178:
meaning out of it. The concept of immaterial labour opens the discussion of the controversy between Big Data
Corporations and users that highlights the exploitation of online users. The concept highlights the ability to use online resources to produce user-generated content out of online platforms such as Facebook, and Google, while being consumers of the products. These products include "knowledge, information, communication, a relationship, or emotional space." Immaterial labour focuses on the compensation of users who do work for Big Data corporations. Immaterial labour which is also deemed free labour. On the Internet, immaterial labour can be considered from a wide variety of actions. It includes posting on Facebook to searching on Google. The introduction of immaterial labour opens up several branches of similar niche concepts that relate to pre-release file sharing. These various relations between Big Data companies and users create various economies can be seen to inhabit pre-release file sharing.
353:
Act: broadcast transmissions, subscription transmissions, and on-demand transmissions. The
Digital Millennium Copyright Act of 1998 acknowledges that it must be revised in order to cater to contemporary material online and acknowledge that "webcasting" should be included as eligible non subscription transmissions. The Digital Copyright Act of 1998 states that a single ephemeral or digital recording acts as the sole copyright of a file under section 112 of the Copyright Act. This allows only one file of a created material to be covered by the Digital Millennium Copyright Act and any other material created in its likeness is excluded from the Digital Millennium Copyright Act's protection which can result in a multitude of regulatory fines.
204:
to pre-released material or being sent a promotional recording and it being streamed online are ways that pre-released files are first distributed. Albums sent to journalist of music magazines such as
Pitchfork, and Grizzly Bear and other online stream services that act as "leak sources" which after being pre-released files are streamed online, are recorded by users and reproduced. The recordings are transfigured into various music file formats and circulated via file-sharing platforms such as Zshare and Mediafire, BitTorrent and various forums. Searching for leaked material can be done by searching in a Google query; the albums name, followed by leak.
269:
projectionist. There are several potential instances that are considerable to insider attacks: Any unauthorized copying of a film in the editing room or nearby. Any copying of a critic's advanced copy of a movie. These copies can be titled
Screener Copy or a specific name to a professional. Unauthorized copies to an award's judge which are presented with 'for your consideration'. Any copying of a promotional copy or preview screening copy. Any copy that is recorded by a projectionist. Any unauthorized copying of a physical medium such as DVD" and other formats.
332:
344:
European part". Hackers released "sensitive information such as actor details, username and passwords of twitter accounts, script details, and emails". HBO is seen to address the hacker situation by not paying ransom as well as taking action for future seasons. "Game of
Thrones producer have taken preliminary action by planning to not give actors scripts for the next season (season eight) with scripts voiced to actors while acting".
397:
addresses to
Voltage Pictures. The Federal Court of Canada ordered Voltage pictures to pay all cost Teksavy in abiding to this Order. TekSavvy quoted Voltage Pictures $ 346,480.68 to reveal the names of the suspected downloaders. Voltage pictures counter-quoted based on their calculations, $ 884. The Federal Court of Canada finalized the cost of $ 21,557.50 for the list.
238:
theater attendance and sales. In a study regarding the leakage of movies, out of "312 films, 183 were located in file sharing sites, whilst 285 films, 70% of these films were leaked by industry insiders". .Pre-release file-sharing considers two instances of piracy with regards to circulation: prior to release in theaters, and prior to release in stores.
31:
414:(GCHQ) have monitored file sharing platforms. Out of the purpose to monitor various online peer-to-peer file sharing platforms for illegal activity such as Kazaa and BitTorrent various web tools and applications were created in order to identify pre-released files. In The Snowden Leak revealed that the NSA was monitoring
464:
LEVITATION was released to CBC after
Snowden's Leak. LEVITATION was a project made by the Canadian Agency Communications Security Establishment. It's sole purpose is to monitor downloads from all over the world as an anti-terrorism measure. LEVITATION monitors over 10 to 15 million downloads everyday
277:
In 2003, an incomplete version of The Hulk was released over the
Internet two weeks before it was due in theaters June 20, 2013. The leak was considered an insider's leak. It was leaked by a member of a Manhattan print advertising firm, which then was leaked to a friend of the colleague. After it was
254:
In 2009 X-Men
Origins: Wolverine was set to be released May 1 2009 in US theatres. Prior to this date an incomplete version of the movie was released over the Internet that consisted of early visual effects. The FBI tracked the spread of the film to Gilberto Sanchez. Sanchez was sentenced by District
168:
Liebowitz's study focused on vacation-related supply stock which was later criticized by
Oberholzer and Strumpf who surmised that Leibowitz's measures were not relevant to the study of pre-release file-sharing on music sales, and required revising. In contemporary usage file-sharing can be seen to be
298:
Pre-release file sharing studies in streaming services focused on the file and its ownership. It is defined as a file service where ownership is switched. The debate of file sharing and streaming focuses on downloading behavior and ethical legal perceptions. Studies have shown that there are ethical
217:
also known as GWW for short. in the summer of 1968. California radio stations were playing the pre-release version of "This Wheel's on Fire" before it had been released in stores. In the Rolling Stone magazine, a publisher had written an article about the song, reporting that it was not the official
185:
and cultural economy. Harvey describes people who contribute to the circulation of pre-released files as "unpaid promotional delegates".The circulation of pre-released files begins to be immaterial labour when users actively promote albums in online communities. This includes posting links in forums
352:
Pre-release file sharing is mainly targeted by the Digital Millennium Copyright Act. The Digital Millennium Copyright Act (DMCA) triggers when files are accessed without proper license or permission. The Digital Millennium Copyright Act of 1998 lists 3 exceptions to the Digital Millennium Copyright
289:
It is noted that there is a difference between files shared rooted from insider attacks and outsider attacks that considers freshness, and quality. Insider attacks are noted to have higher quality compared to outsider attacks. While unauthorized files may be larger, in outsider leaked files, there
268:
There are two types of scenario leaks in movie production: Insider Attacks and Outsider Attacks. Insider attacks occur when a trusted individual participates in unauthorized distribution of a film. These individuals can work various positions in the film industry; and editor, advertiser, or cinema
237:
A movie leak is a type of unauthorized pre-release of a film that raises the issue of security in the film industry. The issue considers stages in the production and distribution of a film that allows access to film materials and its distribution. The pre-release of a film is considered a threat to
226:
The study of pre-release file-sharing has gathered much attention. Studies that have published material of a detrimental causality with pre-release file sharing and film have generally studied after the fact of leakage. In studies that have looked at the "pre-release focusing on prior release there
203:
Album leaking has been seen to act as a promotional tool for music through the creation of "Hype". "Hype" is "the state of anticipation generated through the circulation of promotion, resulting in the crisis of value". Being invited to a listening party was one way in which one was able to listen
147:
is different due to its structure. BitTorrent is a data transfer protocol. It operates through splitting large files into smaller files and Torrent software that uploads, downloads and reconstructs the small files back together. The file type ".torrent" is a BitTorrent file that is used to organize
366:
The infringements that can be considered in sharing of pre-released files vary from degree to fine in the same manner as copyrighted files. In 2008, the Digital Millennium Copyright Act enacted the "personal use download fine. In 2009 a fine of $ 1.9 million was charged to a woman from Minnesota.
343:
was hacked by a hacker of the alias 'Mr Smith', resulting in pre-released video files of several episodes of the 7th season; two of which were before their release over the HBO network: Episode 4 of Game of Thrones was hacked in whilst possession of Sky India, while episode 6 was hacked from HBO's
112:
There are various technologies are involved in pre-release file-sharing. File-Transfer Protocols (FTP) are a type of network that exist by one computer being a host server, whilst other computers log into a FTP Client to connect to the host computer. Peer-to-peer networks (P2P) are similar to FTP
241:
The stream of production begins when different pieces of a movie: video, audio, enter the editing room. In the editing room the physical portion of the film is created. In a post-production process the film may be sent to other companies to do post production effects. The distribution process is
396:
five months before its release. Under Rule 238 of the Federal Courts rules SOR/98-106, the Federal Court of Canada ordered TekSavvy to reveal the names of customers who downloaded movies illegally. On February 20th 2014, The Federal Court of Canada ordered TekSavvy to provide details such as IP
405:
File sharing at its core is not illegal, and occurs when a second-party of the copyrighted material circulates the file without permission. The merit of file sharing relies on its content. Between the uploader and the downloader are online entities and regulation that monitor the circulation of
177:
The discussion of pre-release file sharing as digital labour stems from Communication Studies scholars concept of "immaterial labour". Immaterial labour relies on the commodification of social relationships, where subjectivity becomes raw material and free labour is the process in which creates
375:
A person who is charged under this pretense faces $ 500 per download". Internet service providers also survey traffic of packets in search for files of the same nature of thier customers. Internet service providers first send out a notice for copyright infringement. These notices can result in
104:. It refers to the relationship between privately owned content in media and online users. Illegal pre-released file sharing is file sharing that has been unofficially published outside the official publishing streams of a file by its manufacturer and is accessed and shared over the Internet.
245:
Industry insiders are trusted individuals or companies who receive copies of the film prior to release. These people include "critics and award judges. Employees at cinemas can also be considered to handle film prior to release." "Advertisers who receive pre-released materials can also be
212:
Album leaks are not a new phenomena in the music industry and have occurred earlier than the 2000s outside of online file-sharing. The earliest pre-release album leak dates back to before the invent of the mp3 file format. The earliest album leak recognized is Bob Dylan's
218:
release of the song and in response wrote an article called, "Dylan's Basement Tape Should be Released". Later copies of pre-released Wonder, having 23 songs were released in record stores in an album package that was decorated in white.
376:
charges from $ 200 to $ 10,000. Although Internet service providers may send out 'notice of notice' for infringement Industry Canada deems it nonobligatory to pay a copyright and act as a way to "reduce reoccurring offenses". A
476:
One instance of a NSA Marina database was used to scan through Facebook profile and is sent a list of potential threats to CSE's Office of Counter Terrorism. As of 2012 there have been two successes for the LEVITATION.
194:
An album leak is a method of pre-release file-sharing that entails a music album being circulated before its due date in stores. This type of pre-release file-sharing does not replace the official release of an album.
430:
GRIMPLATE was a NSA initiative that monitored the Department of Defense employees use on BitTorrent to see if the use of BitTorrent could be considered illegal activity to prevent further use of BitTorrent.
473:. Issues of privacy arise from the root of information gathered by telecommunication providers such as cable companies. Once a user is found, their IP address can be mined and put into GCHQ's MUTANT BROTH.
165:
was created and shut down in 2001. Other peer-to-peer applications were created. Studies have shown the effects of Pre-Release File-Sharing to be either beneficial to album sales or detrimental.
286:
Outsider attacks on film consider a "cinema goer's cam recordings at a cinema, unauthorized copying of a physical copying of a film, or copying from cable, satellite or broadcast TV".
1646:
1120:
Byers, Cranor, Cronin, Korman and McDaniel, Simon, Lorrie, Eric, Dave, and Patrick (2004). "An Analysis of security vulnurabilities in the movie production and distribution process".
1800:
1736:
1664:
1622:
1228:
1166:
1065:
1007:
961:
848:
566:
227:
have been conclusion that pre-release file sharing is detrimental to sales as well. The delay of a film's release can habor up to 7% of revenue and box office revenue by 19%".
1604:
1790:
1156:
1299:
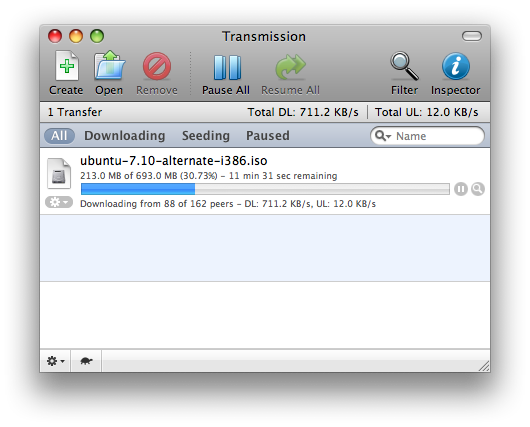
148:
the process by helping users connect to each other. uTorrent for PC, Transmission for Mac, and Vuzer or KTorrent for Linux are examples of BitTorrent software.
985:
1436:
1533:
242:
associated with business aspects which include the marketing of the film and its release. The final edit of the film is what is shown in theaters.
439:
The British's Government Communications Headquarters had created an app called DIRTY RAT that was able to identify a user and their downloads on
1392:
759:
411:
278:
leaked to Kerry Gonzalez who faced charges from posting the file online. He was sentenced to 6 months of house arrest and 3 years probation.
422:. The NSA had an initiative for monitoring file sharing networks called GRIMPLATE whilst the GCHQ created an initiative called DIRTY RAT.
131:
117:
allow users to upload files into an online storage from their web browser or mobile application which can be downloaded later by users..
169:
a new format compared to old formats which assert the dominance of file-sharing as a medium for music greater than vinyl and cassettes.
1714:
1764:
367:
The Copyright Act 2005 made pre-release of film a felony that could give up to 5 years in prison and 10 years on a second charge.
1681:
1272:
299:
conflicts of users ethical perceptions and acceptance to pirate files. Where streaming can be seen to be legal on sites such as
1555:
113:
servers in that each computer acts as a host computer, and a client computer. Other community based online services such as
161:
Pre-Release file sharing has undergone much study over the years. In 1999, a peer-to-peer network sharing platform called
1458:
1026:
Ma, Liye (3 September 2014). "An Empirical Analysis of the Impact of Pre-Release Movie Piracy on Box Office Revenue".
451:
PLAGUE RAT was another GCHQ application that had the ability to tailor search results to a user on the eMule network.
1578:
1369:
407:
1300:"Film fan sentenced to year's prison term for leaking X-Men: Wolverine online a month before general release"
813:
Coté and Pybus, Mark and Jennifer (2011). "Learning to Immaterial Labour 2.0:Facebook and Social Networks".
39:
17:
1338:
1133:
1039:
935:
877:
822:
720:
707:
Oberholzer-Gee and Strumpf, Felix and Koleman. "The effect of file sharing on record sales, revisited".
665:
499:
583:
1325:
Hansen, Jared (September 2013). "The Role of Restrictiveness of Ethical and Legal Awareness Sharing".
120:
101:
545:
494:
Hammond, Robert G. (7 March 2014). "Profit Leak? Pre-Release File Sharing and the Music Industry∗".
182:
143:
Aside from the other network sharing technologies that exist using client and host based networks,
89:
1784:
1408:
1206:
769:
609:
214:
660:
Liebowitz, Stan J. (March 2005). "File Sharing: Creative Destruction or just Plain Destruction".
635:
51:
To find the right sandbox for your assignment, visit your Dashboard course page and follow the
1647:"Voltage Pictures Has To Pay $ 22k To Canadian ISP If It Wants Names For Its Shakedown Scheme"
1245:
755:
1186:
922:
Harvey, Eric (2012). "Collective anticipation: The contested circulation of an album leak".
385:
1506:
331:
1421:
1354:
1218:
1149:
1055:
951:
893:
838:
796:
785:
736:
693:
681:
527:
515:
340:
290:
is a degradation to quality where file size can be smaller due to poor video compression.
960:
The named reference "Harvey" was defined multiple times with different content (see the
1735:
The named reference "Icept" was defined multiple times with different content (see the
1621:
The named reference "Globe" was defined multiple times with different content (see the
1165:
The named reference "Byers" was defined multiple times with different content (see the
1006:
The named reference "Pitch" was defined multiple times with different content (see the
847:
The named reference "Pybus" was defined multiple times with different content (see the
1663:
The named reference "Tech" was defined multiple times with different content (see the
565:
The named reference "life" was defined multiple times with different content (see the
60:
1799:
The named reference "CSE" was defined multiple times with different content (see the
1534:"No, you do not have to pay a 'settlement fee' if you get an illegal download notice"
1227:
The named reference "CNN" was defined multiple times with different content (see the
864:
Terranova, Tiziana (2000). "Free Labour: Producing Culture for the Digital Economy".
1064:
The named reference "Ma" was defined multiple times with different content (see the
81:
1481:
308:
1682:"NSA Spied on Early File-Sharing Networks, Including BitTorrent - TorrentFreak"
130:
470:
466:
144:
85:
986:"Bob Dylan's Great White Wonder: The Story of the World's First Album Leak"
119:
389:
419:
316:
300:
181:
Terranova, who coins the "digital economy" as an intersect between the
162:
114:
93:
1605:"Court orders Canadian ISP to reveal customers who downloaded movies"
97:
1395:. Guardian News and Media Limited. Guardian News and Media Limited
440:
415:
380:
TEKSAVY and JOHN DOEs vs Voltage Pictures - The Hurt Locker (2008)
330:
320:
129:
1765:"Canadian spies track millions of downloads daily: Snowden files"
1715:"NSA BROKE THE ENCRYPTION ON FILE-SHARING APPS KAZAA AND EDONKEY"
1437:"'Game Of Thrones' Actors Will Not Be Given Scripts Next Season"
312:
1273:"'X-Men: Wolverine' Pirate Sentenced to Year in Federal Prison"
1246:"The Story of Gilberto Sanchez, the Man Who Leaked 'Wolverine'"
1507:"Report Says Canadian DMCA To Include $ 500 Fine Per Download"
304:
25:
1393:"Game of Thrones: HBO hackers threaten leak of season finale"
1370:"HBO Hacks and Leaks: How Much Have They Hurt the Business?"
47:
not the sandbox where you should draft your assigned article
752:
Digital labor : the Internet as playground and factory
546:"The beginner's guide to Internet and network file sharing"
1556:"New regulations about illegal downloading go into effect"
55:
link for your assigned article in the My Articles section.
1252:. The New York Times Company. The New York Times Company
406:
online materials such as the DMCA. Entities such as the
1306:. Associated Newspapers Ltd. Associated Newspapers Ltd
1459:"File Sharing vs. Online Streaming: What's the Diff?"
1187:"'X-Men Origins: Wolverine' leaked to Web - CNN.com"
1579:"Some of the biggest pre-release movie leaks ever"
1327:Journal of the Association for Information Systems
924:Convergence: The International Journal of Research
815:Cognitive Capitalism, Education and Digital Labour
186:as well as uploading files to file sharing sites.
43:. You can use it for testing or practicing edits.
1279:. The Hollywood Reporter. The Hollywood Reporter
294:Pre-Release File Sharing and Streaming Services
8:
1789:: CS1 maint: multiple names: authors list (
1461:. The Curators of the University of Missouri
173:Pre-Release File Sharing as Digital Labour
157:Pre-Release File Sharing Studies and Music
1558:. GlobalNews. GlobalNews. 15 January 2017
1155:CS1 maint: multiple names: authors list (
1115:
1113:
1111:
1109:
1107:
1105:
1103:
1101:
1099:
1097:
917:
915:
913:
911:
909:
907:
905:
903:
465:over 102 upload sites such as SendSpace,
1708:
1706:
1704:
1702:
1680:TorrentFreak, Andy (14 September 2017).
1598:
1596:
1193:. Cable News Network. Cable News Network
1095:
1093:
1091:
1089:
1087:
1085:
1083:
1081:
1079:
1077:
979:
977:
975:
973:
1640:
1638:
1636:
1634:
808:
806:
486:
208:Album Leaks Before the Internet History
1782:
1758:
1756:
1754:
1752:
1750:
1748:
1417:
1406:
1350:
1346:
1336:
1214:
1204:
1180:
1178:
1145:
1141:
1131:
1051:
1047:
1037:
947:
943:
933:
889:
885:
875:
834:
830:
820:
792:
781:
777:
767:
732:
728:
718:
689:
677:
673:
663:
539:
537:
523:
511:
507:
497:
134:Torrent Software for Mac :Transmission
1021:
1019:
412:Government Communication Headquarters
199:Pre-Release File Sharing as Promotion
7:
584:"How to Search for BitTorrent Files"
250:X-Men Origins: Wolverine Leak (2009)
49:for a dashboard.wikiedu.org course.
1795:
1731:
1659:
1617:
1482:"The Digital Copyright Act of 1998"
1223:
1161:
1060:
1002:
956:
843:
754:. New York: Routledge. p. 89.
561:
255:Judge Margaret Morrow. for 1 year.
1532:Bogart, Nicole (13 January 2017).
1416:Cite has empty unknown parameter:
636:"A beginner's guide to BitTorrent"
24:
1435:Dawson, James (14 October 2017).
750:Scholz, edited by Trebor (2013).
327:Game of Thrones Season 7 HBO Leak
222:Pre-Release File Sharing and Film
1439:. LADbible Group. LADbible Group
1391:Gibbs, Samuel (21 August 2017).
1368:Spangler, Todd (7 August 2017).
709:Information Economics and Policy
29:
1763:Hildebrandt, Pereira, Seglins.
610:"How Torrent Downloading Works"
1372:. Variety Media. Variety Media
273:The Hulk 2003 Pre-Release Leak
84:that combines the concepts of
1:
1771:. CBC/Radio Canada. CBC News
1028:Information Systems Research
122:File:Dropbox logo (2013).svg
1824:
1480:Copyright Office Summary.
37:This is a user sandbox of
1581:. Custos Media Technology
1122:Telecommunications Policy
1536:. GlobalNews. GlobalNews
1244:Wilson, Michael (2010).
408:National Security Agency
362:United States of America
78:Pre-Release File Sharing
73:Pre-Release File Sharing
281:
1277:The Hollywood Reporter
688:Cite journal requires
522:Cite journal requires
394:The Hurt Locker (2008)
392:for sharing the movie
336:
135:
127:
18:User:RussellThomasWiki
339:In 2017, "HBO's show
335:HBO's Game of Thrones
334:
133:
125:
1185:CNN, By Alan Duke.
388:set charges against
263:
102:digital distribution
582:Mitchell, Bradley.
183:information economy
90:information leaking
1347:|access-date=
1250:The New York Times
1217:has generic name (
1142:|access-date=
1048:|access-date=
944:|access-date=
886:|access-date=
831:|access-date=
795:has generic name (
778:|access-date=
729:|access-date=
674:|access-date=
544:Mitchel, Bradley.
508:|access-date=
410:(the NSA) and the
337:
282:Outsider's Attacks
215:Great White Wonder
136:
128:
1603:TheGlobeAndMail.
1271:Belloni, Mathew.
761:978-0-415-89694-8
70:
69:
40:RussellThomasWiki
1815:
1807:
1806:
1805:
1804:
1794:
1788:
1780:
1778:
1776:
1760:
1743:
1742:
1741:
1740:
1730:
1728:
1726:
1710:
1697:
1696:
1694:
1692:
1677:
1671:
1670:
1669:
1668:
1658:
1656:
1654:
1642:
1629:
1628:
1627:
1626:
1616:
1614:
1612:
1600:
1591:
1590:
1588:
1586:
1574:
1568:
1567:
1565:
1563:
1552:
1546:
1545:
1543:
1541:
1529:
1523:
1522:
1520:
1518:
1502:
1496:
1495:
1493:
1491:
1486:
1477:
1471:
1470:
1468:
1466:
1455:
1449:
1448:
1446:
1444:
1432:
1426:
1425:
1419:
1414:
1412:
1404:
1402:
1400:
1388:
1382:
1381:
1379:
1377:
1365:
1359:
1358:
1352:
1348:
1344:
1342:
1334:
1322:
1316:
1315:
1313:
1311:
1295:
1289:
1288:
1286:
1284:
1268:
1262:
1261:
1259:
1257:
1241:
1235:
1234:
1233:
1232:
1222:
1216:
1212:
1210:
1202:
1200:
1198:
1182:
1173:
1172:
1171:
1170:
1160:
1153:
1147:
1143:
1139:
1137:
1129:
1117:
1072:
1071:
1070:
1069:
1059:
1053:
1049:
1045:
1043:
1035:
1023:
1014:
1013:
1012:
1011:
1001:
999:
997:
981:
968:
967:
966:
965:
955:
949:
945:
941:
939:
931:
919:
898:
897:
891:
887:
883:
881:
873:
861:
855:
854:
853:
852:
842:
836:
832:
828:
826:
818:
810:
801:
800:
794:
789:
783:
779:
775:
773:
765:
747:
741:
740:
734:
730:
726:
724:
716:
704:
698:
697:
691:
685:
679:
675:
671:
669:
661:
657:
651:
650:
648:
646:
631:
625:
624:
622:
620:
605:
599:
598:
596:
594:
579:
573:
572:
571:
570:
560:
558:
556:
541:
532:
531:
525:
519:
513:
509:
505:
503:
495:
491:
443:and BitTorrent.
386:Voltage Pictures
123:
65:
63:
33:
32:
26:
1823:
1822:
1818:
1817:
1816:
1814:
1813:
1812:
1811:
1810:
1798:
1796:
1781:
1774:
1772:
1762:
1761:
1746:
1734:
1732:
1724:
1722:
1721:. The Intercept
1712:
1711:
1700:
1690:
1688:
1679:
1678:
1674:
1662:
1660:
1652:
1650:
1644:
1643:
1632:
1620:
1618:
1610:
1608:
1602:
1601:
1594:
1584:
1582:
1576:
1575:
1571:
1561:
1559:
1554:
1553:
1549:
1539:
1537:
1531:
1530:
1526:
1516:
1514:
1513:. Michael Geist
1505:Michael Geist.
1504:
1503:
1499:
1489:
1487:
1484:
1479:
1478:
1474:
1464:
1462:
1457:
1456:
1452:
1442:
1440:
1434:
1433:
1429:
1415:
1405:
1398:
1396:
1390:
1389:
1385:
1375:
1373:
1367:
1366:
1362:
1345:
1335:
1324:
1323:
1319:
1309:
1307:
1298:Gilani, Nadia.
1297:
1296:
1292:
1282:
1280:
1270:
1269:
1265:
1255:
1253:
1243:
1242:
1238:
1226:
1224:
1213:
1203:
1196:
1194:
1184:
1183:
1176:
1164:
1162:
1154:
1140:
1130:
1119:
1118:
1075:
1063:
1061:
1046:
1036:
1025:
1024:
1017:
1005:
1003:
995:
993:
983:
982:
971:
959:
957:
942:
932:
921:
920:
901:
884:
874:
863:
862:
858:
846:
844:
829:
819:
812:
811:
804:
791:
776:
766:
762:
749:
748:
744:
727:
717:
706:
705:
701:
687:
672:
662:
659:
658:
654:
644:
642:
633:
632:
628:
618:
616:
607:
606:
602:
592:
590:
581:
580:
576:
564:
562:
554:
552:
543:
542:
535:
521:
506:
496:
493:
492:
488:
483:
462:
457:
449:
437:
428:
403:
382:
373:
364:
359:
350:
341:Game of Thrones
329:
296:
284:
275:
266:
261:
259:Security Issues
252:
235:
224:
210:
201:
192:
175:
159:
154:
141:
121:
110:
75:
66:
61:
59:
57:
56:
50:
44:
30:
22:
21:
20:
12:
11:
5:
1821:
1819:
1809:
1808:
1744:
1698:
1672:
1630:
1607:. GlobeAndMail
1592:
1569:
1547:
1524:
1497:
1472:
1450:
1427:
1383:
1360:
1317:
1290:
1263:
1236:
1174:
1073:
1015:
984:Harvey, Eric.
969:
899:
866:Social Text 63
856:
802:
760:
742:
699:
690:|journal=
652:
626:
600:
574:
533:
524:|journal=
485:
484:
482:
479:
461:
458:
456:
453:
448:
445:
436:
433:
427:
424:
402:
399:
381:
378:
372:
369:
363:
360:
358:
355:
349:
346:
328:
325:
295:
292:
283:
280:
274:
271:
265:
264:Insider's Leak
262:
260:
257:
251:
248:
234:
231:
223:
220:
209:
206:
200:
197:
191:
188:
174:
171:
158:
155:
153:
150:
140:
137:
109:
106:
74:
71:
68:
67:
58:
36:
34:
23:
15:
14:
13:
10:
9:
6:
4:
3:
2:
1820:
1802:
1792:
1786:
1770:
1766:
1759:
1757:
1755:
1753:
1751:
1749:
1745:
1738:
1720:
1719:The Intercept
1716:
1709:
1707:
1705:
1703:
1699:
1687:
1683:
1676:
1673:
1666:
1648:
1641:
1639:
1637:
1635:
1631:
1624:
1606:
1599:
1597:
1593:
1580:
1573:
1570:
1557:
1551:
1548:
1535:
1528:
1525:
1512:
1511:Michael Geist
1508:
1501:
1498:
1483:
1476:
1473:
1460:
1454:
1451:
1438:
1431:
1428:
1423:
1410:
1394:
1387:
1384:
1371:
1364:
1361:
1356:
1340:
1332:
1328:
1321:
1318:
1305:
1301:
1294:
1291:
1278:
1274:
1267:
1264:
1251:
1247:
1240:
1237:
1230:
1220:
1208:
1192:
1188:
1181:
1179:
1175:
1168:
1158:
1151:
1135:
1127:
1123:
1116:
1114:
1112:
1110:
1108:
1106:
1104:
1102:
1100:
1098:
1096:
1094:
1092:
1090:
1088:
1086:
1084:
1082:
1080:
1078:
1074:
1067:
1057:
1041:
1033:
1029:
1022:
1020:
1016:
1009:
991:
987:
980:
978:
976:
974:
970:
963:
953:
937:
929:
925:
918:
916:
914:
912:
910:
908:
906:
904:
900:
895:
879:
871:
867:
860:
857:
850:
840:
824:
816:
809:
807:
803:
798:
793:|first1=
787:
771:
763:
757:
753:
746:
743:
738:
722:
714:
710:
703:
700:
695:
683:
667:
656:
653:
641:
637:
630:
627:
615:
611:
604:
601:
589:
585:
578:
575:
568:
551:
547:
540:
538:
534:
529:
517:
501:
490:
487:
480:
478:
474:
472:
468:
459:
454:
452:
446:
444:
442:
434:
432:
425:
423:
421:
417:
413:
409:
400:
398:
395:
391:
387:
379:
377:
370:
368:
361:
357:Infringements
356:
354:
347:
345:
342:
333:
326:
324:
322:
318:
314:
310:
306:
302:
293:
291:
287:
279:
272:
270:
258:
256:
249:
247:
246:considered".
243:
239:
232:
230:
228:
221:
219:
216:
207:
205:
198:
196:
189:
187:
184:
179:
172:
170:
166:
164:
156:
151:
149:
146:
138:
132:
124:
118:
116:
107:
105:
103:
99:
95:
91:
87:
83:
80:is a type of
79:
72:
64:
54:
53:Sandbox Draft
48:
42:
41:
35:
28:
27:
19:
1797:Cite error:
1773:. Retrieved
1768:
1733:Cite error:
1723:. Retrieved
1718:
1713:Lee, Micah.
1689:. Retrieved
1686:TorrentFreak
1685:
1675:
1661:Cite error:
1651:. Retrieved
1619:Cite error:
1609:. Retrieved
1583:. Retrieved
1572:
1560:. Retrieved
1550:
1538:. Retrieved
1527:
1515:. Retrieved
1510:
1500:
1488:. Retrieved
1475:
1463:. Retrieved
1453:
1441:. Retrieved
1430:
1397:. Retrieved
1386:
1374:. Retrieved
1363:
1339:cite journal
1330:
1326:
1320:
1308:. Retrieved
1303:
1293:
1281:. Retrieved
1276:
1266:
1254:. Retrieved
1249:
1239:
1225:Cite error:
1215:|last1=
1195:. Retrieved
1190:
1163:Cite error:
1134:cite journal
1125:
1121:
1062:Cite error:
1040:cite journal
1031:
1027:
1004:Cite error:
994:. Retrieved
992:. Condé Nast
989:
958:Cite error:
936:cite journal
927:
923:
878:cite journal
869:
865:
859:
845:Cite error:
823:cite journal
814:
751:
745:
721:cite journal
712:
708:
702:
666:cite journal
655:
643:. Retrieved
639:
634:Pash, Adam.
629:
617:. Retrieved
613:
603:
591:. Retrieved
587:
577:
563:Cite error:
553:. Retrieved
549:
500:cite journal
489:
475:
463:
455:MUTANT BROTH
450:
438:
429:
404:
401:Surveillance
393:
383:
374:
365:
351:
338:
297:
288:
285:
276:
267:
253:
244:
240:
236:
229:
225:
211:
202:
193:
180:
176:
167:
160:
142:
126:Dropbox Logo
111:
86:data leaking
82:file sharing
77:
76:
52:
46:
38:
1585:23 November
1304:Mail Online
1191:www.cnn.com
715:(2016): 65.
608:Gil, Paul.
481:Works Cited
309:Apple Music
233:Movie Leaks
190:Album Leaks
1775:5 December
1725:5 December
1691:5 December
1649:. TechDirt
1645:TechDirt.
1562:6 November
1540:6 November
1517:6 November
1490:6 November
1465:6 November
1443:9 November
1399:9 November
1376:9 November
1351:|url=
1310:5 December
1283:5 December
1256:5 December
1197:5 December
1146:|url=
1052:|url=
996:5 December
948:|url=
890:|url=
835:|url=
782:|url=
733:|url=
678:|url=
645:6 December
640:Lifehacker
619:6 December
593:6 December
555:6 December
512:|url=
471:MegaUpload
467:RapidShare
460:LEVITATION
447:PLAGUE RAT
348:Regulation
145:BitTorrent
139:BitTorrent
108:Technology
1801:help page
1785:cite news
1737:help page
1665:help page
1623:help page
1409:cite news
1349:requires
1333:(9): 546.
1229:help page
1207:cite news
1167:help page
1144:requires
1066:help page
1050:requires
1034:(3): 602.
1008:help page
990:Pitchfork
962:help page
946:requires
888:requires
849:help page
833:requires
780:requires
770:cite book
731:requires
676:requires
567:help page
510:requires
435:DIRTY RAT
426:GRIMPLATE
384:In 2010,
1769:CBC News
1577:Custos.
1418:|1=
614:Lifewire
588:Lifewire
550:Lifewire
390:TekSavvy
62:Get Help
45:This is
420:eDonkey
317:Spotify
301:Netflix
163:Napster
115:Dropbox
94:hacking
758:
371:Canada
98:piracy
1653:4 Dec
1611:4 Dec
1485:(PDF)
817:: 37.
441:eMule
416:Kazaa
321:Panda
152:Music
16:<
1791:link
1777:2017
1727:2017
1693:2017
1655:2017
1613:2017
1587:2017
1564:2017
1542:2017
1519:2017
1492:2017
1467:2017
1445:2017
1422:help
1401:2017
1378:2017
1355:help
1312:2017
1285:2017
1258:2017
1219:help
1199:2017
1157:link
1150:help
1056:help
998:2017
952:help
930:(1).
894:help
872:(2).
839:help
797:help
786:help
756:ISBN
737:help
694:help
682:help
647:2017
621:2017
595:2017
557:2017
528:help
516:help
469:and
418:and
319:and
313:Hulu
100:and
305:HBO
1803:).
1787:}}
1783:{{
1767:.
1747:^
1739:).
1717:.
1701:^
1684:.
1667:).
1633:^
1625:).
1595:^
1509:.
1413::
1411:}}
1407:{{
1343::
1341:}}
1337:{{
1331:14
1329:.
1302:.
1275:.
1248:.
1231:).
1211::
1209:}}
1205:{{
1189:.
1177:^
1169:).
1138::
1136:}}
1132:{{
1126:28
1124:.
1076:^
1068:).
1044::
1042:}}
1038:{{
1032:25
1030:.
1018:^
1010:).
988:.
972:^
964:).
940::
938:}}
934:{{
928:19
926:.
902:^
882::
880:}}
876:{{
870:18
868:.
851:).
827::
825:}}
821:{{
805:^
790:;
774::
772:}}
768:{{
725::
723:}}
719:{{
713:37
711:.
686:;
670::
668:}}
664:{{
638:.
612:.
586:.
569:).
548:.
536:^
520:;
504::
502:}}
498:{{
323:.
315:,
311:,
307:,
303:,
96:,
92:,
88:,
1793:)
1779:.
1729:.
1695:.
1657:.
1615:.
1589:.
1566:.
1544:.
1521:.
1494:.
1469:.
1447:.
1424:)
1420:(
1403:.
1380:.
1357:)
1353:(
1314:.
1287:.
1260:.
1221:)
1201:.
1159:)
1152:)
1148:(
1128:.
1058:)
1054:(
1000:.
954:)
950:(
896:)
892:(
841:)
837:(
799:)
788:)
784:(
764:.
739:)
735:(
696:)
692:(
684:)
680:(
649:.
623:.
597:.
559:.
530:)
526:(
518:)
514:(
Text is available under the Creative Commons Attribution-ShareAlike License. Additional terms may apply.