38:
574:
552:. While object code will only work on a specific platform, source code can be ported to a different machine and recompiled there. For the same source code, object code can vary significantly—not only based on the machine for which it is compiled, but also based on performance optimization from the compiler.
693:
Access to the source code (not just the object code) is essential to modifying it. Understanding existing code is necessary to understand how it works and before modifying it. The rate of understanding depends both on the code base as well as the skill of the programmer. Experienced programmers have
800:, or the ease of modification. It is usually more cost-effective to build quality into the product from the beginning rather than try to add it later in the development process. Higher quality code will reduce lifetime cost to both suppliers and customers as it is more reliable and
812:
statements only if the code could execute more than once, and eliminating code that will never execute can also increase understandability. Many software development organizations neglect maintainability during the development phase, even though it will increase long-term costs.
644:
may find it helpful to review existing source code to learn about programming techniques. The sharing of source code between developers is frequently cited as a contributing factor to the maturation of their programming skills. Some people consider source code an expressive
807:
Maintainability is the quality of software enabling it to be easily modified without breaking existing functionality. Following coding conventions such as using clear function and variable names that correspond to their purpose makes maintenance easier. Use of
872:, open-source software has additional requirements: free redistribution, permission to modify the source code and release derivative works under the same license, and nondiscrimination between different uses—including commercial use. The free
858:. In 1974, the US Commission on New Technological Uses of Copyrighted Works (CONTU) decided that "computer programs, to the extent that they embody an author's original creation, are proper subject matter of copyright".
817:
is incurred when programmers, often out of laziness or urgency to meet a deadline, choose quick and dirty solutions rather than build maintainability into their code. A common cause is underestimates in
713:(improving the structure without changing functionality) and restructuring (improving structure and functionality at the same time). Nearly every change to code will introduce new bugs or unexpected
826:
courses do not emphasize it. Development engineers who know that they will not be responsible for maintaining the software do not have an incentive to build in maintainability.
739:
uses automated tools to detect problems with the source code. Many IDEs support code analysis tools, which might provide metrics on the clarity and maintainability of the code.
513:
away the details of the hardware, instead being designed to express algorithms that could be understood more easily by humans. As instructions distinct from the underlying
1584:
656:—blocks of text marked for the compiler to ignore. This content is not part of the program logic, but is instead intended to help readers understand the program.
386:
614:
The number of lines of source code is often used as a metric when evaluating the productivity of computer programmers, the economic value of a code base,
723:
by other developers are often used to scrutinize new code added to a project. The purpose of this phase is often to verify that the code meets style and
845:
743:
are tools that often enable programmers to step through execution while keeping track of which source code corresponds to each change of state.
819:
615:
2086:
2067:
2048:
2029:
1981:
1884:
1848:
1829:
1810:
1791:
1772:
1753:
1731:
1712:
1619:
1062:
1043:
1024:
1005:
1205:
935:
601:). The configuration management system also keeps track of which object code file corresponds to which version of the source code file.
702:
1186:
594:
561:
1859:
1895:
220:
1991:
Sen, Ravi; Subramaniam, Chandrasekar; Nelson, Matthew L. (2008). "Determinants of the Choice of Open Source
Software License".
502:
379:
46:
548:
can be directly executed by the machine and is generated automatically from the source code, often via an intermediate step,
1699:
976:
489:(simple instructions that could be directly executed by the processor). Machine language was difficult to debug and was not
50:
264:
1581:
570:. Part of the compiler's function is to link these files in such a way that the program can be executed by the hardware.
1582:
Apple
Computer, Inc. v. Franklin Computer Corporation Puts the Byte Back into Copyright Protection for Computer Programs
1556:
589:. With prologue comments indicated in red, inline comments indicated in green, and program statements indicated in blue.
470:
313:
955:
582:
578:
526:
121:
544:
Source code is the form of code that is modified directly by humans, typically in a high-level programming language.
372:
59:
1274:
869:
237:
208:
663:. Proprietary, secret source code and algorithms are widely used for sensitive government applications such as
453:
it. The translation process can be implemented three ways. Source code can be converted into machine code by a
292:
214:
42:
465:
is machine code ready for the computer. Alternatively, source code can be executed without conversion via an
1279:
822:, leading to insufficient resources allocated to development. A challenge with maintainability is that many
772:
736:
672:
510:
498:
490:
466:
345:
270:
149:
850:
The situation varies worldwide, but in the United States before 1974, software and its source code was not
360:
945:
855:
695:
446:
319:
97:
537:
needed to translate the source code automatically into machine code that can be directly executed on the
776:
764:
653:
518:
458:
450:
242:
225:
137:
127:
78:
54:
796:
is an overarching term that can refer to a code's correct and efficient behavior, its reusability and
2111:
1924:
1822:
Asset Attack
Vectors: Building Effective Vulnerability Management Strategies to Protect Organizations
940:
930:
865:
861:
823:
751:
Source code files in a high-level programming language must go through a stage of preprocessing into
688:
684:
675:
into the algorithm's methodology. The result is avoidance of public scrutiny of issues such as bias.
619:
423:
298:
1591:
in Golden Gate
University Law Review Volume 14, Issue 2, Article 3 by Jan L. Nussbaum (January 1984)
950:
731:. According to some estimates, code review dramatically reduce the number of bugs persisting after
493:
between different computer systems. Initially, hardware resources were scarce and expensive, while
469:. An interpreter loads the source code into memory. It simultaneously translates and executes each
114:
1701:
Zero Days, Thousands of Nights: The Life and Times of Zero-Day
Vulnerabilities and Their Exploits
895:
835:
760:
755:
before the instructions can be carried out. After being compiled, the program can be saved as an
706:
1765:
Software
Development, Design and Coding: With Patterns, Debugging, Unit Testing, and Refactoring
705:(IDE) to improve their productivity. IDEs typically have several features built in, including a
1202:
2082:
2063:
2044:
2025:
2008:
1977:
1960:
1942:
1880:
1844:
1825:
1806:
1787:
1768:
1749:
1727:
1708:
1182:
549:
538:
514:
485:
The first programmable computers, which appeared at the end of the 1940s, were programmed in
2000:
1950:
1932:
839:
809:
793:
788:
732:
710:
664:
586:
567:
486:
419:
92:
659:
Companies often keep the source code confidential in order to hide algorithms considered a
1588:
1209:
920:
915:
801:
728:
724:
598:
494:
274:
258:
154:
64:
477:. Bytecode is an intermediate representation of source code that is quickly interpreted.
1928:
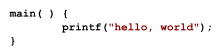
49:. The resulting program prints "hello, world" on the computer screen. This first known "
1955:
1912:
873:
814:
566:
Most programs do not contain all the resources needed to run them and rely on external
431:
232:
132:
2105:
900:
714:
635:
1896:"Source Code versus Object Code: Patent Implications for the Open Source Community"
1741:
910:
890:
752:
660:
646:
442:
187:
107:
1937:
983:
1724:
From
Mainframes to Smartphones: A History of the International Computer Industry
1270:
925:
905:
775:
instead of a compiler. An interpreter converts the program into machine code at
756:
720:
545:
328:
309:
177:
31:
2004:
1974:
Concise Guide to
Software Engineering: From Fundamentals to Application Methods
779:, which makes them 10 to 100 times slower than compiled programming languages.
1841:
Objective-C for
Absolute Beginners: iPhone, iPad and Mac Programming Made Easy
641:
533:. The invention of high-level programming languages was simultaneous with the
462:
427:
416:
144:
2012:
1946:
1568:
1557:"Copyright Law and Subject Matter Specificity: The Case of Computer Software"
709:
that can alert the programmer to common errors. Modification often includes
851:
740:
668:
631:
517:, software is therefore relatively recent, dating to these early high-level
473:. A method that combines compilation and interpretation is to first produce
400:
192:
68:
1964:
735:
is complete. Along with software testing that works by executing the code,
37:
17:
885:
534:
474:
454:
435:
182:
102:
573:
27:
Well-structured, human-readable text that encodes behavior of a computer
2079:
Unraveling
Software Maintenance and Evolution: Thinking Outside the Box
797:
768:
522:
506:
323:
279:
304:
1839:
Kaczmarek, Stefan; Lees, Brad; Bennett, Gary; Fisher, Mitch (2018).
1913:"A Quick Guide to Software Licensing for the Scientist-Programmer"
694:
an easier time understanding what the code does at a high level.
572:
530:
355:
36:
351:
288:
283:
30:
This article is about the software concept. For the film, see
2060:
Software Evolution and Maintenance: A Practitioner's Approach
1336:
1334:
771:
on the computer hardware. Some programming languages use an
763:(part of the operating system) can take this saved file and
1132:
1130:
1722:
Campbell-Kelly, Martin; Garcia-Swartz, Daniel D. (2015).
1248:
1246:
727:
standards and that it is a correct implementation of the
1363:
1361:
864:
is rarely distributed as source code. Although the term
1466:
1464:
1089:
1087:
982:. Bell Laboratories, Murray Hill, N. J. Archived from
1894:
Lin, Daniel; Sag, Matthew; Laurie, Ronald S. (2001).
618:
for projects in development, and the ongoing cost of
501:
became a bottleneck. This led to the introduction of
1911:
Morin, Andrew; Urban, Jennifer; Sliz, Piotr (2012).
1900:
Santa Clara Computer and High Technology Law Journal
1074:
1072:
1061:
sfn error: no target: CITEREFGabbrielliMartini2023 (
1042:
sfn error: no target: CITEREFGabbrielliMartini2023 (
1023:
sfn error: no target: CITEREFGabbrielliMartini2023 (
1004:
sfn error: no target: CITEREFGabbrielliMartini2023 (
876:of open-source software can speed up development.
2058:Tripathy, Priyadarshi; Naik, Kshirasagar (2014).
1671:, Free and Open Source Software (FOSS) Licensing.
1561:New York University Annual Survey of American Law
1056:
1037:
1018:
999:
1746:Big Breaches: Cybersecurity Lessons for Everyone
1403:
1275:"Overview of Software Maintenance and Evolution"
1221:
698:is sometimes used to speed up this process.
497:were cheaper. As programs grew more complex,
380:
8:
1664:
1632:
1506:
1494:
1352:
1325:
1313:
1301:
1173:
1171:
1169:
441:Since a computer, at base, only understands
1784:Software Engineering: A Methodical Approach
1680:
1455:
1443:
1391:
1379:
1340:
1148:
1648:
1105:
387:
373:
74:
1993:Journal of Management Information Systems
1954:
1936:
1555:Liu, Joseph P.; Dogan, Stacey L. (2005).
1265:
1263:
1261:
1179:Code Reading: The Open Source Perspective
717:, which require another round of fixes.
434:source code to control the behavior of a
1618:sfn error: no target: CITEREFBoyle2003 (
846:History of free and open-source software
630:Source code is also used to communicate
1820:Haber, Morey J.; Hibbert, Brad (2018).
1803:Software Quality: Concepts and Practice
1419:
967:
597:to track changes to source code files (
337:
250:
200:
164:
84:
77:
1877:Code/space: Software and Everyday Life
1600:Lemley, Menell, Merges and Samuelson.
1367:
1252:
1237:
1160:
1121:
820:software development effort estimation
1698:Ablon, Lillian; Bogart, Andy (2017).
1613:
1542:
1530:
1518:
1482:
1470:
1431:
1181:. Addison-Wesley Professional, 2003.
1136:
1093:
1078:
7:
2043:. Morgan & Claypool Publishers.
1875:Kitchin, Rob; Dodge, Martin (2011).
1860:"The Paradox of Source Code Secrecy"
1639:, Open Source versus Closed Source.
936:Package (package management system)
1999:(3). Informa UK Limited: 207–240.
703:integrated development environment
509:in the mid-1950s. These languages
338:Notable compilers & toolchains
25:
2022:Concepts of Programming Languages
701:Many software programmers use an
562:Software configuration management
870:public access to the source code
581:source code example. Written in
503:high-level programming languages
2024:(10 ed.). Addison-Wesley.
47:procedural programming language
1282:Department of Computer Science
1163:, pp. 249, 274, 280, 305.
977:"Programming in C: A Tutorial"
593:Software developers often use
1:
2041:Software: A Technical History
1151:, pp. 230–231, 233, 377.
1057:Gabbrielli & Martini 2023
1038:Gabbrielli & Martini 2023
1019:Gabbrielli & Martini 2023
1000:Gabbrielli & Martini 2023
1938:10.1371/journal.pcbi.1002598
1726:. Harvard University Press.
1199:Art and Computer Programming
295:target-specific initializer)
2020:Sebesta, Robert W. (2012).
956:Visual programming language
652:Source code often contains
583:object-oriented programming
122:Intermediate representation
2128:
2005:10.2753/mis0742-1222250306
1917:PLOS Computational Biology
1744:; Elbayadi, Moudy (2021).
843:
833:
786:
682:
559:
60:The C Programming Language
29:
2062:. John Wiley & Sons.
1858:Katyal, Sonia K. (2019).
1805:. John Wiley & Sons.
1782:Foster, Elvis C. (2014).
1602:Software and Internet Law
747:Compilation and execution
1972:O'Regan, Gerard (2022).
1763:Dooley, John F. (2017).
1507:Tripathy & Naik 2014
1495:Tripathy & Naik 2014
1353:Tripathy & Naik 2014
1326:Tripathy & Naik 2014
1314:Tripathy & Naik 2014
1302:Tripathy & Naik 2014
1208:20 February 2018 at the
671:behavior with a lack of
595:configuration management
1280:George Mason University
830:Copyright and licensing
737:static program analysis
634:between people – e.g.,
585:style, it demonstrates
499:programmer productivity
346:GNU Compiler Collection
271:Common Language Runtime
45:source code example, a
2039:Tracy, Kim W. (2021).
1801:Galin, Daniel (2018).
946:Source code repository
856:public domain software
696:Software visualization
590:
449:before a computer can
445:, source code must be
201:Compilation strategies
72:
57:from the seminal book
2077:Varga, Ervin (2018).
1240:, pp. 1186–1187.
854:and therefore always
576:
519:programming languages
226:Compile and go system
40:
1707:. Rand Corporation.
989:on 23 February 2015.
975:Kernighan, Brian W.
941:Programming language
931:Open-source software
868:literally refers to
866:open-source software
862:Proprietary software
824:software engineering
689:Software maintenance
685:Software development
642:Computer programmers
638:online or in books.
620:software maintenance
424:programming language
299:Java virtual machine
221:Tracing just-in-time
1976:. Springer Nature.
1929:2012PLSCB...8E2598M
1567:(2). Archived from
1497:, pp. 296–297.
1446:, pp. 68, 117.
1410:, pp. 348–349.
1328:, pp. 318–319.
1139:, pp. 122–123.
1112:, pp. 238–239.
1021:, pp. 520–521.
951:Syntax highlighting
667:, which results in
115:Optimizing compiler
1864:Cornell Law Review
1587:7 May 2017 at the
1458:, pp. 3, 268.
1382:, pp. 18, 21.
896:Coding conventions
836:Software copyright
802:easier to maintain
707:source-code editor
591:
73:
2088:978-3-319-71303-8
2069:978-0-470-60341-3
2050:978-1-4503-8724-8
2031:978-0-13-139531-2
1983:978-3-031-07816-3
1886:978-0-262-04248-2
1850:978-1-4842-3428-0
1831:978-1-4842-3627-7
1812:978-1-119-13449-7
1793:978-1-4842-0847-2
1774:978-1-4842-3153-1
1755:978-1-4842-6654-0
1733:978-0-674-28655-9
1714:978-0-8330-9761-3
616:effort estimation
550:assembly language
539:computer hardware
515:computer hardware
397:
396:
79:Program execution
69:Bell Laboratories
16:(Redirected from
2119:
2092:
2073:
2054:
2035:
2016:
1987:
1968:
1958:
1940:
1907:
1890:
1871:
1854:
1835:
1816:
1797:
1778:
1759:
1737:
1718:
1706:
1684:
1678:
1672:
1662:
1656:
1646:
1640:
1630:
1624:
1623:
1611:
1605:
1598:
1592:
1579:
1573:
1572:
1571:on 25 June 2021.
1552:
1546:
1540:
1534:
1528:
1522:
1516:
1510:
1504:
1498:
1492:
1486:
1480:
1474:
1468:
1459:
1453:
1447:
1441:
1435:
1429:
1423:
1417:
1411:
1401:
1395:
1389:
1383:
1377:
1371:
1365:
1356:
1350:
1344:
1338:
1329:
1323:
1317:
1311:
1305:
1299:
1293:
1292:
1290:
1288:
1273:(January 2018).
1267:
1256:
1250:
1241:
1235:
1229:
1219:
1213:
1195:
1189:
1175:
1164:
1158:
1152:
1146:
1140:
1134:
1125:
1119:
1113:
1103:
1097:
1091:
1082:
1076:
1067:
1066:
1054:
1048:
1047:
1035:
1029:
1028:
1016:
1010:
1009:
997:
991:
990:
988:
981:
972:
840:Software license
810:conditional loop
794:Software quality
789:Software quality
733:software testing
711:code refactoring
665:criminal justice
587:boilerplate code
487:machine language
461:. The resulting
420:computer program
389:
382:
375:
251:Notable runtimes
238:Transcompilation
85:General concepts
75:
63:originates from
21:
2127:
2126:
2122:
2121:
2120:
2118:
2117:
2116:
2102:
2101:
2100:
2095:
2089:
2076:
2070:
2057:
2051:
2038:
2032:
2019:
1990:
1984:
1971:
1923:(7): e1002598.
1910:
1893:
1887:
1874:
1857:
1851:
1838:
1832:
1819:
1813:
1800:
1794:
1781:
1775:
1762:
1756:
1740:
1734:
1721:
1715:
1704:
1697:
1693:
1688:
1687:
1679:
1675:
1663:
1659:
1647:
1643:
1631:
1627:
1617:
1612:
1608:
1599:
1595:
1589:Wayback Machine
1580:
1576:
1554:
1553:
1549:
1545:, pp. 7–8.
1541:
1537:
1529:
1525:
1521:, pp. 6–7.
1517:
1513:
1505:
1501:
1493:
1489:
1481:
1477:
1469:
1462:
1454:
1450:
1442:
1438:
1430:
1426:
1418:
1414:
1402:
1398:
1390:
1386:
1378:
1374:
1366:
1359:
1351:
1347:
1339:
1332:
1324:
1320:
1312:
1308:
1300:
1296:
1286:
1284:
1269:
1268:
1259:
1255:, p. 1195.
1251:
1244:
1236:
1232:
1220:
1216:
1210:Wayback Machine
1196:
1192:
1176:
1167:
1159:
1155:
1147:
1143:
1135:
1128:
1124:, p. 1194.
1120:
1116:
1104:
1100:
1092:
1085:
1077:
1070:
1060:
1055:
1051:
1041:
1036:
1032:
1022:
1017:
1013:
1003:
998:
994:
986:
979:
974:
973:
969:
964:
921:Obfuscated code
916:Markup language
882:
848:
842:
834:Main articles:
832:
791:
785:
749:
729:software design
725:maintainability
691:
681:
647:artistic medium
628:
622:after release.
612:
607:
599:version control
577:A more complex
564:
558:
495:human resources
483:
393:
273:(CLR) and
259:Android Runtime
155:Virtual machine
65:Brian Kernighan
35:
28:
23:
22:
15:
12:
11:
5:
2125:
2123:
2115:
2114:
2104:
2103:
2099:
2098:External links
2096:
2094:
2093:
2087:
2074:
2068:
2055:
2049:
2036:
2030:
2017:
1988:
1982:
1969:
1908:
1891:
1885:
1872:
1855:
1849:
1836:
1830:
1817:
1811:
1798:
1792:
1779:
1773:
1760:
1754:
1738:
1732:
1719:
1713:
1694:
1692:
1689:
1686:
1685:
1683:, p. 106.
1673:
1657:
1655:, p. 209.
1641:
1625:
1606:
1593:
1574:
1547:
1535:
1523:
1511:
1509:, p. 309.
1499:
1487:
1475:
1460:
1448:
1436:
1424:
1412:
1396:
1394:, p. 133.
1384:
1372:
1370:, p. 272.
1357:
1345:
1343:, p. 375.
1330:
1318:
1316:, p. 297.
1306:
1304:, p. 296.
1294:
1257:
1242:
1230:
1214:
1190:
1177:Spinellis, D:
1165:
1153:
1141:
1126:
1114:
1098:
1096:, p. 121.
1083:
1068:
1059:, p. 521.
1049:
1040:, p. 522.
1030:
1011:
1002:, p. 519.
992:
966:
965:
963:
960:
959:
958:
953:
948:
943:
938:
933:
928:
923:
918:
913:
908:
903:
898:
893:
888:
881:
878:
831:
828:
815:Technical debt
787:Main article:
784:
781:
748:
745:
715:ripple effects
680:
677:
627:
624:
611:
608:
606:
603:
560:Main article:
557:
554:
482:
479:
432:human readable
395:
394:
392:
391:
384:
377:
369:
366:
365:
364:
363:
358:
349:
340:
339:
335:
334:
333:
332:
326:
317:
307:
302:
296:
286:
277:
268:
262:
253:
252:
248:
247:
246:
245:
240:
235:
233:Precompilation
230:
229:
228:
223:
212:
203:
202:
198:
197:
196:
195:
190:
185:
180:
175:
167:
166:
162:
161:
160:
159:
158:
157:
152:
147:
142:
141:
140:
133:Runtime system
125:
119:
118:
117:
112:
111:
110:
95:
87:
86:
82:
81:
26:
24:
14:
13:
10:
9:
6:
4:
3:
2:
2124:
2113:
2110:
2109:
2107:
2097:
2090:
2084:
2080:
2075:
2071:
2065:
2061:
2056:
2052:
2046:
2042:
2037:
2033:
2027:
2023:
2018:
2014:
2010:
2006:
2002:
1998:
1994:
1989:
1985:
1979:
1975:
1970:
1966:
1962:
1957:
1952:
1948:
1944:
1939:
1934:
1930:
1926:
1922:
1918:
1914:
1909:
1905:
1901:
1897:
1892:
1888:
1882:
1879:. MIT Press.
1878:
1873:
1869:
1865:
1861:
1856:
1852:
1846:
1842:
1837:
1833:
1827:
1823:
1818:
1814:
1808:
1804:
1799:
1795:
1789:
1785:
1780:
1776:
1770:
1766:
1761:
1757:
1751:
1747:
1743:
1742:Daswani, Neil
1739:
1735:
1729:
1725:
1720:
1716:
1710:
1703:
1702:
1696:
1695:
1690:
1682:
1677:
1674:
1670:
1668:
1661:
1658:
1654:
1652:
1645:
1642:
1638:
1636:
1629:
1626:
1621:
1616:, p. 45.
1615:
1610:
1607:
1603:
1597:
1594:
1590:
1586:
1583:
1578:
1575:
1570:
1566:
1562:
1558:
1551:
1548:
1544:
1539:
1536:
1532:
1527:
1524:
1520:
1515:
1512:
1508:
1503:
1500:
1496:
1491:
1488:
1484:
1479:
1476:
1473:, p. 12.
1472:
1467:
1465:
1461:
1457:
1452:
1449:
1445:
1440:
1437:
1434:, p. 26.
1433:
1428:
1425:
1422:, p. 28.
1421:
1416:
1413:
1409:
1407:
1400:
1397:
1393:
1388:
1385:
1381:
1376:
1373:
1369:
1364:
1362:
1358:
1355:, p. 94.
1354:
1349:
1346:
1342:
1337:
1335:
1331:
1327:
1322:
1319:
1315:
1310:
1307:
1303:
1298:
1295:
1283:
1281:
1276:
1272:
1266:
1264:
1262:
1258:
1254:
1249:
1247:
1243:
1239:
1234:
1231:
1228:, p. 68.
1227:
1225:
1218:
1215:
1211:
1207:
1204:
1200:
1194:
1191:
1188:
1187:0-201-79940-5
1184:
1180:
1174:
1172:
1170:
1166:
1162:
1157:
1154:
1150:
1145:
1142:
1138:
1133:
1131:
1127:
1123:
1118:
1115:
1111:
1109:
1102:
1099:
1095:
1090:
1088:
1084:
1080:
1075:
1073:
1069:
1064:
1058:
1053:
1050:
1045:
1039:
1034:
1031:
1026:
1020:
1015:
1012:
1007:
1001:
996:
993:
985:
978:
971:
968:
961:
957:
954:
952:
949:
947:
944:
942:
939:
937:
934:
932:
929:
927:
924:
922:
919:
917:
914:
912:
909:
907:
904:
902:
901:Free software
899:
897:
894:
892:
889:
887:
884:
883:
879:
877:
875:
871:
867:
863:
859:
857:
853:
852:copyrightable
847:
841:
837:
829:
827:
825:
821:
816:
811:
805:
803:
799:
795:
790:
782:
780:
778:
774:
770:
766:
762:
758:
754:
746:
744:
742:
738:
734:
730:
726:
722:
718:
716:
712:
708:
704:
699:
697:
690:
686:
678:
676:
674:
670:
666:
662:
657:
655:
650:
648:
643:
639:
637:
636:code snippets
633:
626:Communication
625:
623:
621:
617:
609:
604:
602:
600:
596:
588:
584:
580:
575:
571:
569:
563:
555:
553:
551:
547:
542:
540:
536:
532:
528:
524:
520:
516:
512:
508:
504:
500:
496:
492:
488:
480:
478:
476:
472:
468:
464:
460:
456:
452:
448:
444:
439:
437:
433:
429:
425:
422:written in a
421:
418:
414:
410:
406:
402:
390:
385:
383:
378:
376:
371:
370:
368:
367:
362:
359:
357:
353:
350:
347:
344:
343:
342:
341:
336:
330:
327:
325:
321:
318:
315:
311:
308:
306:
303:
300:
297:
294:
290:
287:
285:
281:
278:
276:
272:
269:
266:
263:
260:
257:
256:
255:
254:
249:
244:
243:Recompilation
241:
239:
236:
234:
231:
227:
224:
222:
219:
218:
216:
213:
210:
209:Ahead-of-time
207:
206:
205:
204:
199:
194:
191:
189:
186:
184:
181:
179:
176:
174:
171:
170:
169:
168:
165:Types of code
163:
156:
153:
151:
148:
146:
143:
139:
136:
135:
134:
131:
130:
129:
126:
123:
120:
116:
113:
109:
106:
105:
104:
101:
100:
99:
96:
94:
91:
90:
89:
88:
83:
80:
76:
70:
66:
62:
61:
56:
52:
48:
44:
39:
33:
19:
2081:. Springer.
2078:
2059:
2040:
2021:
1996:
1992:
1973:
1920:
1916:
1903:
1899:
1876:
1867:
1863:
1840:
1821:
1802:
1783:
1764:
1745:
1723:
1700:
1681:O'Regan 2022
1676:
1666:
1660:
1650:
1644:
1634:
1628:
1609:
1601:
1596:
1577:
1569:the original
1564:
1560:
1550:
1538:
1533:, p. 7.
1526:
1514:
1502:
1490:
1485:, p. 5.
1478:
1456:O'Regan 2022
1451:
1444:O'Regan 2022
1439:
1427:
1420:Sebesta 2012
1415:
1405:
1399:
1392:O'Regan 2022
1387:
1380:O'Regan 2022
1375:
1348:
1341:O'Regan 2022
1321:
1309:
1297:
1285:. Retrieved
1278:
1271:Offutt, Jeff
1233:
1223:
1217:
1198:
1193:
1178:
1156:
1149:O'Regan 2022
1144:
1117:
1107:
1101:
1081:, p. 1.
1052:
1033:
1014:
995:
984:the original
970:
911:Machine code
891:Code as data
860:
849:
806:
792:
753:machine code
750:
721:Code reviews
719:
700:
692:
679:Modification
673:transparency
661:trade secret
658:
651:
640:
629:
613:
592:
565:
556:Organization
543:
484:
443:machine code
440:
412:
408:
407:, or simply
404:
398:
215:Just-in-time
188:Machine code
172:
108:Compile time
58:
2112:Source code
1368:Dooley 2017
1253:Katyal 2019
1238:Katyal 2019
1161:Foster 2014
1122:Katyal 2019
926:Object code
906:Legacy code
874:reusability
798:portability
773:interpreter
757:object file
546:Object code
467:interpreter
430:writes the
405:source code
329:Zend Engine
310:Objective-C
178:Object code
173:Source code
150:Interpreter
98:Translation
51:Hello world
32:Source Code
1843:. Apress.
1824:. Apress.
1786:. Apress.
1767:. Apress.
1748:. Apress.
1614:Boyle 2003
1543:Varga 2018
1531:Varga 2018
1519:Varga 2018
1483:Varga 2018
1471:Varga 2018
1432:Galin 2018
1404:Kaczmarek
1222:Kaczmarek
1203:ONLamp.com
1137:Tracy 2021
1094:Tracy 2021
1079:Tracy 2021
962:References
844:See also:
683:See also:
632:algorithms
610:Estimation
511:abstracted
481:Background
463:executable
447:translated
428:programmer
417:plain text
145:Executable
43:C-language
18:Sourcecode
2013:0742-1222
1947:1553-7358
741:Debuggers
669:black box
568:libraries
535:compilers
471:statement
459:assembler
401:computing
354:and
322:and
312:and
282:and
193:Microcode
128:Execution
2106:Category
1965:22844236
1604:, p. 34.
1585:Archived
1212:, (2005)
1206:Archived
886:Bytecode
880:See also
777:run time
767:it as a
759:and the
654:comments
605:Purposes
521:such as
505:such as
491:portable
475:bytecode
455:compiler
436:computer
267:(Erlang)
183:Bytecode
103:Compiler
71:in 1974.
1956:3406002
1925:Bibcode
1870:: 1183.
1691:Sources
783:Quality
769:process
765:execute
523:Fortran
507:Fortran
451:execute
415:, is a
324:Node.js
280:CPython
138:Runtime
67:in the
55:snippet
41:Simple
2085:
2066:
2047:
2028:
2011:
1980:
1963:
1953:
1945:
1906:: 235.
1883:
1847:
1828:
1809:
1790:
1771:
1752:
1730:
1711:
1667:et al.
1665:Morin
1651:et al.
1635:et al.
1633:Morin
1406:et al.
1224:et al.
1185:
1108:et al.
761:loader
529:, and
457:or an
413:source
305:LuaJIT
217:(JIT)
1705:(PDF)
1287:5 May
987:(PDF)
980:(PDF)
531:Cobol
356:Clang
348:(GCC)
331:(PHP)
314:Swift
301:(JVM)
261:(ART)
211:(AOT)
2083:ISBN
2064:ISBN
2045:ISBN
2026:ISBN
2009:ISSN
1978:ISBN
1961:PMID
1943:ISSN
1881:ISBN
1845:ISBN
1826:ISBN
1807:ISBN
1788:ISBN
1769:ISBN
1750:ISBN
1728:ISBN
1709:ISBN
1669:2012
1653:2008
1649:Sen
1637:2012
1620:help
1408:2018
1289:2024
1226:2018
1183:ISBN
1110:2001
1106:Lin
1063:help
1044:help
1025:help
1006:help
838:and
687:and
579:Java
527:Lisp
426:. A
409:code
361:MSVC
352:LLVM
289:crt0
284:PyPy
275:Mono
265:BEAM
124:(IR)
93:Code
2001:doi
1951:PMC
1933:doi
1868:104
804:.
541:.
411:or
399:In
2108::
2007:.
1997:25
1995:.
1959:.
1949:.
1941:.
1931:.
1919:.
1915:.
1904:18
1902:.
1898:.
1866:.
1862:.
1565:61
1563:.
1559:.
1463:^
1360:^
1333:^
1277:.
1260:^
1245:^
1201:"
1168:^
1129:^
1086:^
1071:^
649:.
525:,
438:.
403:,
320:V8
316:'s
53:"
2091:.
2072:.
2053:.
2034:.
2015:.
2003::
1986:.
1967:.
1935::
1927::
1921:8
1889:.
1853:.
1834:.
1815:.
1796:.
1777:.
1758:.
1736:.
1717:.
1622:)
1291:.
1197:"
1065:)
1046:)
1027:)
1008:)
388:e
381:t
374:v
293:C
291:(
34:.
20:)
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.