119:
277:
22:
220:
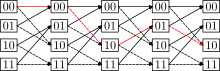
141:) with every node at almost every time connected to at least one node at an earlier and at least one node at a later time. The earliest and latest times in the trellis have only one node (hence the "almost" in the preceding sentence).
318:
337:
261:
352:
342:
105:
39:
43:
86:
58:
134:
347:
311:
65:
187:
Ryan, M. S., & Nudd, G. R. (1993). The viterbi algorithm. University of
Warwick, Department of Computer Science.
32:
153:
254:
72:
304:
168:
54:
118:
205:
161:
145:
247:
284:
200:
123:
157:
288:
231:
79:
331:
276:
227:
21:
149:
219:
117:
15:
167:
The trellis graph is named for its similar appearance to an
292:
235:
46:. Unsourced material may be challenged and removed.
144:Trellises are used in encoders and decoders for
137:whose nodes are ordered into vertical slices (
312:
255:
152:. They are also the central datatype used in
8:
319:
305:
262:
248:
106:Learn how and when to remove this message
180:
7:
273:
271:
216:
214:
44:adding citations to reliable sources
291:. You can help Knowledge (XXG) by
234:. You can help Knowledge (XXG) by
14:
275:
218:
20:
31:needs additional citations for
1:
338:Application-specific graphs
369:
270:
213:
353:Telecommunications stubs
343:Telecommunication theory
283:This article related to
230:-related article is a
126:
169:architectural trellis
121:
206:Trellis quantization
162:Hidden Markov Models
154:Baum–Welch algorithm
146:communication theory
55:"Trellis" graph
40:improve this article
122:Convolutional code
348:Graph theory stubs
285:telecommunications
201:Trellis modulation
127:
300:
299:
243:
242:
158:Viterbi Algorithm
116:
115:
108:
90:
360:
321:
314:
307:
279:
272:
264:
257:
250:
222:
215:
188:
185:
111:
104:
100:
97:
91:
89:
48:
24:
16:
368:
367:
363:
362:
361:
359:
358:
357:
328:
327:
326:
325:
269:
268:
211:
197:
192:
191:
186:
182:
177:
124:trellis diagram
112:
101:
95:
92:
49:
47:
37:
25:
12:
11:
5:
366:
364:
356:
355:
350:
345:
340:
330:
329:
324:
323:
316:
309:
301:
298:
297:
280:
267:
266:
259:
252:
244:
241:
240:
223:
209:
208:
203:
196:
193:
190:
189:
179:
178:
176:
173:
114:
113:
28:
26:
19:
13:
10:
9:
6:
4:
3:
2:
365:
354:
351:
349:
346:
344:
341:
339:
336:
335:
333:
322:
317:
315:
310:
308:
303:
302:
296:
294:
290:
286:
281:
278:
274:
265:
260:
258:
253:
251:
246:
245:
239:
237:
233:
229:
224:
221:
217:
212:
207:
204:
202:
199:
198:
194:
184:
181:
174:
172:
170:
165:
163:
159:
155:
151:
147:
142:
140:
136:
132:
125:
120:
110:
107:
99:
88:
85:
81:
78:
74:
71:
67:
64:
60:
57: –
56:
52:
51:Find sources:
45:
41:
35:
34:
29:This article
27:
23:
18:
17:
293:expanding it
282:
236:expanding it
228:graph theory
225:
210:
183:
166:
143:
138:
130:
128:
102:
96:January 2021
93:
83:
76:
69:
62:
50:
38:Please help
33:verification
30:
332:Categories
175:References
150:encryption
66:newspapers
195:See also
156:or the
131:trellis
80:scholar
82:
75:
68:
61:
53:
287:is a
226:This
135:graph
133:is a
87:JSTOR
73:books
289:stub
232:stub
160:for
148:and
139:time
59:news
42:by
334::
171:.
164:.
129:A
320:e
313:t
306:v
295:.
263:e
256:t
249:v
238:.
109:)
103:(
98:)
94:(
84:·
77:·
70:·
63:·
36:.
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.