202:
365:). For elliptic curves algorithms and asymmetric algorithms, the requirements for key length are 128 bit and 768 bits, respectively. In addition, other items require a one-time review by, or notification to, BIS prior to export to most countries. For instance, the BIS must be notified before open-source cryptographic software is made publicly available on the Internet, though no review is required. Export regulations have been relaxed from pre-1996 standards, but are still complex. Other countries, notably those participating in the
93:
321:. The Commodity Jurisdiction process was replaced with a Commodity Classification process, and a provision was added to allow export of 56-bit encryption if the exporter promised to add "key recovery" backdoors by the end of 1998. In 1999, the EAR was changed to allow 56-bit encryption (based on RC2, RC4, RC5, DES or CAST) and 1024-bit RSA to be exported without any backdoors, and new SSL cipher suites were introduced to support this (
33:
177:. Since in the immediate post WWII period the market for cryptography was almost entirely military, the encryption technology (techniques as well as equipment and, after computers began to play a larger role in modern life, crypto software) was included as "Category XI - Miscellaneous Articles" and later "Category XIII - Auxiliary Military Equipment" item into the
358:-approved electronics, custom cryptographic software, and even cryptographic consulting services still require an export license(pp. 6–7). Furthermore, encryption registration with the BIS is required for the export of "mass market encryption commodities, software and components with encryption exceeding 64 bits" (75
253:
encryption easily exportable using a
Commodity Jurisdiction with special "7-day" and "15-day" review processes (which transferred control from the State Department to the Commerce Department). At this stage Western governments had, in practice, a split personality when it came to encryption; policy
188:
in 1975 meant that commercial uses of high quality encryption would become common, and serious problems of export control began to arise. Generally these were dealt with through case-by-case export license request proceedings brought by computer manufacturers, such as
333:
software containing cryptography, including allowing the key length restrictions to be removed after going through the
Commodity Classification process (to classify the software as "retail") and adding an exception for publicly available encryption source code.
967:
369:, have similar restrictions.On March 29, 2021 the Implementation of Wassenaar Arrangement 2019 Plenary Decisions was published in the Federal Register. This rule included changes to license exception ENC Section 740.17 of the EAR
168:
Two types of technology were protected: technology associated only with weapons of war ("munitions") and dual use technology, which also had commercial applications. In the U.S., dual use technology export was controlled by the
934:
277:
public keys in combination with full size symmetric keys (secret keys) (128-bit RC4 or 3DES in SSL 3.0 and TLS 1.0). The "International
Edition" had its effective key lengths reduced to 512 bits and 40 bits respectively
282:
with 40-bit RC2 or RC4 in SSL 3.0 and TLS 1.0). Acquiring the 'U.S. domestic' version turned out to be sufficient hassle that most computer users, even in the U.S., ended up with the 'International' version, whose weak
254:
was made by the military cryptanalysts, who were solely concerned with preventing their 'enemies' acquiring secrets, but that policy was then communicated to commerce by officials whose job was to support industry.
964:
184:
By the 1960s, however, financial organizations were beginning to require strong commercial encryption on the rapidly growing field of wired money transfer. The U.S. Government's introduction of the
136:
and the ability to prosecute war. Changes in technology and the preservation of free speech have been competing factors in the regulation and constraint of cryptographic technologies for export.
388:
Encryption items specifically designed, developed, configured, adapted or modified for military applications (including command, control and intelligence applications) are controlled by the
931:
932:
Wassenaar
Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies Public Documents Volume IV Background Documents and Plenary-related and Other Statements
301:
and other civil libertarians and privacy advocates, the widespread availability of encryption software outside the U.S., and the perception by many companies that adverse publicity about
423:
is a mechanism which is designed to allow a customer or other party to insert cryptographic functionality without the intervention, help or assistance of the manufacturer or its agents.
625:
An item can be either self-classified, or a classification ("review") requested from the BIS. A BIS review is required for typical items to get the 5A992 or 5D992 classification.
790:
1713:
837:
920:
Wassenaar
Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies: Guidelines & Procedures, including the Initial Elements
235:
In 1989, non-encryption use of cryptography (such as access control and message authentication) was removed from export control with a
Commodity Jurisdiction.
181:
on
November 17, 1954. The multinational control of the export of cryptography on the Western side of the cold war divide was done via the mechanisms of CoCom.
1287:
615:
Technology for the development, production or use of equipment controlled by 5A002 or 5B002 or software controlled by 5D002. Reasons for control: NS1, AT1.
465:(A, B, D, E) with further subdivisions; a country can belong to more than one group. For the purposes of encryption, groups B, D:1, and E:1 are important:
238:
In 1992, an exception was formally added in the USML for non-encryption use of cryptography (and satellite TV descramblers) and a deal between NSA and the
1232:
658:
919:
1238:
236:
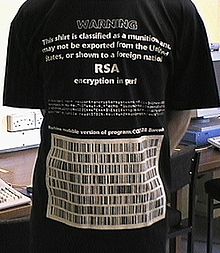
112:). Changes in the export law means that it is no longer illegal to export this T-shirt from the U.S., or for U.S. citizens to show it to foreigners.
769:
876:
1382:
1226:
305:
was limiting their sales and the growth of e-commerce, led to a series of relaxations in US export controls, culminating in 1996 in
President
723:
1149:
973:
557:
1718:
1683:
1504:
1124:
1320:
1723:
1426:
1214:
1185:
949:
770:"January 25, 1999 archive of the Netscape Communicator 4.61 download page showing a more difficult path to download 128-bit version"
378:
318:
109:
76:
43:
1086:
1647:
1107:
232:
in the 1990s created additional pressure for reduced restrictions. VideoCipher II also used DES to scramble satellite TV audio.
1339:
1041:
1010:
343:
239:
1652:
1249:
571:
Systems, equipment, electronic assemblies, and integrated circuits for "information security. Reasons for
Control: NS1, AT1.
1097:. In Karl de Leeuw, Jan Bergstra, ed. The history of information security. A comprehensive handbook. Elsevier, 2007. p. 725
583:
Equipment for development or production of items classified as 5A002, 5B002, 5D002 or 5E002. Reasons for
Control: NS1, AT1.
201:
157:
regulations designed to prevent a wide range of Western technology from falling into the hands of others, particularly the
1464:
1434:
1333:
903:
849:
393:
317:. Furthermore, the order stated that, "the software shall not be considered or treated as 'technology'" in the sense of
178:
1444:
1314:
434:
411:
is an encryption commodity or software (but not the source code), including encryption chips, integrated circuits etc.
382:
58:
1625:
1388:
877:"U. S. Bureau of Industry and Security - Notification Requirements for "Publicly Available" Encryption Source Code"
635:
294:
54:
1484:
1416:
1355:
478:
is a short list of countries that are subject to stricter export control. Notable countries on this list include
430:
1605:
1568:
1535:
1208:
1194:
262:
185:
228:
in 1991 was the first major 'individual level' challenge to controls on export of cryptography. The growth of
1132:
1366:
1350:
1255:
266:
342:
As of 2009, non-military cryptography exports from the U.S. are controlled by the Department of Commerce's
1345:
1309:
1220:
1160:
circa 1997, formerly Top Secret, approved for release by NSA with redactions September 10, 2014, C06122418
641:
577:"Mass market" encryption commodities and other equipment not controlled by 5A002. Reason for Control: AT1.
326:
170:
1116:
1708:
1672:
1573:
1293:
1178:
561:
366:
346:. Some restrictions still exist, even for mass market products; particularly with regards to export to "
314:
970:
528:
can be applied. For the purposes of encryption, the following three reasons for control are important:
287:
can currently be broken in a matter of days using a single computer. A similar situation occurred with
1082:
880:
330:
310:
1128:
CRS Issue Brief for Congress IB96039. Congressional Research Service, The Library of Congress. 2000
703:
389:
229:
221:
218:
1146:
1589:
1304:
965:
Export Administration Regulations: Implementation of Wassenaar Arrangement 2019 Plenary Decisions
355:
97:
1120:
CRS Report for Congress 98-905 F. Congressional Research Service, The Library of Congress. 1998
433:; games, household appliances; printing, photo and video recording (but not videoconferencing);
1105:
CRS Report for Congress RL30273. Congressional Research Service, The Library of Congress. 2001
946:
492:
is a very short list of "terrorist-supporting" countries (as of 2009, includes five countries (
1540:
1266:
1147:
The Evolution of US Government Restrictions on Using and Exporting Encryption Technologies (U)
987:"15 CFR § 772.1 - Definitions of terms as used in the Export Administration Regulations (EAR)"
784:
719:
284:
243:
210:
133:
105:
1545:
1361:
1299:
1171:
711:
359:
274:
174:
92:
1271:
1153:
1143:. National Academy Press, Washington, D.C. 1996 (full text link is available on the page).
1111:
652:
302:
214:
209:
Encryption export controls became a matter of public concern with the introduction of the
804:
265:
technology was widely adopted as a method for protecting credit card transactions using
89:
Transfer from the United States to another country of technology related to cryptography
715:
646:
362:
154:
1101:
976:
Implementation of Wassenaar Arrangement 2019 Plenary Decisions. Archived on 2024-02-09
516:
The EAR Supplement No. 1 to Part 738 (Commerce Country Chart) contains the table with
1702:
1326:
1261:
953:
907:
838:
Commerce Control List Supplement No. 1 to Part 774 Category 5 Part 2 - Info. Security
461:
Export destinations are classified by the EAR Supplement No. 1 to Part 740 into four
125:
117:
1048:
1017:
900:
688:
1620:
1394:
347:
306:
298:
158:
129:
121:
1141:
National Research Council, Cryptography's Role in Securing the Information Society
1140:
986:
668:
501:
472:
is a large list of countries that are subject to relaxed encryption export rules
429:
items are the ones primarily used not for computing and communications, but for
288:
270:
101:
1092:
512:); previously contained six countries and was also called "terrorist 6" or T-6)
1667:
450:
442:
120:
to other countries has experienced various levels of restrictions over time.
1662:
1474:
1439:
1134:
Cryptography and Liberty 2000. An International Survey of Encryption Policy.
351:
404:
Encryption export terminology is defined in EAR part 772.1. In particular:
520:. If a line of table that corresponds to the country contains an X in the
104:
printed on a T-shirt made the T-shirt an export-restricted munition, as a
17:
1479:
1469:
1454:
744:
454:
438:
258:
225:
150:
592:
used to develop, produce, or use items classified as 5A002, 5B002, 5D002
273:. The "U.S. edition" supported full size (typically 1024-bit or larger)
1519:
1514:
1499:
1489:
329:
implemented rules that greatly simplified the export of commercial and
609:
Encryption software not controlled by 5D002. Reasons for control: AT1.
524:
column, the export of a controlled item requires a license, unless an
417:
include non-military encryption commodities, software, and technology.
1677:
1630:
1610:
1509:
1494:
1459:
1085:— An overview of the US export regulations can be found in the
483:
313:
transferring the commercial encryption from the Munition List to the
161:. All export of technology classed as 'critical' required a license.
61:. Statements consisting only of original research should be removed.
1657:
1615:
1449:
1244:
663:
509:
505:
479:
200:
162:
91:
598:
modeling the functions of equipment controlled by 5A002 or 5B002
497:
493:
446:
1167:
704:"The export of cryptography in the 20th and the 21st centuries"
1163:
250:
246:
190:
26:
1095:
The Export of Cryptography in the 20th and the 21st Centuries
1075:
564:(CCL, Supplement No. 1 to the EAR part 774). In particular:
1136:
Electronic Privacy Information Center. Washington, DC. 2000
153:, the U.S. and its allies developed an elaborate series of
621:
Technology for the 5x992 items. Reasons for control: AT1.
205:
Netscape Navigator Install Disk stating "Not For export"
50:
947:
Encryption and Export Administration Regulations (EAR)
809:
EPIC copy of document from U.S. Department of Commerce
556:
For export purposes each item is classified with the
165:
was organized to coordinate Western export controls.
108:
protest against U.S. encryption export restrictions (
805:"Revised U.S. Encryption Export Control Regulations"
589:
Encryption software. Reasons for control: NS1, AT1.
1640:
1598:
1582:
1561:
1554:
1528:
1425:
1404:
1375:
1280:
1201:
937:on 2024-02-09. Wassenaar Arrangement December 2019
772:. Archived from the original on September 16, 1999
437:; industrial or manufacturing systems (including
354:organizations. Militarized encryption equipment,
789:: CS1 maint: bot: original URL status unknown (
1209:Transport Layer Security / Secure Sockets Layer
1412:Export of cryptography from the United States
1179:
8:
1288:Automated Certificate Management Environment
1118:The encryption debate: Intelligence aspects.
601:used to certify software controlled by 5D002
377:U.S. non-military exports are controlled by
1126:Encryption Technology: Congressional Issues
1558:
1233:DNS-based Authentication of Named Entities
1186:
1172:
1164:
659:Restrictions on the import of cryptography
385:(CFR) Title 15 chapter VII, subchapter C.
193:, and by their large corporate customers.
1714:Export and import control of cryptography
1239:DNS Certification Authority Authorization
879:. Bis.doc.gov. 2004-12-09. Archived from
702:Diffie, Whitfield; Landau, Susan (2007),
595:supporting technology controlled by 5E002
547:Encryption Items is currently same as NS1
269:. Netscape developed two versions of its
173:, while munitions were controlled by the
77:Learn how and when to remove this message
922:The Wassenaar Arrangement, December 2009
833:
831:
829:
827:
825:
680:
1383:Domain Name System Security Extensions
1227:Application-Layer Protocol Negotiation
782:
325:with 56-bit RC4 or DES). In 2000, the
7:
558:Export Control Classification Number
116:The export of cryptography from the
1093:Whitfield Diffie and Susan Landau,
708:The History of Information Security
1321:Online Certificate Status Protocol
1042:"EAR Supplement No. 1 to Part 738"
1011:"EAR Supplement No. 1 to Part 740"
25:
1215:Datagram Transport Layer Security
991:LII / Legal Information Institute
457:and other transportation systems.
381:(EAR), a short name for the U.S.
379:Export Administration Regulations
319:Export Administration Regulations
1648:Certificate authority compromise
716:10.1016/b978-044451608-4/50027-4
31:
1653:Random number generator attacks
1340:Extended Validation Certificate
1083:Bureau of Industry and Security
344:Bureau of Industry and Security
240:Software Publishers Association
1250:HTTP Strict Transport Security
710:, Elsevier, pp. 725–736,
1:
132:can play an integral part in
1334:Domain-validated certificate
1103:Encryption Export Controls.
560:(ECCN) with the help of the
421:Open cryptographic interface
394:United States Munitions List
224:and its distribution on the
179:United States Munitions List
1315:Certificate revocation list
971:Page 16482 Federal Register
435:business process automation
383:Code of Federal Regulations
57:the claims made and adding
1740:
1719:United States trade policy
1389:Internet Protocol Security
1202:Protocols and technologies
636:Bernstein v. United States
535:National Security Column 1
1417:Server-Gated Cryptography
1356:Public key infrastructure
1281:Public-key infrastructure
910:The Wassenaar Arrangement
431:digital rights management
149:In the early days of the
1724:Transport Layer Security
1569:Man-in-the-middle attack
1536:Certificate Transparency
1158:Encryption Technologies,
1156:, Micheal Schwartzbeck,
186:Data Encryption Standard
1680:(in regards to TLS 1.0)
1633:(in regards to SSL 3.0)
1367:Self-signed certificate
1351:Public-key cryptography
1272:Perfect forward secrecy
1256:HTTP Public Key Pinning
541:Anti-Terrorism Column 1
267:public key cryptography
1684:Kazakhstan MITM attack
1346:Public key certificate
1310:Certificate revocation
1221:Server Name Indication
745:"Fortify for Netscape"
642:Denied trade screening
427:Ancillary cryptography
327:Department of Commerce
291:for the same reasons.
206:
171:Department of Commerce
113:
1673:Lucky Thirteen attack
1574:Padding oracle attack
1294:Certificate authority
562:Commerce Control List
367:Wassenaar Arrangement
315:Commerce Control List
311:Executive Order 13026
204:
95:
901:Participating States
518:country restrictions
409:Encryption Component
689:"Munitions T-shirt"
390:Department of State
257:Shortly afterward,
230:electronic commerce
222:encryption software
1590:Bar mitzvah attack
1305:Certificate policy
1152:2016-05-09 at the
1110:2019-02-28 at the
522:reason for control
207:
114:
96:Export-restricted
42:possibly contains
1696:
1695:
1692:
1691:
1267:Opportunistic TLS
1077:Crypto law survey
725:978-0-444-51608-4
373:U.S. export rules
285:40-bit encryption
211:personal computer
134:national security
124:illustrated that
106:freedom of speech
87:
86:
79:
44:original research
16:(Redirected from
1731:
1559:
1546:HTTPS Everywhere
1362:Root certificate
1300:CA/Browser Forum
1188:
1181:
1174:
1165:
1087:licensing basics
1063:
1062:
1060:
1059:
1053:
1047:. Archived from
1046:
1038:
1032:
1031:
1029:
1028:
1022:
1016:. Archived from
1015:
1007:
1001:
1000:
998:
997:
983:
977:
962:
956:
944:
938:
929:
923:
917:
911:
898:
892:
891:
889:
888:
873:
867:
866:
864:
863:
854:
846:
840:
835:
820:
819:
817:
816:
801:
795:
794:
788:
780:
778:
777:
766:
760:
759:
757:
755:
741:
735:
734:
733:
732:
699:
693:
692:
685:
415:Encryption items
295:Legal challenges
175:State Department
82:
75:
71:
68:
62:
59:inline citations
35:
34:
27:
21:
1739:
1738:
1734:
1733:
1732:
1730:
1729:
1728:
1699:
1698:
1697:
1688:
1636:
1594:
1578:
1555:Vulnerabilities
1550:
1524:
1427:Implementations
1421:
1400:
1371:
1276:
1197:
1192:
1154:Wayback Machine
1112:Wayback Machine
1072:
1067:
1066:
1057:
1055:
1051:
1044:
1040:
1039:
1035:
1026:
1024:
1020:
1013:
1009:
1008:
1004:
995:
993:
985:
984:
980:
963:
959:
945:
941:
930:
926:
918:
914:
899:
895:
886:
884:
875:
874:
870:
861:
859:
857:www.bis.doc.gov
852:
848:
847:
843:
836:
823:
814:
812:
803:
802:
798:
781:
775:
773:
768:
767:
763:
753:
751:
749:www.fortify.net
743:
742:
738:
730:
728:
726:
701:
700:
696:
687:
686:
682:
677:
653:Junger v. Daley
631:
554:
402:
375:
340:
303:weak encryption
215:Phil Zimmermann
199:
147:
142:
90:
83:
72:
66:
63:
48:
36:
32:
23:
22:
15:
12:
11:
5:
1737:
1735:
1727:
1726:
1721:
1716:
1711:
1701:
1700:
1694:
1693:
1690:
1689:
1687:
1686:
1681:
1675:
1670:
1665:
1660:
1655:
1650:
1644:
1642:
1641:Implementation
1638:
1637:
1635:
1634:
1628:
1623:
1618:
1613:
1608:
1602:
1600:
1596:
1595:
1593:
1592:
1586:
1584:
1580:
1579:
1577:
1576:
1571:
1565:
1563:
1556:
1552:
1551:
1549:
1548:
1543:
1538:
1532:
1530:
1526:
1525:
1523:
1522:
1517:
1512:
1507:
1502:
1497:
1492:
1487:
1482:
1477:
1472:
1467:
1462:
1457:
1452:
1447:
1442:
1437:
1431:
1429:
1423:
1422:
1420:
1419:
1414:
1408:
1406:
1402:
1401:
1399:
1398:
1392:
1386:
1379:
1377:
1373:
1372:
1370:
1369:
1364:
1359:
1353:
1348:
1343:
1337:
1331:
1330:
1329:
1324:
1318:
1307:
1302:
1297:
1291:
1284:
1282:
1278:
1277:
1275:
1274:
1269:
1264:
1259:
1253:
1247:
1242:
1236:
1230:
1224:
1218:
1212:
1205:
1203:
1199:
1198:
1193:
1191:
1190:
1183:
1176:
1168:
1162:
1161:
1144:
1138:
1130:
1122:
1114:
1099:
1090:
1080:
1071:
1070:External links
1068:
1065:
1064:
1033:
1002:
978:
957:
952:2024-02-09 at
939:
924:
912:
906:2012-05-27 at
893:
868:
841:
821:
811:. January 2000
796:
761:
736:
724:
694:
679:
678:
676:
673:
672:
671:
666:
661:
656:
649:
647:Export control
644:
639:
630:
627:
623:
622:
616:
610:
604:
603:
602:
599:
596:
593:
584:
578:
572:
553:
552:Classification
550:
549:
548:
542:
536:
514:
513:
487:
473:
463:country groups
459:
458:
424:
418:
412:
401:
398:
374:
371:
339:
338:Current status
336:
323:RSA_EXPORT1024
198:
195:
155:export control
146:
143:
141:
138:
88:
85:
84:
39:
37:
30:
24:
14:
13:
10:
9:
6:
4:
3:
2:
1736:
1725:
1722:
1720:
1717:
1715:
1712:
1710:
1707:
1706:
1704:
1685:
1682:
1679:
1676:
1674:
1671:
1669:
1666:
1664:
1661:
1659:
1656:
1654:
1651:
1649:
1646:
1645:
1643:
1639:
1632:
1629:
1627:
1624:
1622:
1619:
1617:
1614:
1612:
1609:
1607:
1604:
1603:
1601:
1597:
1591:
1588:
1587:
1585:
1581:
1575:
1572:
1570:
1567:
1566:
1564:
1560:
1557:
1553:
1547:
1544:
1542:
1539:
1537:
1534:
1533:
1531:
1527:
1521:
1518:
1516:
1513:
1511:
1508:
1506:
1503:
1501:
1498:
1496:
1493:
1491:
1488:
1486:
1483:
1481:
1478:
1476:
1473:
1471:
1468:
1466:
1463:
1461:
1458:
1456:
1453:
1451:
1448:
1446:
1443:
1441:
1438:
1436:
1435:Bouncy Castle
1433:
1432:
1430:
1428:
1424:
1418:
1415:
1413:
1410:
1409:
1407:
1403:
1396:
1393:
1390:
1387:
1384:
1381:
1380:
1378:
1374:
1368:
1365:
1363:
1360:
1357:
1354:
1352:
1349:
1347:
1344:
1341:
1338:
1335:
1332:
1328:
1327:OCSP stapling
1325:
1322:
1319:
1316:
1313:
1312:
1311:
1308:
1306:
1303:
1301:
1298:
1295:
1292:
1289:
1286:
1285:
1283:
1279:
1273:
1270:
1268:
1265:
1263:
1262:OCSP stapling
1260:
1257:
1254:
1251:
1248:
1246:
1243:
1240:
1237:
1234:
1231:
1228:
1225:
1222:
1219:
1216:
1213:
1210:
1207:
1206:
1204:
1200:
1196:
1189:
1184:
1182:
1177:
1175:
1170:
1169:
1166:
1159:
1155:
1151:
1148:
1145:
1142:
1139:
1137:
1135:
1131:
1129:
1127:
1123:
1121:
1119:
1115:
1113:
1109:
1106:
1104:
1100:
1098:
1096:
1091:
1088:
1084:
1081:
1079:
1078:
1074:
1073:
1069:
1054:on 2009-05-09
1050:
1043:
1037:
1034:
1023:on 2009-06-18
1019:
1012:
1006:
1003:
992:
988:
982:
979:
975:
972:
969:
966:
961:
958:
955:
954:archive.today
951:
948:
943:
940:
936:
933:
928:
925:
921:
916:
913:
909:
908:archive.today
905:
902:
897:
894:
883:on 2002-09-21
882:
878:
872:
869:
858:
851:
845:
842:
839:
834:
832:
830:
828:
826:
822:
810:
806:
800:
797:
792:
786:
771:
765:
762:
750:
746:
740:
737:
727:
721:
717:
713:
709:
705:
698:
695:
690:
684:
681:
674:
670:
667:
665:
662:
660:
657:
655:
654:
650:
648:
645:
643:
640:
638:
637:
633:
632:
628:
626:
620:
617:
614:
611:
608:
605:
600:
597:
594:
591:
590:
588:
585:
582:
579:
576:
573:
570:
567:
566:
565:
563:
559:
551:
546:
543:
540:
537:
534:
531:
530:
529:
527:
523:
519:
511:
507:
503:
499:
495:
491:
488:
485:
481:
477:
474:
471:
468:
467:
466:
464:
456:
452:
448:
444:
440:
436:
432:
428:
425:
422:
419:
416:
413:
410:
407:
406:
405:
399:
397:
395:
391:
386:
384:
380:
372:
370:
368:
364:
361:
357:
353:
349:
345:
337:
335:
332:
328:
324:
320:
316:
312:
308:
304:
300:
296:
292:
290:
286:
281:
276:
272:
268:
264:
260:
255:
252:
248:
245:
241:
237:
233:
231:
227:
223:
220:
216:
212:
203:
196:
194:
192:
187:
182:
180:
176:
172:
166:
164:
160:
156:
152:
144:
139:
137:
135:
131:
127:
126:code-breaking
123:
119:
118:United States
111:
107:
103:
99:
94:
81:
78:
70:
67:November 2022
60:
56:
52:
46:
45:
40:This article
38:
29:
28:
19:
1709:Computer law
1411:
1395:Secure Shell
1157:
1133:
1125:
1117:
1102:
1094:
1076:
1056:. Retrieved
1049:the original
1036:
1025:. Retrieved
1018:the original
1005:
994:. Retrieved
990:
981:
960:
942:
927:
915:
896:
885:. Retrieved
881:the original
871:
860:. Retrieved
856:
844:
813:. Retrieved
808:
799:
774:. Retrieved
764:
752:. Retrieved
748:
739:
729:, retrieved
707:
697:
683:
651:
634:
624:
618:
612:
606:
586:
580:
574:
568:
555:
544:
538:
532:
525:
521:
517:
515:
489:
475:
469:
462:
460:
426:
420:
414:
408:
403:
387:
376:
348:rogue states
341:
322:
309:signing the
307:Bill Clinton
299:Peter Junger
293:
279:
256:
234:
208:
183:
167:
159:Eastern bloc
148:
145:Cold War era
130:cryptography
122:World War II
115:
73:
64:
41:
1541:Convergence
1195:TLS and SSL
669:Crypto wars
502:North Korea
443:fire alarms
400:Terminology
331:open source
289:Lotus Notes
271:web browser
102:source code
100:encryption
1703:Categories
1668:Heartbleed
1058:2009-06-27
1027:2009-06-27
996:2021-09-30
887:2009-11-08
862:2022-10-10
850:"CCL5 PT2"
815:2014-01-06
776:2017-03-26
731:2023-08-12
675:References
451:automotive
280:RSA_EXPORT
51:improve it
18:RSA EXPORT
1663:goto fail
1475:MatrixSSL
1440:BoringSSL
1211:(TLS/SSL)
526:exception
352:terrorist
110:Back side
55:verifying
1599:Protocol
1529:Notaries
1505:SChannel
1480:mbed TLS
1470:LibreSSL
1455:cryptlib
1385:(DNSSEC)
1376:See also
1150:Archived
1108:Archived
974:Archived
968:Archived
950:Archived
935:Archived
904:Archived
785:cite web
629:See also
455:aviation
439:robotics
259:Netscape
226:Internet
151:Cold War
1520:wolfSSL
1515:stunnel
1500:s2n-tls
1490:OpenSSL
1405:History
1391:(IPsec)
392:on the
356:TEMPEST
140:History
49:Please
1678:POODLE
1631:POODLE
1626:Logjam
1611:BREACH
1583:Cipher
1562:Theory
1510:SSLeay
1495:Rustls
1460:GnuTLS
1323:(OCSP)
1290:(ACME)
1258:(HPKP)
1252:(HSTS)
1235:(DANE)
1229:(ALPN)
1217:(DTLS)
722:
508:, and
484:Russia
350:" and
244:40-bit
197:PC era
1658:FREAK
1621:DROWN
1616:CRIME
1606:BEAST
1450:BSAFE
1445:Botan
1397:(SSH)
1358:(PKI)
1317:(CRL)
1245:HTTPS
1241:(CAA)
1223:(SNI)
1089:page.
1052:(PDF)
1045:(PDF)
1021:(PDF)
1014:(PDF)
853:(PDF)
754:1 Dec
664:FREAK
619:5E992
613:5E002
607:5D992
587:5D002
581:5B002
575:5A992
569:5A002
510:Syria
506:Sudan
480:China
363:36494
242:made
163:CoCom
1465:JSSE
1342:(EV)
1336:(DV)
1296:(CA)
791:link
756:2017
720:ISBN
498:Iran
494:Cuba
482:and
447:HVAC
445:and
249:and
128:and
1485:NSS
712:doi
539:AT1
533:NS1
490:E:1
476:D:1
449:);
297:by
275:RSA
263:SSL
261:'s
251:RC4
247:RC2
219:PGP
217:'s
191:IBM
98:RSA
53:by
1705::
989:.
855:.
824:^
807:.
787:}}
783:{{
747:.
718:,
706:,
545:EI
504:,
500:,
496:,
453:,
441:,
396:.
360:FR
213:.
1187:e
1180:t
1173:v
1061:.
1030:.
999:.
890:.
865:.
818:.
793:)
779:.
758:.
714::
691:.
486:.
470:B
278:(
80:)
74:(
69:)
65:(
47:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.