
872:
844:
837:
817:
784:Brent Waters
777:
585:
582:Applications
524:
105:
87:
83:
82:
62:Derived from
44:Brent Waters
955:Crypto 2013
770:otherwise.
864:2005926095
799:References
792:Amit Sahai
780:Amit Sahai
590:(IBE) and
96:ciphertext
56:Yael Kalai
40:Amit Sahai
928:1210.5287
788:Dan Boneh
758:⊥
677:⊥
521:encrypts.
410:←
341:←
250:←
174:λ
156:←
48:Dan Boneh
36:Designers
999:Category
527:security
774:History
31:General
981:
862:
852:
825:
481:where
255:Keygen
947:(PDF)
923:arXiv
919:(PDF)
882:(PDF)
730:when
649:when
161:Setup
979:ISBN
860:LCCN
850:ISBN
823:ISBN
782:and
525:The
969:hdl
959:doi
415:Dec
346:Enc
264:msk
222:msk
149:msk
1001::
977:.
967:.
953:.
949:.
921:.
884:.
858:.
807:^
790:,
424:sk
355:pk
295:sk
246:sk
200:pk
141:pk
88:FE
54:,
50:,
46:,
42:,
987:.
971::
961::
931:.
925::
903:.
888:.
866:.
831:.
738:k
718:x
715:=
712:)
709:x
706:,
703:k
700:(
697:F
657:k
637:x
617:)
614:x
611:,
608:k
605:(
602:F
566:)
563:x
560:(
557:f
537:x
509:c
489:x
469:)
466:x
463:(
460:f
457:=
454:y
434:)
431:c
428:,
420:(
407:y
397:.
385:x
365:)
362:x
359:,
351:(
338:c
328:.
316:f
274:)
271:f
268:,
260:(
235:.
179:)
170:1
166:(
153:)
145:,
137:(
114:f
86:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.